Google, Microsoft and Apple commit to passwordless sign-in standard
Google, Microsoft and Apple have announced support for expanding passwordless sign-in support across major operating systems and devices. The three companies announced plans on May 5, 2022 to support a passwordless sign-in standard, that has been created by the FIDO Alliance and the World Wide Web Consortium.
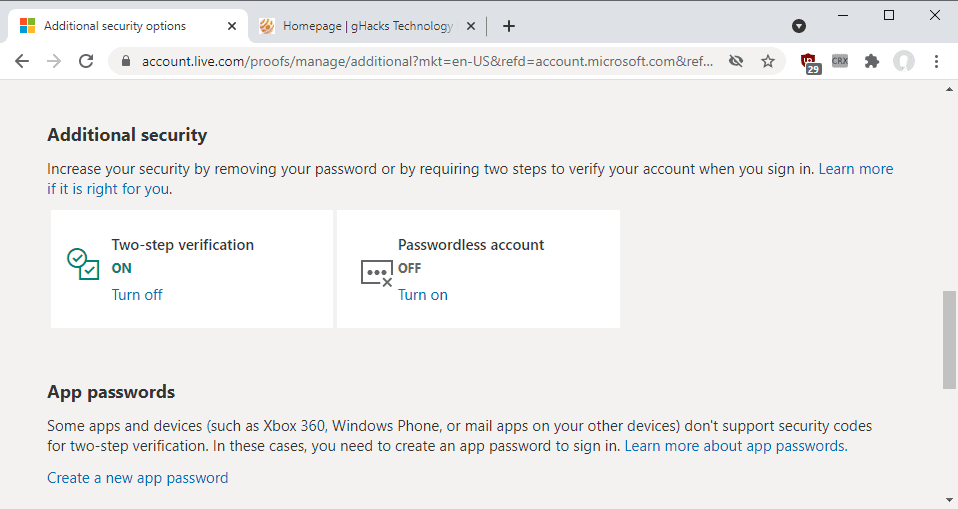
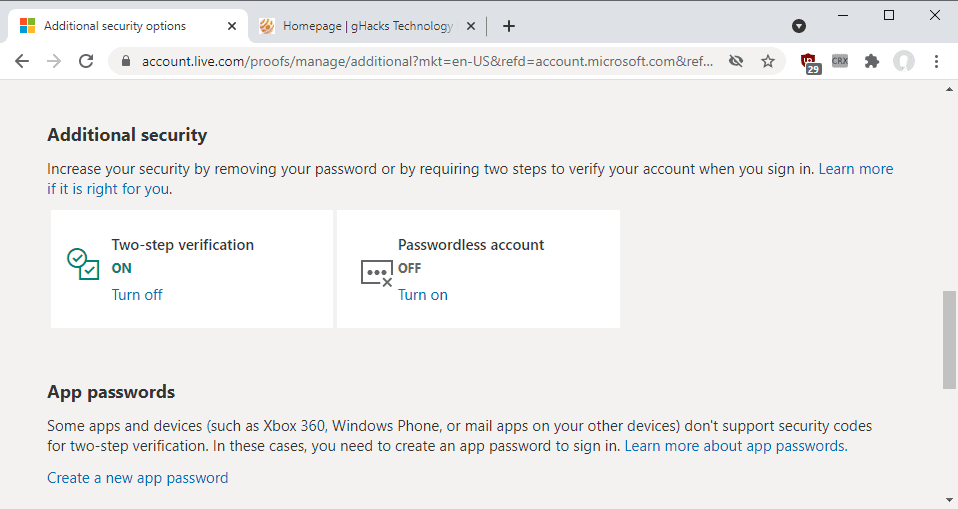
Current passwordless sign-in are specific to certain operating systems or services. Microsoft introduced support for passwordless accounts in 2021 and support for passwordless sign-ins nearly five years ago.
