BlackBox Security Monitor, Monitor Computer Systems In A Network
Monitoring other computer systems in a local area network is always a delicate matter. Those administrators who understand the risks, both legal and technical, associated with monitoring other systems might find BlackBox Security Monitor useful in this regard. The free software program is available for download after a short registration process on the developer's website.
The monitoring software combines monitoring of various PC activities, reports and an alerts and warnings system under its hood. It supports monitoring of websites visited, program launches, web searches, emails sent and received, keystrokes, instant messenger chat logs and screen captures of the computer desktop.
- Every Program launched: when program was started/ended, what is the program name, what is the text in program title;
- Every Web site visited: the web site address, when it was, even the IP address;
- All Web Searches: what was this search for;
- Computer usage time;
- All E-Mails sent and received;
- All Web Mails sent and received on HotMail/LiveMail, YahooMail, Google GMail, AOL Web Mail;
- Instant Messengers chat and conversations via Windows Live Messenger, AOL, Yahoo/ICQ, Jabber, etc;
- All keystrokes typed;
- Record screen captures in color and high resolution with highest compression rate available;
- Total network traffic.
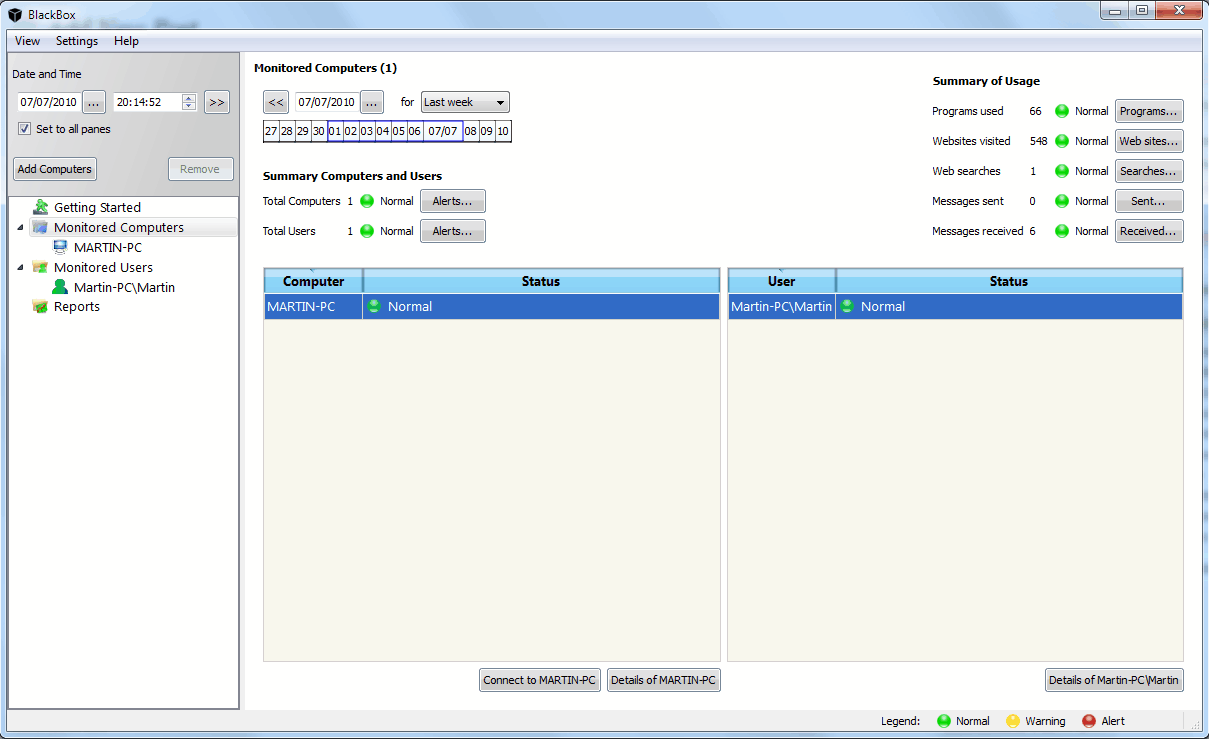
BlackBox Security Monitor displays an add computer wizard on first run which can be used to add the local PC or another PC in the network to the list of monitored systems. The add computer menu is available from the program's main interface at anytime should the need arise to add additional PC systems. It is furthermore possible to monitor all or only specific users of a system.
The program lists all monitored computer systems and users in the left sidebar. Reports and the getting started page are listed there as well. Selecting a user or computer displays the relevant information on the right side.
Both the user and computer listings display the information in a tabbed interface divided into sections like programs, websites or emails. Date and time are presented on the screen with options to take a look at a specific date or time frame to see the activities during that time.
Several reports can be created after clicking on the reports entry in the left sidebar. Among them options to list the most popular websites, programs and web searches.
- User Activity report;
- 10 Most popular programs;
- 10 Most popular Web sites;
- 10 Most popular searches on the Web;
- 10 Most active Instant Messenger users;
- 10 Most active E-Mail users;
- Program launched report;
- Web sites visited report;
- Alerts/Warnings generated report.
Alerts can be configured to instantly notify a user by email or cell phone on specific activities including program launches, web mails or websites visited.
BlackBox Security Monitor offers enterprise grade functionality, currently for free. The program is available for both 32-bit and 64-bit editions of the Microsoft Windows operating system.
Advertisement



















i want to make monotoring security threats on networked computer project so plz help me how to make this software
Thanks!
Nice info.
it doens’t seem to be working on WIndows 7…
I tested it on Windows 7 and it worked fine.