
It's not been a good few weeks for technology companies with all manner of high-profile hackings being reported, not just on technology websites such as gHacks, but worldwide on the early evening […]
One thing that's been annoying YouTube users for quite some time is the subscriptions bar that may be automatically displayed at the bottom of the screen. Many users refer to it as […]
I like my web browser UI as compact as possible. To achieve that I have no problem of getting rid of some of the lesser used interface elements. Basic examples are compacting […]

It happens that I get tired in the late afternoons, so tired in fact that I'm hard pressed not to go to bed directly to sleep the sleep of the brave. This […]
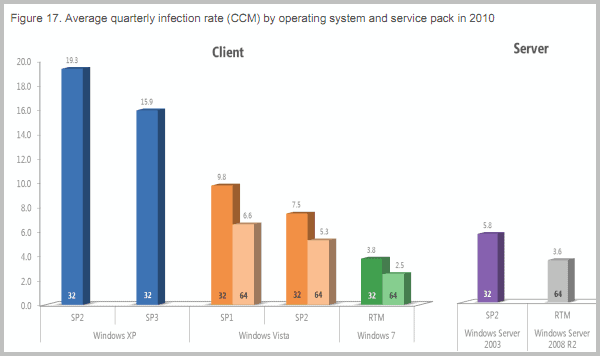
If you were looking for a reason to make the switch to Windows 7, you may have found it in form of Microsoft's latest Security Intelligence Report. The document, available for public […]

So the Chromebook has finally been announced, and first models will ship on June 15 in select countries (US and several European countries). Both Acer and Samsung have revealed some of the […]
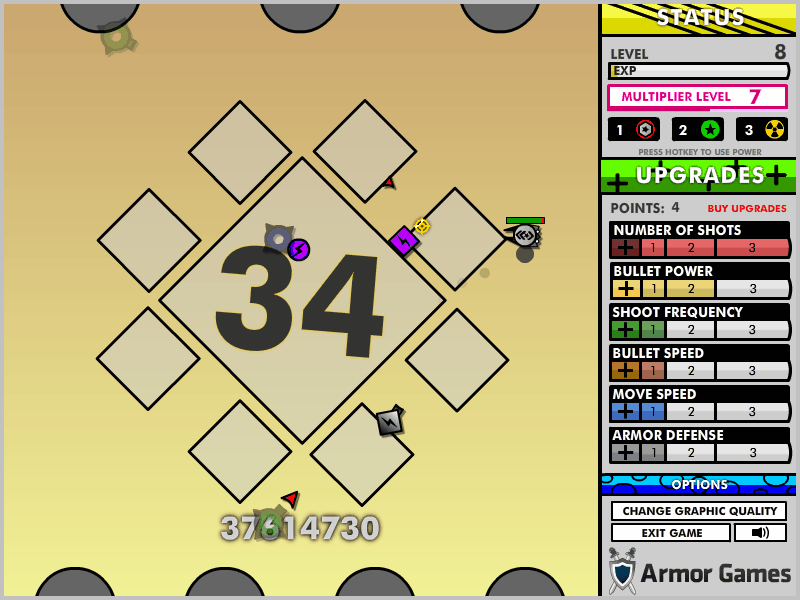
Diepix Arena 2 is a shoot'em up browser game featuring incredible music and fast paced action. You take control of a ship that you move with the WASD keys. You shoot with […]

Didn’t I write recently on Facebook's general lack of privacy, intentional or otherwise? How ironic is it then that Facebook chose to attack Google on its general disrespect for personal data privacy? […]
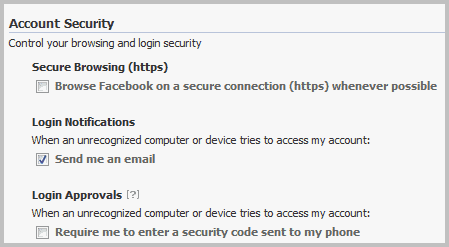
Facebook began to roll out a two-factor authentication system designed to protect user accounts from unauthorized access in 2011. Two-Factor authentication is designed to add a second layer of authentication to the […]
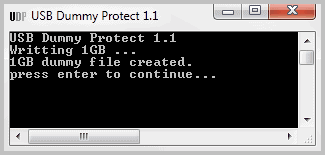
Question: How can you protect USB devices like sticks or drives from being infected with computer viruses? Some users are lucky enough to have USB devices that have write protection switches, just […]