Customers may set up the feature online to use the company's Authenticator application, Windows Hello or other authentication options, to sign-in to their accounts across Windows devices and Microsoft services. The company claims that more than 240 million customers are signing-in to their accounts without using a password each month.
More than 330,000 customers have removed the password from their Microsoft Account completely in the last six months according to the company.
Simpler, stronger authentication’ is not just FIDO Alliance’s tagline — it also has been a guiding principle for our specifications and deployment guidelines. Ubiquity and usability are critical to seeing multi-factor authentication adopted at scale, and we applaud Apple, Google, and Microsoft for helping make this objective a reality by committing to support this user-friendly innovation in their platforms and products,” said Andrew Shikiar, executive director and CMO of the FIDO Alliance.
The improved standard bridges the gap between different operating systems, devices, apps and services, so that websites, services and apps may offer "consistent, secure, and easy passwordless sign-ins to consumers across devices and platforms" according to the announcement.
Passwords are "one of the most common entry points for attackers" according to Vasu Jakkal, Microsoft Corporate Vice President, Security, Compliance, Identity, and Management. Attacks on passwords have nearly doubled over the past 12 months according to Microsoft.
Two-factor authentication mechanisms help protect accounts, as they block 99.9% of all attacks according to a Microsoft study. While attackers may steal user passwords, for instance, through phishing attacks, brute force attacks, or malware, two-factor authentication blocks access to the account until a secondary form of authentication is completed. Authentication apps may be used for that, but also other means.
Passwordless sign-in systems go a step further by removing passwords from accounts. Users use the same authentication options that they use for two-factor authentication, e.g., an authenticator app, security key, Windows Hello, or codes that are sent to mobile devices or to email accounts, but without having to supply a password.
The expanded standard gives websites and applications an option to offer end-to-end passwordless sign-in options to their users and customers. With the new system enabled on their mobile devices, users will use the same verification methods for signing-in to apps or services, that they use regularly on their devices. They may enter their PIN, or use biometrical authentication options, if supported by the device.
Apple, Google and Microsoft are expected to introduce support for the expanded standard in 2023.
The benefits of the new passwordless standard
The new passwordless standard has been created by the FIDO Alliance and W3C. It is backed by Microsoft, Google and Apple, who will add support into their platforms. The three companies have "led development of the extended set of capabilities" to extend what is supported already.
