Brave browser adds native support for uBlock and Fanboy annoyances lists and social list
Brave browser's built-in ad-blocker has been boosted by some additional options. The Chromium fork's Brave Shield now supports three popular privacy-friendly filter lists, namely uBlock Annoyances List, Fanboy Annoyances List and Fanboy Social List.
What are these filters anyway? Do I need them? As you may know, ad-blocking extensions and Brave Shield disable advertisements, banners, and other forms of ads. But most websites have additional elements on their website such as social sharing buttons such as Facebook, Twitter, or other elements that users may find annoying.
The new filter lists block the tracking functionality of these elements (they're visually removed too), and also removes pop-up stuff like subscribe or welcome banners.. Yes, those social share buttons actually track your visits, even if you never use them. If the buttons are available on the page, it acts as a tracker and sends the information to their parent site, that's how Facebook Pixel works.
Tired of those "we use these cookies" notices? Some sites employ anti-adblock features, these annoyance lists ensures that these get blocked as well.
Since Chromium-based browsers lack the power of Firefox containers, which in my opinion offers better privacy, these annoyance lists are welcome additions for Brave browser users who want to prevent social-networks from tracking you.
That's great, but these new options are not enabled in the Brave Shield by default. That's probably because not everyone may want to use them.
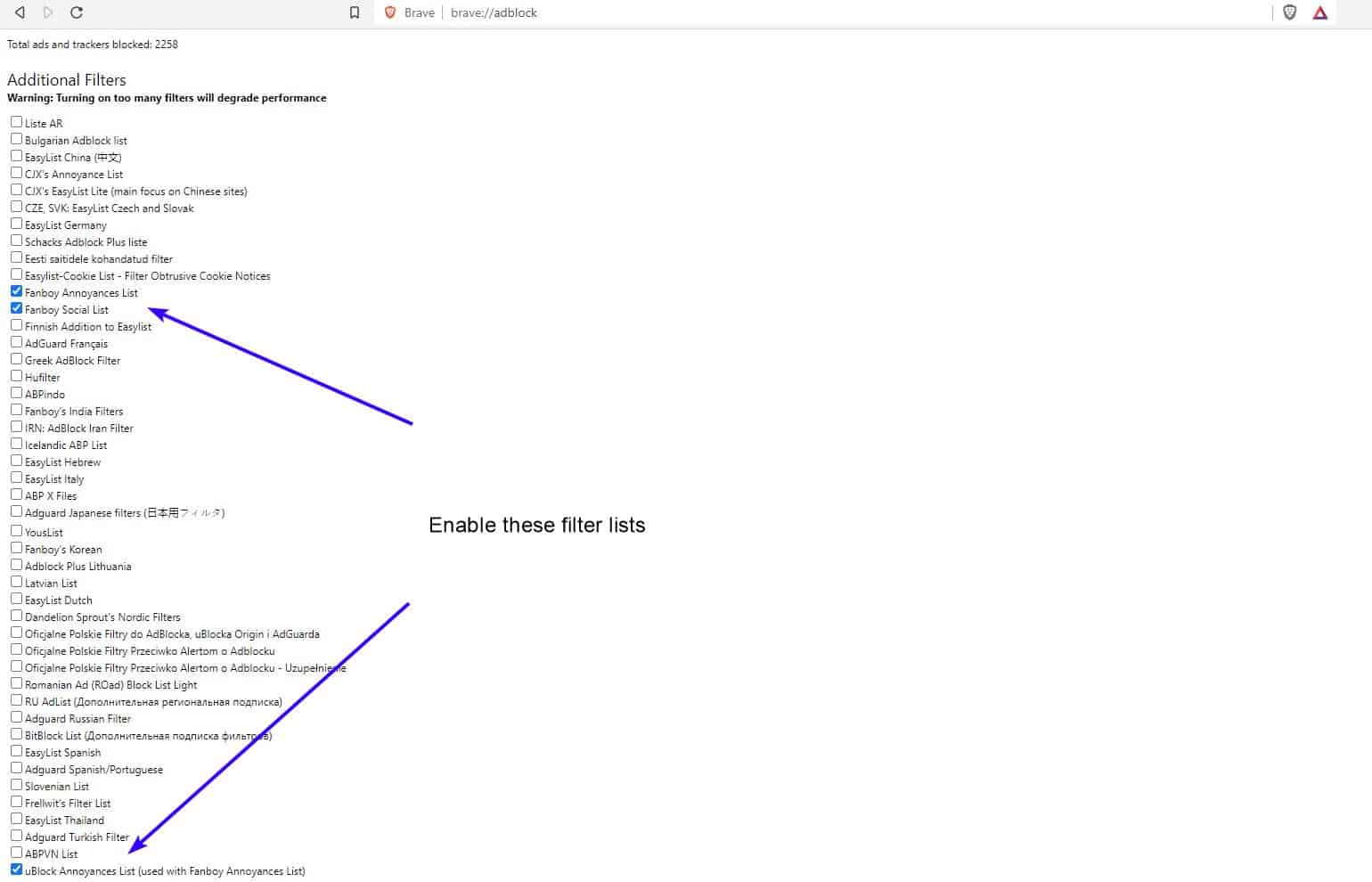
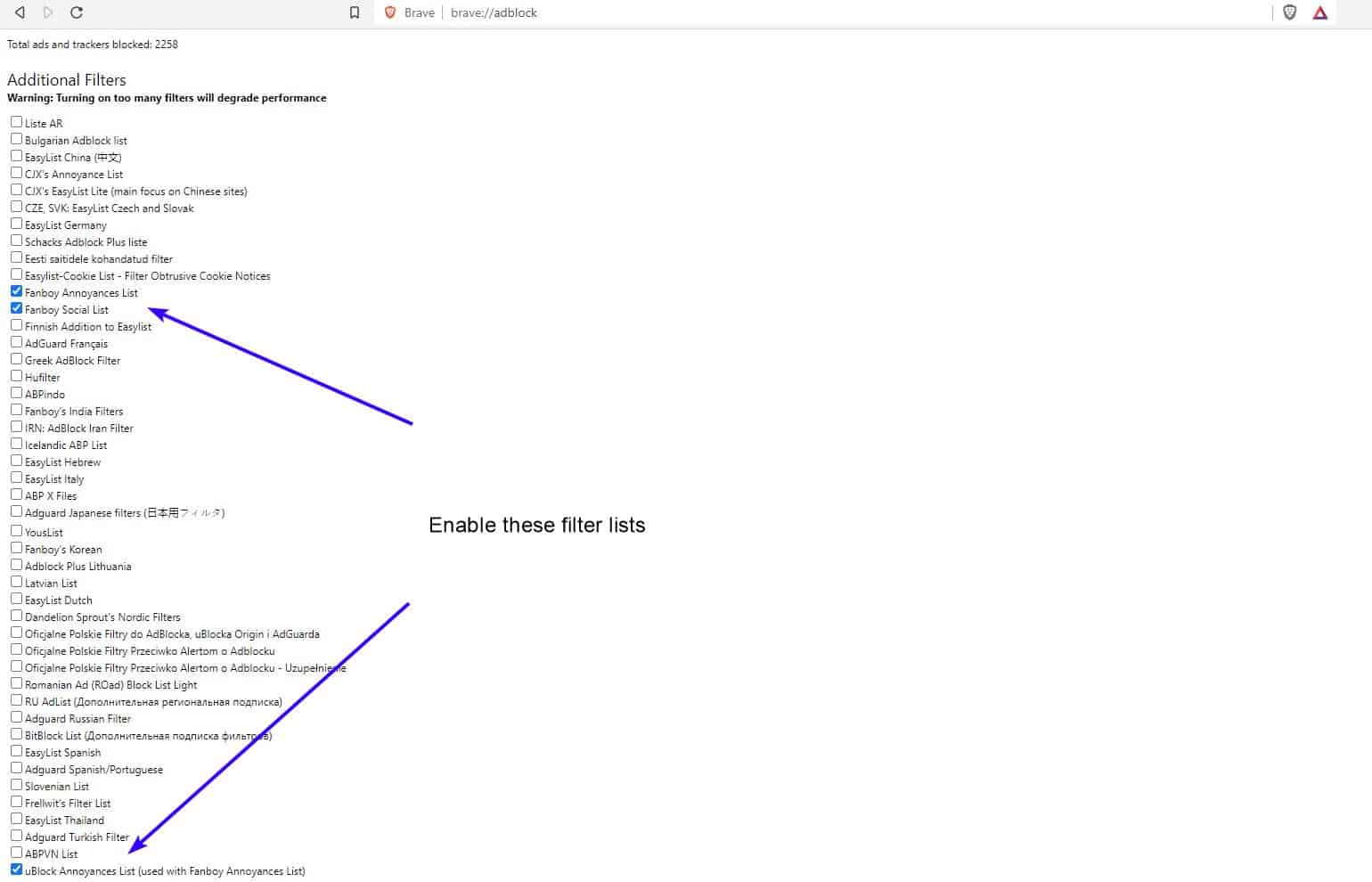
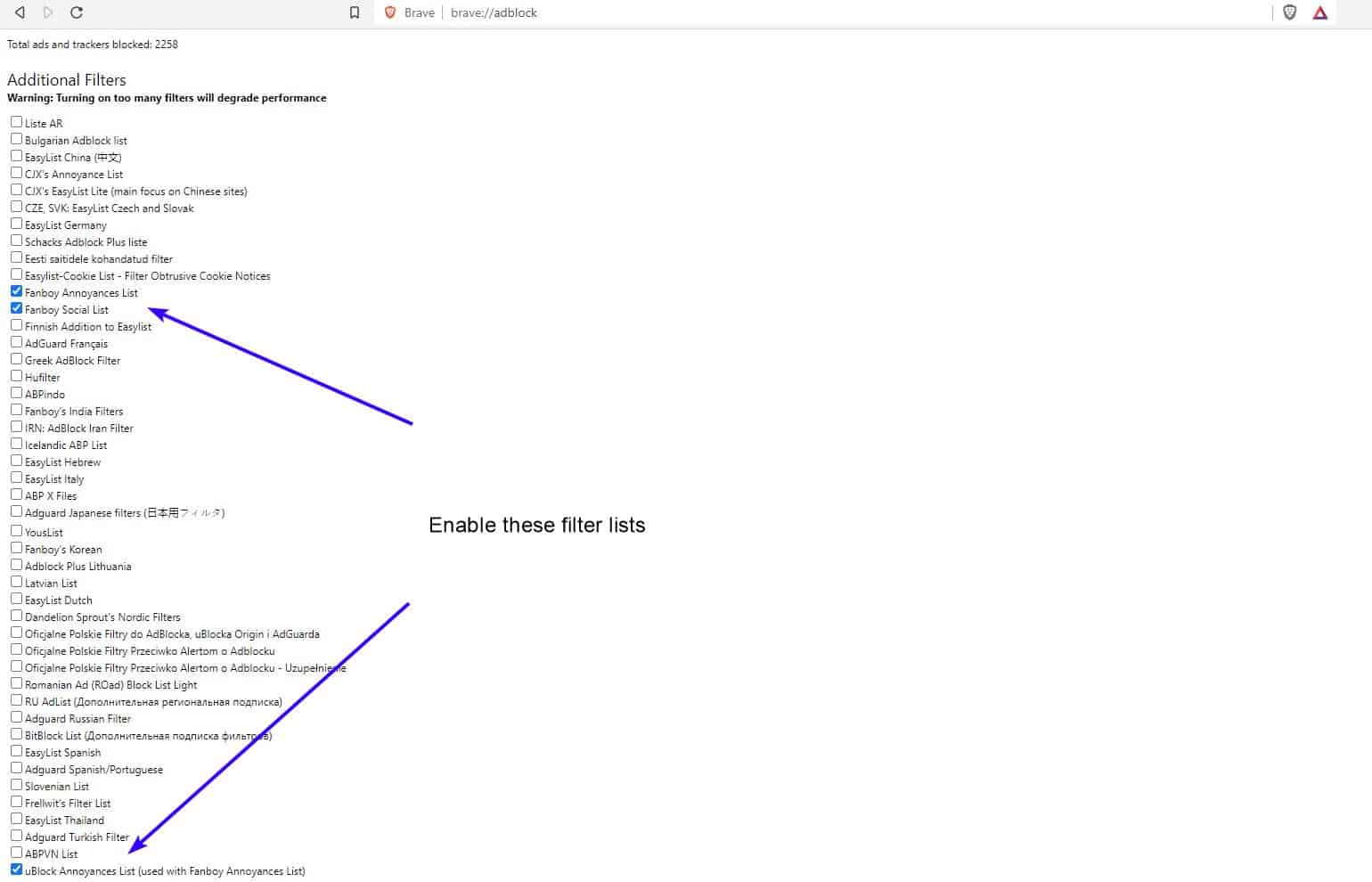
How to enable uBlock Annoyance List, Fanboy annoyances List and Fanboy Social list in Brave browser
To activate the new filter lists, head to the following page.
brave://adblock
The settings aren't listed in alphabetical order, so you may have to search for them manually. The uBlock Annoyances list appears at the end of the list for me, wile the Fanboy Annoyances List and Fanboy Social List are located in the top half of the list.
Check the box next to the option that you want to use, and you're good to go. I wouldn't recommend enabling all the options available on that page, since it could result in heavy resource usage and also prevent websites from loading correctly. So, you should only enable the ones you actually need.
Technically, if you were using uBlock Origin specifically for these lists, you no longer need the extension. But the add-on does more than that and supports custom lists, filters, and elements, so you may want to keep it anyway. That's what I would do.
Tip: Firefox, Edge (and other Chromium-based browsers) users can enable these annoyance lists from uBlock Origin's dashboard > filter lists. You don't have to do this since the add-on does a great job out of the box, but the options are there if you want to enable them.
An issue filed on Brave's GitHub regarding support for the new filter lists was fulfilled in early December. This reddit thread says that the lists appeared in Brave Nightly 1.20.19, but according to a new post these options were added to the stable release channel in version 1.19.92.
If you don't have the new ad-blocking filter lists in your browser, check whether you have the latest version. Hey, I still see the social buttons on a website. Make sure that Brave Shield is enabled for the site, click on the icon next to the address bar, and also check if the first drop-down menu says "Trackers and ads blocked" (and not set to "Allow all trackers and ads").



















