Malware tricks that you may not know about

There is a constant cat and mouse game between malware, security software companies and computer users, and the chance of one side winning the battle seems slim at best.
Malwarebytes revealed recently on Malwarebytes Unpacked how Vonteera, a malware previously classified as adware, operates.
While it may not be of interest to many how that particular malware operates, the methods that it uses to infect computer systems and remain on them may very well be as they are used by other malware as well.
Vonteera does a lot to stay on the system: it installs a scheduled task, a service, a browser helper object in Internet Explorer, replaces known browser shortcuts to load select sites on startup, enables a Chrome policy that enables them to install apps and extensions in the browser that cannot be uninstalled, and adds several certificates to the untrusted certificates listing.
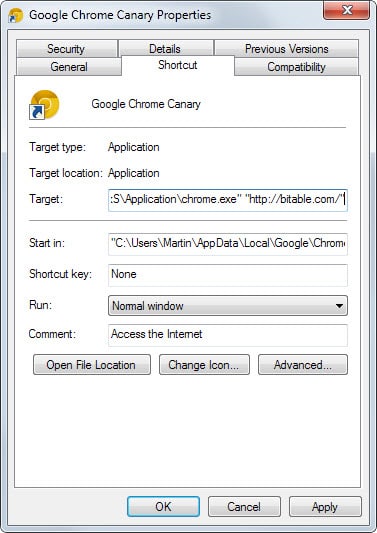
Manipulation of browser shortcuts
Some methods are used by adware and malicious software alike. The changing of the browser shortcut for instance to load sites on start. We have mentioned this method back in 2014 and it seems popular as it is easy to do and highly effective.
To check your shortcuts, right-click on the shortcut and select properties. Locate the target line on the page and check the parameters in the target field. If you find a url there, it will be opened on start.
Service installation
Services may be loaded on start of the operating system, or when they are needed depending on their configuration.
You can check all existing services by tapping on the Windows-key, typing services.msc and hitting enter. You may get an UAC prompt which you need to accept.
The interface offers limited information only. While you can sort services by name or status, there is no option to sort them by installation date.
If malware installs a service on the system, you can find out more about it in the Windows Registry.
- Tap on the Windows-key, type regedit.exe and hit enter.
- Navigate to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\ServiceName
- Check the ImagePath variable, as it highlights which file gets executed when the service is started.
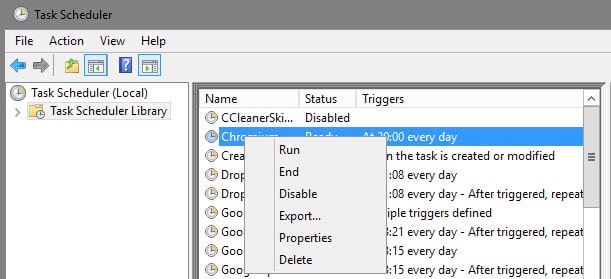
Scheduled Tasks
Tasks can be run under certain conditions, for instance on system start or shut down, at a specific day or time, or when the computer is idle.
To check Tasks on Windows, do the following:
- Tap on the Windows-key, type Taskschd.msc and hit enter.
- Select Task Scheduler Library and go through the listed tasks there.
You can delete tasks with a right-click and selecting "delete" from the context menu. You may disable them as well there, or check their properties (to see when they run, what they run and so on).
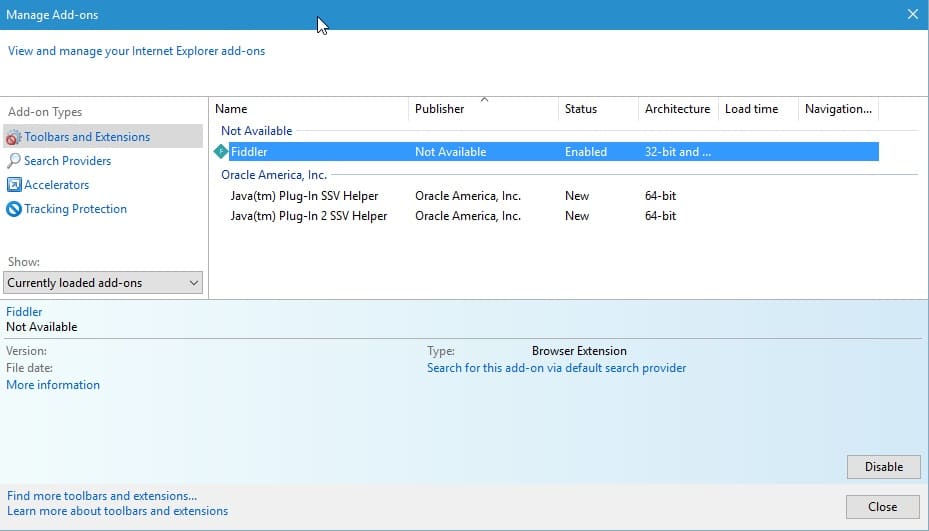
Internet Explorer Browser Helper Object
Browser Helper Objects are supported only by Internet Explorer. Microsoft's new browser Edge does not support them.