The main advantage of the extended standard is that it adds additional capabilities that improve the experience significantly:
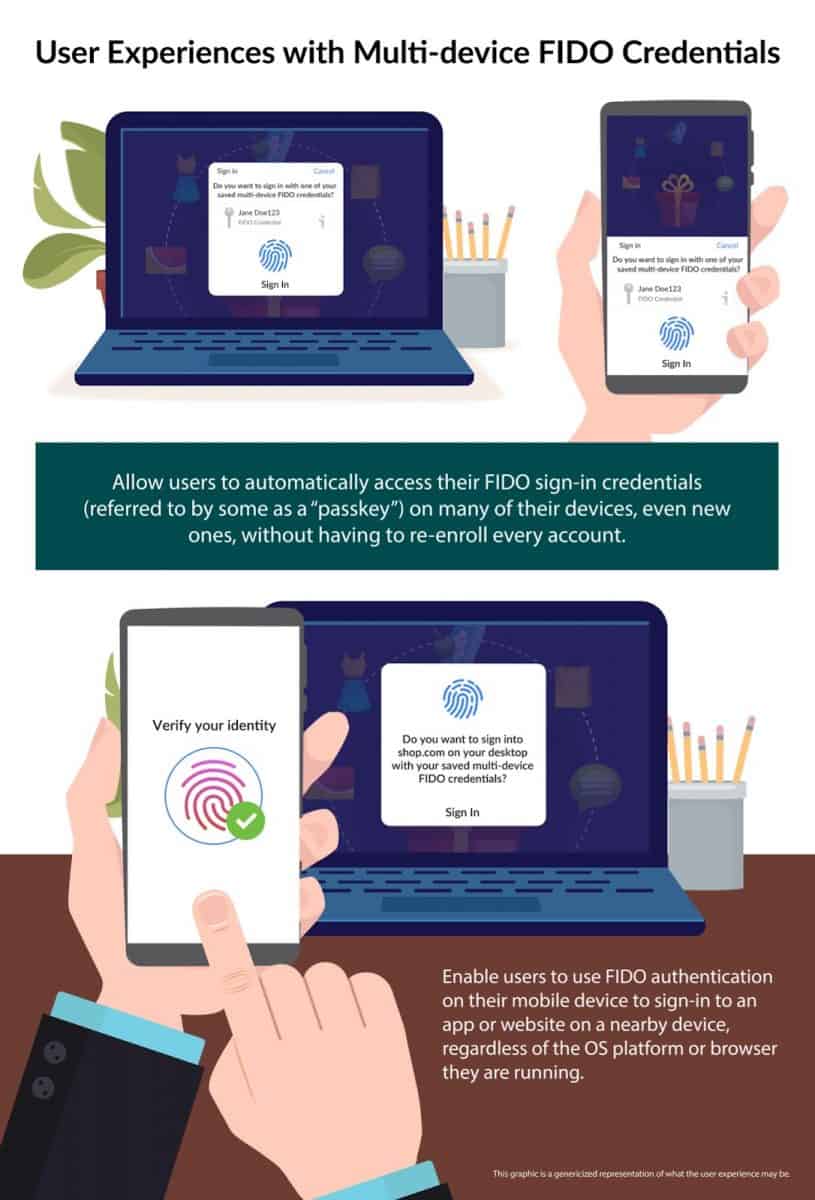
- Users may use the authentication option provided by FIDO on their mobile devices to sign-in to any app, website or nearby device, regardless of the operating system or the browser that is being used.
- Access FIDO sign-in credentials on any device that a particular users owns "without having to re-enroll every account".
The FIDO Alliance notes that the new standard is "radically more secure when compared to passwords and legacy multi-factor technologies such as one-time passcodes sent over SMS". When Internet companies started to introduce two-factor authentication options about a decade ago, many relied on insecure delivery channels, including email or SMS, for the secondary authentication code. While still more secure than sign-ins with passwords, these insecure channels could still be exploited by dedicated attackers.
The introduction of authentication apps, such as Microsoft Authenticator or Authy, eliminated that risk. Codes were created by the applications locally without any network activity.
The extended standard that will become available in 2023 offers the same advantages plus cross-device and platform support. The user's biometric information, which is used for authentication across sites, apps and services, is available locally only. The passkey information can be synced across devices, again without any platform limitations, provided that the platform itself supports the extended standard.
It has been difficulty in the past to install and use some authenticator applications on multiple devices; the new standard will make this easier and improves the experience for users who lose access to their devices or switch to other devices.
Microsoft's Windows Hello authentication system supports passkey sign-ins on all sites that support the functionality already. Soon, Apple and Google device owners may use passkeys to sign-in to Microsoft Accounts.
The removal of passwords eliminates attacks that aim to steal account passwords. Phishing attacks target user passwords and authentication information often, but without a password and password authentication, attackers run into brick walls when trying to steal data that does not exist.
Microsoft announced new passwordless sign-in capabilities this week:
- Passwordless support is now available for Windows 365, Azure Virtual Desktop and Virtual Desktop Infrastructure in Windows 11 Insider preview builds. Microsoft plans to roll out support to Windows 10 and 11 in the near future.
- Microsoft Authenticator supports multiple passwordless accounts for Auire AD. The new functionality will roll out to iOS devices in May 2022 and to Android devices later this year.
- Windows Hello for Business Cloud Trust improves the deployment experience for hybrid environments according to Microsoft.
- Temporary Access Pass in Azure AD has been in public preview for some time. The update allows users to use the feature to sign-in for the first time, configure Windows Hello, and join a device to Azure AD.
