Malwarebytes 4.4.4 adds RDP Brute Force Protection among other things
Our last look at the security software Malwarebytes dates back to 2019 when Malwarebytes 4.0 was released. The release had its fair share of issues that included incompatibilities with other programs, high memory usage among other things.
Malwarebytes for Windows 4.4.4 was released this week, and it is the latest of many releases of the program's 4.x branch.
The release is already available via the security program's built-in updating functionality. Users who download the offline installer won't get version 4.4.4 at this point but version 4.4.3. The online installer, which requires an Internet connection, will install the latest version.
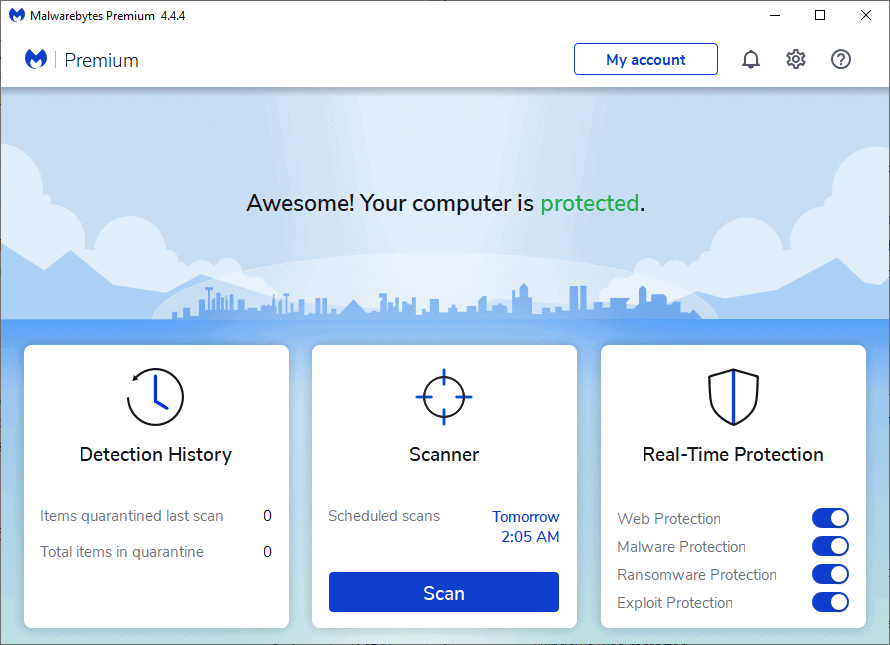
Malwarebytes 4.4.4's memory usage changed significantly between states. Minimized, the program used about 150 Megabytes on a Windows 10 system; this went up when the GUI was shown and during scanning activity.
Malwarebytes 4.4.4
Malwarebytes 4.4.4 includes several feature additions. One of the main new features of this release is that it may protect against remote Desktop Protocol (RDP) brute force attacks. The feature is available for all Malwarebytes for Windows and Teams customers, and was disabled by default on our test system.
Select Settings > Security to enable the Remote Desktop Protocol (RDP) brute force protection.
Blocks Remote Desktop Protocol (RDP) attacks from hackers attempting to access your computer over a network connection by guessing the username and password.
Once enabled, an advanced options button becomes available. The options allow you to change the port and trigger rules for the protection. By default, IP addresses are blocked if five failed attempts are made within 5 minutes.
Remote Desktop Protocol attacks have risen during the Covid-19 pandemic due to an increase in remote work environments, usually work from home. Administrators may reduce attack vectors through various means, including requiring strong passwords, using custom ports, monitoring logs or limiting access to certain IP addresses.
The second new feature in version 4.4.4 of Malwarebytes for Windows adds protection against unauthorized uninstallation of the program to all Windows and Teams customers.
Select Settings > General an enable the User access feature on the page that opens.