Firefox keeps track of all websites that you open in the web browser. It stores those information in a global history and makes individual histories for each tab that you have open […]
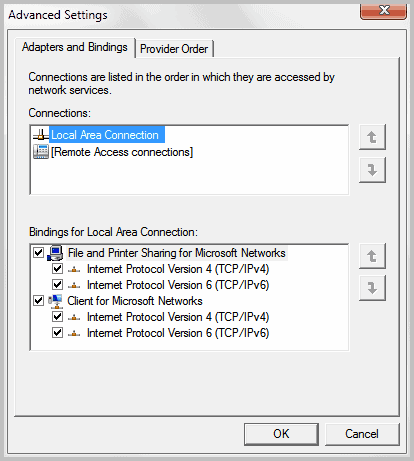
A computer running Windows 7 may connect to networks with various adapters. Probably the most common example is a notebook or mobile device that can connect to the Internet via a wireless […]
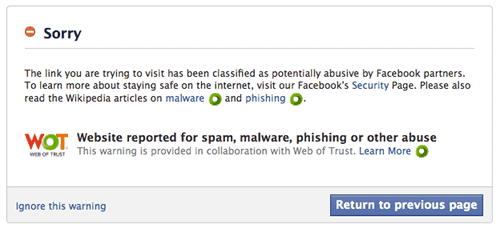
Web of Trust is a community driven website reputation service. It is available as a look-up service on the company website, and as an automated software for various web browsers. The service […]

Google has just released an update for the stable branch of Google Chrome that brings the version of the web browser to 11.0.696.68. The update, which is available for Microsoft Windows, Apple […]
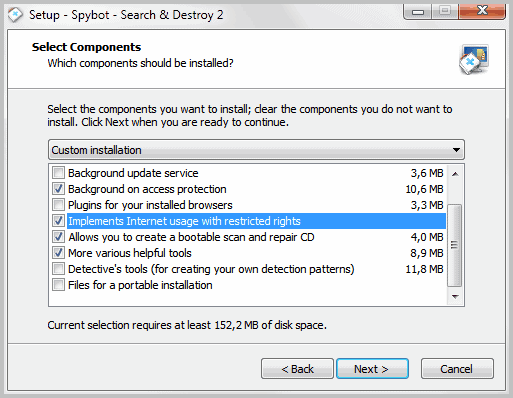
The developers of the popular antispyware scanner and cleaner Spybot-Search & Destroy have released a first public beta version of the soon to be released version 2.0 of the application. You will […]
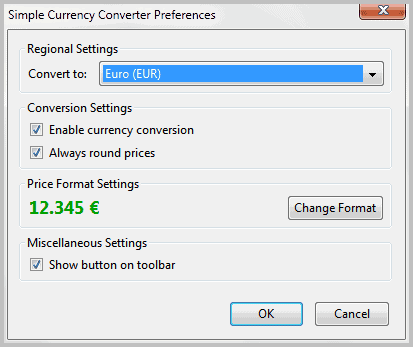
The Internet offers global shopping opportunities. I can buy items in England, the United States, Japan or any other country of this world. One problem that international shoppers may run into regularly […]

In Building A Custom PC 2011 Part 1: The Assessment I mentioned what I'd needed in a new Pc that I was about to build. I have mentioned my expectations and other […]
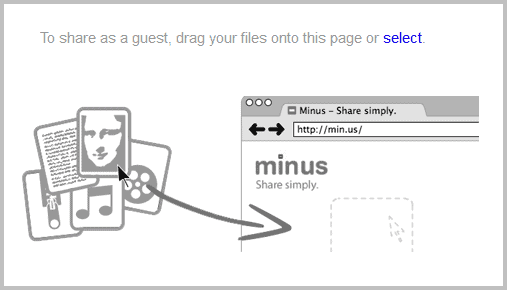
Which web service or program are you using if you need to send a friend, business partner or your mom a file? The majority of you will likely answer that they use […]
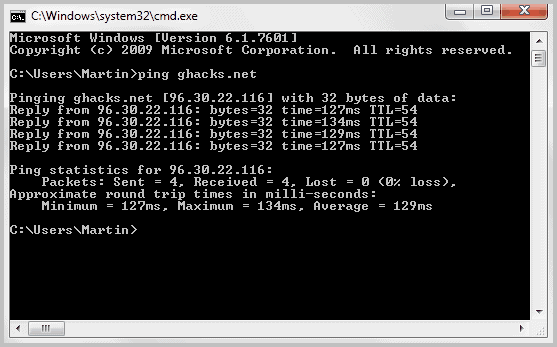
This article is the first in a series delving into the basics of network troubleshooting. It covers what tools to use and how to use them. While this is a basic tutorial, […]
When it comes to security on the Internet, it can be extremely complicated for end-users to find out who is telling the truth, who is not and who is bending it. Two […]
I use online file viewers for two core reasons. First, they allow me to view files even if the computer system I'm working on has no compatible viewer installed, and second, they […]

