Securing your PC with True Crypt
Only a few days ago I published an article about true crypt and recommended it. Back then I bought a usb 2.0 hard drive with 300 GB capacity and encrypted its entire partition with the data encryption software. This was done to test the programs functionality but also to see if it would slow down my main computer (athlon 64 3000+, 1 gb ram) or file operations.
To my great surprise it did not slow down the PC and I decided to expand the encryption to cover all of my computer's hard drives. Let me tell you why and how I did this and why you should also be considering this.
Why?
The first question that comes to my mind and probably yours as well is: Why would someone want to encrypt the hard drives / part of the hard drives? (note you can also encrypt other storage devices like usb sticks)
There are numerous reasons for this. It can be as profane as to hide your daily dose of naked ladies from your wife, hide personal information from other people who might have access to your PC or encrypt your files on a removable storage device for transportation to prevent that the files can be accessed when the device is stolen.
Now what?
Now, why encrypt the whole drive(s) and not just a small part of it?
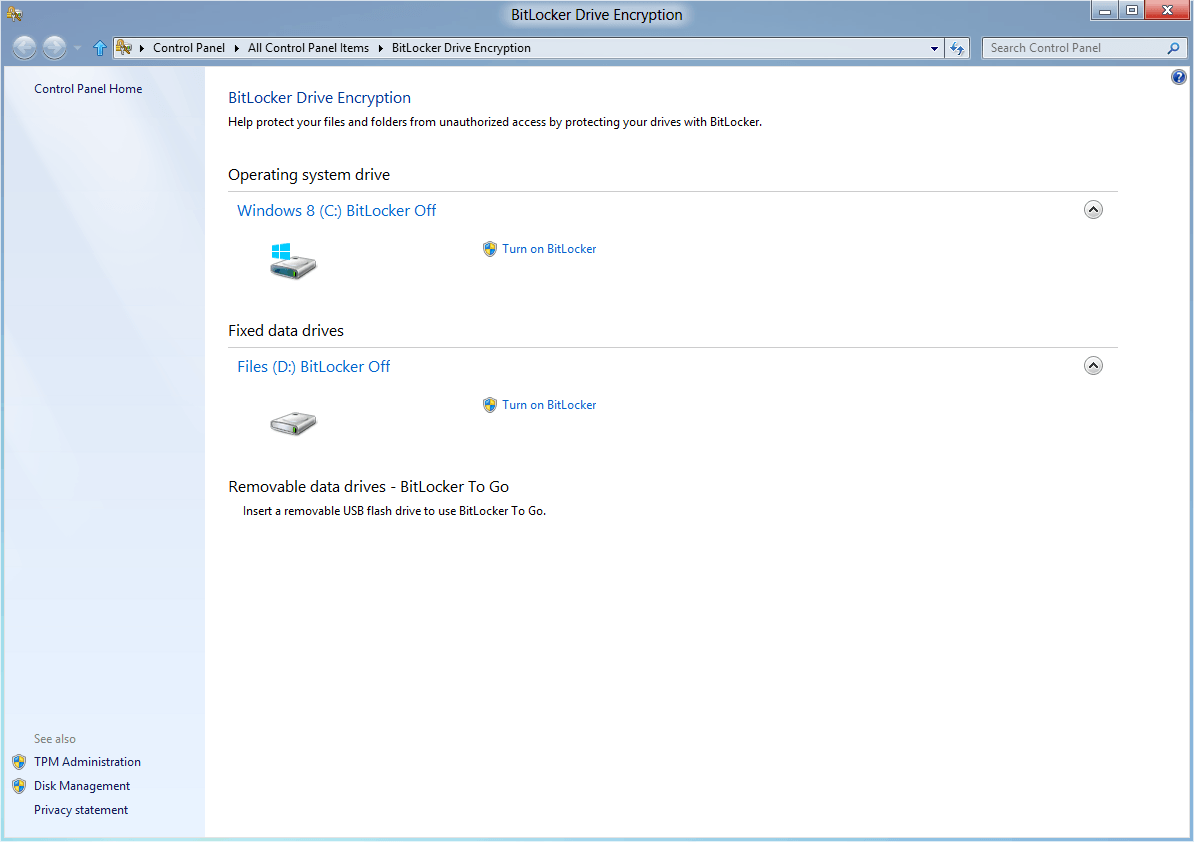
This is a good questions and I have to answer it to some lengths. Let me first tell you that true crypt is not able to encrypt an operating system and boot from it at the same time. That means either you use a second unencrypted operating system or move all sensible user data to the encrypted partitions. (Update: The most recent version of True Crypt can encrypt the operating system partition as well)
As I said earlier I only encrypted the removable usb hard drive before. All my tools that I've been using daily are still on the unencrypted internal drive. Guess what happens when I open Open Office and load a document from the encrypted drive?