If you think most all the comments here about privacy are extreme and/or silly, and simply want to use the browser that works the best, then I suggest Edge.
But if you fear you’re life will be ruined because you’re not crazy enough about privacy, then perhaps Brave might be the placebo you need. Also, you might look to see if “they” put a chip in your head.
lol …you guys are arguing none sense. If you go online using a browser…any browser there is you will be tracked…there is no escape out of it. Weather Google, Microsoft or Apple Facebook does it…it matters not. Your ISP knows everything you do online. lol
What a senseless commen,. ISP is not a problem if they don’t sell cutomers data (with UUID), and if you’re concerned you can pay for a VPN (hopin’ that the evil google chromium “opensource” browsers don’t leak dns queries).
The real problem is mass surveillance from Evil GAFAM & friends, and this can be avoided (not so much with evil google chromium “opensource” browsers)… At least until they implement server-side tagging!
@SpywareFan – “ISP is not a problem if they don’t sell cutomers data”
That’s a big IF…if you read the fine print you would realize all ISP’s do collect data and sale them.
@SpywareFan – “and if you’re concerned you can pay for a VPN”
Why in a world would one want to use a VPN for? don’t you know that all VPN providers are lose canyon…No one really knows who’s behind a VPN…you basically trusting someone else from god knows where to keep your browsing and everything you do online private…lol that’s a NO…NO..Go.
Two guys on opposite sides of a street were arguing over who had a bigger knife. It got to be a very heated discussion and resulted in them both starting to cross the street towards each other, intent on proving their point in a knife battle…
They both got hit by a bus.
Period.
Which browser is the bus? Haha
what’s wrong with that? C’mon…
>https://github.com/brave/brave-browser/wiki/Deviations-from-Chromium-
>(features-we-disable-or-remove)
Thanks for pointing out it!
@Iron Heart
1) Does this change your Brave setup recommendations?
2) You mentioned that you are trying to deGoogle by using Brave, DuckDuckGo and not Gmail, what are you using in place of GMail?
@Anonymous
1) No. The more adblocking lists you enable under brave://adblock/ the better. uBlock Annoyances and Fanboy’s Annoyances are great lists to have.
2) Tutanota. Only works within their own mail client (available for all major platforms) or their own website, though. Other good services include e.g. CounterMail (perhaps too weird to set up, admittedly) and Posteo.
This happens to be rather informative, concerning email services: https://digdeeper.neocities.org/ghost/email.html
“Since Chromium-based browsers lack the power of Firefox containers…”
I recently discovered “SessionBox” which has similar functionality as Firefox containers. It’s a freemium extension. Unfortunately the free version is not as elegant as Firefox containers. The paid version is a subscription service with gives you more functionality but seems to be targeting enterprise. I can’t justify the cost.
https://chrome.google.com/webstore/detail/sessionbox-multi-login-to/megbklhjamjbcafknkgmokldgolkdfig?hl=en
I just like to add –after reading a lot of posts regarding Brave vs. Firefox and FP– just this:
in principle, It does not matter which browser is best as default because companies tracking users just use anything to get you.
However, if you think is more recommended to go with default settings, do it but I rather disabled all that is irrelevant, tweak things to minimize attack surface. Because that is a bigger problem than FP, IMHO.
Last, if want a simple solution, try this: use an add-on like uMatrix, turn off Javascript, cookies and third party sites. An only turn them on specifically on sites you need it (sites you probably log on, so they already know who you are.)
My two cents: in the end, it doesn’t really matter how much technical wizardry Firefox has (and some of it is genuinely impressive). What really matters is how well the web works for you, and – objectively speaking – the web is a WebKit/Blink world now.
@ShintoPlasm
The “technical wizardry” of Firefox is mostly concepts stolen from other people. For example: FPI? Safari began to implement this, like, seven years ago. And yet the fools in this comment section celebrate it as if Mozilla had just discovered the fire. My god… You can only celebrate this if you are totally ignorant of most tech news. I am being serious here.
> Safari began to implement this, like, seven years ago.
Doesn’t matter, I only care that the feature is available on Firefox, while various Cripplemium knock offs will have it, like, never. Because they’re specifically designed to be anti-privacy, among other reasons.
@Brass Spleen
1) Safari isn’t even Chromium, it’s WebKit-based. Those two projects do not have that much to do with each other these days.
2) Chromium isn’t specifically designed to be anti-privacy. It’s designed to be a web browser that implements web standards. The web standards themselves, how they are drafted, is problematic. One particularly egregious example is WebRTC – it’s problematic in Chromium, but it’s also problematic in Firefox or in any other browser which implements it. If you mean the connections Chromium establishes to Google – there are ungoogled builds for that, like Vivaldi, Ungoogled Chromium, or Brave. Problem solved.
You might not care when Firefox gets what, but I really wonder what that has to do with it being a ripoff and not an original Mozilla intervention. Frankly, I don’t care that you don’t care – just don’t celebrate this as a novelty when it clearly isn’t.
> Safari isn’t even Chromium
Good thing no one’s saying it is then. If this is the way you read your “research papers”, it certainly explains a lot.
> One particularly egregious example is WebRTC
Maybe you could just disable it… Oh wait.
> If you mean the connections Chromium establishes to Google – there are ungoogled builds for that, like … Brave.
Brave’s absolutely not ungoogled. I suppose you could manually disable garbage like Safe Browsing, but that would go against your mantra of supposedly sane defaults, wouldn’t it.
> but I really wonder what that has to do with it being a ripoff and not an original Mozilla intervention.
The point being people in general don’t care whether a different browser on a different OS had a certain feature years ago – what’s important is that my setup provides the feature right now.
> just don’t celebrate this as a novelty when it clearly isn’t.
I’m afraid you might be making something up only to be mad about it.
@Brass Spleen
> That may be the case, but at least I won’t be spending my free time prancing around, convincing myself how wonderful that is.
I don’t need to convince myself, or anyone, of anything. I think the market developments of the last decade prove me correct. If Firefox was such a good product, it wouldn’t have plummeted from 30% market share to 5%. It was horrible performance and stability-wise for years and is still playing catchup.
> I mean, it probably can’t hijack your referral links, but you know.
Firefox “hijacks” any kind of search you perform of it with a referral, you fool. This is not unique to Brave and is a legitimate and privacy-neutral means of funding (which is why I never criticize it despite the fact that every major browser vendor does it).
Firefox on Android has literal trackers built-in, you can’t claim any kind of moral high ground even if you tried: https://old.reddit.com/r/privacy/comments/blt6ft/mobile_firefox_app_shares_your_data_with/
If the moral high ground is important to you, you shouldn’t be using Firefox. Just saying.
> Good thing no one’s saying it is then.
Me: Safari had it before.
You: Firefox gooooood! Chromium will never have this!
Me: Safari ain’t Chromium, pal.
You: Whoever claimed this?
> Maybe you could just disable it… Oh wait.
Dude, I was pointing out that how the web standards are drafted is problematic, not the browsers themselves for the most part. Whether or not it can be disabled (and WebRTC can be disabled in any browser, if you know how) wasn’t even the topic.
> Brave’s absolutely not ungoogled.
It absolutely is:
https://github.com/brave/brave-browser/wiki/Deviations-from-Chromium-(features-we-disable-or-remove)
> I suppose you could manually disable garbage like Safe Browsing, but that would go against your mantra of supposedly sane defaults, wouldn’t it.
SafeBrowsing is a security feature and it’s fully understandable why they wouldn’t disable it by default, for all users. They also proxy requests to SafeBrowsing through their own servers, genius:
https://github.com/brave/brave-core/pull/108
Anyhow, Firefox is much more “googled” than Brave:
– Uses SafeBrowsing as well (this time non-proxied, lol)
– Uses Google’s location service
– Promotes Google Search by setting this as the default
– FF on Android comes with a Google Ad ID and a hardcoded Google Analytics tracker
– FF uses Google Analytics on the internal add-ons page and for Activity Stream
And you complain about “googled” based on proxied requests for a security feature… Would be funny if it weren’t so sad.
> I’m afraid you might be making something up only to be mad about it.
Dude, you were the one writing a salty reply to my 100% true statement. What goes around comes around, no complaints accepted.
> I don’t need to convince myself, or anyone, of anything.
QED.
> If Firefox was such a good product, it wouldn’t have plummeted from 30% market share to 5%.
Ah, yes, because the market share is always reflective of technological superiority. That must be why the general public is largely running on the Windows PC/Android phone combo.
> Firefox “hijacks†any kind of search you perform of it with a referral, you fool.
Which is obviously a nuisance, but at least it happens a predictable way and it can be configured. As opposed to the user being randomly used to earn the latest shiny Shitecoinâ„¢.
> This is not unique to Brave and is a legitimate and privacy-neutral means of funding
Lmao.
> Me: Safari had it before.
> You: Firefox gooooood! Chromium will never have this!
> Me: Safari ain’t Chromium, pal.
> You: Whoever claimed this?
Well… yes, that’s how the exchange went on? Your point being?
> It absolutely is:
_Some_ of the Google “features” removed =/= ungoogled browser
> SafeBrowsing is a security feature and it’s fully understandable why they wouldn’t disable it by default, for all users.
No arguing about that, it’s a browser targeted at non-technical users who don’t value their privacy that much after all!
> They also proxy requests to SafeBrowsing through their own servers
And that’s supposed to make me feel more secure, is it?
> Anyhow, Firefox is much more “googled†than Brave:
Yeah, I just, you know, disable these/use the F-Droid build on Android.
> Dude, you were the one writing a salty reply to my 100% true statement. What goes around comes around, no complaints accepted.
Well, there’s no clearer way of saying it. your “statement” about people celebrating FPI as a novelty is a load of bollocks. All people are saying is it’s an advantage over Cripplemium&co.
@Brass Spleen
> Ah, yes, because the market share is always reflective of technological superiority.
Chrome pioneered multiprocessing, and its Javeascript engine left Firefox in the dust for years. Its sandboxing is superior. Better dev tools. Better everything. So yes, technical superiority, which also extends to all other Chromium-based browsers.
> it can be configured.
Nope. Unless by “configured” you mean never using Google Search within Firefox again.
> As opposed to the user being randomly used to earn the latest shiny Shitecoinâ„¢.
Dude, Brave and Binance were and are officially partners. It’s not hidden, either, you can find it on their website.
You also help Mozilla get $$$ from Google whenever you perform a search within Firefox, why are you such a hypocrite? Developers need to eat, if it can be done without violating user privacy, great. Referrals are one example of how it can be done without violating user privacy.
> Lmao.
Static referrals are legal and have zero privacy impact. There are worse ways of getting funding. Very funny indeed.
> _Some_ of the Google “features†removed =/= ungoogled browser
If you are trying to ride the fact to death that Brave keeps SafeBrowsing (like Firefox, haha), then I can only say that I’ve already explained their reasoning to you. SafeBrowsing is beneficial from a security point of view, hence why it was kept, while other (useless) parts connecting to Google were not.
> No arguing about that, it’s a browser targeted at non-technical users who don’t value their privacy that much after all!
If keeping around SafeBrowsing is your criterion for being “non-technical” and “not caring about one’s privacy that much”, then I can say the same about Firefox users. Firefox has Google SafeBrowsing enabled by default. Again I have to ask: Why are you such a hypocrite?
> And that’s supposed to make me feel more secure, is it?
As far as any concern of leaking data to Google is concerned, yes. By proxying the connection, they are introducing an anonymization layer between you and Google.
> Yeah, I just, you know, disable these/use the F-Droid build on Android.
I can disable this in Brave as well, and it has much fewer Google connections to begin with. Again: Why are you such a massive hypocrite?
> Well, there’s no clearer way of saying it. your “statement†about people celebrating FPI as a novelty is a load of bollocks.
Ah, you think? The usual Firefox fanboy gathering places celebrated it recently as if humanity had just discovered the wheel.
> All people are saying is it’s an advantage over Cripplemium&co.
Sorry to break this to you, but: Isolation is a cross-browser development that web devs also have to adapt to. Chromium already isolates the cache and will isolate more things in the near future. Truth is, if Google wouldn’t have agreed to implement it (forcing web devs to adapt to it thanks to their market share), then it is likely that Mozilla wouldn’t have begun implementing it, either. Fact.
@Brass Spleen
Oh and by the way, you’ll be using “Cripplemium” (the most crippled browser out there is the Android version of Firefox, lol) as well, things are not looking too rosy for Mozilla (upper management still gets an undeserved pay rise, though):
http://calpaterson.com/mozilla.html
People have left the sinking ship in droves over the past few years, and this trend is unlikely to reverse. Have fun while it lasts.
> you’ll be using “Cripplemium†as well
That may be the case, but at least I won’t be spending my free time prancing around, convincing myself how wonderful that is.
> the most crippled browser out there is the Android version of Firefox, lol
Fenix might be an abortion of a release, but there’s no doubt it still has more features than, say, Android Brave. I mean, it probably can’t hijack your referral links, but you know. Lol.
> Have fun while it lasts.
Oh, I fully intend to, my man.
@IH:
In the world of IT everyone steals from everyone, and for most part that’s a good thing. I don’t deny your point about Firefox/FPI, although I’m not sure whether their implementation is the same as Safari’s (does Safari have dFPI?). Still, my main argument stands: it’s a Chromium world now, so whatever new (copied?) things Firefox includes, it’s like putting a plaster on a gunshot wound to the heart.
@ShintoPlasm
Yeah, everyone copies from everyone in the industry, it’s not a secret and that is not the point I am trying to make here. The point is that the most toxic browser community, which is arguably also the most toxic open source community in existence, sometimes needs a reality check. I am providing them with something invaluable here by giving them their daily dose of realism – it’s the only thing stopping this place from becoming another r/firefox. Believe me.
Good move from Brave. They have come a long way since their first version. I appreciate that Martin gives this info and hope he will continue to do it.
Some people ignore this. How sad.
@Klaas Vaak
That rule is only being enforced for some.
@Iron Heart: hi, long time no speak, good to touch base. I was referring to some of the characters here became a bit abusive to you. Oh well ……
Interesting discussion between you and Pants, who is defending FF and cannot stand any criticism of it.
I just noticed yet more comments that I have not read yet.
Anyway, good replies from you. I am still on Brave.
