Check whether your antivirus is vulnerable to exploitable RWX addresses
AV Vulnerability Checker is a free program for Windows that determines whether antivirus software installed on the computer is vulnerable to exploitable constant Read-Write-Execute (RWX) addresses.
Vulnerabilities are bad, regardless whether they are found in the operating system or programs running on it. One of the worst kind affects security software, programs that are designed to protect the system from attacks.
Ensilo, the company behind the product of the same name that "offers a real-time exfiltration prevention platform against advanced targeted attacks", revealed the security vulnerability that is affecting various antivirus products in a recent blog post.
It discovered the vulnerability while investigation a collision of the company's own enSilo product with AVG antivirus software.
Vulnerable anti-virus solutions "allocate a memory page with Read, Write, Execute permissions at a constant predictable address" and for various user-mode processes including those of web browsers or Adobe Reader.
The vulnerability enables attackers to bypass certain Windows mitigations against exploits, for instance ASLR or DEP since the attacker knows where to write and run code.
The company found the vulnerability in several antivirus products including McAfee Virus Scan for Enterprise version 8.8, Kaspersky Total Security 2015 and AVG Internet Security 2015.
Both AVG and McAfee appear to have fixed the issue in recent updates already.
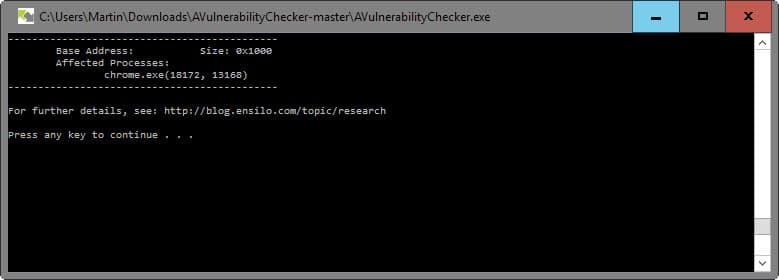
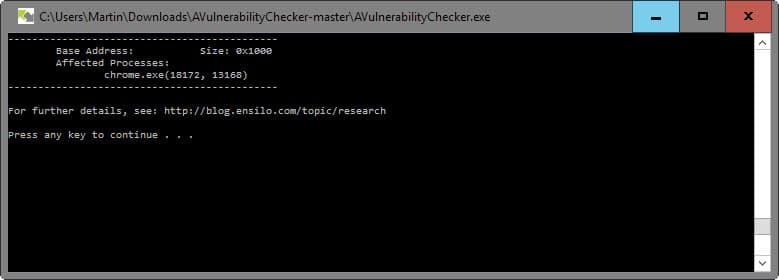
Ensilo released a program for Windows that tests other antivirus solutions for the vulnerability. The tool is available on Github.
- Click on download on Github and download the archive to the local system.
- Extract the archive afterwards to a local directory.
- Run AVulnerabilityChecker.exe.
The program tests the vulnerability using web browsers on the system. For it to work, you need to have a web browser open, and close it when the program requests you to do it.
Then you need to restart the web browser and open at least two new tabs in it. The program will then check whether the vulnerability can be exploited on the system.
Any memory region that exists in both scans is likely predictable and the program indicates this by listing those addresses and processes.
What it won't do is reveal the security solution that is vulnerable to the attack. The researchers suggest that you use a debugger to find that out, but if that sounds too complicated, you may want to disable security software instead and re-run the tests to find the culprit or culprits this way.
If you find out that a product that you run is vulnerable, there is little that you can do about it. After making sure that it is up to date, you may inform the developer of the program about the vulnerability.
















Bitdefender Internet Security 2016 Build 20.0.24.1290 is VULNERABLE with Windows 10.0.10586.17 & Google Chrome 47.0.2526.80 m
Is there any easy way to check which application is vulnerable?
Thank you.
i had a BSOD when i clicked the program. Anyone else have this problem
i got BSOD when i clicked on the program anyone else get this
In the source code it’s easy to see that it only tests for the vulnerability in the following processes : “chrome.exe”, “iexplore.exe”, “firefox.exe”.
Shame it didnt detect PaleMoon being an active browser, had to go back to IE, still said it wasnt vulnerable, though Panda never had to block anything, strange :)
Hey Martin
It gives me the message: (Your computer is likely to be vulnerable to exploitable constant RWX addresses) Even when my antivirus is shut off it gives me that message. Does that mean that my antivirus is clear or does that mean that my antivirus and something else is vulnerable?
Must be another program then, I fear that you will have to use a debugger in this case to find out.
May want to read what is really going on. The brief article here suggests that the vulnerability is a “browser” issue which it is not. The RWX vulnerability may exist in any application. As of September, all AV products had been patched. It’s really a MS issue, one of an unintended operating system design problem that is most likely mitigated by running EMET.
http://blog.ensilo.com/the-av-vulnerability-that-bypasses-mitigations
It’s not in the browser, in fact the article you posted a link to actually say as much.
“It is important to note that although we use browsers to check this vulnerability – the vulnerability is not in the browser”
The “brief article” does not suggest that it is a browser issue.
It’s got nothing to do with other programs, the AV programs created a hook in memory for each user-mode processes launched, a hook that used the same memory address each instance of the user-mode processes, it’s why they used two browser processes to cross reference the two and find the memory address that the AV program was using.
It was without doubt a problem with the AV software, that’s unless you’re suggesting that the AV software devs wrote patches for software that they have no experience with.
I beg to differ after searching for and reading the original article. The synopsis here implies only “user-mode processes including those of web browsers or Adobe Reader” and the browser that is used to check for the vulnerability may be affected.
As well, the news comes from September when all of the referenced AV software in the article patched the products in question.
By comparing the written brief here with the original Ensilo information, one discovers that any number of programs on a computer may be vulnerable, and the “tool” does nothing to identify which program may be vulnerable, only that one out of, perhaps, 90, could be compromising the security of a Windows system.
What then should a reader do who discovers his/her system is vulnerable? There’s no mention of steps to take. All great information, Martin, but . . . it’s like telling someone to use a thermometer to check for fever. Say the “someone” has a fever.
Next?
“There is little that you can do about it.”
Pointless diatribe?
File blocked by 360 Total Security.
Panda neutralized the executable on Firefox 42 as suspicious. I’m thinking this is a good thing?
Like Mike O says, not working with Pale Moon. Program just closed on me. Using Win 7
AVulnerabilityChecker would not work with Palemoon. It indicates no browser found. I then tried IE and the program ran correctly.
Tried it and my system is not vulnerable. Using Kaspersky Internet Security 16
Bitdefender Internet Security 2016 Build 20.0.24.1290 is VULNERABLE with Windows 10.0.10586.17 & Google Chrome 47.0.2526.80 m