Custom browser protocol handlers may be used for fingerprinting
When you install certain applications on your desktop systems, so-called custom protocol handlers may be added. These are used to launch the application in question, e.g. to initiate a Skype call or open a game on Steam.
Popular applications such as Skype, Spotify, Discord, WhatsApp, TeamViewer, or Slack make use of custom protocols.
Sites may test for support for these protocols in a browser and use the information for fingerprinting.
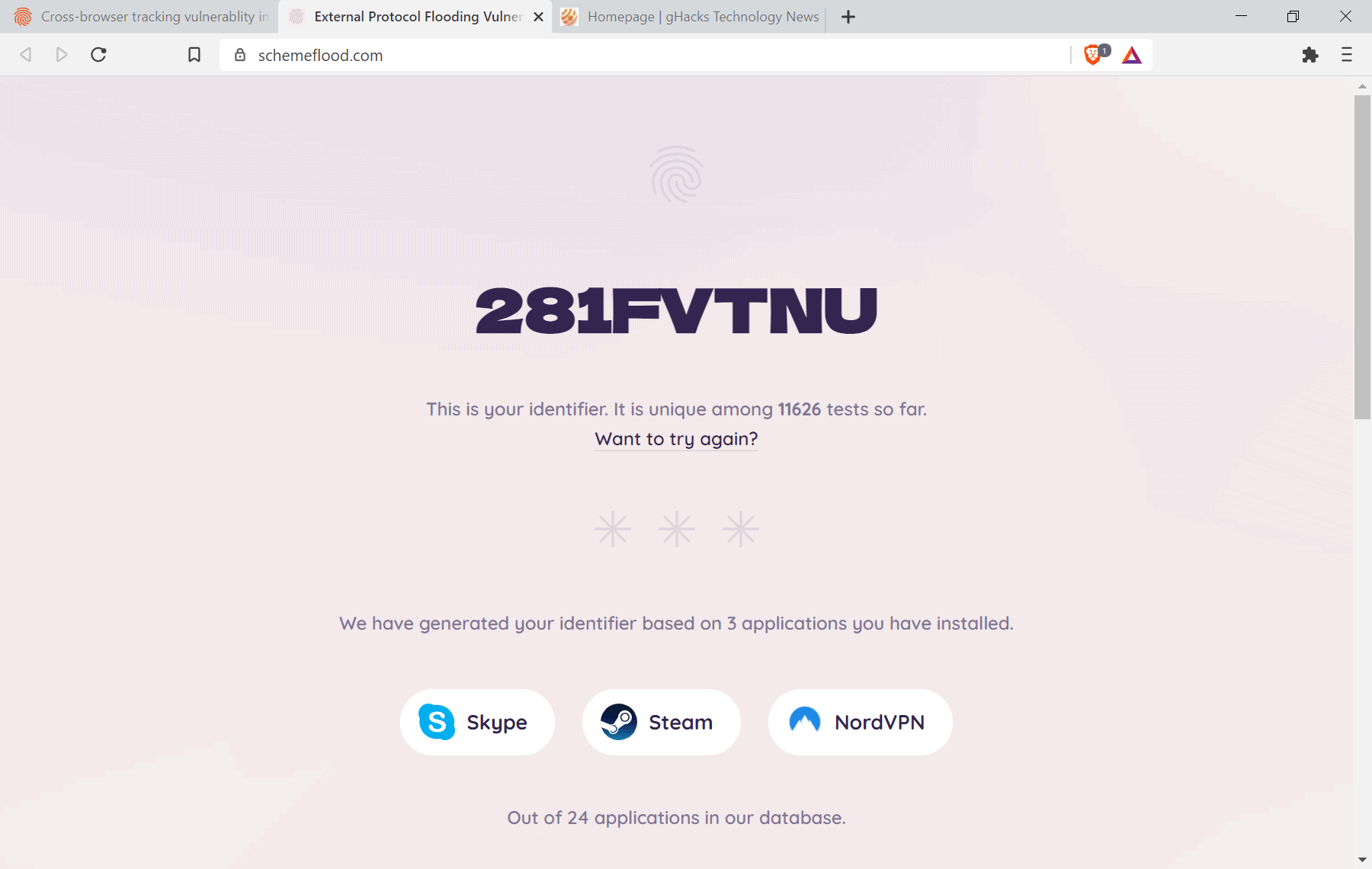
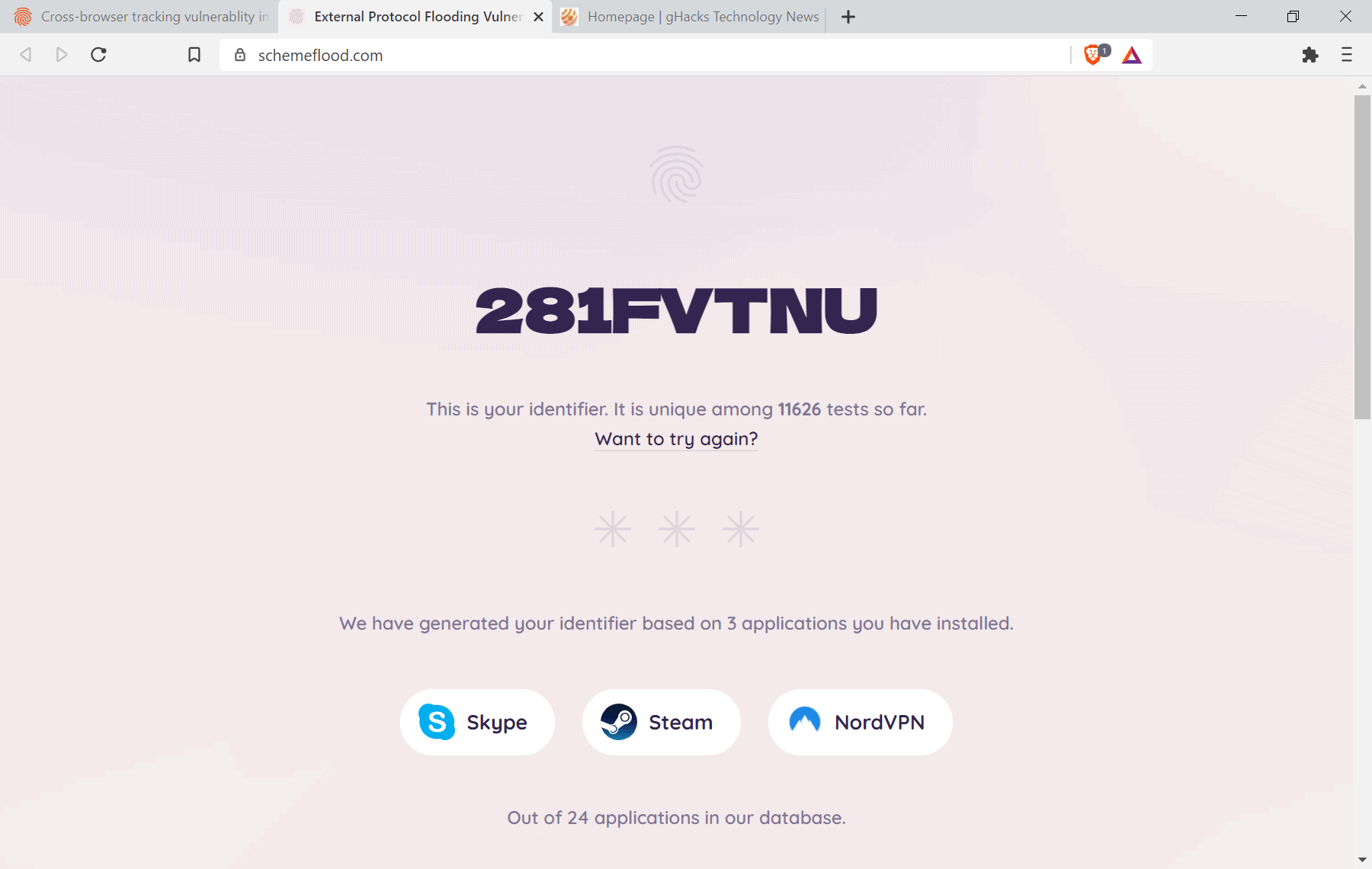
A demo site has been created that checks if the custom protocol handlers of 24 applications are supported (on Windows). A total of 32 different application protocol handlers are supported right now.
The identification works across operating systems and browsers. It can be used, at least in theory, to identify a user based on the results of the test alone.