> and Pants, who is defending FF and cannot stand any criticism of it
I can stand criticism of Firefox – it’s part of what makes a critical thinker. I’ve never said Firefox shouldn’t be held up to scrutiny. What I’m objecting to is the misleading and false statements, the shilling, the totally useless comments (like who invented something .. WTF?), the relentless unwarranted bashing and repetitiveness of it all (it’s the same six or seven things: non-stop), usually off-topic .. in almost every single FF article, and the personal attacks (not just at me)
personal attacks: like claiming I’m unemployed, and constantly making false off-topic claims about the arkenfox user.js. To date, at least 30 IH replies to me have had to be edited because of claims about my coding that he cannot know
> IH: Get lost
No. You don’t get to dictate to me. When you post in a public forum, others are allowed to join in. If you keep posting stupid things, I’m going to call them out. If you keep going off-topic and attacking me, then I’m going to reply
If you don’t like it, then stop attacking me, stop telling lies, stop posting stupid things, stop going off-topic. You are the one who brought up containers/isolation, you’re the one who brought up the PDF, you’re the one who brought up the sandboxing, you’re the one who brought up fingerprinting and the user.js
You’ve had long arguments with three people alone in this article’s comments: me, Brass Spleen, Carl Gustav. You’ve had so many arguments with others in other articles. The commonality in all of this is YOU. Think about it. A simple article about Brave adding some blocklist changes: cool. Instead you start ranting about containers, firefox’s FPI/dFPI, sandboxing, CEO salaries, a Firefox user.js, fingerprinting, the contents of a PDF, and how cool it is to have hundreds of profiles
@Pants
– You bring up the same 6 – 7 things (all mountains out of molehills as per usual) about Brave, too. Stop being a hypocrite with double standards. At least my criticism of Firefox is not unfounded.
– You do it in an off-topic manner as well, under Brave articles. Exhibit 1: This comment section. Stop being a hypocrite.
– You are bashing anything that isn’t ‘holier than thou’ Firefox, stop being a hypocrite.
– You being unemployed was speculation on my part, because you seemingly have no time constraints on your personal crusade against me. Work would be such a time constraint.
– Your replies to me get edited as well and often, despite the favoritism going on here. Stop being a hypocrite. At least I am not inventing outright lies and conspiracy theories about the opposing party (you knpw exactly what I am referring too…), so I can still look in the mirror at least.
– You oftentimes try to “prove me wrong” by mixing up different things or by crafting deliberate misrepresentations. For example, I bring up containers, you mix the topic up with FPI (which is not the same thing), saying that I was wrong when I was not. I bring up the study, you say it is only about the phoning home aspect (because the title says so, and apparently you can’t read further and hope that others can’t, either), I prove this wrong by quoting from the study, you ignore it because the usual deflection tactics have failed again.
– I didn’t start “ranting about anything”, dear liar, I was addressing one single line about containers (which are not FPI) from the article, and that was on-topic because it was literally in the article. The following comments were all, without exception, me dealing with you and your acolytes, and I had to discuss several things because you(!) brought them up. Examples? You love to claim that I have no idea about fingerprinting, so I have to discuss it. You bring up your irrelevant user.js, so I discuss it. It goes on and on… You bring up these things, mostly in a provocative and insulting manner directly targeted at me, and then have the audacity to complain when I react to this, calling it a “rant” (wherever I “ranted” here, I can’t seem to spot it)…
– Another commonality in discussions between Firefox fanboys and me is not just the *me*, it’s also the fact that the opponent is always a *Firefox fanboy*. That’s true for you, Carl Gustav, Brass Spleen and so on… And the same ignorant arguments are found in all of those comments leveled against me. When I engage such people, it matters not that they might be different persons (Are they?) when the shit they are writing is all the same, all the time.
– Last but not least, it’s always the same 5-7 people I have to engage with because they claim shit about me and / or Brave, a majority of gHacks readers doesn’t hate me, and usually I have cordial exchanges with all the other commenters. Another thing worth thinking about.
If you think you can drive me from the comment section (which will subsequently devolve into r/firefox levels of fanboyism, no doubt), you are wrong. There is no way in hell I would let you get away with your trumped up accusations against me, or with promoting the privacy reduction script as if it was improving privacy for users when it really achieves the contrary! That would be an outright embarrassing, intellectually dishonest, and cowardly move on my part. Not going to happen. You either come to terms with me being here, or you choose to continue your little personal crusade against me (with the usual accusations and lies and hypocrisy attached to it). I don’t care either way.
You also should understand the following: In my eyes, you are not an expert, and you are no authority whatsoever. You are some random person with an irrelevant Tor copycat script erroneously applied to Firefox (see my other comments above), with the result being the destruction of privacy instead of its protection.
* [Editor: removed, don’t make unsubstantiated claims]
You are just a gal with a far too high opinion of herself, an opinion strongly mismatched to reality (reality being some irrelevant, privacy-reducing script). I don’t respect that, because why should I? That’s the most annoying thing about your comments here, you thinking that you speak with some kind of higher authority, however not having anything to show for it… I’d certainly respect you if you had Whonix dev level expertise (ironically, these people are laughing at your script, I wonder why…), but you don’t – this also explains why you engage me instead of them, because I am seemingly the easier target. You would never approach a developer in this manner because you know that you’d be chastised for it, so why not try it in the gHacks comment section, where the one-eyed can play king of the blind? This is SAD.
@Martin Brinkmann
Dear Martin, how inept can your censorship possibly get? She admitted to the fact that she has never written a line of code already(!!!!!), and you know yourself that it’s not the only privacy reduction script out there. You also never censor stupid ass claims she makes about me, even if they are 100% conspiracy theories. I have to specifically request deletion when that happens, like, always.
Yeah, no favoritism at all. What a shit show this sometimes is.
> She admitted to the fact that she has never written a line of code already(!!!!!)
I did no such thing
> Proof
I’m not doxing myself to you. Get this into your head. I have MANY handles, including my real name. I use many platforms, including mailing lists. I have many contacts and email is a thing. I am private by nature. Just because you can’t link the public real me to “Pants” is BY DESIGN. A lot of it is private anyway, and I’m simply not going to divulge it.
I’m more than happy to provide Martin with proof: receipts of travel and events, emails, private github conversations, hidden access denied tickets (with some redactions): but I do not need to because it is IRRELEVANT
Here: look at this: https://github.com/brave/brave-browser/issues/12069#issuecomment-771369004
Peter indicated that the ticket, marked as a P5 (super low priority), as resolved because of something else. When I saw that I talked to him again (this time via a private github repo), to illustrate that it wasn’t fixed (it actually makes canvas completely by-passable). It was only THEN that he realized what it was that I said all along, and he apologized for mistaking my PoC and original email: it was immediately re-opened and a patch applied the SAME DAY – clearly not a P5 then.
I do not make things up. Do you still think I am lying when I said “finding exploits in Brave or RFP to be patched (and the Brave one was serious once Peter realized what I was saying: I have proof of that too: once realized he fixed it with hours)”?
There’s only so much I’m willing to share with you: for starters I cannot trust you given your hatred and animosity. secondly, you wouldn’t understand it. Thirdly, you’d use it against me: dox me, spam me or something.
NO. WAY. AM. I. REVEALING. THE. REAL. ME. TO. YOU.
Do I constantly ask about your coding skills, or your body of work, or what you do all day? No. Grow up and behave like a normal human being please
> user.js
You’ve said three times now that Whonix are laughing at the script: where? who? show me? You’re making it up
Nowhere have I argued anything contrary in any of your links
First: it actively and explicitly tells users to use Tor Browser if it fits their needs: casual browsing right down to whistleblowers. Of course a enforced set of users is much better
– At no point have I said that a disabled API doesn’t provide a metric
– At no point have I said that changing prefs in Firefox can’t affect fingerprints
– At no point have I said that extensions can’t affect fingerprints
– At no point have I said that an enforced set of users (e.g Brave at default, or Tor Browser, or Whonix) is not required for anti-fingerprinting to work best (e.g advanced scripts)
– and.. at no point has the user.js ever claimed to beat fingerprinting scripts
Here’s what it says
“The arkenfox user.js is a template which aims to provide as much privacy and enhanced security as possible, and to reduce tracking and fingerprinting as much as possible”
That’s it. That all it states that it does. And it does exactly that: including reducing fingerprinting (see naive scripts, and the fact that doing nothing you are already unique: the user.js can hardly make that worse)
The user.js is not trying to hide it’s fingerprint, it’s almost impossible against an advanced script without a universal buy-in. Brave has theirs on by default but lack enough metrics. Firefox covers almost enough metrics but is not on by default. Both when on fool naive scripts, which make up the bulk of the scripts out there (pretty sure from memory that Peter has said this, as well as OpenWPM crawls, etc: you can grab lists of known FPing scripts and inspect them you know). Therefore the user.js, with RFP, DOES reduce fingerprinting – no-one ever said in all cases
Your claims that it does nothing for privacy are ludicrous
And all the added privacy measures are NOT NEGATED just because an advanced script MIGHT get through and fingerprint the browser on a few sites. The browser is ALREADY unique doing nothing (Firefox webgl alone on windows with the right script hits about 98% of users as unique). And the two identical hardware setups is a myth as well (I’d explain why but you wouldn’t understand)
And you’re overplaying the FPing script: first it has to get through, and then it ALSO needs to be universally widespread to be of any use. Granted, it’s useful for first parties, but the threat is a lot less than you’re making it out to be
Don’t talk about things you do not understand. Your knowledge on entropy and how linkability works is appalling. You should stop advising people here immediately and refrain from posturing as an expert: pointing at articles by others and misinterpreting them with wild misleading generalizations does not help anyone
Pants did provide proof and it is impressive and certainly backs up her expertise.
@Martin Brinkmann
I don’t care. Reasons:
1) Provided someone knows lots of things about fingerprinting, that doesn’t mean that it is a good idea to apply that to Firefox, since Firefox by default doesn’t protect against fingerprinting. Again, I can detect these defenses and I can detect that it is not Tor. This is idiotic and totally undermines the intended effect.
2) Firefox not doing it by default is a problem, and several experts in the field, including the devs of Whonix and Tor, agree with me here. Tor having a different default configuration solves these issues, but then again, Pants’ users are not Tor users and this can be 100% detected.
3) Why does the user.js even exist as a separate entity? It rather mindlessly imitates Tor, and one can already use Tor. It also gets the majority of its info from Tor. Imitating Tor is a bad idea because it is not Firefox’s default behavior and Firefox and Tor can be told apart.
4) Pants is not the one implementing these defenses and by default ranks below the people doing the heavy lifting. She doesn’t understand the defenses at the code level.
5) All of that is totally irrelevant because Firefox won’t exist anymore in a few years. When Firefox becomes irrelevant (bound to happen), Pants will become irrelevant (more so than she already is, I don’t see many people using her script, compared to the total number of FF users).
Again: I don’t care about your special friend Pants, and have my reasons for that. Would be glad if she left me alone, and if you wouldn’t censor my posts in a one-sided, highly biased manner.
Whether or not something is edited out is up to you. It is quite easy actually. Also, you don’t know anything about the comment editing here and see only part of it.
Stay away from personal attacks, and yes, that includes suggesting that someone cannot code or is no expert, without providing any proof of that claim. Pants provided me with proof and it is solid. I did not ask for this, but I think everyone here on this site would appreciate it if the discussion would come to a fruitful end, e.g. by making suggestions or whatever, or by just admitting that there is no point in going on.
@Pants
> I did no such thing
Yes, you did. Not that you need to, however, since we already know that your GitHub history is pure emptiness – despite the projects you are attached to being on GitHub. If you had contributed anything, we would know of it by now.
> I’m more than happy to provide Martin with proof
Don’t care, and why should anybody else care. Provided such “proof” even exists (I strongly doubt it).
> Peter
Yeah, whatever. Brave’s (and Firefox’s) anti-fingerprinting implementations receive patches all the time. You found that Brave leaked a real value via some testing suite? Great, cool, whatever. Am I supposed to celebrate that? You were not the one patching it in the end, were you? Such reports hit Brave Software and Mozilla on a regular basis.
> Do you still think I am lying
I never said that you were unable to operate a testing suite. It’s just not something I have any kind of respect for – anyone can do that, with little prior knowledge.
> for starters I cannot trust you given your hatred and animosity
That goes for me as well, lol.
> Thirdly, you’d use it against me: dox me, spam me or something.
Boy, you have lots of imagination. Firstly, you are totally irrelevant to me. I don’t care about you. If you weren’t spamming / doxing MY POSTS, I would likely forget about you. Secondly, I have never doxed your virtual self, either. Noticing that your GitHub history is empty took me one (1) click, hardly doxing in my book.
> NO. WAY. AM. I. REVEALING. THE. REAL. ME. TO. YOU.
OK, then reveal the “work” you’ve done under other pseudonyms, I’d likely recognize your nasty self. It’s not like I want your passport and home address, haha. Pointing me to some achievements of yours conducted under a pseudonym would be enough.
By the way, your virtual self already tells me the things I need to know about you (no GitHub contributions, privacy reduction script, heaps of time on your hands etc.). I do not need to know your real identity to see any of that.
> Do I constantly ask about your coding skills, or your body of work, or what you do all day? No. Grow up and behave like a normal human being please
Yeah, I am not posing as an expert here, you do. I just want to see some stuff that would back up your self-grandiosity, and I am sure I am not the only one.
> You’ve said three times now that Whonix are laughing at the script: where? who? show me? You’re making it up
Oh, you forgot about it already? No problem, posting it again:
https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
“Madaidan” is a leading Whonix dev. Doesn’t seem to praise your work, eh? Why not take the fight to them, dear * [Editor: removed, stay polited]? Show them your so-called expertise and how they are wrong, personally I can’t wait for that. Your skill level certainly matches theirs, according to your last comments here.
> Of course a enforced set of users is much better
Thanks for admitting it. Only took you 10 comments this time.
> At no point have I said that a disabled API doesn’t provide a metric
I said this repeatedly in my comments when you were still talking about “reduced attack surface”, just because the number of reported values goes down when you disable an API. Bean counting is not efficient here, however. WebGL being enabled (and several values leaking as a result) is not as bad as disabling it on Firefox, you are automatically more unique even tough the absolute result count was reduced.
> At no point have I said that changing prefs in Firefox can’t affect fingerprints
I said this repeatedly in my comments, and yet you still don’t understand that your user.js creates a unique fingerprint.
> At no point have I said that extensions can’t affect fingerprints
Cool, me neiter.
