How To Protect USB Sticks And The Data On Them

Carrying an USB-stick around with you can be beneficial in numerous situations. USB devices are for instance ideal to copy data without having to carry a larger device like a notebook or netbook around. They are also ideal for accessing portable programs on third party computer systems; nothing beats working with familiar programs on unfamiliar systems.
But USB devices introduce several security risks that computer users did not have to cope with since the demise of the floppy disk. Programs like USB Dumper can for instance copy all contents of a connected USB-stick directly to the host computer's storage devices without the owner ever knowing that this happened.
But losing confidential data is not the only risk. USB devices can also be targeted by malicious software which use the USB-stick as a host to infect other computer systems it gets connected to.
This article takes a look at some of the options that USB-stick owners have to protect their sticks from those dangers.
Protecting the data on the stick
Data on USB devices can be read by any computer user on any system by default. The data is not protected and all it takes is to connect the stick to access the data on it. This alone can be a problem if the stick is lost or stolen.
While there are USB devices available that support hardware encryption to protect the data, they are not very common.
The only reasonable option is to protect the confidential data on the stick by encrypting it. We have seen other tips in the past that suggested to use the NTFS file system to protect the data from third parties. That tip might work if the third party is using a Windows NT based system, it fails if they are not.
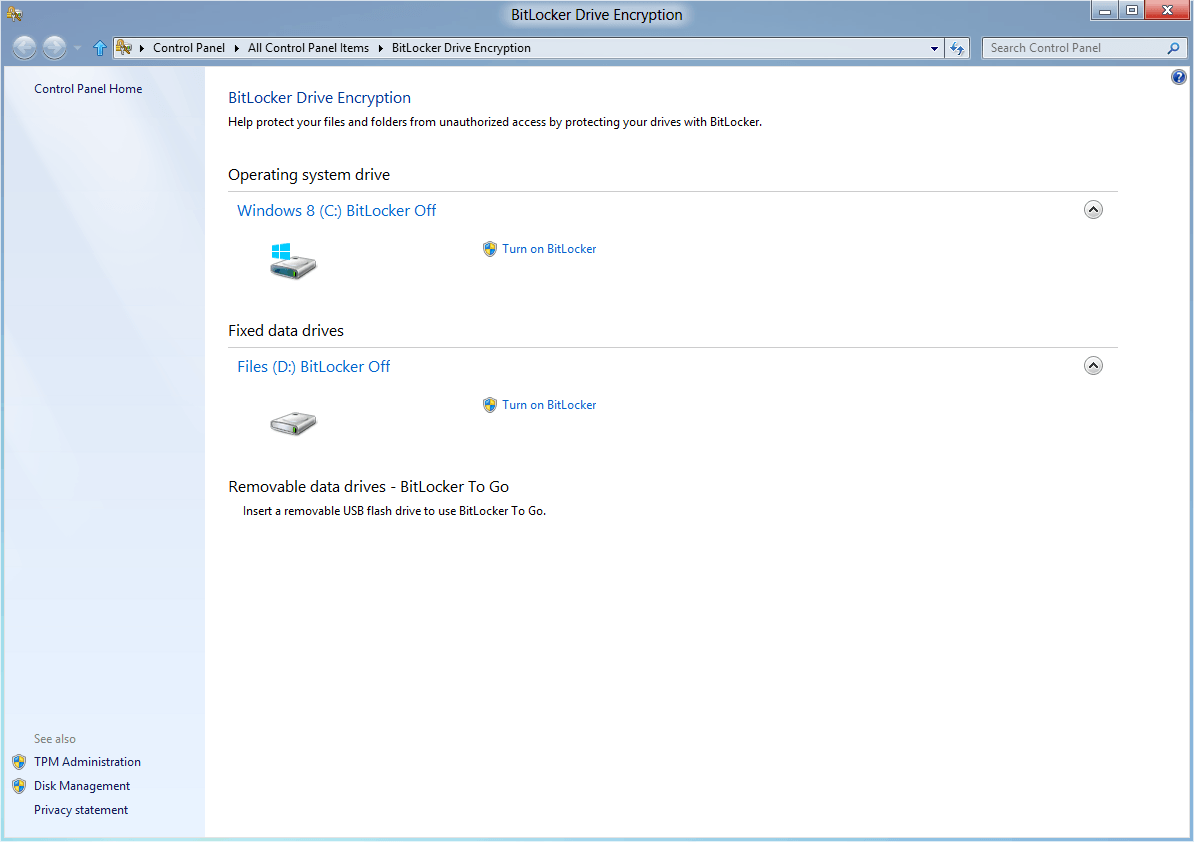
Encryption software like True-Crypt, USB Safeguard, Bitlocker or AxCrypt can be used to protect the data on the stick. It is often not necessary to encrypt the whole storage. True-Crypt can for instance be used to encrypt part of the space on an USB-stick. It creates an encrypted container on the disk which protects files that you save in it so that no one can access the data unless the right master password is entered first.
The disadvantage of True-Crypt is that the encryption software is needed to decrypt the container. AxCrypt on the other hand creates self-extracting encrypted files. This is handy for single files that need to be protected but not a viable option if dozens or hundreds of files need to be protected.
True-Crypt can be installed in traveler mode on the USB stick. Admin rights are still needed to execute the program on other systems though.
All reviewed options until now have been software based. An alternative to that are secure USB devices that use build-in security to protect the stick and data.
All popular manufacturers from Kingston to Corsair offer secure USB devices. The multitude of different security mechanisms and options makes the field quite hard to overlook.
Devices differ in encryption algorithms used, their encryption strength and handling. Some require hardware based authentication on keypads while others are software based solutions that might not be compatible with all operating systems.
Ironkey is a notable exception as it is compatible with Windows, Linux and Mac operating systems. Encryption and decryption is hardware based. The price is however on the upper end of the pricing scale for secure storage devices. The IronKey personal and basic sticks for instance retail for $79 with 1 Gigabyte of storage. Corsair's Padlock offers 8 Gigabytes for $55.
Update: Prices have come down a lot in recent time. Here are a couple of example devices that use hardware encryption:
- Ironkey with 16 Gigabyte of storage (about $70)
- 1 TB external Ironkey drive (about $200)
- Corsair Padlock 32 Gigabyte (about $40)
Both hardware and software based solutions to secure an USB device have advantages and disadvantages. Software based security comes with no additional costs while hardware based devices don't require software at all.
Hardware based solutions are not necessarily more secure than their software counterparts though. It has happened in the past that manufacturers had to recall their products after a flaw had been detected that could be exploited to gain access to the data on the devices.
Securing data with any of the above solutions ensures that data cannot fall into the wrong hands if the device is stolen or if its lost.
Misc Helpful Programs