Security has been one of the top topics of the last 30 days. We have had the Last Pass incident and the Sony PSN hack. Both incidents demonstrated that your data may […]
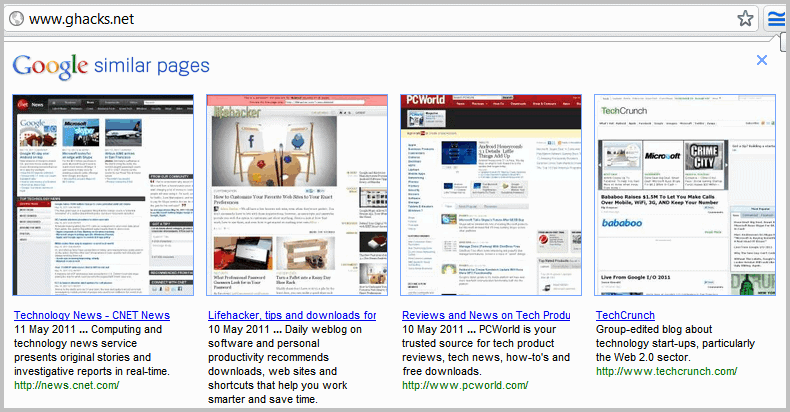
Unless you are running the new experimental search interface on Google, you can make use of a feature called similar pages directly on the search results page. This feature displays a list […]
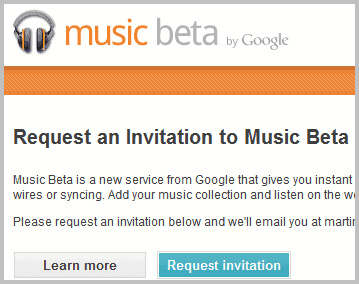
Google yesterday announced the immediate availability of Music Beta, a new cloud based music service that shows many parallels to Amazon's Cloud Drive service that has been rolled out earlier this year. […]

There have been two recent advancements in technology that will make it easier for manufacturers to put a lot more punch in smaller packages. Intel released news about a new 3d transistor […]

Microsoft released two security bulletins on this month's patch day. Every second Tuesday of a month is so called patch day at Microsoft where a number of security related updates are released. […]

Microsoft is buying Skype for $8.5 billion Dollars, that's the big news today. This deal brings up lots of questions. Did Microsoft overpay for Skype? The current owners have bought Skype one […]
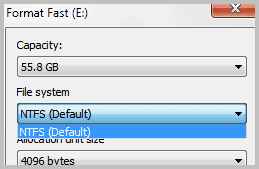
It is usually recommended to format hard drive to NTFS in Windows as the file system offers several advantages over its alternative, Fat32. Sometimes however you may need to format a drive […]
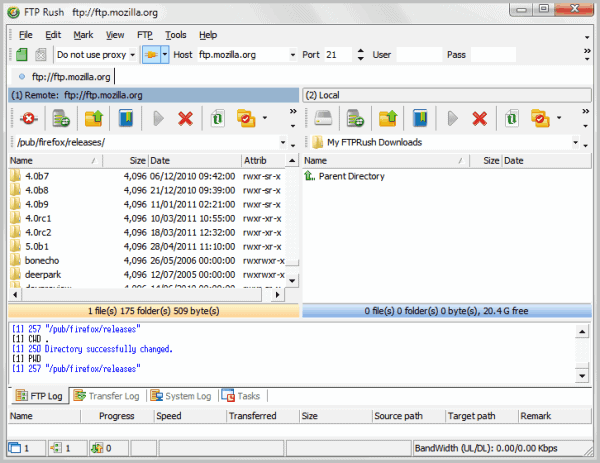
I'm using WinSCP to transfer files from and to my web servers. The free sftp client offers everything that I could possibly need, and has never let me down. Not everyone likes […]
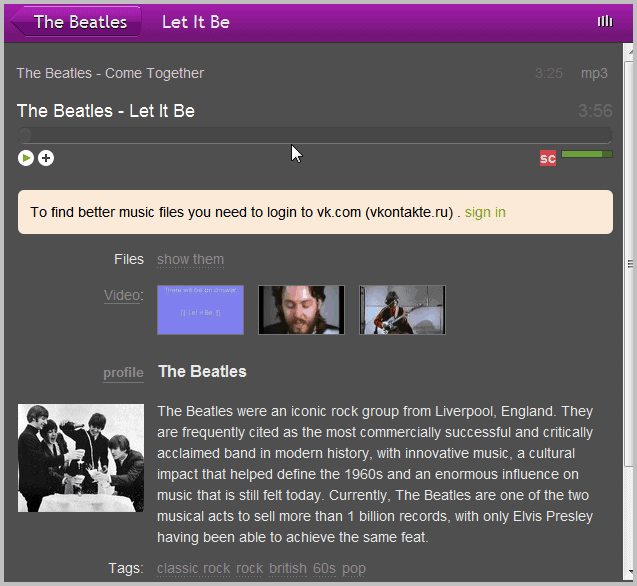
Seesu is a small software for various browsers that combines the vast Last.fm music library and database with mp3 libraries on VKontakte and Soundcloud. At its core, Seesu is a music player […]
The cloud has been rather rainy, lately. Sony has had a rough month, to say the least. They’ve been hacked and info has been stolen. At the time of writing PSN has […]