> At no point have I said that an enforced set of users (e.g Brave at default, or Tor Browser, or Whonix) is not required for anti-fingerprinting to work best (e.g advanced scripts)
Ah, so you admit that Firefox not having FP defenses on by default (resulting in people having it on by default being a minuscule minority) is a problem? How come?
> and.. at no point has the user.js ever claimed to beat fingerprinting scripts
It aims to defeat FP scripts, that it not always succeeds in this is self-explanatory. Brave doesn’t succeed in all cases, either. It comes with the territory and is hardly an argument.
> The arkenfox user.js is a template
If users really take your “template” talk seriously, they’ll be even more unique than they would be already by applying your script. Users of your script are a tiny minority already, and users running that script in a modified fashion are even more unique than that.
Furthermore, your “template” talk is already proven wrong by the fact that you are considering usability (if in an insufficient manner) when creating your script, such considerations would be unnecessary in a real template from which users pick what they like / need (hopefully not, as I said, that would be even worse than outright applying your script).
> The user.js is not trying to hide it’s fingerprint, it’s almost impossible against an advanced script without a universal buy-in.
You see, even a primitive script only checking for WebGL and a small range of other things would already be enough to identify your users – that’s how heavily you alter the fingerprint any given Firefox would normally produce.
> Both when on fool naive scripts, which make up the bulk of the scripts out there (pretty sure from memory that Peter has said this, as well as OpenWPM crawls, etc: you can grab lists of known FPing scripts and inspect them you know).
I still remember you screeching for proof when I said some time ago that the grand majority of scripts are primitive (and for which Brave anti-FP is good enough most of the time) – I pointed to the fact that such databases exist, you ignored it, now you provide the very same proof yourself, you snake. That’s how dishonest you are. Not saying that what you say here is wrong (I am aware of this, too), I am just appalled at your methods.
> Your claims that it does nothing for privacy are ludicrous
Correction: I didn’t say it does nothing for privacy (which would be neither good nor bad), I said that it actively REDUCES privacy by creating a highly unique fingerprint for FF users. And I stand by that – the only result is a highly unique fingerprint. It’s not only me saying this, either. The Whonix project (you know, the OS often used by dissidents fering for their lives) says it, too.
> The browser is ALREADY unique doing nothing
…but still less unique than if your script were applied, believe me.
> And the two identical hardware setups is a myth as well (I’d explain why but you wouldn’t understand)
It’s not a myth. There are only so many things that can differ on identical hardware. Hardware concurrency wouldn’t differ, anything related to the GPU wouldn’t differ, RAM wouldn’t differ, screen solution (both browsers maximized – I realize that window dimensions are a threat) wouldn’t differ. Fonts wouldn’t differ, unless the user installed new fonts (except maybe those of MS Office, which is widespread enough not to matter). Battery would be a threat, but only on mobile devices.
I can identify different hardware on the network level (MAC address), your script stupidly suggests turning off IPv6 in response to that (instead of, you know, randomly spoofing the MAC address, but whatever). The fake MAC address would be the solution, however, I can detect that someone falls back to IPv4 when an IPv6 connection would the default, and fewer and fewer people fall into that category. While the fake MAC address isn’t sticking out, your users increasingly do. What I am saying is that your script is also messing up at the network level, where identification of different hardware could be done in the easiest manner. That also includes timing attacks, but they are too resource-intensive to be carrie out on a wider scale.
Network-level identification of different hardware would be easier than (oftentimes unreliable) results from fingerprinting identical hardware, but your script messes with that, as well. It’s so messed up, seriously.
> And you’re overplaying the FPing script: first it has to get through, and then it ALSO needs to be universally widespread to be of any use. Granted, it’s useful for first parties, but the threat is a lot less than you’re making it out to be
Yeah, remember when I said the exact same to you? You then went on and on about how your script is supposedly a “comprehensive solution” (while in fact just resulting in a highly unique fingerprint), in response to me pointing out that scripts are not that varied in the wild (likely most of them get blocked by an adblocker) and that it would have to target Brave’s weaknesses. You were in total denial of that, now you are pointing it out yourself. Cool. It’s obviously only correct when Pants says it – as always.
> Don’t talk about things you do not understand.
You don’t understand shit, either:
– Produces a script that among other things is meant to combat fingerprinting, but doesn’t understand that it makes users more unique in the end.
– Talks about being identical to Tor’s fingerprint but fails to realize that Firefox and Tor can be told apart on the network level.
– Doesn’t understand that WARs are not the only way to detect extensions when behavioral patterns are a thing.
– Doesn’t understand that the web compatibility implications of randomization are lesser when compared to the “everyone looks the same” approach, hence why the letter approach is hard to maintain.
– Fails to understand that the fact of using Firefox alone already is pretty special these days (not in a good way).
– Fails to understand that security is relevant as well (many deanonymizations are facilitated by weak anti-exploit measures).
– Generally has zero idea about the network fingerprint.
– Doesn’t know what an unsolitcited request is, fails to stop it when it appears (because coding skills beyond about:config would be required).
And so and so forth…
> Your knowledge on entropy and how linkability works is appalling. You should stop advising people here immediately and refrain from posturing as an expert:
My gal, I am not the one playing expert here. That would be you. And you lack the skill to pose as such.
> pointing at articles by others and misinterpreting them with wild misleading generalizations does not help anyone
I don’t get the impression that I come up with “wild generalizations” here, but OK, whatever.
When you devolve to name calling “fanboys”, no one can take you seriously
> You are bashing anything that isn’t ‘holier than thou’ Firefox
Not so. I’m bashing YOU. Not my fault you keep repeating the same stupid things, and always about Firefox
> under Brave articles. Exhibit 1: This comment section
I didn’t bring up the topics of PDF, sandboxing, containers/FPI/dFPI, user.js, CEO salary, etc. YOU DID!
> I bring up containers, you mix the topic up with FPI (which is not the same thing)
See, more lies. It was all totally on topic as a factual reply to your nonsense, not mixing it at all. YOU claimed using hundreds of profiles was cool (lulz, so cool bro), and that containers did not isolate favicons. I pointed out that they did because they ARE THE SAME (95%) as the other OAs, e.g. with those aforementioned favicons: and that FPI/dFPI (also OAs) are alternatives to your fun times of using hundreds of profiles
Pro Tip: fact check yourself before opening your mouth
> I don’t respect that, because why should I
I don’t want your respect. Your respect is worthless to me. And you know nothing about what I have and haven’t done: I don’t see you being flown around the world all expenses paid for your fingerprinting knowledge, I don’t see you being emailed (unsolicited) and having private conversations on github about upcoming changes in Brave’s anti-fingerprinting (this time on fonts), I don’t see you building multiple new-or-independent PoCs, I don’t see you collaborating to actually get things done upstream at a browser level, I don’t see you reading thousands of articles and hundreds of research papers on the topic, I don’t see you being asked for advice on a new FPing technique by an independent researcher (a well known published one, like I was yesterday), I don’t see your suggestions being implemented into Firefox’s RFP, I don’t see you finding exploits in Brave or RFP to be patched (and the Brave one was serious once Peter realized what I was saying: I have proof of that too: once realized he fixed it with hours) .. in fact, I don’t see you in this field at all (you’d be easy to pick out due to your lack of knowledge). I talk to people in the fingerprinting field all the time and have done so for almost a decade. Trying to talk to you about it is like going back to the stone age.
And I can prove all that about me (except the reading part), but I don’t need to, because it’s irrelevant: I deal in FACTS .. follow the FACTS
I only want you to acknowledge the FACTS, well not even that: I’m content with just rebutting your stupid comments so at least readers can make their own mind up: I give these FACTS to you all the time, but it seems in your burning hatred, you can’t hold a conversation and keep quadrupling down: that’s not MY fault
Already you have just claimed I copy tor browser, that I have no body of work except one script, that I do nothing but comment on here because I apparently have oodles of free time. You’ve implied, nay, stated that I must be unemployed. All that has nothing to do with FACTs that are presented. Instead these are personal attacks. I don’t claim irrelevant facts about your life, do I? I only make observations on your posts here. And now you’re implying that I’m posting as three people. Yeah, right!
I thought there was a crack down on personal attacks. That one edit, Martin took out a four word, genuine question from me, and that was it. “How d _ _ b are you?” seems extremely reasonable in the light of your last comment, which just shows you reverting to your nasty type when you can’t “win” or someone else has an opinion – I mean, look at your nasty reply to the lego dude who was just declaring his glee of firefox awesomeness. I see Martin has already edited a heap of your posts in this thread alone. You’ve had at least several hundred edits for being a [editor: insert nasty word here], not to mention numerous deletions
Because you don’t like being wrong, hate Firefox with the passion of a thousand burning suns, and can’t abide ANYONE ELSE’s opinions, you keep making personal attacks and being rude
– “Firefox fanboy” sadly is not name calling, it is, as you would say, merely “my observation of your comments”.
– Thanks for admitting it is a personal crusade of yours: “I’m bashing YOU.” – Wasn’t obvious at all.
– Even if I did bring up some topics… Dude, I am allowed(!) to do this when I feel it’s applicable. And so are you! I am bringing stuff up in reaction to others claiming bullshit as per usual. And as everyone here can see, most of my replies were just myself dealing with your nonsense. Thanks for hijacking yet another article with your trolling of my comments – it’s trolling, not FACTS (I know you like this word written in capital letters), because you are highly dishonest in your so-called refutations.
– I don’t see any proof of any achievement of yours that exceeds the irrelevant user.js that can be found on GitHub and which effectively reduces privacy when applied. I don’t see any code contributions in your entire GitHub history – despite the fact that the project you are attached to, Firefox, has its code on GitHub. So if you had ever contributed any code portion, something would be visible there. And… Nothing, emptiness, nada. Zero contributions.
– Therefore, and because of the fact that you actually reduce the privacy of the users of your script, instead of listening to experts like the Whonix devs who are laughing at your effort, I don’t believe you have any kind of expertise that exceeds having read some studies and maintaining your user.js with the kind assistance of the Tor project’s docs.
– You claim lots of stuff about your expertise in the field, but I can’t verify anything of it. (@Martin: Wouldn’t that be another case of “unsubstantiated claims”?) When I asked you some time ago to point me to any kind of major effort that you were a part of, you were not able to, using my supposed unworthiness to look at your most sacred work as a sad excuse. Not questionable at all, you see. Those are the FACTS.
– “flown around the world” – for a person so occupied with her (presumed) work, in a field that constantly evolves no less, you seem to have a great amount of time on your hands, so much so that you troll my posts here and find the time to keep around a complete protocol of my posts. Yeah, not buying into it. Sorry my gal. Too much suspension of disbelief required for that.
– You seem to have that odd idea that you are allowed to keep coming back here, troll my posts (despite having no oodles of free time for that, of course), while I am not allowed to react to that at all. When I react, you call it “quadrupling down”. Well, you are “quadrupling down” as well when you leave your work for hours on end to monitor this comment section and engage me repeatedly. How is that not “quadrupling down”? Oops, I forgot, you are a white knight protecting the FACTS of course – you never lied about anything here at all, oh no… Pants would never do that, and it’s not a personal crusade at all, it’s just fact checking for the betterment of humanity! Seriously? Your posts here speak a different language entirely.
– You whine about me supposedly “claiming” things about you – that your GitHub history has no commits in it and that you obviously have heaps of free time on your hand are not “claims”, by the way – but it is you who occasionally yet creatively invents most outrageous lies about me, such as me supposedly having agitated the moderator politically while also harshly insulting him in the process (LOL, if true, this would have earned me an insta-ban here), but you had no post you could point to to prove it – this was so obvious a lie that it hurt. And yet you complain about me “claiming” things that are aready 100% obvious to anyone following you. Sorry, but the kind of moral high ground you believe to have is lost to you by now.
– I am not here trying to “win” anything. I have an opinion different from yours, and I have good reasons for not using Firefox. You can’t have that, come back again and again, harassing me and molesting my posts. It’s also obvious as f__k that you are specifically targeting me because you are on a personal crusade (not that I care, just pointing it out).
Pants, going by the unsubstantiated claims (no sources given at all) of your last comment, I think you have lots of other things to do, I think your irrelevant user.js needs your attention – contrary to me, you see.
@Klaas Vaak
What annoys me to no end in those endless and tiresome Brave vs. Firefox discussions is the following two things:
1) Before even discussing Firefox and Brave in terms of “privacy protection”, you’d have to ignore other aspects like security, performance, and web compatibility – in all of which Brave (or really any Chromium-based browser) totally beats Firefox. When you discuss them as equals, you have implicitly declared all of those aspects as irrelevant already, showing how skewed and one-sided, non-holistic the discussion is before it even started.
2) In order to achieve parity with Brave, you have to modify Firefox’s default configuration. Whenever such a modification relates to the web as such (I mean stuff that goes beyond disabling the invasive telemetry or SafeBrowsing of Firefox – this is not detectable), it becomes visible to scripts, and people who have modified Firefox “for the better” are only a tiny weeny part of the Firefox user base, meaning they make themselves highly unique by modifying it. Disabling things doesn’t “reduce the attack surface” because “nothing returned” is also a result that is being recorded, and it is a highly unique one for Firefox. Combine this with the fact that most people do not bother to protect themselves at the network level (e.g., real IP address leaks) and you have a recipe for disaster.
Pisses me off that the discussion is one of ignorance, and seems to be driven by fanboyism more so than by the pursuit of knowledge. If you really want to combat fingerprinting or in more general terms protect your privacy, Brave is the best clearnet browser to do so – because its default values are already sane and those default values are what most Brave users would go with. Tor is also good (not ideal for clearnet browsing), however imitating its configuration in Firefox is pointless because 1) why then don’t you just use Tor and 2) because I can differentiate between Tor and Firefox, meaning the “modified Firefox” users remain in their tiny weeny subset.
Good to meet you again, voices that maintain their cool and are rational are more than needed here.
“The truth is that Firefox is the most private browser by default”
I recently read a benchmark by someone who tested the first 10 seconds of several freshly installed browser’s connections at startup…
Firefox was at the top. I guess you become this deluded after reading so many about:config switches Mozilla shoves down your throat.
In addition to uBlock Origin, I like using:
StevenBlack /hosts
https://github.com/StevenBlack/hosts
I use uBlock Origin in pretty much all of my browsers (including Brave), but it’s good to also have a native way of implementing these blocklists in Brave, in case something bad happens to the Chrome Web Store version of uBlock Origin … which I gather is not out of the realm of possibility.
