Anti-Bot protects you from visiting bot spreading websites
Depending on the web browser you use, its version, settings, extensions and plugins installed, it is sometimes enough to visit a website to become a victim of a successful malware attack. There are a couple of things that you can do to protect your system and yourself, including making sure that everything is always up to date and that you have at least one security suite installed on your system that may catch the attack before it is executed successfully.
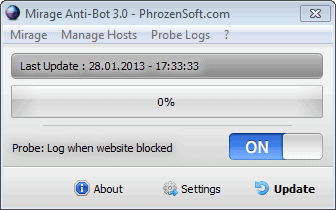
Mirage Anti-Bot is a free program for the Windows operating system that will add a blacklist of websites, domains and IP addresses to the Windows hosts file to block connection attempts to these sites automatically when they occur.
The program uses information provided by abuse.ch which maintains a database of known malware related websites. It should be clear that the protection is not 100% as the list does not contain all known or future malware domains and sites yet. It does however take care of popular sites used to spread malware.
If you are using a service to automatically blacklist sites using the hosts file, you may want to check if abuse.ch is already included. If that is the cause, there is not really a need to run Anti-Bot in addition to the other program. If you do not use any program yet, Anti-Bot may be a good start.
To add information to the hosts file install Anti-Bot on your system, run it with administrative privileges - and not after installation using the check box - and click on the update button to download the latest site list and update the hosts file with it.
You can check if the hosts file has been edited by opening C:\Windows\System32\drivers\etc\hosts in a plain text editor such as Notepad. All domains are redirected to 127.0.0.1.
You can exit the program afterwards as it is only needed to update the hosts file. You may want to run it regularly though to work with the latest data set.
I recommend you enable the logging of connection attempts to sites that are automatically blocked in the program settings.
Verdict
If your resident anti-malware solution does not block bot-related websites then you may want to use the program to add protection to it using your system's hosts file and the abuse.ch block list. While it won't keep everything out, it includes many popular attack domains.




















@Transcontinental, I updated to the Beta version and have no problem now!!!
Thanks,
Panama Patrick
Anti-Bot also protects from the Palevo C&C Domains and, while there is also a dedicated page for Palevo Tracker ( https://palevotracker.abuse.ch/blocklists.php ), unfortunately it seems there is no dedicated HOSTS file. All I found was a domain list ( https://palevotracker.abuse.ch/blocklists.php?download=domainblocklist ) which because of its non HOSTS format cannot be downloaded via HostsMan.
I had to download it apart and add a leading 127.0.0.1 (or 0.0.0.0 or 0) to every line, which is cumbersome even if the list is excessively small (48 entries at this time). I have no idea of the dynamism of this list and, being unable to have it be checked with HostsMan, I’ve set a rule on changedetection.com to alert me if/when the list would change.
@Transcontinental: My Hostman update will not allow any webpages using https: I get an error, when I drop the ‘s’ as http: Hostman accepts that webpage but when downloading the Host file from those locations get error message …failed . failed.
Any ideas as to why https: is not allowed?
Patrick
Patrick, I have no idea at this time why HostsMan on your system refuses above mentioned https urls. I have both links accepted here.
When you added those https in HostsMan’s ‘Manage Update Sources’, have you checked the link via ‘Edit…’ and ‘Test Connection/Test’ ? It should work for https and refuse http, bacause the page is https only …
I’ll think about it. This is odd. If anyone has an idea …
@Patrick, maybe is the issue related to HostsMan v3.2.73 ? I am running HostsMan 4.0.88 Beta 9, though the latest beta is HostsMan 4.0.90 Beta 10 (but I dislike latest output).
HostsMan 4.0.88 Beta 9 is really keen, much faster than v. 3.2.73. I’m not a beta fanatic but moods are made to be trespassed sometimes, here I think is a valid opportunity, IMO.
Perhaps will the https issue be resolved with 4.88.9 or 4.0.90 Beta 10.
@Transcontinental: I hit the edit button and got the message: a big red X Protocol (:https” not supported.
I am using HostsMan v3.2.73 (latest stable)
if I take the ‘s’ out of the https then it passes Edit test but when updating I get the following:
– SpyEye Tracker blocklist… check failed.
Strange, anyone can help?
I read that having a large hosts file could significantly degrade network performance because the system scans the hosts file during each transaction. Is that true?
I’ve been told large HOSTS file issues could occur when the DNS Client service was running. I’ve set this service to disabled 10 years ago and never had to switch it back on. Never understood the pertinence of that service …
Otherwise, depends what “large” is. I have a 60,000 items’ HOSTS file, but I don’t know how things would run with 10x more. I think that the DNS Client Service closed should prevail in demonstrating that the issue is the port rather than the file size….
maybe someone “not so lazy” instruct us how to add to HostsMan those 3 blocklist from abuse.ch (ZeuS, SpyEye, Palevo – which links) and if it is redundant having Malaware domain list .
If you’re managing a HOSTS file by yourself and/or use HostsMan as it’s manager application, following links for direct download (works fine in HostsMan’s source ) :
SpyEye Tracker blocklist : https://spyeyetracker.abuse.ch/blocklist.php?download=hostfile
ZeuS Tracker blocklist : https://zeustracker.abuse.ch/blocklist.php?download=hostfile
More info for tracking lists :
SpyEye Tracker : https://spyeyetracker.abuse.ch/blocklist.php
ZeuS Tracker : https://zeustracker.abuse.ch/blocklist.php
Thanks, great info.
I quit using HostsMan because of problems but I see Two whole years later, it’s
finally been updated. Thanks.
Spybot search and destroy does this too
And for the lazy who want the MVPS hosts file and others as well, Abelhadigital’s Hostsman does great job. http://www.abelhadigital.com/hostsman
For the not-so-lazy:
winhelp2002.mvps.org/hosts.htm
There does not seem to be any way to download the Mirage Anti-Bot software. Can’t get past this page http://phrozensoft.com/processdl_21.ps …there’s no download button or link, etc.
Is it just me? I tried the page in 3 different browsers.
I had no issues with the latest version of Firefox after I did enable JavaScript.
Oh. Thank you.