Another problem that users face from time to time is to forget to disconnect their USB stick from a computer. The data may be encrypted but losing the stick may still mean that a day's work is lost as well.
USB Stick Watcher is a small background application for Windows that will notify the user in regular intervals that the USB stick is still plugged into the computer. It will furthermore display the notifications on shutdown or logoff.
USB Stick Watcher is a useful utility for people, who transfer their data (documents, music and more) across different computers. This will display recurring reminder if your pen drive is still plugged in PC. Also, USB Stick Watcher will show warning message every time when you try to turn PC off, or log off without unplugging your pen drive. USB Stick Watcher will ensure that you never leave your USB Stick plugged in to a computer!
An alternative to this software based solution is to put the usb stick on the same keychain as the car / home keys. People will usually pay more attention to their keys than the USB stick they are working with.
(Download Removed)
USB Write Protector is another interesting free software program. The write protection of USB devices can be enabled with this software. It only works on Windows PCs but is a small portable program that fits perfectly on USB devices of any site.
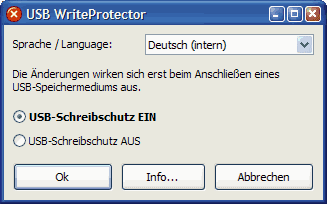
Thumbscrew is an alternative to USB Write Protector. It provides access to the same functionality.
Thumbscrew has a few limitations:
1. I can't guarantee it's 100% forensically sound. Buy a proven USB hardware write blocker if you want to be sure.
2. USB mass storage devices that are already mounted as writeable will stay writeable until they are removed and reinserted. The same applies if you turn off read only protection while a USB mass storage device is active, it will become writable and stay that way until removed and reinserted.
USB devices with hardware write protection switches add an extra layer of security. All software based solutions need to be executed on the host system before they become active which is a problem if malicious software is already active on the host system.
Hardware based write protection ensures that no data is written on the USB stick for as long as the protection is in place. Putting an antivirus solution on the USB stick could for instance be used to scan the host system to ensure it is clean before disabling the write protection on the USB stick.
Are you using USB sticks regularly? Let us know how you protect your sticks in the comments.





















USB sticks can be protected right but they are just like time bombs.And anytime they can crash.I use only safecopy online backup.They are cheaper compeared to any other online backup system.I can now backup all my 2 computers on one account unlike other online backup where one has to pay for each computer.
I’ve moved completely to Dropbox.
Mostly I use 3 different computers of my own, so I don’t have big security issues, and I use the dropbox site if I’m on a different computer (rarely). I only use the usb when I have to move large files.
As a developer, is it possible to modify the usb mass storage driver such that whenever the usb drive is plugged into a computer, certain files ( or partitions) are password protected?
Perhaps windows likes to force the use of a standard mass storage device driver, but just wondering if in theory it’s possible.
Maybe there is a way to do file / folder partition protection within the stack of the usb hardware itself! (If it’s has a Cypress or Microchip controller for example…)
I’ve been rather lazy lately with USB protection, but Rohos Mini Drive may still be my favorite–only 2GB of data with the free version, though. USB Safeguard should suffice for my needs.
http://www.rohos.com/products/rohos-mini-drive/
I picked up my Ironkeys on eBay for about $40 each :)
I’ve been using Ironkeys for years now. It’s pretty good. And if you forgot to click lock data and just pull the stick out – you generally will not have any problem with data corruption as long as you had disabled delayed write in Windows.
The only head ache is that in Windows Vista and 7, you have to run the ironkey program (inside the Ironkey usb itself) in Admin mode.
I never had the need for such a high-priced solution but would probably pick up one of them if I would ever come into a situation where I had to use an USB stick regularly on different computer systems.