Closing Words
Cross-platform and device support for the passwordless sign-in standard will make it more appealing to users, as it removes the hassle of having to juggle between different passwordless authentication options if different platforms are used.
It remains to be seen how the three major players will implement support, and how well everything works once support has been introduced on all three platforms.
Now You: do you use two-factor authentication or passwordless sign-ins?

















FIDO Alliance? Would it not be a courtesy to say what the letters mean, or do you assume we are all are teenagers.
I don’t have my cell phone on all the time. And even when it is on, I rarely use it. Passwords that are long and just a mess of letters, numbers, and characters, seems to work well. But I guess I’m not as much of a tech geek as most of you guys. 8-)
I recently experienced a problem with a form of 2FA which didn’t work. I use an app called LINE a lot because all my friends do and had uninstalled / reinstalled it again in an attempt to fix a problem with sending images.
However, unlike previous reinstallations LINE now requires users to type a verification code sent to your device in order to login and start using it again.
The problem here was that the verification code didn’t arrive. The alternative method to have the code sent audibly didn’t work either. I spent four days without being able to use the app which was particularly frustrating because all my contacts were locked on that app and I couldn’t access them other than by logging into it.
To cut a long story short, I finally persuaded LINE to send the verification code to my registered webmail account with Tutanota after convincing them that my login password over there can’t be retrieved via the site and needs the account recovery code to access it in the event the account gets locked.
Whether or not that falls into the same category as 2FA I wouldn’t know, but it represents an example of where things can go pear-shaped if the technology doesn’t function the way it’s supposed to.
I love my fingers to stay at my hands so I will use classic passwords for a long time. Thanks for the article! :]
For me there is one problem with this new way of authentication: user choice. They want to REPLACE the passwords, not to give you an option between passwords and FIDO method. And for me this is unacceptable; give me a choice, and maybe I will consider your solution, force me and I will put maximum effort into getting around it.
When Google, Microsoft and Apple jointly announce an “improvement”, “an effort to make the web more secure and usable for all”, you can be 100% certain it’s a privacy-related regression.
And you should be very concerned.
Paranoia. Nobody will ever convince you of the truth. If you don’t trust it, join the Luddites. Shut down your PC.
@Anonymous, so “the truth” is that these 3 are not involved in data collection at all, and have the users interests at heart, as their mission. Not profit.
Ok. So, all these years of “use strong passwords” were not “the truth”.
Ok. Or perhaps, “the truth” has now changed and the big 3 bring forth a brand new shiny truth.
Steve Gibson (of Security Now podcast and grc.com) already solved this whole debacle with SQRL. Look it up. It works seamlessly, is a complete Digital Identity solution and a truly password-less solution. Obviously FIDO will win because of the names behind it, but SQRL is a better solution in every way.
Would be nice to have a simple explanation here. A lot of technical details to wade through in the “Explainer PDF” https://www.grc.com/sqrl/SQRL_Explained.pdf If it is so much easier and seamless, seems worth providing that at least.
Well, I never said it was easier. Convenience often lowers security, generally speaking, so SQRL’s solution is putting in a little work to create an actual digital identity which is not tied to any company, can be kept completely offline, and is verifiable by the proprietor of the identity using proven cryptographic methods. In the end you’ll have to just try it to understand the enormous potential. I just went and used the Android app, created my identity, and suddenly I can login to these two sites that Steve set up with the proper login prompts:
https://forums.grc.com/
https://sqrl.grc.com/
Being logged in to your Google phone 24/7 is slightly more convenient that having to enter a pin or secure password from time to time to prove you are you, but I’ve already temporarily lost access to Facebook, Instagram, and Google accounts at various times, so some people, myself included, enjoy the idea of more direct control of our identities. I’m sure there are many more uses for this type of secure digital identity, so I hope someone rediscovers it to bring it to the attention of more people.
Wow, I’ve seen 1 intelligent, informed comment in this whole thread, @ECR.