This isn’t a new development, but I guess it’s good to let the readers at Ghacks know.
Great article!
The link you shared (https://old.reddit.com/r/brave_browser/comments/lfoken/brave_added_annoyance_lists_fanboy_annoyances/) is so informative.
I can understand that most people try to block ads on browsers, but thesi is the last step to do. Better way is:
– DNS (some dns protect from malware and even ads)
– domain list, IP list (many tools, I suggest Acrylic DNS Proxy)
– PAC files
Optimistically, only blocking tools as umatrix should be used on browsers (with per site options for make them work), as long lists checks during site loading make most browsers run hard on memory/CPU
Do they block website elements as that’s why I use browser adblockers.
Fanboys Social List is included in Fanboys Annoyances List so you do not need to activate both. The Brave AD team says it’s recommended to use both, Fanboys Annoyances and UBlock Annoyances. Here is the quote:
“If you use Fanboy Annoyances, you won’t need Fanboy Social or Easylist Cookies. I would recommended using uBlock Annoyances also with Fanboy Annoyances”
best browser ðŸ‘
I know that it may come across as unusual for me to react negatively to news about Brave, but: The thing reported here is totally irrelevant. They add lists to the default list selection all the time, do you want to draft a report for every single occasion? You fail to report that the project has hit a new milestone, despite me pointing you to it…
https://brave.com/25m-mau/
…but then you report about irrelevancies like this one. It’s even an irrelevancy as far as its practicality is concerned; as you yourself pointed out, if I had wanted those lists, I could just have added them to uBlock Origin (which is a must have extension in brave anyway until they add support for custom lists). They are good lists, but an article on them being added? Seriously? Anyhow, what you report on is your business, not mine, but you seem to have great difficulty separating irrelevancies from actual news.
Also another minor gripe I have with this article:
> Since Chromium-based browsers lack the power of Firefox containers, which in my opinion offers better privacy, these annoyance lists are welcome additions for Brave browser users who want to prevent social-networks from tracking you.
Containers are about isolating local data, mainly stuff like cookies, localStorage, indexedDB, HTTP cache and so on and so forth – they have nothing to do with adblocking or anti-tracking lists, aside from the fact that both are privacy features:
https://wiki.mozilla.org/Security/Contextual_Identity_Project/Containers
You using containers in Firefox doesn’t mean that you suddenly don’t need an adblocker. Those are not the same thing, and containers do not lessen the need for adblocking. No idea why they are mixed up here.
Secondly, that there is no isolation in Chromium is not true. I can fully isolate different activities by using different profiles, either permanently or in a temporary manner. In case of Brave, its Tor mode is also its own full profile, meaning that what you do in there is also fully isolated from your other activities. Separation via full profiles is also stronger than containers because things like history (yeah, history sniffing is a thing…) and favicons are also isolated via multiple profiles, whereas no isolation of those would take place when containers are being used. Containers also can’t prevent your identification via fingerprinting; if Facebook fingerprints you on some website, you using a container when on facebook.com doesn’t stop them from re-identifying you – containers, while helping privacy as far as local data are concerned, do not prevent server-side re-identification and could insofar bestow upon you a false sense of privacy.
So IH basically opens every eTLD+1 in it’s own profile in order to gain parity with Firefox’s isolation/partitioning
– see https://www.ghacks.net/2020/12/13/brave-1-18-stable-launches-with-brave-today-global-privacy-control-support-and-more/
– from that link: I quote (just search for the word bingo)
> > [me] which means you’re advocating one domain per profile
> [IH] Bingo
Want to regularly visit 200 websites, no problems, just use 200 profiles (or you know, use a one off Tor window which makes you stand out as well since the engine isn’t Gecko/View: literally a 1ms JS check). Wow, all those profiles to maintain. And if they’re temporary ones: what happens to all the tweaks/settings changed for privacy… WTF happens to extensions like uBO? Seems like a stupid solution to me, outside of a few profiles to separate major components: such as banking, social media … OMG .. that’s exactly what containers are for. Siri: play “Ironic” by Alanis Morissette
EPIC FAIL to try and make Firefox and Tor Browser’s superior isolation/partitioning sound like it doesn’t do anything really, and it’s just as easy to have multiple profiles. The experts at Tor Project and Mozilla would like to have a word
– superior: because it covers far more than anyone else: in fact it covers everything needed to practically be a new profile
– FPI: has been around since FF52
—
> and favicons are also isolated via multiple profiles, whereas no isolation of those would take place when containers are being used
EPIC FAIL!! This is wrong
– look up what Origin Attributes are. They all function the same way: FPI is a type of OA, so is a container. They all isolate “networking” (like favicons, cache, image cache, dns, etc) as well as persistent web storage (IDB, localStorage, cookies, etc)
– Firefox now ships with a superior networking partition compared to all other browsers: so favicons are isolated with or without FPI/dFPI/containers/pb mode (yes pb mode is an origin attribute)
– here’s a list: https://groups.google.com/g/mozilla.dev.platform/c/uDYrtq1Ne3A : can you see the word favicon?
The truth is that Firefox’s Origin Attributes (being rebranding and tweaked as network partitioning and dFPI) is superior because you do not need to set up or create multiple profiles: meaning that extensions and tweaks/settings persist rather than fall back to default on new (temp) profiles, or on permanent profiles, having to maintain them all
disclosure: FPI works exactly as intended to block cross-origin logins that violate FPI (not all cross-domain logins break with FPI). This is expected. FPI is doing it’s job. As IH has said himself, to paraphrase: it’s stupid to use cross domain logins, but hey it’s a thing. This is true.
– Not everyone uses cross-domain logins, so FPI is perfect
– Additionally, as IH himself points out, you can use a second profile for those few problem sites.
– And lastly, dFPI will solve those cross-domain logins, but still allow users to switch to a more strict mode
—
> Separation via full profiles is also stronger than containers because things like history
History sniffing is practically impossible in Firefox due to timing mitigations, as well as the fact that all links are re-rendered regardless of visited status. It’s still possible given very advanced scripts and lots of time (these are very slow scripts), but highly unlikely as the payoff is extremely abysmal (needing to check each full URL individually)
@Pants
> FPI is perfect
LOL, FPI breaks cross-site login forms and causes reCAPTCHA hell:
https://www.ctrl.blog/entry/firefox-fpi.html
Perhaps you should evaluate if the “solutions” you propose actually work in the wild, as otherwise it’s just a useless mental game that is not beneficial to anyone. Yes, you’ll talk a lot about dFPI – I’ll discuss it when it has left its perpetual alpha state.
Separate profiles mitigate the problems because, lo and behold, containers within the same profile and separate full profiles are NOT the same thing.
> History sniffing is practically impossible in Firefox
Oh yeah? You sure about that?
https://www.ghacks.net/2018/11/04/browser-history-sniffing-is-still-a-thing/
> FPI is a type of OA, so is a container.
FPI was inspired by what containers do, but the containers I was talking about:
https://wiki.mozilla.org/Security/Contextual_Identity_Project/Containers
…are not the same as FPI and do NOT isolate the things (breakage-causing) FPI would isolate. Don’t mix up things to score points here, everyone here knows that it’s not the same thing.
* Removed [Editor: this has no place here]
> > History sniffing is practically impossible in Firefox
> Oh yeah? You sure about that?
Totally
– your link is outdated, please do try to keep up
– in FF77+ they mitigated it: https://bugzilla.mozilla.org/1632765
– words matter: “practically” .. i.e it is not PRACTICAL to use this anymore due to slow scripts and abysmal returns. It was hardly practical before FF77, now it’s even less practical
> [containers] are not the same as FPI and do NOT isolate the things (breakage-causing) FPI would isolate
I said they are both OA’s, and OA’s isolate the same things: in your case: favicons, to call out your nonsense. It’s all right there in the code, if you look.
I’ve never seen or heard that FPI breaks recaptcha: must be the odd case where it’s violating first partyness: good job FPI works so well: for those few sites, use a secondary profile: you know, those things you are advocating using hundreds of.
– PS: dFPI solves all that :) Not sure what part of SOLVES you don’t understand
– PPS: dFPI is landing soon: Firefox is the best browser by default for privacy, hands down
@Pants
> Thanks for the shout out: here’s the link everyone
It’s not a “shout out” when it’s being referenced in a negative way, friend. Do you know what a “shout out” is? Always has to have a positive connotation, otherwise it’s not a “shout out”, sorry to break this to you.
And yes, your script only serves to make fingerprinting easier. I can detect that you are “the guy who cared”, i.e., I can spot changes “for the better”, but because I can spot them, I can fingerprint you with them. Even the flags related to fingerprinting, I mean:
“You cannot configure your browser to prevent tracking either. Everyone will configure their browser differently so when you change a bunch of about:config settings such as privacy.resistFingerprinting and pile on browser extensions like Privacy Badger, you’re making yourself stand out and are effectively reducing privacy.”
“The only real approach to preventing browser tracking/fingerprinting is by using a browser that is designed to prevent this by default and the users do not change it. The most effective browser that does this is the Tor Browser.”
source: https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
I can detect changes, I can detect changes meant to mitigate fingerprinting, and since almost nobody enables fingerprinting mitigations in Firefox, you stand out in an extreme fashion. I can tell on the network level that you do not use Tor (as you should), and therefore you stand out even more. There are three categories here:
– Firefox (default settings)
– Firefox (modified settings)
– Tor Browser Bundle
I can tell the difference between the 1st and 2nd, and I can tell the difference between the 2nd and 3rd. Your script only reduces privacy by making users stand out in a fairly extreme manner. That’s why I am always saying that defaults matter, good defaults should be obligatory because then users are protected well and do not have to go out of their way to change settings “for the better”, thereby fingerprinting themselves because those changes can be detected.
> chromium has pretty much gotten to the end of what they can do with sandboxing, and now need to turn to e.g. rust
Firefox has abysmal sandboxing (see my sources already provided), their lax security standards are mentioned here again:
https://marc.info/?l=openbsd-misc&m=152872551609819
Nice name dropping you did there with “Rust”, the problem is, only a minor percentage of the Firefox code is in Rust (single digit numbers), most of it is written in C++. Relevant components in Firefox are not written in Rust, so the vast majority of its code is still written in a memory-unsafe language, plus its weak sandboxing is a mess as mentioned. Various security experts actively shun Firefox. Do you know how most Tor users get deanonymized? By its weak security (inherited from Firefox) being breached as if it was nothing.
> You’re making a massive molehill out of nothing.
You mean I am using your own techniques against you? Nope, I am not. Firefox’s security issues are real and the myriad of memory safety bugs and sandbox escpapes which are being patched monthly (and yet bugs of the same type appear again and again, how odd…) prove my point.
What do you want here? The solutions your propose (FPI) break shit, and I am not going to use a browser that has worse security, worse performance, and worse web compatibility, only to fingerprint myself in the end by using your script and making myself stand out in an extreme manner. Not gonna happen. Why are you here? What do you try to “call out” here? Unworkable solutions in irrelevant browsers are not the answer to anything.
PS: I laughed hard at the fact that you are saying “FPI works as it should” when I point at breakage. People want to use web browsers, not proofs of concept. Breakage is bad and must be addressed, hence Mozilla’s alpha state experiments with dFPI (which is not going to leave alpha any time soon, by the way).
Oh it is a shout out, because once people see it, they’ll go “holy cow, this is wicked”. If you want to keep going off-topic and attack the messenger instead of the message, and call the repo stupid names, I’m going to link to it – so thanks
Link: https://github.com/arkenfox/user.js/
> your script only serves to make fingerprinting easier.
Not true. You severely lack real fingerprinting knowledge and don’t even how entropy and linkability work. It’s practically a waste of time trying to explain basics to you. So I’ll keep this as short and as simple as possible for you, as it’s OFF-TOPIC… again
The script actually lessens entropy: do some basic math in your head for starters
– if nothing was done, then it’s highly likely to be unique: e.g. fonts, screen metrics, canvas, webgl
– but we do do something (ha ha, I said “do do’) – and that is to use the built-in RFP
– additionally webgl (and web audio) is disabled as that is high entropy and not covered by RFP yet: i.e it is better to kill it until RFP handles it as it’s too identifying
– we do not recommend anti-FPing extensions
– web extension APIs are severely lacking and reveal that they are lying and often they can be bypassed via other methods to reveal the real values (more so on chromium: Firefox comes with an exportFunction)
– ^^ those same rules would apply to any browser: including Brave
The overall affect is to severely limit the entropy with a small set of plausible results (that naturally match Tor Browser, which helps a little) and reduce the attack surface = reduced fingerprint. If you claim otherwise, then I say BS, because you do not have any real world data to back you up. Neither do I for Firefox (kinda), but math says I am right: especially on metrics that are commonly checked in scripts: and real world tests have repeatedly shown that TB’s anti-FPing is solid (for Tor users as a set)
But fingerprinting is the least of the repo’s goals: it’s a bonus: security trumps tracking trumps anti-fingerprinting as a general rule. If a script wanted to dig deep enough, I’m sure it could find enough fine details: in Brave this wouldn’t be hard at all since it lacks parity in several dozens of metrics that RFP covers – so I wouldn’t go crowing on about Brave in this regard just yet (but best of luck to Brave: becuz fuck fingerprinting). But at least in Firefox, I know for a fact that the main damage that can be done has been mitigated somewhat: the fingerprinting is practically guaranteed to have been lowered (not hard when you’re coming down from almost certainly unique).
I’m not saying the solution is perfect, but it is what we have to work with. Disabling an API is not great: e.g. webgl, but the data entropy is too high. And sometimes there are better solutions: like subtle randomizing on canvas would be great: canvas use has changed in three years. Hopefully it gets revisited as the compat cost climbs a little: but that’s up to Mozilla, Tor Browser, and RFP.
We can only use what is available in-browser. So assuming a script gets through, and it digs deep enough: both Brave+Shields and Firefox+RFP+a-couple-of-other-pref-tweaks (both browsers not using any anti-FPing extensions) would be pretty much unique: Brave almost certainly, since it lacks so much parity
@Pants
> Oh it is a shout out, because once people see it, they’ll go “holy cow, this is wickedâ€.
I would hope that people would realize that you are in fact maintaining a privacy reduction script. More on that below.
