How to dump all USB files without the user knowing
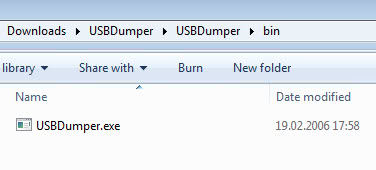
USBdumper runs silently as a background process once started and copies the complete contents of every connected usb device to the system without the knowledge of the user. It creates a directory with the current date and begins the background copying process. The user has no indication that the files stored on the USB device are copied from the USB to the local system.
The only indication to find out is to find the process listed in the Windows Task Manager or a third party process manager, or to accidentally stumble upon the directory the files are copied to.
The program itself is listed in the Task Manager but you would still have to investigate further to find out what it is doing and that requires sophisticated programs that monitor the system so that you can check out all the activities and events that happen on it.
Just imagine this tool running on a public computer with no access to the task manager or a software like Process Explorer. You would not know that the files are copied. What could you do to protect against this program? You could encrypt your data, if you use a tool like True Crypt for example. Even if the files are copied they are useless unless the "attacker" knows your passphrase. That is of course, unless you decide to mount the encrypted container to make the files accessible on the PC.
The files are automatically stored in the directory the program is started in. Depending on the size of the drives that get connected to the PC, enough storage space needs to be available on the drive the program is executed from.
The program can obviously be used for other than malicious purposes, for instance to automatically backup the data on USB flash drives that are connected to the PC without having to worry about that at all.
It has a very low memory threshold and should not have any impact on the performance of the operating system while it is running. While initially designed for Windows XP, it appears to work fine under newer versions of Windows as well.
Advertisement


















Ruchier… Why is the majority of your dump malwares Or Trojans Or spies?
you can access data of password protected PC through USB drive using booytable USB
follow this link
http://hackyogi.com/how-to-boot-system-using-usb-drive/
Sorry that was incomplete pasting.Below is the complete analysis of USBDumper,plz delete my first post and read only this report——————–
File USBDumper.exe received on 2010.03.10 06:10:24 (UTC)
Current status: finished
Result: 37/42 (88.10%)
Compact Compact
Print results Print results
Antivirus Version Last Update Result
a-squared 4.5.0.50 2010.03.10 Riskware.RiskTool.Win32.USBDump.a!IK
AhnLab-V3 5.0.0.2 2010.03.09 Win-Trojan/Usbdump.45056
AntiVir 8.2.1.180 2010.03.09 SPR/Spy.USBDumper.A
Antiy-AVL 2.0.3.7 2010.03.09 RiskTool/Win32.USBDump.gen
Authentium 5.2.0.5 2010.03.10 W32/HackTool.GD
Avast 4.8.1351.0 2010.03.09 Win32:USBDump
Avast5 5.0.332.0 2010.03.09 Win32:USBDump
AVG 9.0.0.787 2010.03.09 PSW.Generic2.OBL
BitDefender 7.2 2010.03.10 Application.Spy.Usbdump.A
CAT-QuickHeal 10.00 2010.03.10 Trojan.Agent.ATV
ClamAV 0.96.0.0-git 2010.03.09 Trojan.Spy.USBDump
Comodo 4091 2010.02.28 UnclassifiedMalware
DrWeb 5.0.1.12222 2010.03.10 Trojan.DownLoad.37552
eSafe 7.0.17.0 2010.03.09 Win32.Spy.BusDmp
eTrust-Vet 35.2.7350 2010.03.10 –
F-Prot 4.5.1.85 2010.03.09 W32/HackTool.GD
F-Secure 9.0.15370.0 2010.03.10 Application.Spy.Usbdump.A
Fortinet 4.0.14.0 2010.03.09 W32/BUSDMP.A!tr
GData 19 2010.03.10 Application.Spy.Usbdump.A
Ikarus T3.1.1.80.0 2010.03.10 not-a-virus:RiskTool.Win32.USBDump.a
Jiangmin 13.0.900 2010.03.10 –
K7AntiVirus 7.10.993 2010.03.09 Non-Virus:RiskTool.Win32.USBDump.a
Kaspersky 7.0.0.125 2010.03.10 not-a-virus:RiskTool.Win32.USBDump.a
McAfee 5915 2010.03.09 Spy-BusDmp
McAfee+Artemis 5915 2010.03.09 Spy-BusDmp
McAfee-GW-Edition 6.8.5 2010.03.10 Riskware.Spy.USBDumper.A
Microsoft 1.5502 2010.03.09 –
NOD32 4930 2010.03.09 a variant of Win32/RiskWare.USBDump.A
Norman 6.04.08 2010.03.09 –
nProtect 2009.1.8.0 2010.03.09 –
Panda 10.0.2.2 2010.03.09 Application/USBDumper.A
PCTools 7.0.3.5 2010.03.09 Trojan-PSW.Gasval
Prevx 3.0 2010.03.10 Medium Risk Malware
Rising 22.38.02.02 2010.03.10 Trojan.Spy.UsbDump.b
Sophos 4.51.0 2010.03.10 USB Dumper
Sunbelt 5811 2010.03.10 Trojan.Win32.Generic!BT
Symantec 20091.2.0.41 2010.03.10 Infostealer.Gasval
TheHacker 6.5.2.0.228 2010.03.10 Trojan/Spy.USBDump.a
TrendMicro 9.120.0.1004 2010.03.10 TROJ_BUSDMP.A
VBA32 3.12.12.2 2010.03.09 Trojan-Spy.Win32.USBDump.a
ViRobot 2010.3.10.2219 2010.03.10 Not_a_virus:RiskTool.USBDump.45056
VirusBuster 5.0.27.0 2010.03.09 RiskTool.USBDump.F
Additional information
File size: 45056 bytes
MD5 : 984dbc9abdf9b3053852331911a2fd81
SHA1 : 0459e1f2c98a3fdb123c908411566a5430508951
SHA256: 19882c712c33ec2e9798fc3a268f10350d1d154bbea2407678c3bd738db47dfa