Two of the core reasons for installing Google Chrome are the browser's speed and security. Especially the latter with its sandboxing approach proved to be very effective against many common attack forms […]
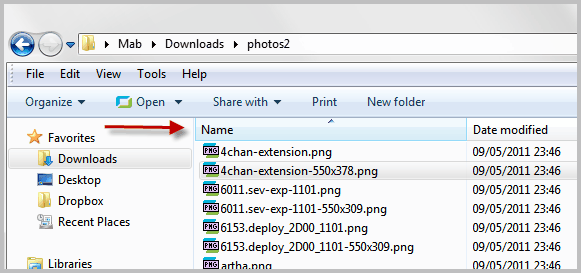
Files and folders can be viewed in various view modes in Windows Explorer. From extra large icons over details and lists to the extended view mode. If you pay attention to the […]
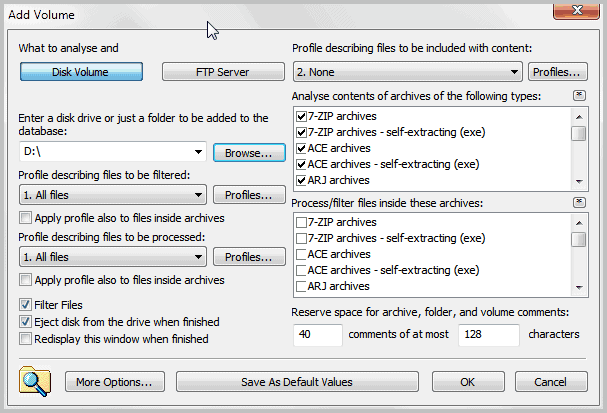
Disk Explorer Professional is a free disk cataloging software for Windows. You can use it to catalog a wide variety of devices, from internal hard drives over CDs, DVDs and other optical […]
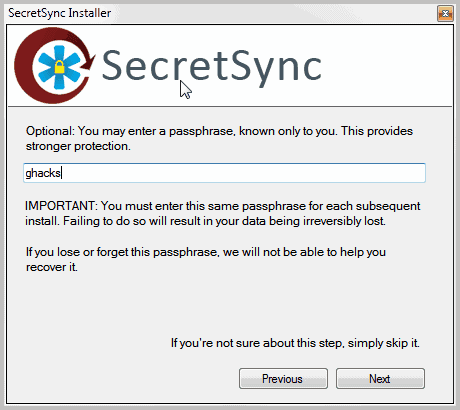