> Not true. You severely lack real fingerprinting knowledge and don’t even how entropy and linkability work.
You severely lack knowledge yourself and I am going to prove this to you – however, contrary to you, I don’t have to misrepresent what was said in order to achieve that goal.
> if nothing was done, then it’s highly likely to be unique: e.g. fonts, screen metrics, canvas, webgl
You can’t generalize the uniqueness of the real values like that. If I use Firefox on a Windows 10 PC, only the default fonts (or whatever comes with MS Office) installed, popular processor, popular screen resolution, popular GPU etc., the uniqueness of these values, the real values I mean, is not too great. But yeah, if e.g. WebGL is enabled, unique values would leak.
> but we do do something (ha ha, I said “do do’) – and that is to use the built-in RFP
Yeah, but what does that “do do” really mean for users in the end? Stay tuned.
> additionally webgl (and web audio) is disabled as that is high entropy and not covered by RFP yet: i.e it is better to kill it until RFP handles it as it’s too identifying
And there lies your mistake: When you disable WebGL, I can detect this right away. Not many people bother to disable it, so your users stick out in an extreme fashion. Tor disables it by default, but I can detect at the network level that you are not using Tor without much difficulty. Tor doing it by default means that all(!) Tor users return empty values here, whereas Firefox users should return some value. If you return nothing on Firefox (and as I said, I can differentiate between Firefox and Tor at the network level) you are unique as can be. “Nothing returned” becomes part of your fingerprint, you using Firefox is part of you fingerprint, and both together in one fingerprint is extremely unique.
Stop trying to justify the existence of the privacy reduction script, I have explained to you – despite allegedly having no idea about fingerprinting – that this is a terrible idea. Someone using Firefox on popular hardware without any fingerprinting protection, thus returning the real values, is (ironically) likely much less unique than the few users of your script.
> we do not recommend anti-FPing extensions (…) web extension APIs are severely lacking and reveal that they are lying and often they can be bypassed via other methods to reveal the real values (more so on chromium: Firefox comes with an exportFunction)
Good, but it matters little. By altering the default config (in a way mimicking Tor, without having Tor’s network fingerprint) you are already making your users highly unique, useless anti-fingerprinting extensions would only make it worse.
> those same rules would apply to any browser: including Brave
You mean that any browser, including Brave, gets in contact, and has to deal with, fingerprinting? Yeah, I don’t even dispute that. However, in Brave I don’t have to make myself more unique by altering the default configuration, so it is not directly comparable to what you do (luckily so).
> The overall affect is to severely limit the entropy with a small set of plausible results
Returning nothing by disabling some components like WebGL is not “plausible”, it is implausible. Firefox in the default configuration would return a value.
> (that naturally match Tor Browser, which helps a little)
Again, I can detect that you are not using the Tor browser (as you should) on the network level. Probing for that is easy. Because I can differentiate between Firefox and Tor, your users remain unique. Them imitating Tor browser while not actually using Tor browser is detectable, and the subset of people doing this is extremely small.
Also, if your script tries to achieve what Tor already does by default, why does it even have to exist as a separate entity, not even achieving the intended goal (because you in effect make users more unique, not less)? I guess that’s a topic for another wasted morning.
> and reduce the attack surface = reduced fingerprint.
You are not reducing the attack surface, point in case:
Default Firefox with WebGL enabled: Returns some value for this.
Modified Firefox with your user.js, WebGL disabled: Returns nothing here.
You are not “reducing” the attack surface by reporting nothing here, WebGL is still being checked, that your users return nothing is being recorded as the result for WebGL, and makes them unique as far as this metric is concerned. If WebGL is disabled, scripts do not magically stop checking for its value (this would be the only case where the “attack surface” is reduced) – the only thing that happens is that no value is returned, which is highly unique, and that result is recorded same as any other value. Or to make it even easier to understand: 0 (disabled) is a value, but so are 1, 2, 3… Using numbers here to illustrate my point. By reporting “0” or “disabled”, you aren’t reducing anything.
> If you claim otherwise, then I say BS, because you do not have any real world data to back you up.
I have the negative opinion of the highly respected Whonix project towards random user.js scripts for Firefox:
https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
They understand what you don’t understand – that returning nothing is itself a value that is being recorded all the same, and that this makes your users more unique (because almost nobody, except for Tor – which I can detect that you don’t use – disables e.g. WebGL).
> and real world tests have repeatedly shown that TB’s anti-FPing is solid (for Tor users as a set)
1) Your users are not in the set of Tor users, I can detect that they don’t use Tor at the network level.
2) Tor does all of this by default, for instance, for WebGL *all* Tor users would return nothing, whereas Firefox should return something and the number of people returning nothing for Firefox (after having altered the defaults) is minuscule.
You fail to grasp both things, and the relationship they have with one another.
> in Brave this wouldn’t be hard at all since it lacks parity in several dozens of metrics that RFP covers
You know, while Brave may leak something if a script digs deep enough (most don’t – but in theory I agree), I am still better off with it than if I was running a highly unique Firefox configuration – which would be the result of applying your script.
> But at least in Firefox, I know for a fact that the main damage that can be done has been mitigated somewhat: the fingerprinting is practically guaranteed to have been lowered (not hard when you’re coming down from almost certainly unique).
You haven’t “mitigated” anything here – all you have achieve is making your users extremely unique, much more unique than if they just reported the real values on popular hardware.
> Disabling an API is not great: e.g. webgl, but the data entropy is too high.
The real values leaking is bad but what is also bad is returning nothing – on Firefox no less, which should return something by default – because that is highly unique as well and is being recorded as such. Why do you fail to understand this?
> Brave almost certainly, since it lacks so much parity
Brave may lose against Tor (if users stick to the laboratory conditions and don’t change anything in Tor), but it’s 100% guaranteed to still be superior to a highly unique Firefox setup – because that is what your users are, highly unique.
Your post contained an extreme number of fallacies and exposes your failure to understand basic concepts. You think by disabling things, you are reducing the attack surface, while in reality you are just making your users more unique because “nothing returned” is also a value that is being recorded and would be unique for Firefox – wouldn’t be unique for Tor, but as I said, I can easily detect whether or not someone uses the Tor network at the network level. Can we please pause this discussion until you understand that disabling some stuff is making your users more unique rather than less? If so, bless you. If not, here we go again.
Wow, all that typing that shows your absolute ignorance. You can’t even keep your facts straight
quote IH: “But yeah, if e.g. WebGL is enabled, unique values would leak”
quote IH: “You are not reducing the attack surface, point in case: Default Firefox with WebGL enabled: Returns some value for this. Modified Firefox with your user.js, WebGL disabled: Returns nothing here”
“returns some value” is actually “unique values would leak” : not some cherry picked common device + hardware with no changes to it: but universal
When it’s between returning a unique value vs returning a single value: i.e API disabled (which many users do: e.g Tor Browser: and not all scripts bother to check for TB vs non-TB-gecko: first, none of them that I have seen can do it reliably from JS: they rely on things like inner window = screen = rounded 100s: = flawed). So it’s a least have some commonality by reducing the attack surface vs having none
look up the definition of “attack surface”: by removing the API as the only viable in-browser solution, the surface has been reduced: from all the webgl parameters, webgl1, webgl2, hardware vs software rendering, webgl-experimental, shader info and so on.
* [Editor: removed, please stay polite] So where did you prove me wrong
> that returning nothing is itself a value
no-one said otherwise
as for all the rest, you’re out of your league (keep using Brave in default config with 200 profiles: you are still unique: for starters, canvas isn’t even fully protected, it leaks: makes me wonder if webgl leaks as well) .. go home, you’re embarrassing yourself
@Pants
> “returns some value†is actually “unique values would leakâ€
I do not even dispute that. But returning nothing (which is in itself a value), is objectively worse (i.e., more unique) than the leakage related to most hardware. Even if the real values leaked, usually I’d still be less unique than if nothing were returned instead. The Firefox users with modified settings are a joke as far as their numbers go, your configuration is highly unique.
> not some cherry picked common device + hardware with no changes to it: but universal
Again: What you do is worse than if the real values leaked, as far as most hardware is concerned. Firefox returning nothing for some values is implausible because the default configuration of Firefox would return something!! Tiny weeny pool of users returning nothing, you see – this is problematic.
> which many users do: e.g Tor Browser
Once again, I can detect whether you use the Tor Browser or ordinary Firefox. Your users will never be in the pool of “Tor Browser users” because of clear differences in the network level behavior.
> and not all scripts bother to check for TB vs non-TB-gecko: first, none of them that I have seen can do it reliably from JS:
I don’t need to do this from JS – I can do this purely at the network level already; I can see Tor end nodes approaching a website, too. Tor leaves a common network fingerprint that Firefox just doesn’t leave. Accept that and move on.
> look up the definition of “attack surfaceâ€: by removing the API as the only viable in-browser solution, the surface has been reduced: from all the webgl parameters, webgl1, webgl2, hardware vs software rendering, webgl-experimental, shader info and so on.
Nice selection of values, I tell you what: The real values leaking for all of them(!) would in most cases be better than “WebGL: returns nothing”, because with the latter you are still more unique than with the former. Try again.
> So where did you prove me wrong
I have proven, repeatedly, that modifications to the default settings can be recorded and that users with modified settings (such as those fools running your user.js) are extremely unique, hence why your script is not a privacy enhancement script, but rather a privacy reduction script.
> for starters, canvas isn’t even fully protected
And it’s never going to be addressed… Wait a second, I thought there was an active GitHub issue for that!? As you yourself like to proclaim: No protection is perfect, everything needs time to be implemented. Bugs are bugs, and will be resolved. Bad ideas need to go (such as your user.js for privacy reduction).
> you’re out of your league [blah blah] go home, you’re embarrassing yourself
The Whonix devs are embarrassing you and your ridiculous, irrelevant script when they clearly state:
“You cannot configure your browser to prevent tracking either. Everyone will configure their browser differently so when you change a bunch of about:config settings such as privacy.resistFingerprinting and pile on browser extensions like Privacy Badger, you’re making yourself stand out and are effectively reducing privacy.”
“The only real approach to preventing browser tracking/fingerprinting is by using a browser that is designed to prevent this by default and the users do not change it. The most effective browser that does this is the Tor Browser.”
source: https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
God, I love posting it again because it is so true – the users who think that by deviating from the defaults in detectable ways(!) they are improving their privacy are clear cut FOOLS, and your project therefore is a problem for and by fools. Ask the Whonix devs, people who know more about privacy and anonymity (and how to achieve it) than you ever will, then YOU will be massively out of your league. Can’t wait until you no longer target me, but take the fight directly to them, if you dare (I know that you don’t, haha).
> the users who think that by deviating from the defaults in detectable ways(!) they are improving their privacy
Nowhere have I disputed the contents of that link.
It is you who confuses security with privacy, and that the user.js is trying to hide those changes: IT IS NOT trying to hide that. Blocking well-known tracking techniques used in the wild (usually, but not always, detectable): the benefits can far outweigh the possible fingerprinting. e.g. Blocking adverts is detectable, but no one cares: the benefits far outweigh the potential script that may get through that checks this.
Look up what a risk threat matrix
—
IH: claims something a study doesn’t claim – gets called out on it
IH: claims something about containers and firefox’s isolation and gets called out on it
IH: claims using hundreds of profiles is an easy solution to gain parity with firefox’s isolation – gets laughed at
When IH can’t “win” a discussion, he turns to attacking the messenger: in this case: going off-topic and claiming wild claims about arkenfox user.js
–IH’s CLAIM IS (surprise!) FALSE–
IH claims that the arkenfxos user.js doesn’t reduce fingerprinting (FP for short). By that we are talking about the usability of it for tacking, not the fact that a FP script can run]. This is false and misleading.
FIRST: misrepresenting the user.js
1. No-one, not the user.js and not even Tor Browser, claims that they can protect aganst ALL FPing
2. It’s a question of priorities: e.g. blocking a known tracking technique or security risk (e.g. WASM) vs possible mitigation of a FP metric IF an advanced enough script gets through. The user.js is not trying to, and cannot, reduce FPing for ALL scripts: if it can help against some scripts, then that is a bonus
SECOND: DEBUNKING THE CLAIM
1. It uses RFP which has a poison pill for canvas. Any naive scripts that run, the FP is tainted and unusable
2. It reduces at least one metric from almost-certainly a unique value, to one that is shared among many (i.e not one). Without reducing this entropy, you are screwed: therefore the user.js renders the metric useless as a unique identifier: therefore the user.js reduces the FP
BOOM. Proof the user.js reduces FPing. No one has ever claimed that ALL cases of FP is mitigated. Remember, that if you do nothing, you’re unique. The user.js changes that and in some cases, you are 100% definitely protected, and in many others you are at least not unique (whereas you would have been had you done nothing)
IH’s claim is complete BS and an attempt to deflect and attack the messenger
@Pants
> It is you who confuses security with privacy,
I am not. I was discussing your user.js which is hardly related to security at all. Of note: Hardly.
> Blocking adverts is detectable, but no one cares: the benefits far outweigh the potential script that may get through that checks this.
False equivalency. Your fingerprinting countermeasures increase the fingerprintability of the users of the script. This is not a side effect of a different goal (for example, adblockers have the goal of, well, blocking ads, that the extensions themselves or their lists can be detected is a coincidental side effect), what you do is just failure. Nice strawman, but easily debunked.
> claims something a study doesn’t claim – gets called out on it
Yeah, so I said that the study claims that Brave is the most private browser. You “called me out” by saying that the study only covers the outgoing connections of browsers, commonly known as “phoning home”, which I in turn called out as false, quoting from the study and showing that it also covers other aspects. So much for you “calling me out”. You called me out by not understanding what they study covers? Is that how your “calling out” works?
> IH: claims something about containers and firefox’s isolation and gets called out on it
I claimed something about containers, you mixed it up with FPI which is not the same as containers at all, saying that I was wrong after mixing up different topics. I wasn’t wrong at all.
> IH: claims using hundreds of profiles is an easy solution to gain parity with firefox’s isolation – gets laughed at
Yeah, but only “laughed at” by Firefox zealots like you, or in all honesty, only you (hint: I don’t care, you just annoy me). My solution is smart in that it avoids the problems FPI causes, FPI is NOT like full profiles in nature, and therefore my solution that is more or less free of bugs is necessarily superior. I know that you don’t give a shit about usability, but unfortunately for you, others do. You can laugh at people wanting to actually, you know, use their browsers… But it’s idiotic to do so.