It leaves traces. Last used files are normally shown, it probably gets cached in windows cache as well. That means, although the file itself is encrypted the possibility exists that it can still be accessed by other means. There are lots of scenarios like this, a browser caches the pages you visit, a media player keeps records of last played files aso.
Wouldn't it be much securer if those tools are also stored on an encrypted disk?
The setup:
I decided to do the following. I already have a partition for the operating system. All other partitions will be encrypted. The user data from the operating system resides on an encrypted disk, as does the pagefile and all other caching related locations like the browser cache.
On a side note:, one could also install a clean operating system on that partition and use vmware to install another operating system on encrypted drives. BartPE is another possibility. The operating system is stored on a read only device then so that it cannot record information about files that you access nor cache them.
All my tools reside on the encrypted drives, making it impossible for someone else to access them. (unless one would keep the PC running when leaving..)
How to:
I suppose you already are using your drives. True Crypt will erase all data on a partition if its applied to it. Therefore you should move or backup your files before you start this process. (Update: True Crypt can now encrypt partitions without deleting the data on them)
Download true crypt and install the program. Download the true crypt user manual as well. Then backup / move your files if you have not done so already.
Start True Crypt and select Create Volume. You have the choice of creating a standard or a hidden True Crypt Volume. The difference between the two is the following. A hidden volume has its own pass phrase and always resides inside a standard volume. If someone forces you to reveal the pass phrase you provide the one for the standard volume. Its impossible to say if a hidden volume exists even if the standard volume has been mounted (True Crypt partitions are always filled with random data and one can't therefore analyze the data to find out about hidden volumes).
Select standard partition now and in the next window you have the option to store the encrypted data in a file or encrypt a whole device. We want to encrypt a complete hard drive, select device and chose your hard drive that you want encrypted.
Encryption Options:
You have to select an encryption algorithm and a Hash Algorithm now. I don't want to recommend one to you but as of now none has been officially cracked. Some people are discussing their choices on the official true crypt forum, if you are unsure you might want to go there. You can also use Wikipedia for more information. (Blowfish information in this example)
Make sure that in the next step the whole hard disk space will be encrypted.
Selecting a password:
You will have to select a password which you will have to enter every time you want to mount your encrypted drive. Recommendations are that yours should be 20+ chars that consist of a mixture of upper- and lowercase, special chars and numbers. Its hard to remember at first but it will become easier over time. Its suggested that you do not write it down but that's up to you..
Volume Format:
Move the mouse around for 30+ seconds, select a file system (ntfs for Windows xp recommended), leave cluster size at default and click format afterwards. The whole partition will be formatted and encrypted, all data that is left on the device will be lost forever. Make sure there is none that you still need left.
Mounting:
You have to mount an encrypted partition to make the files it contains available. Chose Select Device in the main menu of True Crypt and pick the encrypted drive. Then click on mount and enter your pass phrase. If its correct the drive will appear and you can fill it with data.
The drive letter remains the same as before, so there should not be any problems with broken program links or the like.
Final Words:
Depending on your choices in regards to an unencrypted operating system, BartPE or VMware you need to make sure that all personal data and caches are stored on the encrypted partition. I strongly suggest you use one of the latter for the best security.
If you encounter errors I suggest you visit the true crypt forum which is well visited and contains lots of valuable topics of users that had problems with the tool.
I for myself decided to give BartPE a go and forget about the idea to have the operating system on the unencrypted partition. This saves a lot of the hassle of moving all cache and personal data locations to ones on the encrypted drive.
Advertisement


















I found a solution called WitchFile ( http://www.witchfile.com )
how about WitchFile ?
So you create a Truecrypt volume container (say J: drive) with a specified size, say 5gb.
And you save some files onto this volume like you would a normal hard drive.
After your done, you dismount. But then you accidently delete the volume container,
do you then loose all the data in that container? I mean Truecrypt is good for hiding and encrypting data, yes,
but if it can be deleted so easily (when dismounted), what’s the point, there’s no benefit.
