Security vulnerabilities found in Intel and AMD processors
Security researchers have discovered vulnerabilities in Intel and AMD processors that may lead to information disclosure.
Most Intel 10th, 11th and 12th generation processors are affected by a new vulnerability that the researchers have named ÆPIC Leak. The vulnerability is an architectural bug according to the researchers, which sets it apart from Spectre and Meltdown vulnerabilities that have haunted Intel and AMD in the past years.
AMD Zen 2 and 3 processors are affected by a security vulnerability that the researches named SQUID. It is a side channel attack that is targeting CPU schedulers.
The following paragraphs provide a high-level overview of both security issues. We provide links to the research papers and security advisories released by Intel and AMD.
Most home devices with affected processor models should be safe, as the attacks have certain requirements that make attacks on home systems unlikely.
ÆPIC Leak: important resources
Security researchers from Sapienza University or Rome, Graz University of Technology, Amazon Web Services, and CISPA Helmholtz Center for Information Security published the research paper ÆPIC Leak: Architecturally Leaking Uninitialized Data from the Microarchitecture recently.
The name is derived from the Advanced Programmable Interrupt Controller (APIC) and affects all Intel processors that are based on the Sunny Cove architecture. In particular, Ice Lake and Alder Lake processors are affected.
Attackers may exploit the vulnerability to retrieve data from the cache hierarchy. Without going into too many details -- the research paper provides all the technical information needed -- Æpicleak exploits a bug in Sunny-Cove based processors. When reading data on Sunny-Cove based CPUs, stale data from the superqueue is returned; this is not by design, as it should result in undefined behavior instead according to Intel.
The researchers note that the returned data is not restricted to security domains.
The uninitialized data returned from ÆPIC Leak is not restricted to any security domain, i.e., the origin can be userspace applications, the kernel, and, most importantly, SGX enclaves.
Experiments confirmed that the superqueue is used "as a temporary buffer for APIC requests". The superqueue contains recent memory loads and stores, and the APIC "only overwrites the architecturally-defined parts of the register and leaves the stale values in the reserved part".
In other words, attackers may exploit the bug to read data, including AES-NI keys from SGX enclaves.
Several different attack techniques are described in the research paper:
- Leaking data and code pages -- The most straightforward attack type combines "Enclave Shaking and Cache Line Freezing" to "leak data (and code) at rest of an SGX enclave.