Passwordless can and is VERY frequently implemented in a completely non biometric manner. The FIDO2/WebAuthn Protocol for passwordless sign-in works just as seamlessly when instead of a biometric token, a physical token is used. The company I work at enforces passwordless via the use of Yubikeys. On every device I use, (while I COULD opt to use my biometrics) I instead simply tap my Yubikey and am granted the exact same passwordless, single sign on access as somebody touching their thumbprint or scanning their face. Hardware keys are baked into FIDO2 moreso than biometrics, in actuality, because mobile phones are the only platform where biometrics are part of the package; desktops don’t come with biometric scanners, and they are used for work a whole lot more than a damn phone is.
Microsoft and Google have been endorsing the use of Yubikeys for passwordless adoption for far longer than any biometric method. It’s only because of Apple’s market share in mobile that the FIDO2 protocol was built to support indirect biometric authentication via a hardware token (your iPhone) that utilizes biometrics locally.
And it is actually true that the biometric mapping (which is nowhere even close to your entire Face/Finger) never leaves the device’s secured hardware enclave, it’s a cryptographic attestation that is utilized, or in much dumber terms a yes or no response. It either is you or it is not you. Red or Green. Period. The complex computations that determine that yes or no all occur within the TEE hardware, which is not proprietary, and conforms to the TPM standards that ensure it operates in a deterministic manner, inaccessible to the OS, Firmware, Software and all other hardware in the device. Any attempt to even observe it’s functions will by design break its ability to provide a yes or no.
This is so utterly asinine, spying on you using literally the hardest most not possible method of spying on you. I mean, aside from the fact they can’t do it, why would they? They can ACTUALLY spy on you using the phones camera and microphone by way of coding any app on your phone to do exactly that, or they could just track all the stupid selfies you take/post and the calls you make, and obviously the GPS tells them everywhere you ever are should they actually care about any of that stuff which for 95%+ of you I’m sure they don’t.
In any event, as any and virtually every cyber-security researcher has stated, this is long overdue and will finally bring the abhorrent amount of cyber crime and security breaches ocurring everywhere to a fraction of what it currently is. About effin’ time.
Yubikeys may not work if your OS isn’t Windows 10 or later. The type which were supported on earlier versions such as Windows 7 or 8.1 have been discontinued.
I contacted Yubico recently to ascertain what the position was and they advised me that the latest versions might work, but weren’t supported which isn’t very encouraging.
Presumably this also implies that once Windows 10 support expires in 2025 you’ll have to update your hardware token as well as the OS.
Biggest issue in this method is Device fingerprinting. These companies tag your device, afterall that’s how a prompt is generated. I use 2FA on all my accounts possible and have the authentication key stored in password manager. As long as signing in on to a personal device remains optional, all good because smathphones and desktops already make tons of connections even without signing in. 2FA codes are as secure IMO and no personal device sign in required or any fishy biometric ‘local’ data. BTW don’t ever use your phone number and SMS for 2FA authentication to those who’re using them currently.
This is concerning.
In an era of fake news, we will now have our devices storing our fingerprints, face image, retinal print, voice print etc.
Given what is possible with Deep Fakes currently just by using your face image and voice print, imagine how easily someone could be framed from crimes.
Planting fingerprints, creating facial masks, etc.
Sure there are people that say that it is only stored locally on your machine. But in a world that is moving away from passwords, if your device profile is backed up to the cloud and needs to be restored to a new device after your device has been lost or stolen or broken, you would obviously need to authenticate it using biometrics no? Where would those biometrics be stored?
Concerned I don’t use any hand held devices at all. I will only use a desktop computer, nothing else. I don’t use the cloud. No sign in info or password. Never use credit cards. Hell I don’t even use a cell phone. If your really concerned about privacy then stop using hand held devices or anything that infringes on your privacy, problem solved. I suggest keep things very simple and minimized as much as possible. It’s not hard to keep a very low profile about things. Just takes some work.