These work in similar fashion to extensions, meaning that they can change and record Internet sites and traffic among other things.
To manage browser helper objects in Internet Explorer, do the following:
- Open the Internet Explorer browser on your system.
- Tap on the Alt-key, and select Tools > Manage add-ons from the menu bar.
Go through all listings there, especially toolbars and extensions. You can disable items with a right-click and the selection of "disable" from the context menu. A click on "more information" reveals the Class ID of the Helper Object and additional information about it.
To delete them, you need to use the Registry Editor instead. Open the Windows Registry Editor and run a search for the Class ID using the Edit > Find menu. Enter the Class ID and delete all keys that come up.
I suggest you create a backup before you run the operating just to make sure you can go back if things turn out wrong.
Chrome Policy
Google's Chrome browser and Chromium support a large list of policies which enable enterprises to configure preferences on the system Chrome is run on.
The policy ExtensionInstallForcelist adds extensions to the browser for all users on the system that these users cannot remove from it.
The apps or extensions get installed silently, without user interaction, and all permissions requested get granted automatically.
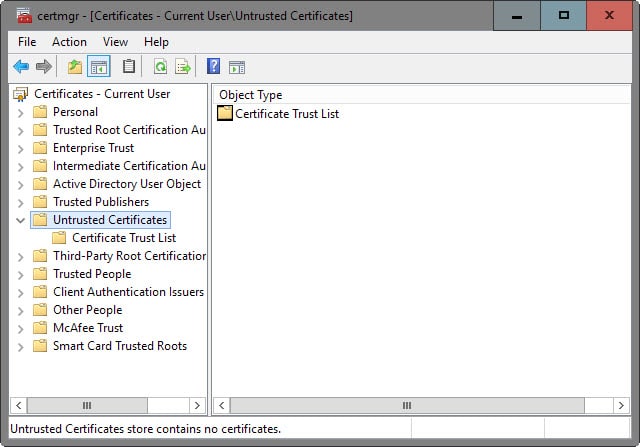
Untrusted Certificates
The malware added certificates of trusted antivirus solutions to the list of untrusted certificates on Windows.
This prevented the program from being started on the system, and it prevented the download of programs from the developer website as well (provided that the browser uses the Windows Certificate Store which Internet Explorer and Chrome do, but Firefox odes not).
- Tap on the Windows-key, type certmgr.msc and hit enter.
- Navigate to Untrusted Certificates and check all certs listed there.
- A right-click enables you to remove them from the list of untrusted certificates.
Now You: Know of other tricks malware uses?
















@Andy
Ninite.com is where I get my fresh installs or program updates. It never installs any of the bloatware or malware that is current at other download sites and many creators sites.
Where can one still find a safe download site at this time for security products for windows ? Thanks for your help
Thanks martin
My computer has 58 certificates listed as untrusted. Many have expired expiration dates. Is it ok to remove those? Some, supposedly issued by “Microsoft Services PCA”, have an expiration date of March 31, 2018. How can I quickly determine which certificates really belong in this list. Do I need to do an WEB search for each one? I have not experienced any strange behavior and my virus, rootkit, and malware scans have not found anything.
Martin,
NirSoft has the following that does allow sorting by “Last Write” not exactly install date, but might help narrow things down.
http://www.nirsoft.net/utils/serviwin.html
Good suggestion, thanks!
places fake iexplore.exe in some directory and modifies PATH variable (beginning of it)