I was searching for encryption solution where i found relatively simple solution which is the data encryption software called TrueCrypt. There is lots of software available, but TrueCrypt is Free, comprehensive, multi-platform and easy to use. but backup with TrueCrypt is not good idea so for backup there you better use Norton Ghost. Where TrueCrypt provides truly encryption solution so for more details see http://www.techarena.in/guide/12587-truecrypt-freeware-encryption-program.htm
Good information.. Thanks
I will give it a try
Chill the fuk out, wtf is this an english class? who gives a shit about some grammar errors…Get the mouse out of your asses
I agree, TrueCrypt is an amazing tool that other than the simple fact of leaving some traces behind, is nearly impossible to crack. Considering 64bit and 128bit encryptions take a few days to a few weeks to crack(depending on your system). A 256 could take years, but TrueCrypt uses 3 separate 256bit algorithms. Even with Government super computers it would be beyond anybody’s lifetime before it get’s cracked. Just be careful because a lot of standard programs cache files you’ve visited negating the purpose of an encrypted file
TrueCrypt 6.0 now allows full-disk encryption, so you can encrypt the whole operating system in its entirety.
AJ Hall, you need to download a tool called: Tweak UI. That will allow you to hide specific drives.
I’ve been using TrueCrypt for 2 years now. Best encryption utility I’ve found so far. Used it on Windows so far, am about to try it on Linux.
Hey, I’ve been using Truecrypt for years now and find it invaluable to the protection of valuable software. And am still facinated by the mounting of hidden and encrypted devices. I was wondering though if one chooses to format the entire drive, windows recognises this drive as unformatted and requests you to format it if you ever select the device. Is there any way of hiding your drive completly from windows and having only truecrypt recognise it?
I have a 160 Gb external HD used only for storage on the go – 10 gb primary partition and 150 Gb extended partition. If found that I had to change extended partition to primary partition so that TrueCrypt can format the device (150Gb partition) as NTFS. Otherwise, it can only format the extended partition as FAT.
Why is that? Curious.
Thanks for the interesting and helpful article. I guess I’ll be trying TrueCrypt very soon. I see you’ve learned that you will meet all kinds when you take on a project such as this. Never mind the clowns who haven’t yet figured out that it’s much harder to learn a foreign language than to learn manners and proper decorum. (Apparently they failed that manners course, too). You do much better in English than I would do if I tried writing this in your native language.
nice article but it is difficult to take you seriously or even finish reading this page with your poor spelling and grammar….use your computer to help with this basic task….and then attempt to educate us on how to encrypt our hard drives…..
Wow, what a rude little bitch you are! Enjoy hell!
i want to install this software to try it
Excellent article. Thanks for sharing.
To the people who find fault with the spelling or grammar, I say get a grip! Not everyone in the world has English as their first language (though it tends to be used on Web pages disproportionately) and one must understand the value of getting something valuable for essentially no cost. If you pay for it then you have a right to complain, if not I suggest you offer helpful advice rather than criticism.
Thank you Martin for your article. It was most helpful.
The strange thing is, I´am using Internet Explorer 6 to check if the site displays fine with this browser and the links are clearly visible for me..
hm, anyone with very good css knowledge who would be able to assist ?
You need to check how the links in the article look in Internet Explorer 6. The links look like normal text. In Firefox they’re displayed ok.
It is spelled “TrueCrypt” not “True Crypt” ;-)
The link to truecrypt.org in the article is displayed as normal text in Internet Explorer 6. In In Firefox it is ok. Looks like broken markup.
1. I´am not a native speaker, if you find errors tell me and I will correct them.
2. My partition was 5 gigs, about 3 have been used with the pagefile on another drive
3. Use http://www.truecrypt.org , which browser are you using ?
4. thanks a lot for your comment ;)
Thank you. This is the software i’ve been looking for..
–budiw
The link to the TrueCrypt website is not visible.
Hey, I’ve been toying with this tool for quite awhile now, and its pretty slick. Thanks for sharing your experience, I will probably be doing just this on my laptop. Do you have any recomendations for OS partition sizes using windowsXP if I’m going to have my OS on an unsecured partition? Thanks!
nice article but it is difficult to take you seriously or even finish reading this page with your poor spelling and grammar….use your computer to help with this basic task….and then attempt to educate us on how to encrypt our hard drives…..