- Leaking register values -- Attack targets a specific cache line to reconstruct the value of the register.
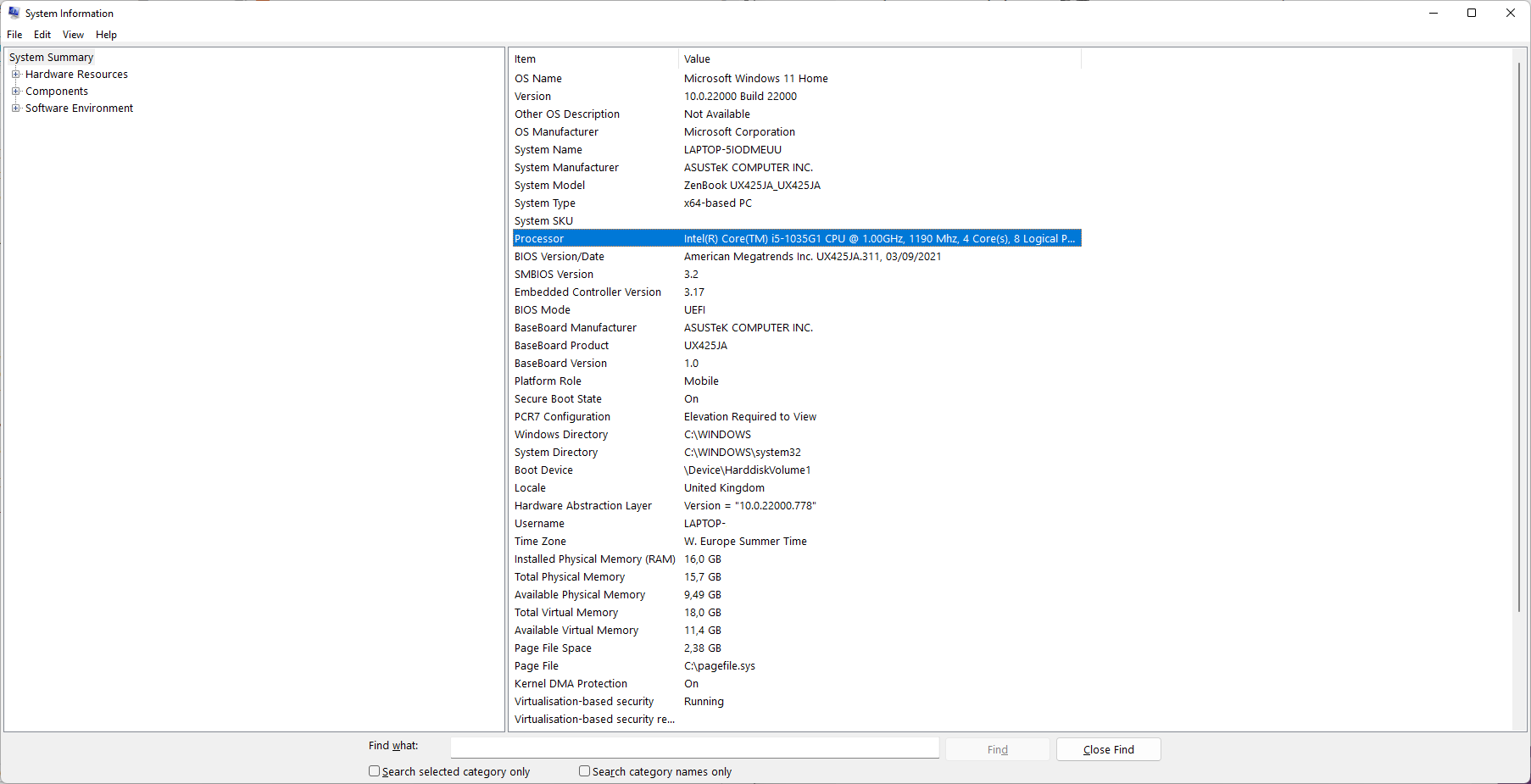
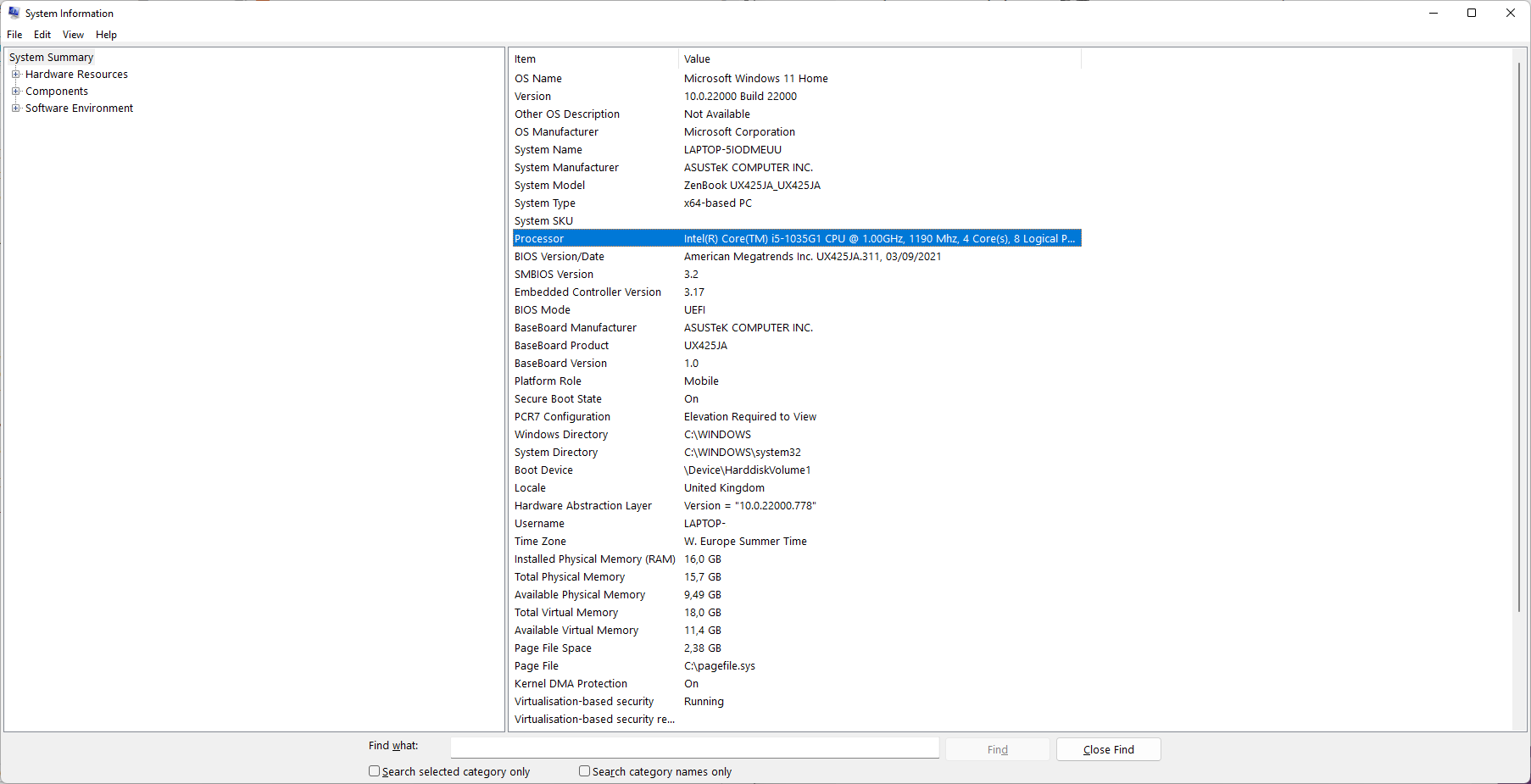
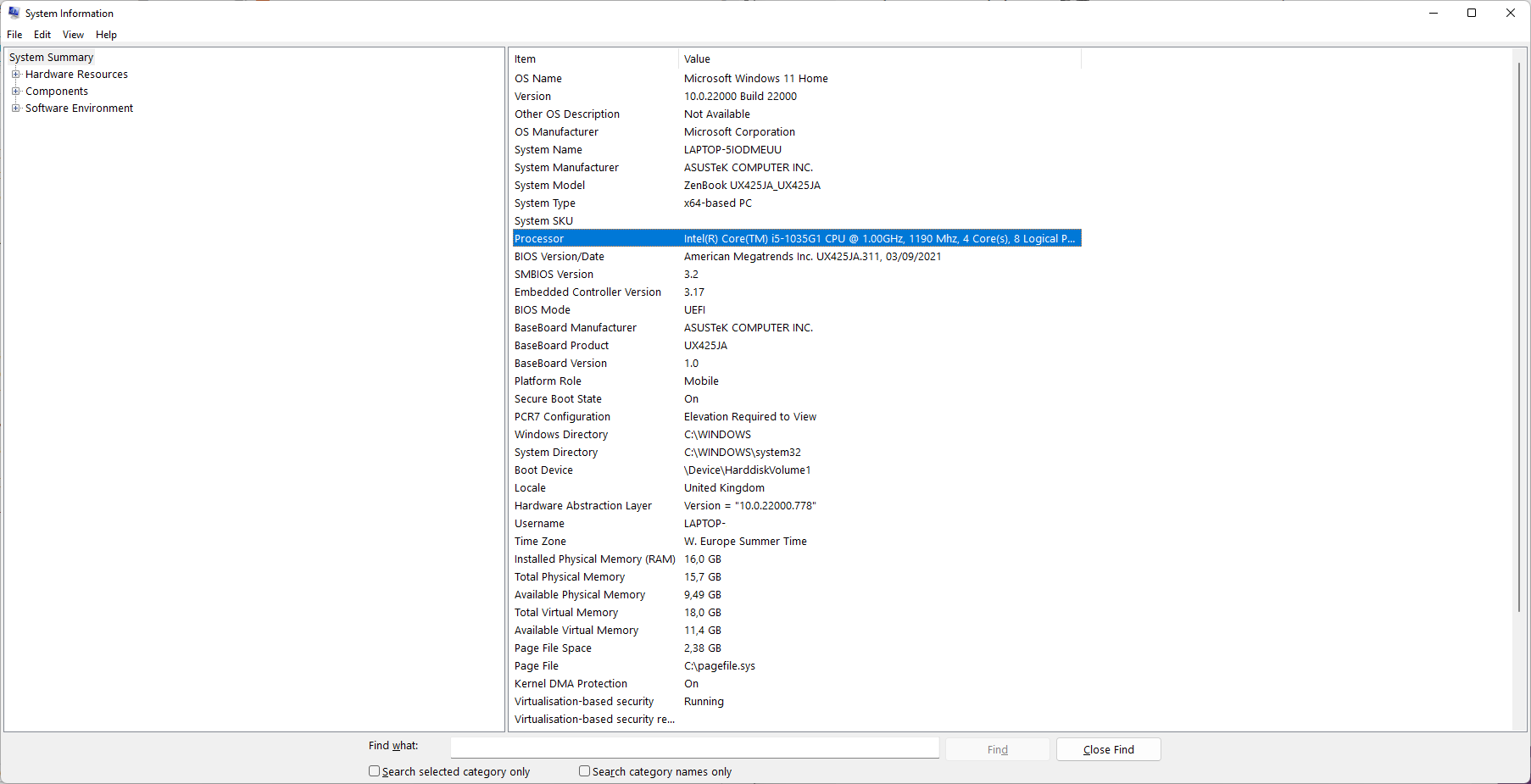
How to look up the processor generation on Windows
Windows users may do the following to check the processor generation of Intel processors:
- Open the Start Menu.
- Type System Information.
- Load the System Information result.
- Check the value of the processor entry, and there specifically the first or the first two digits after the dash, e.g., Intel Core i5-1035G1 is a 10th generation processors.
Sunny-Lake based processors are not vulnerable to Meltdown attacks.
Mitigations and fixes
The vulnerability requires root or administrative level access to the machine to exploit the vulnerability. Most home systems should be safe because of that, but it is still recommended to install updates once they become available.
Æpic Leak requires a hardware fix according to the researchers. They assume that the fix should not be too complex, as older processors are not affected by the issue. The research paper lists several mitigation suggestions, ranging from disabling SGX to disabling caching for EPC.
Intel reveals on the 2022.2 IPU - Intel® Processor Advisory support page that customers should install the latest firmware versions provided by the system manufacturer to address the issue. Intel plans to release SGX SDK updates once the public embargo is lifted.
Intel has released microcode updates for affected processors that are already available on the company's public GitHub repository.
AMD processors affected by SQUIP vulnerability
A new research paper by researchers from Lamarr Security Research, Graz University of Technology and Georgia Institute of Technology have discovered a new vulnerability affecting certain AMD processors.
Resource links:
- Execution Unit Scheduler Contention Side-Channel Vulnerability on AMD Processors
- SQUIP: Exploiting the Scheduler Queue Contention Side Channel
The linked research paper provides technical details on the vulnerability. Researchers discovered a vulnerability in CPU schedulers of affected AMD processors. SQUIP is the first side-channel attack on scheduler queues, according to the research paper.
The SQUIP attack observes the occupancy level from within the same hardware core and across SMT threads.
An attacker could extract sensitive data from a co-located victim in under 45 minutes, according to tests performed by the research team.
Hardware and software mitigations are suggested in the research paper. One of the easier options is to deactivate SMT or to prevent that processors from different security domains from running co-located on the same core.