PEInfo: PE Structure information
( base data )
entrypointaddress.: 0x19CC
timedatestamp…..: 0x43F8A3BA (Sun Feb 19 17:58:34 2006)
machinetype…….: 0x14C (Intel I386)
( 3 sections )
name viradd virsiz rawdsiz ntrpy md5
.text 0x1000 0x529F 0x6000 6.09 25ecc03ea0dd23afdbe831995d7939a3
.rdata 0x7000 0xA8C 0x1000 4.06 04f8ed203500412d24352231a69fed73
.data 0x8000 0x4068 0x3000 0.56 ee46501ef16a84edcc9317615f3cd280
( 2 imports )
> kernel32.dll: CopyFileA, GetLocalTime, FindClose, FindNextFileA, FindFirstFileA, SetStdHandle, GetStringTypeW, GetStringTypeA, LCMapStringW, LCMapStringA, MultiByteToWideChar, SetFilePointer, FlushFileBuffers, LoadLibraryA, GetProcAddress, GetCurrentDirectoryA, GetFullPathNameA, GetDriveTypeA, GetLastError, CreateDirectoryA, GetModuleHandleA, GetStartupInfoA, GetCommandLineA, GetVersion, ExitProcess, HeapAlloc, TerminateProcess, GetCurrentProcess, UnhandledExceptionFilter, GetModuleFileNameA, FreeEnvironmentStringsA, FreeEnvironmentStringsW, WideCharToMultiByte, GetEnvironmentStrings, GetEnvironmentStringsW, SetHandleCount, GetStdHandle, GetFileType, GetEnvironmentVariableA, GetVersionExA, HeapDestroy, HeapCreate, VirtualFree, HeapFree, RtlUnwind, WriteFile, VirtualAlloc, HeapReAlloc, GetCPInfo, GetACP, GetOEMCP, CloseHandle
> user32.dll: DefWindowProcA, wsprintfA, RegisterClassExA, CreateWindowExA, ShowWindow, RegisterDeviceNotificationA, GetMessageA, TranslateMessage, DispatchMessageA
( 0 exports )
TrID : File type identification
Win32 Executable MS Visual C++ (generic) (65.2%)
Win32 Executable Generic (14.7%)
Win32 Dynamic Link Library (generic) (13.1%)
Generic Win/DOS Executable (3.4%)
DOS Executable Generic (3.4%)
ThreatExpert: http://www.threatexpert.com/report.aspx?md5=984dbc9abdf9b3053852331911a2fd81
ssdeep: 384:9PWcaTCSS4cXZLOelasgeP0SYoHKr4esjd/ECehPcfYyO6JO33+3csH7i0Jt1B:9O/CSmXZ5apetxq2Tcdv7HXsO0Jtn
sigcheck: publisher….: n/a
copyright….: n/a
product……: n/a
description..: n/a
original name: n/a
internal name: n/a
file version.: n/a
comments…..: n/a
signers……: –
signing date.: –
verified…..: Unsigned
Prevx Info: http://info.prevx.com/aboutprogramtext.asp?PX5=F52E7D9C000AB040B06100A2497F8200984A3755
PEiD : Armadillo v1.71
CWSandbox: http://research.sunbelt-software.com/partnerresource/MD5.aspx?md5=984dbc9abdf9b3053852331911a2fd81
RDS : NSRL Reference Data Set
–
ATENTION ATTENTION: VirusTotal is a free service offered by Hispasec Sistemas. There are no guarantees about the availability and continuity of this service. Although the detection rate afforded by the use of multiple antivirus engines is far superior to that offered by just one product, these results DO NOT guarantee the harmlessness of a file. Currently, there is not any solution that offers a 100% effectiveness rate for detecting viruses and malware.
Well the program has all the traits of a malicious program but that does not make it malicious by default.
Welll there are similar versions here as well as some that do a whole lot more damage:
http://www.usbhacks.com
HI
do any of you know if there is a new version USBdumper program out there???,- the first version does not work any more once you update your antivirus program! It just delete the USBdumper.exe from your devise! If any of you know please post it here
thank you
Ike
Right Chris this would work at home but not on public terminals. The keyfile would be stored on the stick as well.
True, but you better have alot of files on the stick so they can’t figure out which one you used! Better yet, do private things in private!
Here is the original source of the video and more info/links etc:
http://www.watchyourend.com/2006/09/15/usbdumper-endpoint-security-hack-video-demonstration/
Quasimodo has a good point =]
Simple lesson:
Don’t use public computers for personal things.
Ever.
Right Chris this would work at home but not on public terminals. The keyfile would be stored on the stick as well.
But true crypt allows you to use keyfiles, so If they have the password but not the keyfile it would be useless for them!
tash that is true of course. If a keylogger is running as well and the encrypted files are accessed the “hacker” will have everything he needs.
Remember that some usb devices don’t have leds, especially those small ones that are plugged into a port on the back..
If you want 100% security don’t use them at computers that you can’t check. Buy a second one with unimportant data only and use that one on public terminals.
Interesting.. Though if someone has a number of large files on their usb drive, they might notice the led on it being in use more than it should be. And the thing about truecrypt or any encryption; if someones willing to copy all your files, they can easily run a keylogger with it.. The encryption becomes useless(assuming you accessed the encrypted files.. if you don’t type your password, you’re still safe)