> When IH can’t “win†a discussion, he turns to attacking the messenger
Your comment had to be redacted because you were attacking me. Projecting much? I have never claimed one untrue thing about you to my knowledge.
> IH claims that the arkenfxos user.js doesn’t reduce fingerprinting (FP for short). By that we are talking about the usability of it for tacking, not the fact that a FP script can run]. This is false and misleading.
How is it misleading? By making your users more unique, you also help in linkifying their activities. You help tracking via FP. What you call “misleading” (I know that you like to throw around that term whenever you’re being criticized for your stuff) are just the facts.
> No-one, not the user.js and not even Tor Browser, claims that they can protect aganst ALL FPing
I never claimed that, it would be enough if it didn’t make fingerprinting users easier by making them more unique.
> It uses RFP which has a poison pill for canvas. Any naive scripts that run, the FP is tainted and unusable
I didn’t say that you fucked up EVERY metric, yeah, pick one where false values get reported instead of no value / disabled, this is not proving anything at all. If you fuck up other metrics, a poison pill for canvas won’t be enough to save the sinking ship. I can still identify your users without much of a hassle, canvas or not.
> Proof the user.js reduces FPing.
What you said doesn’t prove that the user.js reduces fingerprinting. It proves that it handles one metric correctly, while fucking up others.
> The user.js changes that and in some cases, you are 100% definitely protected, and in many others you are at least not unique (whereas you would have been had you done nothing)
The fingerprint caused by your user.js is highly unique, and is much worse than if nothing was done on most hardware. I don’t mean every single metric (go ahead, prove that one or two metrics were handled correctly – it’s irrelevant, I don’t care), I mean the sum of the parts is utter garbage because it’s unique as hell.
I mean, the WebGL fuckup is already bad enough: Firefox enables it by default, you recommend disabling it. I can detect that users of your user.js have it disabled, I can detect that they are not Tor users… Again, it’s just one example, but in the end, you ease fingerprinting, and that’s not the only example.
Look, Pants, I know that your zeal to prove me wrong is limitless and that you seemingly have no time constraints (Dare I ask: Unemployed?), but I am tired of this at this stage. I said what I had to say. I’ll take you more seriously once you no longer deflect and lie, use strawmans, and most importantly, take the fight to experts like the Whonix devs who will shame you as if there was no tomorrow on first sight. I am just a commenter here who is tired of your molestations, obvious and repetitive fallacies, and overall nastiness. I am done here. Get lost.
It’s not breakage if FF blocks the kind of tracking that *Google* [Editor: please use the correct company name] Chromium whitelists, Google Spycaptcha is only one of the mass surveillance tools from the Spyware Company that must be eradicated from the web.
This is the kind of privacy and security that you can’t understand, from this PoV all Google chromium browsers are pretty useless and not bugless as you suppose.
@SpywareFan
If you have to go through tons of captcha riddles to enter a website, it’s objectively a miserable browsing experience and what I would call “broken” without much of a second thought. Especially Cloudflare uses this, and most websites sadly rely on them, including this one here (gHacks).
I don’t want this to be understood as me calling reCAPTCHA a good thing – it is not, it is a great plague with which Google torments privacy-aware web users. However, reCAPTCHA is a reality of today’s web, and if a browser degrades user’s browsing experience by provoking it, I’d be hard-pressed to call this a good thing from a usability point of view, even though I personally consider reCAPTCHA to be a pestilence (one doesn’t have much to do with the other – reCAPTCHA being objectively bad doesn’t mean I have a right to make the browsing experience of others miserable).
> bugless
No software is “bugless”, some software is just less buggy and better vetted than other software.
I have no issues with reCaptcha or hCaptcha using a hardened FF+uBo+uMa+Temporary Containers+CanvasBlocker, so if something breaks it’s not because of FF or unGoolaged. (but I block all Goolag IP’s, so if a website force me to allow Goolag spyware I go elsewhere)
Chromium breaks less because of all the browser locked “capabilities” imposed by Goolag, adding more lists to the adblocker helps, but doesn’t prevent unwanted data scraping and tracking from The Cancerâ„¢.
Yes, chromium is better vetted, but not less buggy than other browsers, see last year memory safety bugs (125 critical) or last week zero-day.
@SpywareFan
If you have no issues with reCAPTCHA, then this means that nothing you do really triggers it. Which is not a good sign, as far as privacy protections are concerned, but appreciable from a usability point of view – as far as the whole privacy protections vs. usability matter is concerned.
> CanvasBlocker
…is a sure way of making yourself more unique. Better stick with the built-in fingerprinting defenses, but note that if you enable those, you also stick out – “the guy who cared” can be identified as such. If you really want to combat fingerprinting, use Tor, if that’s not an option, use some browser that tries to mitigate fingerprinting by default(!), like Brave. Seriously.
> but I block all Goolag IP’s, so if a website force me to allow Goolag spyware I go elsewhere
Please understand that this is a fairly extreme stance not applicable to most users – and I am saying that as someone who is trying to do his part: I use an ungoogled version of Chromium (Brave), I use DuckDuckGo instead of Google whenever possible, I am blocking their trackers, apart from browsing I have also never used GMail. Some of their stuff is harder to replace, though (YouTube, to a lesser degree Google Maps). Please understand that most people will only accept limitations and inconveniences to a limited degree, and I can’t blame them – people need to get stuff done. Most here are trying to do their part, but again, but your stance seems most extreme to me.
> Chromium breaks less because of all the browser locked “capabilities†imposed by Goolag, adding more lists to the adblocker helps, but doesn’t prevent unwanted data scraping and tracking from The Cancer™.
I don’t know what you mean here – Chromium is open source and nothing is “locked” there. Or do you mean that Google specifically enhances the experience for Chromium users on their services? I’d call this an urban myth – Google services are not horrible on other browsers, and in the end, your data is more valuable to them than making your life miserable, they WANT you to use their services.
> Yes, chromium is better vetted, but not less buggy than other browsers, see last year memory safety bugs (125 critical) or last week zero-day.
CVE counting is idiotic, sorry to say. The number of security issues doesn’t tell you much by itself, because it fails to account for:
– the severity of discovered issues, which does vary, and
– the popularity of different browsers, meaning that the most popular one (Chrome and therefore everything based on Chromium) naturally receives more scrutiny than others.
Firefox has weaker exploit mitigations than Chromium, though both browsers had zero days (as did any other major software product). What is more interesting here is a) the frequency of severe security issues and b) whether or not the same general type of security issue (e.g. memory safety hazards) repeats itself over and over again, or not. And I think Firefox loses in both categories.
@Pants
I don’t have time for this nonsense today. By directly comparing Firefox and Brave, you implicitly already assume that things like security, performance, web compatibility (all of which are miles better in Brave and any other Chromium-based browser compared to Firefox) are totally irrelevant, as otherwise Firefox wouldn’t even be considered before even entering the “privacy” discussion. I won’t compromise my system by using Firefox and its weak exploit mitigations, I also don’t plan on needlessly widening my attack surface, thank you very much.
Besides, your project only helps Firefox users in fingerprinting themselves, just ask the Whonix devs (i.e., people who know what they are talking about):
https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
* [Editor: removed, please stay polite]
> Besides, your project [followed by lies]
Thanks for the shout out: here’s the link everyone: https://github.com/arkenfox/user.js
Why are you going off topic? It actually reduces fingerprinting and this is demonstrable and easily proven. Please stop talking about things you do not understand. And stay on topic.
> https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
https://old.reddit.com/r/firefox/comments/lbu6q2/why_do_people_say_chromiums_sandbox_is_better/glxjrjg/
quote from the link
> How does that wash out in the end? It’s really hard to say and pretty much impossible to quantify
Also: here’s the flip side
– https://www.zdnet.com/article/chrome-70-of-all-security-bugs-are-memory-safety-issues/
– chromium has pretty much gotten to the end of what they can do with sandboxing, and now need to turn to e.g. rust
So on one hand, you have chromium with a stricter sandbox but the need to (and I assume they are) migrate away from C/C++. And on the other hand you have Firefox with large amounts of rust, but a less strict sandbox, while they finalize fission, which is almost done.
I repeat: “How does that wash out in the end? It’s really hard to say and pretty much impossible to quantify”
Mainstream browsers are already highly vetted and very secure. Firefox is secure enough for 99.999% of people, no problems, as long as they stay up to date. You’re making a massive molehill out of nothing.
This means Brave is on the path of autonomy where uBlock Origin may become obsolete. The problem is that even this is probably not enough for a clean browsing experience. Without uBlock Origin, pop ups still open rampantly, which makes Brave useless without uBlock Origin.
Especially on mobile Brave needs to either enable extension support or include all of uBlock’s filters into their built-in content blocking, because Brave on Android is completely useless as it is.
I use Poper Blocker to block popups + Behind The Overlay Revival to manually remove overlays on pages.
@John
If you have uBlock Origin installed, you don’t need Poper Blocker, because uBlock already blocks all pop ups. Even on my Android phone with Kiwi Browser, uBlock Origin never let and ad or a pop up through.
Also Ghacks wrote an article how Poper Blocker could be dangerous malware, but now when I look for it, it’s no longer there, I wonder why.
Brave needs to add:
– the ability to add custom lists, not just custom rules.
– a visual picker tool to select ads on the page.
– a detailed log through which you can select/filter and create new rules.
This is a good choice from Brave(TM).
Adding this type of native ad blocking in browsers is just going to result in advertising and marketing companies becoming even more sneaky and aggressive.
It’s better for browsers to allow all ads by default, and then allow only the people who really care about not seeing ads to block them.
On the other hand, it would be better for society and the world if there were no ads at all. That would put a huge dent in the excessive consumerism that plagues today’s world. But that’s unlikely to happen without real intervention. This action by Brave just makes a bad situation worse in the long term. It’s the typical short-sighted thinking that got us into this problem in the first place.
I respectfully disagree. Showing ads is much more than convincing people to buy my products. Because of the very nature of the underlying technology used to serve those **targeted** ads, it’s a non-negotiable requirement that you surrender all kinds of data about yourself. In an ideal world that would be the end of it, but data can be used for other purposes like social manipulation.
A lot of people don’t care about this stuff and that’s understandable, but many others “don’t care” because they don’t know how to approach the problem since it required technical knowledge to some degree. Some browsers started implementing ad blocking features because of this. And it’s now a competitive feature that you must have, and that is a good thing albeit not perfect (as with so many other things)
You can just turn off the adblocking feature if you want to see ads?
When Manifest V3 comes, adblocking extensions will become useless, hence the native adblock.
Not only Brave but also other browsers already have their own native adblocking already.
This is of course the opposite of short sighted lol, I don’t understand what you’re thinking.
Manifest V3 is already live, adblocking extensions still works normally.
Your reply is useless.
Also Brave and other Chromium browsers except GC are unaffected by manifest V3.
“Manifest V3 is already live”
Wrong, do your research first * [Editor: removed, please stay polite].
Your reply is useless.
There’s a big trend (which goes for many companies!) in monetizing other people’s free and open-source work. By forking or including end-products as a resource.
And influencers receiving big money.
I don’t know every detail of course, but I’m not sure how I feel about many of these decisions.
This is just about adding some more popular lists, I don’t think anything is being monetised.
I guess he means that Brave usage might go up due to such changes, so naturally they will profit more.
Use Firefox.
Imagine telling people to use a browser from a company that promotes censorship in the way that Mozilla Firefox does!
Or did people already forget how Mozilla was saying few days ago “We need more than deplatforming” in a blog post or few months ago they started to tell people on their twitter and even sent as push notification in their android phone to boycott Facebook because apparently Facebook, in their dumb heads, wasn’t already banning enough people and was allowing the so terrible hate speech blabla?
Did people already forget it, are they just blind or they just ignore it because it fits the narrative they were brainwashed to believe?
or maybe I am wrong and I guess I shall read and believe the lie “We work to ensure the internet remains a public resource that is open and accessible to all.” in Mozilla Twitter page?… because yeah… that’s exactly what they have been promoting for years… sure.
Maybe it is just my imagination that Firefox aren’t saying they will try to control what you read and see on the internet like they also have been promoting for years, first with a lame excuse like “hate on the internet” or “hate speech” oh uh uh so terrible, words hurtz me wah wah. and maybe I shouldn’t believe once they get there they will not move more and more the ‘goal post’ of deplatforming until only the people who are sheep enough to agree with dumb Firefox and Silicon Valley companies mentality use the internet… just my imagination.
They can enjoy the google money if they want, but I hope more and more people stop using Mozilla crap.
The Ramones loathed legacy culture
Yeah, if you want to weaken your security:
https://madaidans-insecurities.github.io/firefox-chromium.html
https://grapheneos.org/usage#web-browsing
Study finds Brave to be the most private browser by default (study includes Firefox):
https://www.scss.tcd.ie/Doug.Leith/pubs/browser_privacy.pdf
Dying browser is still dead:
http://calpaterson.com/mozilla.html
To those who think that they can “tweak” Firefox to improve their privacy, the developers of Whonix (to those who don’t know: Whonix = highly respected operating system which aims to provide perfect anonymity) seem to disagree:
https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
By tweaking Firefox, i.e. trying to reach the level of privacy which Brave provides by default, you are only fingerprinting yourself, thereby ironically reducing your privacy. Have fun.
IH: “Use only our corporate malware browsers and use them exactly as we made them or you will be fingerprinted and not secure.”
It looks like after Google and Mozilla, Brave’s marketing too embraced this slander campaign that I have noticed started some time ago in various places with this false argument against those fighting their corporate malware and the free software philosophy in general.
Brave has less users than Firefox, so your story about fingerprinting yourself doesn’t really work when the less used browser is obviously gonna be more fingerprintable. Sure, Brave uses Chrome’s UA which automatically would seem to make it less fingerprintable than Firefox, but that isn’t the only fingerprinting vector used nowadays.
@wrong.
Brave has 25 million monthly active users as per the last report of their blog. It has fingerprinting protections enabled by default, meaning most Brave users would currently be using them. Firefox has more users than Brave, but the subset of Firefox users altering the default settings “to protect themselves from fingerprinting – while fingerprinting themselves by virtue of having messed with the defaults in a detectable fashion, thus returning results to fingerprinting scripts that are uncommon for Firefox – is much, much, much smaller than the subset of “Brave users”.