The following processors are affected by the vulnerability:
- AMD Ryzen 2000, 3000 and 5000 series
- AMD Ryzen 4000 and 5000 with Radeon graphics series.
- 2nd and 3rd generation AMD Ryzen Threadripper processors.
- AMD Ryzen Threadripper PRO processors.
- AMD Athlon 3000 mobile processors with Radeon graphics.
- AMD Ryzen 2000 mobile processors.
- AMD Ryzen 3000 mobile processors.
- AMD Ryzen 3000, 4000 and 5000 processors with Radeon graphics.
- AMD Athlon 3000 series with Radeon graphics. (Chromebook)
- AMD Athlon mobile processors with Radeon graphics. (Chromebook)
- AMD Ryzen 3000 series processors with mobile graphics. (Chromebook)
- 1st, 2nd and 3rd generation AMD EPYC processors.
AMD users may use System Information to look up the processor. Other options include opening Settings on Windows 10 or 11 devices, and to select System > About to display the processor make and model.
AMD does not plan to release any kernel mitigations or microcode updates for affected processors. Instead, the company offers the following recommendation:
AMD recommends software developers employ existing best practices1,2, including constant-time algorithms and avoiding secret-dependent control flows where appropriate to help mitigate this potential vulnerability.

















“Repeating each cache line leak 2000 times, we achieve a leakage rate of 334.8 B/s with an average error rate of 7.8 %. Decreasing the number of repetitions to 200 , the leakage rate increases to 1.76 kB/s with an average error rate of 16.0 %”
“Due to ÆPIC Leak limitations (cf. Section 4.1), this approach leaks 37.5 % of a page.”
so…. less than 40% of the data is read, with a 7-16% average error rate?
scary :/
“No problem. The Next Generation CPUs will fix them.”
“That’s not a bug, that’s a feature!”
As far as actuall access to computer is neccessary – meaning exploit can’t be executed remotely, then it’s irrelevant for desktop computers at home.
For Windows users there’s the Intel Processor Identity Utility: https://www.intel.com/content/www/us/en/download/12136/intel-processor-identification-utility-windows-version.html which according to Intel identifies the current microcode running on the machine.
But don’t you just hate these Intel menus! There’s no easy way to search the list of CPUs and the Haswell processor in my laptop doesn’t appear in the initial list of i5 CPUs. This means you’re forced to scroll through all of them instead of being able to search the list as would be the case if they were located on a normal html page.
only apple soc for me – macos+ios
just because no one reported security vulnerabilities for apple m series CPUs doesn’t mean they don’t exist there
I swear processors are trash these days.
Very lazy AMD… VERY LAZY!
I guess we will have to wait for a third party to do their job for them… AGAIN!
Hell yeah.
With every generation come several more vulnerabilities and mitigations which undo the performance gains.
Just like the Meltdown vulnerability, nothing will happen, no hacker will be using it. The only thing that will happen is once they patch it your CPU will be slow as Pentium II.
I wouldn’t say “no hacker” will be using it. Depending on the purpose of the attack a hacker could get in, do what they have to do and leave without you noticing. Such attacks could be the infiltration of sensitive data, they don’t have to rob you and then set fire to your home when they leave.
If the process slows down after a patch then we should direct our frustrations towards manufacturers such as AMD and Intel to make them responsible or if need be begin some sort of class action.
That’s why I disabled the Spectre and Meltdown mitigations in Linux Mint.
I have an old Haswell processor…
[https://romanrm.net/disable-meltdown-spectre-patches]
There are already protections against Spectre and Meltdown in my browser.
[https://blog.mozilla.org/security/2021/05/18/introducing-site-isolation-in-firefox/]
Ma boi AMD does not care about users. Interesting…
None of the massive corporations do
https://www.ghacks.net/2022/01/14/intels-dropping-of-sgx-prevents-ultra-hd-blu-ray-playback-on-pcs/
Based on this article you wrote earlier in the year, does that mean that concerns regarding any impact on SGX is non-existent on 11th Gen and Beyond? Since SGX is depreciated and does not exist on newer CPUs anymore.