The popular file synchronization and hosting service Dropbox encrypts all uploaded files and folders automatically to protect network snooping and other forms of attack and unauthorized access to those files. Dropbox recently […]
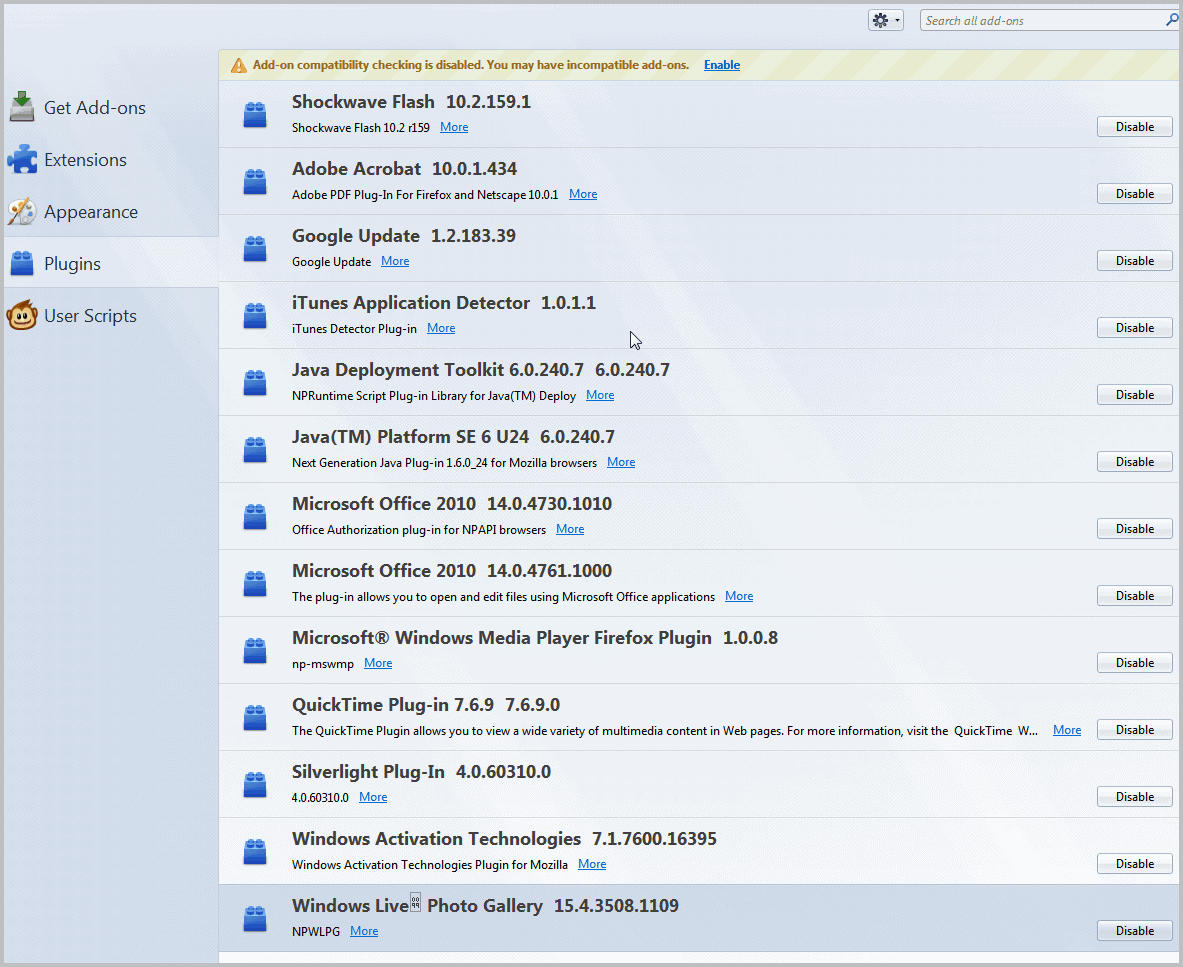
When I look under plugins in the Firefox add-on manager I notice many plugins there that I never use. Among them illustrious plugins like Google Update, iTunes Application detector, Microsoft Office 2010, […]
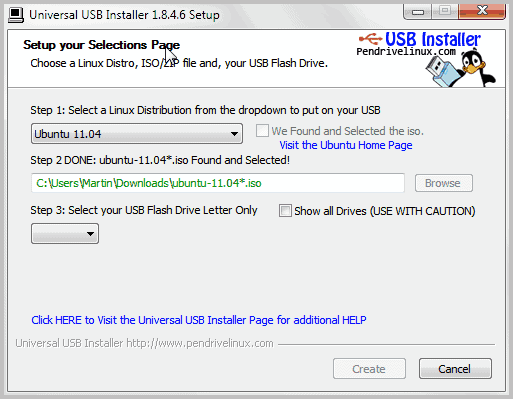
I just got the replacement battery for my Acer Aspire 3810T and decided to make a clean cut. Instead of continuing to use Windows 7 as the operating system I have decided […]

