With Pixel Binary Transparency, your phone is safer than ever

In a continuous effort to enhance user security, Google has introduced a groundbreaking security feature called Pixel Binary Transparency for its Pixel line of smartphones.
This innovation aims to bolster the protection of Pixel handset users against potential hacking attempts and unauthorized modifications to the device's software.
With the increasing reliance on smartphones for personal and sensitive information, device security has become a paramount concern.
Google's Pixel Binary Transparency addresses this concern head-on by providing an exclusive security layer that ensures the integrity of a Pixel phone's operating system.

What is Pixel Binary Transparency?
Pixel Binary Transparency is an innovative security feature introduced by Google for its Pixel line of devices, primarily smartphones. It's designed to enhance the security and trustworthiness of Pixel devices by ensuring the authenticity and integrity of their software.
This feature employs a public, cryptographic log that records metadata about official factory images.
With Pixel Binary Transparency, users can mathematically prove that their Pixel devices are running factory images that match what Google has released and haven't been tampered with. The transparency log stores information about these factory images, allowing users to verify the authenticity of their devices independently.
This technology aims to strengthen security by providing verifiable evidence that the software on a Pixel device has not been compromised or altered maliciously.
How does Pixel Binary Transparency work?
Pixel Binary Transparency operates by employing a layered security approach. It begins with the Google Tensor system-on-a-chip (SoC) hardware, extending its reach all the way to the Android operating system and data center.
This end-to-end protection sets a new standard in mobile security, making Pixel phones among the most secure devices available.
One of the key features of Pixel Binary Transparency is the ability for users to independently verify the integrity of their devices. This means that users can check whether their Pixel phone has been compromised or tampered with in any way.
This verification process empowers users to have full transparency and control over the security of their devices.
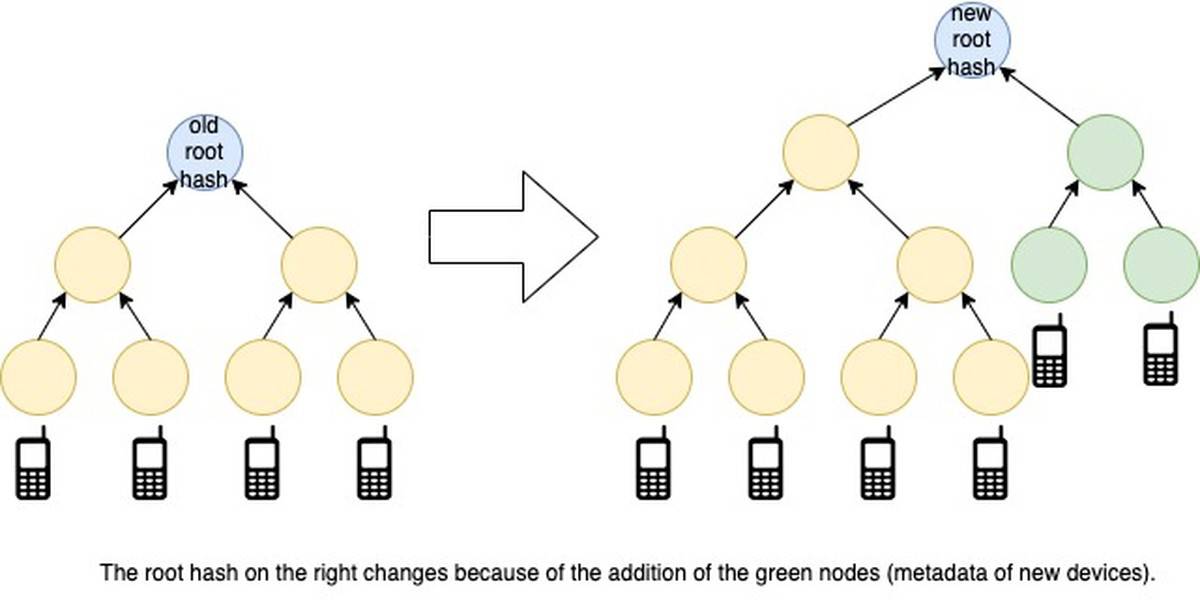
According to Google, For those who want to understand more about how this works, the Pixel Binary Transparency log is append-only thanks to a data structure called a Merkle tree, which is also used in blockchain, Git, Bittorrent, and certain NoSQL databases.
Read also: Google Chrome 116: more Telemetry and 26 security patches.
Integrated with Android 14
Pixel Binary Transparency seamlessly integrates with Android 14, the latest version of Google's mobile operating system. This integration further enhances the security ecosystem, ensuring that users' devices are safeguarded against potential threats and vulnerabilities.
Security experts commend Google's efforts to prioritize user security. The introduction of Pixel Binary Transparency showcases Google's commitment to staying ahead of evolving security challenges in the mobile landscape.
By providing users with the tools to verify the authenticity of their devices, Google empowers its users to take an active role in their digital security.
Featured image credit: Google
Advertisement