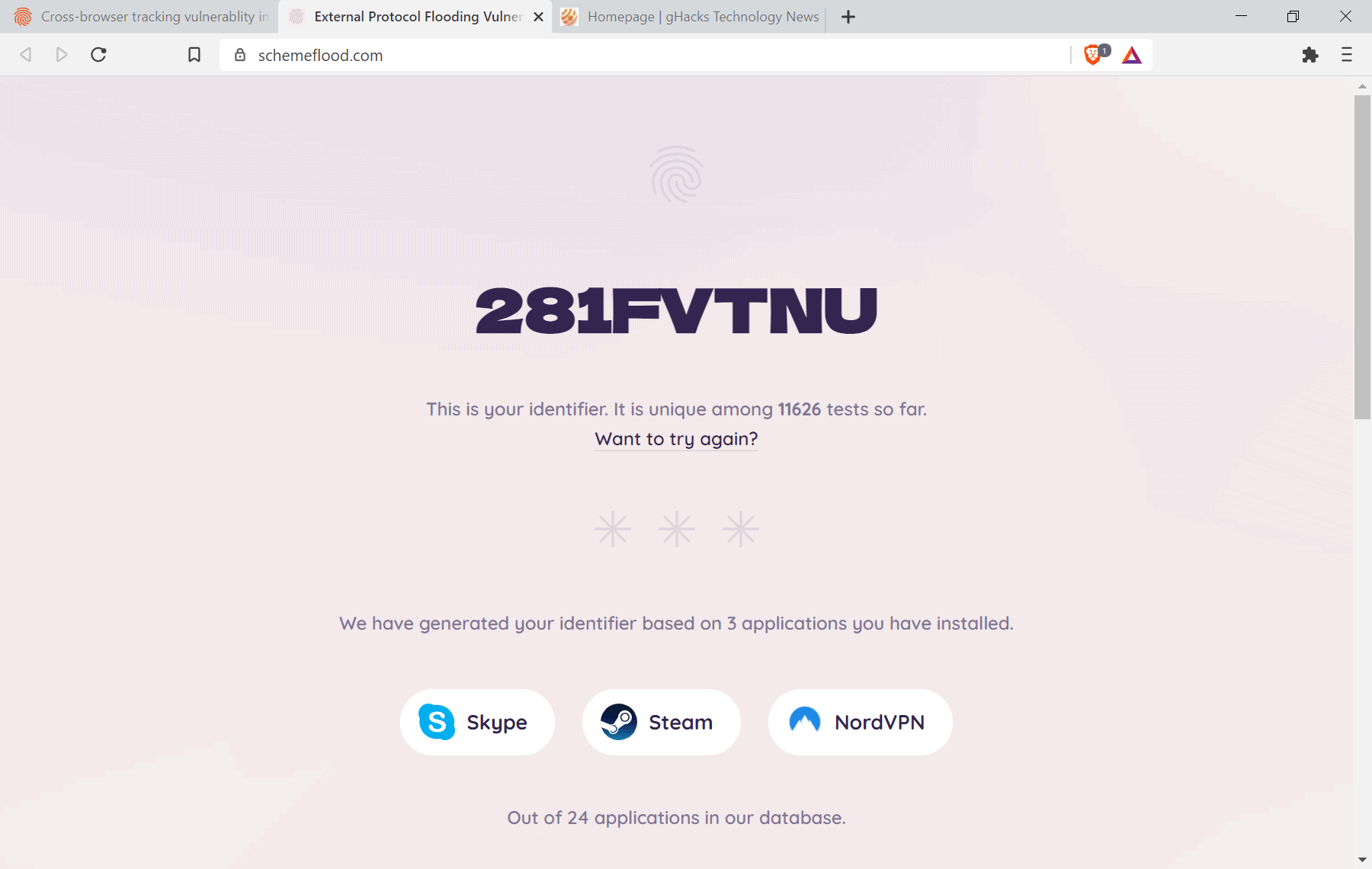
The demo site computes an identifier based on its findings each time the test is run. The developers suggest that you may run the test in different browsers, e.g. Firefox, Chrome. Safari and Tor Browser, to check if you can be identified based on the support of external protocols.
Fingerprinting can be improved by using other identifying factors next to those used in the demo. The checks for the supported custom protocol handlers are clearly visibly when you run the demo in three of the four browsers that are officially supported (Chrome, Firefox and Safari).
The information may be used to identify users of the Tor browser, but also for targeted advertisement or user tracking and profiling. The type of applications that are installed may reveal valuable information to advertisers and potentially also to malicious actors. A user who has several game clients installed may respond well to game-related ads, while a TeamViewer or Slack user to business-related ads.
The developers reveal how they managed to run the identification script in the four tested browsers. They note that Google appears to be aware of this and is working on a solution to prevent the attack from taking place. It is likely that other browser companies will implement security protections of their own to block this attack from being successful.