Everyone knows the risks of working on an open Wi-Fi connection. Everything can be stolen from your security to your bandwidth. But the courts in the US have been historically unaware of […]
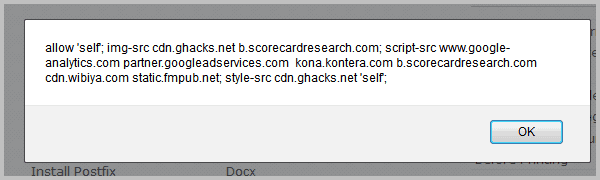
Content Security Policy is a standard developed by Mozilla designed to protect against cross site scripting (XSS) attacks. Cross site scripting attacks use vulnerabilities in websites to inject JavaScript code into pages […]
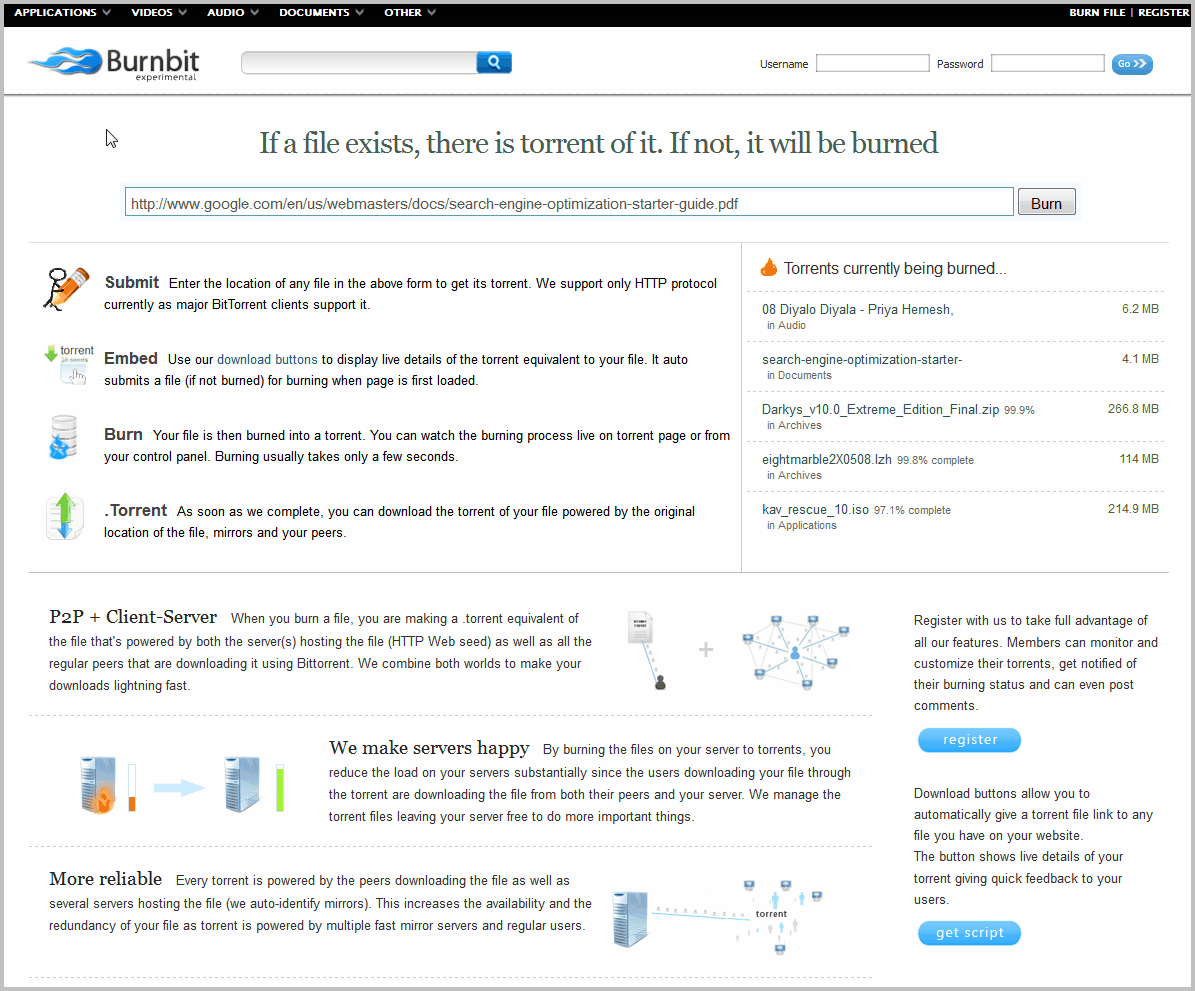
The experimental online service BurnBit can be used to create torrents out of any file that is hosted on the Internet. That's interesting for webmasters who want to reduce the bandwidth usage […]