You Got That Wrong, Say Google And Facebook
When it comes to security on the Internet, it can be extremely complicated for end-users to find out who is telling the truth, who is not and who is bending it. Two days ago news broke that French security company Vupen managed to bypass the Chrome browser's sandbox, something that no one had managed to do before.
A demonstration video was shown, but no proof of concept website or exploit information were revealed besides that.
Google's official investigation of the vulnerability is still ongoing and taking longer than usual as Vupen is not sharing details of the exploit with Google.
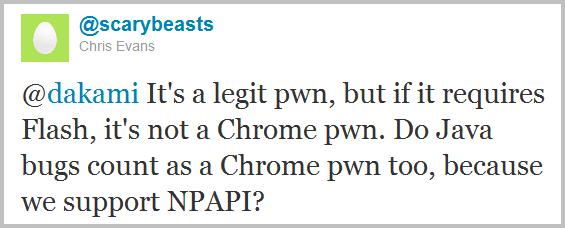
Google engineers on the other hand expressed their opinion about the discovery on Twitter. Tavis Ormandy, a Google security engineer, posted a message on Twitter saying that Vupen had it all wrong, and that they exploited a Flash bug and did not penetrate the sandbox of Chrome. Others like Chris Evans posted similar messages on Twitter.
Discussion between Chrome engineers and Vupen researchers continued for some time on Twitter, and grew heated at times. Vupen meanwhile announced that they got the exploit to work both on Chrome 11 and 12.
There are now two sides to the story. Vupen on the one side claiming to have beat Google Chrome's sandbox, and Google on the other saying that it was not the case. Google's adamant in defending their browser's security concept and sandboxing, as it is one feature that distinguishes it from other web browsers. A successful exploit could put a dent into the browser's reputation as one of the most secure web browser.
Does it make a difference if a Flash vulnerability was used to load the Calculator on Windows? From a technical perspective yes, from an end users perspective no.
But Google was not the only company who refuted security allegations today.
Symantec published research on the company blog yesterday that revealed information about an access vulnerability discovered on the social networking site Facebook. According to Symantec's research, Facebook applications may leak access keys to advertisers and other third parties. Access keys are generated when a user gives an application privileges on Facebook, and used to act with the user's privileges.
With those keys in the wrong hand, they could be used to perform actions that the user has authorized the application for. This includes posting on the user's wall, accessing a user's profile or profiles of friends, or reading messages that the user has written in the past.
Facebook spokeswomen Malorie Lucich downplayed Symantec's allegations in an email to PC World. She basically said that the report had inaccuracies, and that no private information could have been passed to third parties.
That sounds like a definitive no. Lucich continued stating that Facebook had no evidence of a privacy breach, and that the engineers took the necessary steps to resolve the issue, which again sounds like there has been a issue, and that Facebook did fix it after it was reported to them.
The truth in this case may be somewhere in the middle. Facebook did not deny Symantec's findings directly, which indicates that there may be some truth to the findings after all.
If you look at the story from an end-user perspective, you are again left with no definitive answer as to what has happened. Were applications able to leak access tokens? Likely. Did advertisers or third parties exploit the issue? That's not as likely, according to Symantec, and not possible according to Facebook.
Advertisement















As I’ve speculated here when the story first broke, it’s most likely Adobe Flash. It’s very very hard to sandbox badly written codes like Adobe’s. Using Adobe products is a guarantee dumb down of your PC’s security to Apple levels.
I seems to be inclined towards Vupen and Symantec here ;)
Well I do not know who is right and who is not. When I do not know I usually assume the worst ;)
I remember Google stating that they had sandboxed Flash within Chromium.
http://blog.chromium.org/2010/12/rolling-out-sandbox-for-adobe-flash.html