At least 1% of the Top 10000 websites use fingerprinting to track users
Computer users are exposed to a variety of tracking technologies when they browse the Internet. From traditional third party tracking cookies to local storage, Flash cookies and fingerprinting.
Companies that develop browsers aim to reduce the tracking their users are exposed to on the Internet, for instance by implementing Do Not Track options or changing the way third party cookies are handled.
While that takes care of some forms of tracking, it does not touch others.
Fingerprinting became a topic back in 2010 when the EFF released an online tool to compute a browser's fingerprint. It was a first attempt to demonstrate that fingerprinting could indeed be used to track users on the Internet.
While it was common knowledge that fingerprinting was used, it was not really clear how popular it really was.
Fingerprinting study
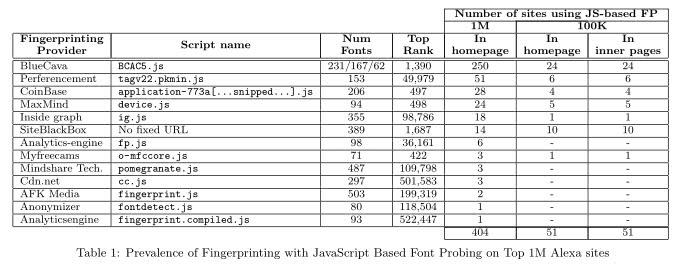
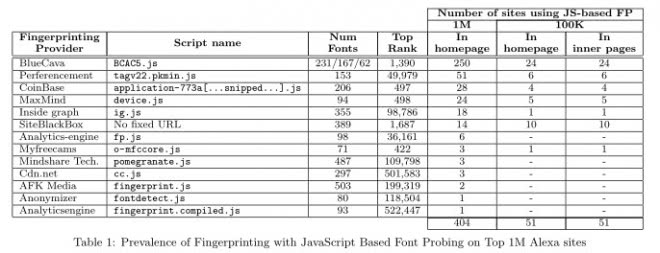
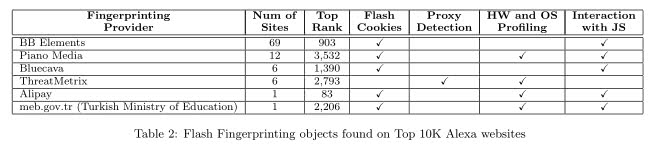
A recent study suggests that at least 1% of the top 10000 websites use fingerprinting techniques to track users. The researchers used the rankings provided by Alexa, an Amazon company, for their study.
They identified four different fingerprinting technologies: JavaScript-based, Plugin-based, Extension-based and Header-based & Server-side.
All have in common that they extract data either directly during connection attempts or afterwards by parsing log files to identify unique data sets that can be associated to single Internet users.
Information are exchanged with web hosts whenever users connect to servers or Internet websites. In addition to the standard exchange of data, additional queries can be made by using technologies such as JavaScript or Adobe Flash.
It is for instance possible to retrieve the list of installed fonts, the screen size or the installed plugins from a user system.
The program the researchers used crawled the top 1 million websites according to Alexa to determine if common fingerprinting techniques were used by the sites.
While at least 1% of the top 10,000 sites have been found to use fingerprinting tracking, only 404 of the top 1 million sites according to Alexa were found to use fingerprinting.
It needs to be noted at this point in time that it is quite possible that the actual number is larger than that. First, the developers were not able to determine whether server-side fingerprinting tracking was used by a website. Second, there is no common fingerprinting standard, which means that it is possible that attempts were not detected correctly.
One interesting result is a list of fingerprinting providers that the researchers discovered.
The research paper lists detailed information about the methodology used to crawl the sites, counter-measures, and other information that you may find useful.
The script used to crawl the sites will be published in the future on the website linked above. This is also the location where the research paper can be downloaded as a pdf document.
Now Read: How to modify your browser’s fingerprint so that it is no longer unique
Advertisement















Ghostery currently does not block finger printing, but they have it logged under considerations. So at least it is on their radar somewhat.
Given that the EFF study went “viral” in 2010, it’s astounding that this has only just emerged and that it’s a mere 1% of the top 10,000 sites. I suspect that it’s probably a lot more and if it isn’t now, give it a week or two and it will be!
The issue is there’s a reason for tweaking the preferences/plugins/etc. Can’t they be spoofed? i.e report to websites plugins as enabled when they are disabled? Can/could the same principles be applied to the other forms of fingerprinting?
Where can I find list of websites that use fingerprinting?
They have not published the list of websites.
Technitium MAC Address Changer will solve a few of them some other tricks on hand is to use a websitesniffer and see what files the site generates and then blocking the actual creation of theses files or do like I do run the stuff on a crypted ramdrive with random size now this truly (excuse the expression) screws the system over. But nothing is perfect and having a nuclear explosion for a magnetic pulse well the hard drive will be wiped clean but so will the rest of it ;-)
I usualy bitch at any add that repeats itself in a awkward way from one site to another… needless to say they must be tracking nicely because I usualy get more and more 404 errors on the actual ads xD