About passwordless sign-ins:
This World Password Day consider ditching passwords altogether – Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/05/05/this-world-password-day-consider-ditching-passwords-altogether/
Passwordless authentication is becoming commonplace
a passkey lets you sign in simply by authenticating with your face, fingerprint, or device PIN.
In short, the only means of authentication will be “biometrics” or “device PIN”.
Biometrics is touted as an absolute, flawless means of authentication, but it would be a disaster if such absolutely unique personal information were to be leaked (or copied).
In the first place, it is unclear how biometric data will be managed.
The fact that the most important “biometric” means of authentication in personal information is being formulated by for-profit Platformers (Google, Microsoft, Apple) is in itself distrustful.
I categorically refuse “biometric” means of authentication.
Incidentally, the company I work for (an international company with more than several hundred thousand employees) has come to the conclusion that password authentication is the best solution as in the past, because “the leak or leakage of biometric data, the ultimate personal information that cannot be changed, would lead to a catastrophe, and there is no perfect measure to prevent it”.
Then your company must have an incredible batch of employees who never share passwords, fall for Phishing attacks or are individually corrupted by criminals. IMPOSSIBLE! Human nature is human nature. Work on the basis you can’t trust 5% of the people you work with.
@Anonymous,
> IMPOSSIBLE! Human nature is human nature. Work on the basis you can’t trust 5% of the people you work with.
Decent international companies have a rigorous personnel screening process and will never hire you if you lack the skills (knowledge, skills, and potential) that are essential to the company (job position). Personnel are not influenced by high academic credentials or nepotism.
Employees have a “progressive and adequate training program” throughout their entire period of employment until they retire, and are assigned to positions and workplaces based on their proficiency and ability.
The assignment is not fixed, but rather regular job rotations are available for reassignments, transfers to other offices, and overseas business trip or work programs, allowing employees to enhance their skills and mutual exchange and sharing as they work.
IT equipment used in the workplace is not appropriated from off-the-shelf products, but is completely rebuilt by the company’s own systems department and controlled by enterprise policy, making it impossible to divert it for private use.
Usage methods and standards are defined in the “bylaws,” and multiple (supervisor approval and logging) checks work in office work, so there is virtually no room for mistakes or irregularities to occur.
The reality in an unspecified home-user situation and in the enterprise of the most highly skilled elite organization are not similar, you know.
What I am trying to say is that an international company with such a thorough “safety concept” is rejecting “biometric authentication”.
In international companies, “accident prevention and the dignity of the individual (employee)” are priorities, and as a result, they have come to the conclusion that password authentication is the best and most realistic method.
https://www.ghacks.net/2022/04/28/ransomware-payments-are-marginal-when-compared-to-the-overall-costs/#comment-4520430
So, just chop off some random persons hand and use that. This will be the new norm.
Make accountless operating systems instead, you fu**ers.
Digital identity WILL come. It’s being rushed through across many countries and with it a raft of more stringent, more privacy and freedom eroding surveillance. This is just another step in that direction. Where I am the legislation is sitting in parliament waiting for the election to be done and then it will be implemented.
A sad day for all of us.
1) Your phone account is hacked. ALL your passwordless accounts are done for.
2) Good luck changing your face or finger print once that has been pilfered from a vendor’s files.
What could go wrong? Your biometric ID linked to everything you do, leaving a trail everywhere from your sign in to Twitter to yell at Elon Musk to the five Martinis at the bar after work when you told your wife you were working overtime. Maybe your life isn’t that exciting but do you really want a world with zero anonymity, zero privacy in which Bill Gates and Joe Biden watch everything you do? Then what happens if Trump is re-elected? Trump with access to everyone’s devices? He will shut down all the heretics.