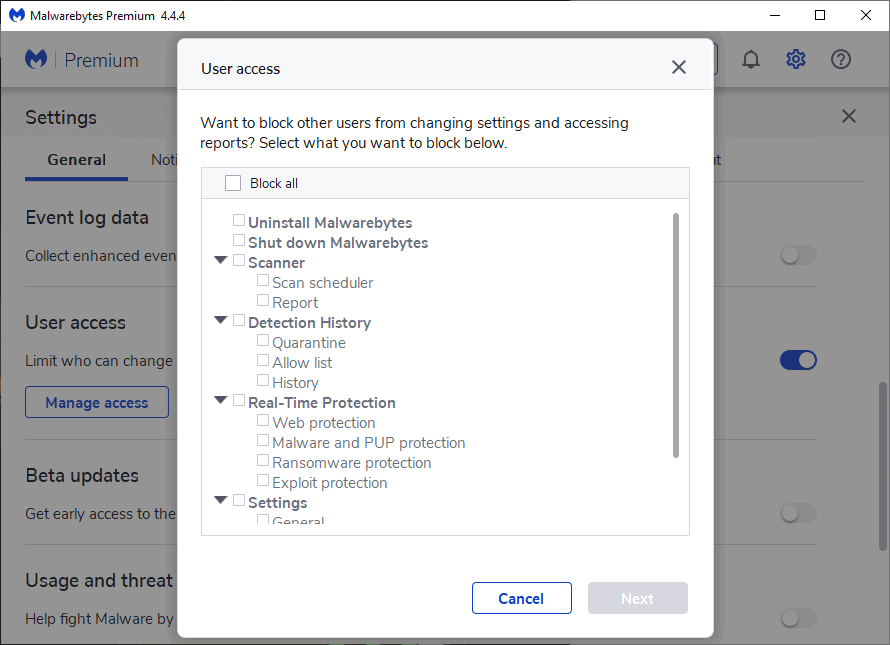
You may prevent access to settings and reports here, and the uninstallation or shutdown of the Malwarebytes application. Once activated, users need to supply a password that is set during setup of the protective feature.
Malwarebytes displays a threat summary notification every 30 days by default. You could disable the notification entirely already, but have now a new option to hide it if no threats were detected in the period.
Select Settings > Notifications and select the "Only show if threats were detected" option at the top of the page.
The new version fixed several issues that users experienced in previous versions. Several address issues of the Browser Guard extension, including one that caused high memory usage in Google Chrome when Chrome was reopened on Windows.
You may check out the entire changelog on Malwarebytes support website.
Now You: which security programs do you use to protect your devices? (via Techdows)

















Very bad software https://nl-be.trustpilot.com/review/malwarebytes.com Best is not to mentioning again. Have also seen professional tests a year ago and was also terrible. Most get some to give it a + but is a — DYOR.
The [full] offline installer for Malwarebytes 4.4.4.228 (digitally signed 2 AUG 2021) is now live for download (203 MB).
If you’re outside of Russia, use Kaspersky (or some other non-whatever-your-country-is) if you’re in Russia, use American made scanners. It’s funny how this works, I’ve found stuff with software from one country that most of the others fail to find.
“If you’re outside of Russia, use Kaspersky (or some other non-whatever-your-country-is) if you’re in Russia, use American made scanners.”
Lol
For years they claimed MWB wasn’t an AV, now it is? There seemed to be a general industry marketing tact distinguishing between viruses and malware and MWB filled the malware niche well.
MWB has good brand recognition but maybe should work on a new name since the various attack vectors are all more or less lumped together now. All AV’s, browsers, ad blockers, whatever have claimed to block malware for years. Not sure the term is as meaningful today. Sentiment goes only so far.
If you really do pick up something nasty, there are now many legitimate utilities available to kill it, not just MWB.
Over the last few years I don’t know that I’ve had MWB catch much other than PUAs. It seemed 8-10 years ago MWB was ahead of the game (certainly in the free category), and yeah maybe since around v3 they may have lost their edge
On Win 10, note that Win Home doesn’t come with RDP (although there is a hack to install it, if you want), so this isn’t an issue.
Out of curiosity, has anyone ever had MWB “save” them from a actual dangerous threat? I like and recommend the company’s tiny Anti-Ransomware beta, and I usually install their Anti-Exploit beta on pre-Win-10 machines (Win 10 has most of that protection baked-in, especially if you use ConfigureDefender to harden Win Defender).
But the main MWB program has been a buggy resource hog since v3, and I just haven’t found it useful to save my clients from anything in the real world.
Never. As an always on program, it’s a massive slower downer. I used to install it every six months or so, run it, then uninstall. Their Adware utility found a few rather benign things years ago. Don’t see any point in MWB these days.
Isn’t RDP open only to LAN/VPN by default anyway? I used hacks from GitHub to enable RDP on Windows Home editions.
Thanks for the review. One quick note.
There is no such thing as a “strong passwords,”
MFA, or even better, replacing passwords with much stronger auth is the the real solution. The others are just partial protection for RDP brute force attacks.
I have a perpetual license for Malwarebytes but stopped using it with us high memory. I have since transitioned Acronis True Image that has a built in AV and will also look after my backups. Best of both worlds imo.