When security products make systems less secure
There has been an increase in reports pf security products recently which make user systems less secure when they are installed, used or even just present on the system.
Many antivirus companies have added tools and products to their security programs in recent years to increase the perceived value of the product, add new features to them that users may find useful, and to add new revenue opportunities in form of custom search deals.
It is quite common for instance that companies deploy browser extensions on systems that change the search provider, new tab page or home page. Others have created custom versions of the Chromium browser to improve user security while the browser is being used, often calling these custom browsers secure or safe to indicate that.
Google started to analyze browser extensions and custom browsers recently and the results are quite disturbing.
The three custom Chromium-based browsers the company analyzed were found to weaken security instead of improving it.
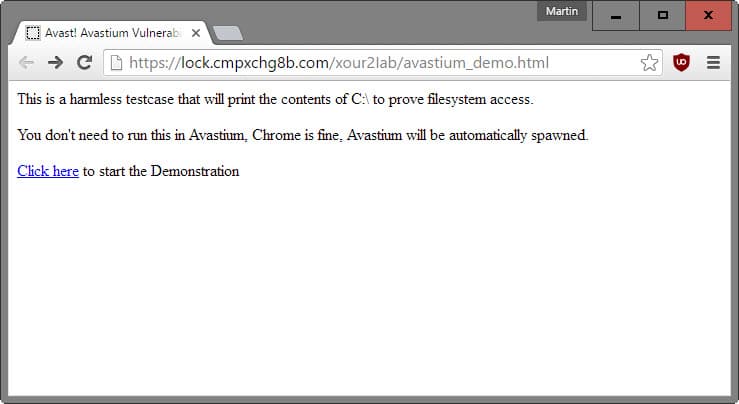
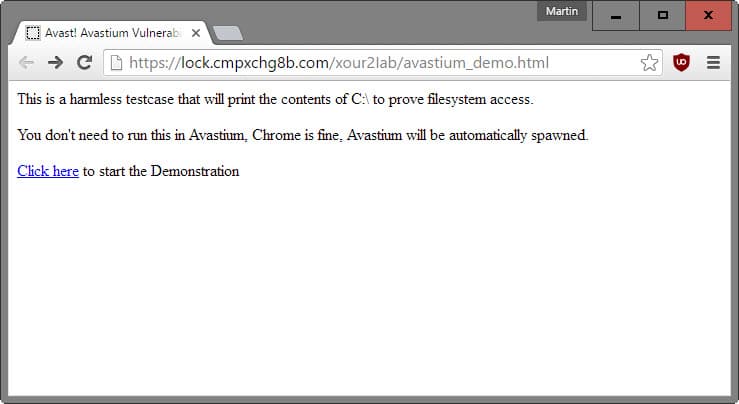
The latest company that Google contacted about security issues found in their products is Avast. The company's SafeZone browser, based on Chromium, allowed attackers to read any file on the system by getting users to click on links.
This worked even if users never used SafeZone, as data is automatically imported from a Chrome installation when the program is installed on the user system.
You don't even have to know the name or path of the file, because you can also retrieve directory listings using this attack. Additionally, you can send arbitrary *authenticated* HTTP requests, and read the responses. This allows an attacker to read cookies, email, interact with online banking and so on.
The company released an update in the meantime that fixed the issue. SafeZone is secure if you have build number 2016.11.1.2253 or newer installed.
Avast is not the only company that has been reprimanded by Google for weakening user security. Just two days ago, it was Comodo and the company's Chromodo browser, also based on Chromium, that was shamed publicly by Google.
And before that, Google revealed vulnerabilities in products by AVG, Trend Micro, Malwarebytes, and several other products as well.
While there is certainly always the possibility that software programs have security vulnerabilities, some may find it a fair assumption that these add-on products and services do more harm than good.
What weights even more is that these security companies should know better, considering that security and keeping users safe is their business.
Some companies provide users with options to customize what is installed during installation while others don't offer these options at all. It is probably a good idea to block the installation of any add-on service, browser extensions or standalone browsers, considering the findings of the past couple of months.


















Avast forced installed that browser on user today
https://forum.avast.com/index.php?topic=184577.15
https://forum.avast.com/index.php?topic=184576.0
And the representative said the users are ‘lucky’ to get that lol
Avast was my first choice since year 2002. Then it became nothing but a spam. I completely removed it from Windows and Android also. Trust no one. Instead virus is better.
Google has had it’s own walk of shames too in the past and present… do a search.
Any time a third party is involved especially with closed source there is a higher risk of security and privacy issues. Networks of Trust and transparency should be established to maintain some semblance of digital serenity.
Corrections to issues should be addressed professionally as well and preferably without name calling. e.g. abusive comments.
Quote for today:
“Judge Not Lest Ye Be Judged! and Let Him Who is Without Sin Cast the First Stone” * some theology rhetoric that has some good wisdom behind it :)
I’m curious as to what all Google has looked at. Maybe we will hear more as time goes along.
Very good Martin…thanks!
Giant is giant: Google does the ability to archive its goals effectively — Mind your back (* backdoor – in someway, security holes = backdoors), as Google is looking at you (your holes) — LOL, just kidding!
I’m curious to know if Epic Privacy Browser is as safe as they say. Has Google looked at them yet?
Any good product should be secure and in no need of any additional/upgraded/exended “security”. All those security products that people are encouraged to buy and install without any clue other than that feeling that they are buying the pig in a sack – they are just that: protection racket. Of course the scam is adapted to 21st century society…
“should” is the key word though. Most security flaws in software is due to bugs.
hence “most”
backdoors are not “flaws”.