Be wary whenever they say something is to help you and it makes your life more complicated and more dependent on a corporation’s “service”. Corporations with direct ties to intelligence agencies.
people already give their information mostly voluntarily anyway, and to make an apple, google or microsoft account and others of course, you already have to provide too much information so this is not going to change anything at all.
but if you worry so much and you mention biden, i would worry more about the fact he is pushing for world war 3 and idiots are agreeing with it and the propaganda with all a theater US is doing against Rusia through Ukraine with the help of other criminals accomplices and parasites of many other governments and non-democratic criminal organizations like UN and NATO.
so, why even mention a hypothetical 2024 election and trump and having access to your devices? it’s like you sound really ignorant, like if US government and others didnt already had access to your devices and information even before you were born because i am sure you are not 6 years old to somehow talk about trump today who has nothing to do with current world events or anything about microsoft or google or apple.
of course we can mention how biden today decided to create their Ministry of Truth, and that seems like it is more dangerous than apple, microsoft and google wanting to control how you log in to their services. no? there was no ministry of truth when people posted something on twitter or facebook and they got FBI and CIA knocking at their doors
why do you even mention trump who has nothing to do in any current world event today, while you are probably doing nothing about Mary Poppins in charge of the ministry of truth and the other clowns who should be in a psychiatric but somehow they get political positions where they follow the agendas of their masters and might really affect peoples lives.
anyway, about bill gates, well, unless you talk about his depopulation programs masked as bs philanthropism, he has no room on this either since he doesnt work at microsoft anymore but i am sure people voluntarily already gave him a lot of data though world death(ealth) organization and hospitals and anything fake labeled as ‘health’.
Robert Highlander on Windows 10 IoT Enterprise LTSC 2019 I don’t use any sign in info at all. Will never use a Microsoft account is long as I live. I don’t use Microsoft Apps either. Got them completely removed off of Windows 10. Very true about evil Bill Gates and the so called Ministry of Truth.
Then don’t use technology.
Did you complain about this since you were born? I mean, what about your ID, social security number, driver licenses, bank accounts, voting registration and pretty much everything else?
You always have to provide address, phone numbers and everything that directly identifies you to many entities and not just the governments knowing what exactly you are doing or where you are.
People who complain about digital identity are funny, because you can still choose not to use technology, but are you willing to stop doing that? of course, like I said, governments will not stop spying you and wanting to control you. This is talks about Google, Microsoft and Apple, so choose to use other services where you have to still provide phone numbers, an email address, sometimes a real name (like on facebook)… how is that better?
Maybe someday you will accept that fact that internet is incompatible with privacy, and maybe you will understand that your identity is never going to be protected… your extensions, vpn and firewalls and dns servers and Linux (since it seems clueless people think OS matters), will never protect you nothing, you go to google, microsoft, apple, facebook, twitter and any other big tech company (and any small or medium company) and they will always gather information about you because you are in THEIR domain and using THEIR servers. So you either choose technology or not, of course, your privacy is still not secured with all the camaras watching population, with all the ‘security’ measures governments and companies take, when you get a passport, when you use your passport, when you get to buy alcohol or cigarettes and you have to provide your ID and your debit and creidt card…
Do you really think that password or passwordless really matter? seems like you are clueless when everything is mean to spy you, do you live in the real world or you think internet is all that matters?
Again, since you were born, you were given a number, like barcode like in a product you see in a supermarket… so, do you think companies and governments will make things better today? when everything is about internet today and people have allowed because of ‘commodity’ and ‘quicker and easier access’? That’s why more and more technology have internet access even if it doesn’t make sense like refrigerators or smart dumb crap like lights and sockets and whatever because ‘controlling it with my phone is so kewl’.
Your whole argument is just nonsense when you apparently don’t talk how it was always like this before internet, and internet just made it worst because that was the most obvious thing.
There is literally ‘zero anonymity’ (using your words) today, before and ever since you were born. We are not in the 1800s where maybe that was a little easier to accomplish, but people aren’t going back to those times, we are actually going worst and worst because people are allowing technology to take over… so move to the real world, it wasn’t good before internet was created and it will not be good ever even if you wish to live in a fairy tale of supposedly anonymity life especially if you want to use the internet.