Bugs were reported to Mozilla, Google and Apple. You can check the bug on Mozilla's bug tracking site to find out if and when it gets fixed in Firefox (and Tor).
The source code for the demos has been released on GitHub.
As far as protection in the meantime is concerned, a script-blocker may prevent the attack from being carried out in the first place.
Now You: do you have programs with custom protocol handlers installed on your devices?




















It works.
On Windows I block it by injecting DLL library which hooks advapi32.dll!RegOpenKeyExW function (https://docs.microsoft.com/en-us/windows/win32/api/winreg/nf-winreg-regopenkeyexw) and returns ERROR_ACCESS_DENIED if hKey == HKEY_CLASSES_ROOT and lpSubKey doesn’t contain backslashes ‘\’.
Does anybody know how to fix it on Linux?
Read this: https://www.fortinet.com/blog/threat-research/leaking-browser-url-protocol-handlers
This “check” is utter nonsense. Tried 3 times and the results are different each time! :D
On the second try it stated that I am running 22 of the 24 in the database. I have none of these installed… and I’m running linux to boot.. it should have returned nothing.
It says i have spotify installed but i freshly installed windows and there is no spotify on my computer. I wanna know how reliable is this?
after reading the explanation of how the fingerprinting works, on chromium browsers disabling the PDF reader (I.E. switching Always download PDF files to true in about:settings/content/pdfdocuments) removes this vector of attack.
theoretically, a site can use any extension to bypass chromium’s protection against this attack, so beware, the PDF reader is just the most convenient as it exists on every chromium browser.
Brave browser – Skype and ExpressVPN
Went to Settings>Privacy & security>Site and Shields settings>Additional content settings>PDF documents>Download PDF files On
Tried to run the test but was blocked from running. Win?
Schemeflood identification results for me, with 3 of the 24 identifier apps installed (Skype, Spotify, and MS Word):
— Firefox 78.10.1 ESR: shows all 24, so not right.
— Vivaldi 3.8.2259.37: finds only one of the installed 3 (Skype), so not right.
— Chrome 90.0.4430.212: finds the installed 3, so correct.
So in my case, this kind of identification may only work with Chrome.
That’s strange. Of the 24 applications I currently run 3 but it says I am running 23 of the 24. I did have Battle.net at one point but have since uninstalled it. Clearly uninstalling applications doesn’t uninstall the protocol handler. So can this be done manually.
It says I am running steam but steam has never been installed. Neither has teamviewer and a host of others, so do applications share the same handler? Why would it report that I am running applications that have never even been installed?
Whoever has all those applications installed deserved to be tracked.
I only have one.
Moral of the story: reduce your attack surface.
Or build different VMs and separate work, play, social media, etc. from one another.
Tells me I have Skype (surprisingly, yes never used); Zoom (yes); and, Microsoft Word. Run thrice for three different identifiers.
Brags “That means it is 99.97% unique.”
So far, I rate it a fail.
Skype: not listed as an installed program or Microsoft app and not found by my uninstaller program
Looks like most of the software on the database are bloated electron garbage. Glad I don’t use any of those to be fingered.
Awesome…for Firefox says it found 24 out of 24. And I have none of them installed.
Brave: 4 identifiers found.
Firefox: 5 identifiers found.
Microsoft Edge: 0 identifiers found.
God bless Microsoft!
That’s just you. The test couldn’t even open on my Ungoogle Chromium. LOL
https://i.imgur.com/9obo2cg.jpg
works only on Edge for me
How do I disable application URL schemes?
as that page seems to belong to or be sponsored by “fingerprint.js” it would seem to me that all you are doing is helping making their fingerprinting system better.
Ungoogled-Chromium: https://i.imgur.com/A4e3mzA.png
The test can’t even run here. [Open] does nothing.
FirefoxESR (own config): https://i.imgur.com/6xjzUqt.png
Complete nonsense. Out of everything listed there only Steam is installed on this machine, and the handler is disabled for that within Windows.
Same nonsense result as Yuli on FF ESR. It says I have 23 apps installed, when actually I have none of them. It gives me a “unique identifier” that is the same as Yuli’s with a couple of extra zeros.
This is a useless waste of time.
This doesn’t apply to most people but if you have a rare application installed then you can be easily tracked. It also doesn’t prove much of anything if you use multiple browsers.