There was NO anonymity or privacy in this world when you were born, there is no going to be anonymity or privacy when you die. Just get it already and be honest, you will not stop using and buying new phones and computers and new hardware and etc etc, you don’t care about it, you would rather buy from Amazon, than going to a local store and having to walk to buy stuff yourself.
Funny how you mention Trump like a real clueless TDS clown, and you are not complaining about Biden, who is probably going to cause WW3 through a proxy war against Ukraine, I mean, one thing would be that thanks to a nuclear war, your devices, internet, cryptocurrencies and electricity and anything will just not work the way it works today… so you will finally get back the anonymity you will so want so much (even if you are here on the internet commenting).
I mean, your TDS is so strong and blinds you that you really think you had privacy and anonymity before 2016, before 2008, before 2000, before 1990, 1980, 1970… you pick it.
Maybe it is time to start using your brain and drop the fairy tales.
I’m not sure if I’m reading this right, but it appears to me that the “solution” to weak passwords is for all of the big tech companies (and probably their spy agency partners) to share all of our biometric data amongst themselves.
Do I have that right?
No you don’t have it right. The theory is the system fetches an identifier, not your personal details. Whether they do it with cunning (as bad as the Phishing they are theoretically stopping) or simply break the law is a different matter. My opinion is being discovered breaking the law kills the share price. Most would prefer to do it with high-priced lawyer’s weasel words in the ridiculously lengthy privacy agreement.
Courts need a reasonability and simplicity test for privacy agreements (e.g. ‘Could an 8 year old understand the words and structure of the agreement’.
That’s incorrect. You can use a numerical PIN, or an alphanumeric PIN (password) instead if you want. However, regardless of whether you use a PIN, or biometrics such as fingerprint or facial recognition, these are all local only – these never get sent to a server. They don’t need to be, as the passkey server (for syncing between devices) and the individual websites you’re logging in to are only interested in private/public keys (asymmetric public-key cryptography). The purpose the PIN/biometrics serve is just for you to authenticate (allow) the private key stored locally on a secure hardware chip of the device to solve the encrypted challenge a website sends to it.
When you first sign up to a website such as Amazon, your local device generates a private/public key pair and sends the public key to the website. A public key is, well public, so if the website is hacked they have no passwords in their database, just public keys, which are useless.
The next time you need to log in to that website, the website creates a challenge to solve, encrypts it with your public key and sends it to your device. Your device will then decrypt the challenge using its private key and respond to the website with the answer to the challenge to prove it’s you trying to log in to the website.
This will never happen. These companies are out of touch with reality. Not everyone is using a smartphone, have access to internet 24/7, or stable power grids.
Watch when I-net goes down and you can only get back online with the new digital ID and phone…
For these reasons it will most likely be an option rather than mandatory, as is log in with Google authentication now.
Our private phone numbers is *the* golden egg these tech firms deeply desire. What we really need is less intrusion into our private lives, not more. Tech firms have proven time and again they lie, continue to steal our private data, are underhanded, and cannot be trusted.
https://www.theverge.com/2018/8/30/17801880/google-mastercard-data-online-ads-offline-purchase-history-privacy
Bonus, read the un-redacted DOJ reports on google’s war diving
Not to mention reliability issues, no internet for you. Just today, Xbox log in services are down worldwide with users unable to play games they “own”. And these same incompetents want to by my single point of failure unto the internet? Right.
https://www.bleepingcomputer.com/news/technology/xbox-is-down-worldwide-with-users-unable-to-play-games/
As if that has ever stopped companies/governments from making asinine decisions before
Companies are way out of touch. In my area alone internet outages occur from time to time. Mobile cell services are useless, circa 2004
Passwordless authentication will make things easier to track individuals.
Password managers are my tools to login into my accounts.
I use two factor authentication via yubikeys and Google prompt.
Then where is he inputting password