I have detailed this here: https://www.ghacks.net/2021/02/10/brave-browser-adds-native-support-for-ublock-and-fanboy-annoyances-lists-and-social-list/#comment-4485851
@Iron Heart
> By tweaking Firefox … you are only fingerprinting yourself
This is a false generalization that does not correspond to reality. The specifics of one particular add-on or tweak does not mean that all others work the same way. This is a common misconception, most add-ons and settings do not affect the fingerprint. Either you are incompetent or you deliberately mislead people here.
You also mix security, privacy and anonymity in one heap, which again speaks of either incompetence or deliberate manipulation.
Please stop spreading incompetent lies by copying from your carefully composed accusatory collection at every mention of FF.
@Carl Gustav
Yes, not every single setting affects the fingerprint, but many many settings do. You also single yourself out at the network level in addition to fingerprinting, for example by disabling IPv6 – instead of sanely spoofing your MAC address, the user.js suggests outright disabling IPv6 entirely, and I can detect this at the network level. A VPN would not mitigate this issue, either.
> Please stop spreading incompetent lies by copying from your carefully composed accusatory collection at every mention of FF
My “incompetent lies” directly rely on the statements of e.g. devs of the Whonix project and security researches like Daniel Micay. Perhaps you would want to take the fight to them if you really think they are wrong, dear Firefox fanboy. Don’t shoot the messenger.
@Iron Heart
No matter how much researches and authorities you add from your carefully prepared anti-FF * [Editor: please keep religion out of this site] , I pointed out only one specific phrase with a deceitful generalization. I remind you if you have forgotten what it was about:
> By tweaking Firefox … you are only fingerprinting yourself
I’m glad we agreed that this generalization is false. (Why are you untiringly spreading it is a separate question, but I think many people here know the answer.) Anyway, discussion of separate examples or authorities from your dissertation has nothing to do with my remark.
I advise you for the future to stick to the topic and refrain from naive trolling with personal attacks—these cheap demagogic tricks only emphasize the weakness of your position and hinder constructive discussion.
@ EVERYBODY
PLEASE NOTE !!!!!!!!!!
THIS ARTICLE IS ABOUT BRAVE.
HOW THE HELL DID IT TURN INTO A FLAME FEST ABOUT FIREFOX, BRAVE, CHROME, FINGERPRINTING, ETC. ETC. !!!!!!!!!
JUST STOP THIS NONSENSE.
NB YES I KNOW I AM “SHOUTING” BY USING CAPS. IT IS BECAUSE I AM SO BLOODY ANGRY AT THE COMMENTS BEING HI-JACKED BY ALL AND SUNDRY.
FURTHERMORE, THE COMMENTS ARE LOADED WITH POINT SCORING LINKS TO “FACTS”, MANY OF WHICH ARE THE PERSONAL OPINIONS OF THE WRITERS.
@Carl Gustav
All user.js files, and all “privacy-enhancing” Firefox configurations I have seen, involved settings altering the fingerprint. So yes, I think the statement “By tweaking Firefox… you are fingerprinting yourself” has merit to it, because that’s the reality of all those guides and configs out there. Point me to one, and I really mean just one, guide that avoids fingerprint-altering settings. Bet you can’t find one, even if you try. Your accusations are therefore nonsensical.
I think there is no point discussing with anyone trying to imply I said something wrong when I clearly didn’t, or anyone so willfully ignorant of the fact that they need to be called a “carefully prepared anti-FF Talmud”.
@Iron Heart
It’s strange why are you afraid to even quote yourself in full and cut the words from the quote:
> By tweaking Firefox … you are ONLY fingerprinting yourself
This statement is a pure lie and I’m glad you admitted it. You’ve been caught yet again in lies and vilification. At least do your job cleanly.
@Carl Gustav
> By tweaking Firefox … you are ONLY fingerprinting yourself
Again, this is true. All the guides I know of have recommendations in them for settings altering the fingerprint. Are you seriously denying that? If not, the point I’ve raised is true. Case closed.
I have no time for your sophistry and insistence on single word choices that do not even alter the meaning of the sentence in the slightest(!). You are trying to prove me wrong so intensively that it’s getting ridiculous at this point. Grow up, I really mean it.
@Iron Heart
Of course it’s not true because you said so. You’re a very funny dude if you think that someone here will take your word, and you can close some case just because you read some guides. Some tweaks and add-ons can change the fingerprint, but most of them don’t. These things are well known to those who at least somehow understand what they are talking about.
I’m just pointing out once again what you are doing here, spreading here deliberately pure lies.
Besides, why are you still reading guides if you haven’t used this browser since 2017 and didn’t do anything useful but throwing incompetent mud here for years? This is a very dubious level of expertise.
@Carl Gustav
OK, this will be my last reply to you simply because I am tired of your childish BS and sophistry… Use some logic:
1) I say: In all of the guides, there are settings altering the fingerprint.
2) You say: There are also settings that don’t alter the fingerprint.
2) is not the denial of 1), my dude. It’s very simple logic. The denial of 1) would be “There are no settings altering the fingerprint.”, but that is not the case in any guide I know of, hence my conclusion that FF users are only fingerprinting themselves by following those guides. Even you don’t make that claim.
I am not using Firefox myself anymore, but I have to support people who do, so I know what is going on because I have to know. Also, what kind of “argument” is this even? How can you know what I get in contact with almost daily? Pure speculation, right?
* [Editor: please stay polite]
@Iron Heart
This is not an argument. I’m not interested in your replies to some made-up sockpuppetry-styled dialogs. You were just politely told to stop spreading knowingly false generalization. Instead of modestly apologizing, you spew dirty curses here, rejecting and misinterpreting your own words, discussing some of your fictitious “cases.†(The “Support,†I suppose, is a copy-paste of barely understood paranoid guides from web?)
Why are you rewriting your own quotes here in a distorted form, when everyone can read the entire history of comments here? It’s just a pointless flood without arguments.
>OK, this will be my last reply … because I am tired
Here I always have a good chuckle. As I said earlier, I really do appreciate your sense of humor. I also like the signature punchline “I have no time.†If you’re tired, then I advise you to try to stop flooding here 24/7 with paraphrases, swearing, anecdotes and lies, wash your mouth and read which particular phrase was the reason for my remark.
If you really wanted to bring some benefit to society, I and many others would be grateful if we could compile a list of main tweaks and their useful and side effects. Your many years of expertise in this matter will be invaluable.
@Carl Gustav
Have you something better than your good ol’ accusations? I contributed useful things and explanations in this thread, in contrast I never(!) saw you contributing anything useful here. All you are capable of is complaining about me, because you have an axe to grind. This is tiresome by definition.
> I and many others would be grateful if we could compile a list of main tweaks and their useful and side effects.
Dude, do you still fail to understand one of my main points? By using a browser with shitty defaults, like, say, Firefox, and by altering these defaults in a detectable fashion, you are making yourself more unique, not less. Why should I support and endorse such a shitty idea that lessens privacy instead of strengthening it? There are already several privacy reduction scripts, choose one.
@Iron Heart
I’m glad that you still found the strength to reply. Your point has long been understood—constantly changing the subject and flatly flaming with a monotonous agenda.
You often mention the problem of poor reading comprehension, apparently, the problem is familiar not by hearsay? Because as I said earlier, your multiple “points†don’t interest me. You’ve been reprimanded about one (!) word—“only/not onlyâ€â€”and you still dance around it. All you can answer in your defense is give a link to the arkenlist and say “study itâ€? Haha what a petrified trolling.
The statement about “reducing privacy only†is dismissed as unfounded by nothing other than your allegedly personal bad experience with some scripts.
Moreover, it’s not clear how you know about the details of work of these scripts if you have not been using FF since 2017? Do you test them on those you “support†here? It’s brilliant!
And by the way, about “intellectual honesty and one-sidedness†from the next answer—I have to admit I haven’t seen anywhere else the best anti-advertisement for the Brendan’s Chrome clone than your activity here. I’m going to notify Ms. Baker to put some money out of their tiny budget to reward such outstanding performance. I authorize you to continue answering with irrelevant fables and references, which will come in handy for the nomination.
@Garl Gustav
> I’m glad that you still found the strength to reply.
???
OK, now that you point it out, sometimes I do have to wonder why I am still replying to you. Masochism, I guess.
> You’ve been reprimanded about one (!) word—“only/not onlyâ€â€”and you still dance around it.
OK, you want a reading comprehension lesson?
“By altering the default config, Firefox users are fingerprinting themselves.”
“By altering the default config, Firefox users are ONLY fingerprinting themselves.”
There is no tangible difference in meaning between those two sentences. The ONLY reinforces my point about Firefox users fingerprinting themselves with the usual scripts, leaving it out doesn’t change anything. “Only” is used as an emphasis mine here.
Not that it matters, your case that I am a “liar” was preordained already, no matter how I phrase my stuff, because anything I say or do here has to be NEGATIVE in your eyes. Regardless of that, next time, you should apply greater care and first check if there is a substantial difference in meaning between two sentences before you ride irrelevant word choices to death. Only when the meaning is being changed, it becomes somewhat close to relevant, and it didn’t have any effect on the meaning here. Boy, this gets tiresome…
> The statement about “reducing privacy only†is dismissed as unfounded by nothing other than your allegedly personal bad experience with some scripts.
Nope. You can prove this statement yourself by applying the popular scripts and testing whether or not you have a unique fingerprint. There are various testing suites for that, try it out. You don’t have to “believe” me here, anyone is free to reproduce this.
> Moreover, it’s not clear how you know about the details of work of these scripts if you have not been using FF since 2017? Do you test them on those you “support†here? It’s brilliant!
Firefox hasn’t been my primary browser since 2017, but I have it installed for testing purposes. Applying this script takes, like, two minutes. You are making it seem like it would be a huge difficulty for me to test this, when it literally isn’t difficult at all.
And I should emphasize again that you have ZERO clue regarding what I have or don’t have installed, it is pure speculation on your part. Not to mention that my personal application choice and count could literally change any hour.
> Ms. Baker
…is the biggest anti-advertisement for Firefox, she wrote this:
https://twitter.com/mozilla/status/1347633954497548289
No way this drove users away, going by the comments.
> Brendan’s Chrome clone
…is, contrary to Firefox, growing exponentially. Eich shows that he isn’t an idiot by choosing Chromium. If he chose Firefox as the base, his browser project would die with Mozilla before it even started. By choosing Chromium, Brave has better security, better web compatibility, better performance by default. Not that any of this would matter to you, you are really thinking that’s a bad thing.
> their tiny budget
Half a billion annually from Google is a “tiny budget”? LOL.
@Iron Heart
> …why I am still replying to you. Masochism, I guess.
No, just the usual narcissism—you cannot leave the last word to someone else. This is so intolerable for you, although it would seem such a trifle. Therefore, you will answer here endlessly as long as I want you to do so.
> You can prove this statement yourself by applying the popular scripts
No, the burden of proof lies with the claimant. So far, it’s just repetition trolling. The rest of the talk is about semantics—“I said this, but I mean that.†Of course not. You make a deliberate distortion to throw dirt. But at least it’s good that you narrowed the statement down to some mysterious “popular scripts.†As we can see, you’re still not hopeless and can admit when you are wrong.
I mostly use extensions (canvasblocker, multi-containers etc.) and don’t use ready-made scripts at all. It’s like all sorts of magic debloaters for Windows that can break more than improve, a completely amateurish approach. Now I glanced quickly in my notes on setting up FF and couldn’t find what my config tweaks are affecting fingerprint. Given the breadth and variety of fingerprinting methods, it seems to me that config tweaks are the last problem. I would be grateful if you could provide some specific examples (apart from privacy.resistFingerprinting, I don’t need to go that far, it’s easier to start Tor).
> Applying this script takes, like, two minutes
In another answer here, you state that you need weeks to provide a list of the impact of tweaks on fingerprint. It’s rather strange that during meticulous testing for years you have not yet shown the world a complete reference book. Write down at least some of your two-minute test results next time.
> Half a billion annually from Google is a “tiny budget� LOL.
I was hoping that I didn’t need to put big red “irony†tag here, come on.
I completely agree about the deplatforming statement, this is such idiocy. But what amazed me more was the reaction of the fanboys™, who, foaming at the mouth, rushed to prove that this was not a call for censorship. Very bad PR, but as long as the browser works the way I like it, and this missionary woman does not introduce censorship lists, I’m not political enough to worry about specific cultural issues in sunny California.
Of course, Eich made a smart business choice, betting on a monopolist developed by a trillion-dollar corporation. But, according to my thorough academic research (https://i.imgur.com/ngdL23G.png), by 2023, while Mozilla still have Google money, the number of FF users will decrease to only 175 million. And the most optimistic scenario of doubling annually, Brave will have slightly over 100 million. However, there is a high probability that Baker and friends will screw everything up much earlier than the fall of 2023. Anyway, when the lines intersect, I will gladly open champagne for exponential Brave and complete uncontested Chromotopia.
@Carl Gustav
> as long as I want you to do so.
You seem to forget that it’s me writing my responses, not you. And I do so only because your lies and accusations are outrageous, and need to be cleared up for others. I am writing these replies for others, not for “you” (it’s the very pinnacle of narcissism on your part to think that) – you aren’t worth my time.
And you really think you can “make” others write anything in response to you. To which there is only one appropriate response: LOL.
> No, the burden of proof lies with the claimant.
IH: The popular Firefox script(s) are in fact reducing privacy.
CG: That’s just your personal bad experiences with the script(s).
IH: If you don’t believe me, you can check it out yourself. Prove it for yourself.
CG: The burden of proof lies with you.
If you don’t understand that such an exchange is objectively moronic, then I can’t help you. Any proof I provide are my “personal bad experiences”, when I ask you politely to test it out yourself, you want to see proof from me, presumably to call it “my personal bad experience” once provided. The circularity is real.
> “I said this, but I mean that.â€
You seem to know better what I wanted to say than I myself do – which is again, moronic. Sorry to say, but it really is. You’d score a point here if you demonstrated that I alter the meaning of my statements as I go along, but you don’t. You ride irrelevant word choices with no effect on the ultimate meaning of my sentence to death, in the hopes that this will make me seem like a liar in the eyes of complete morons. This is tiresome, but not much else.
> mysterious “popular scripts.â€
Nothing “mysterious” here, they are well-known by basically everyone here, including you. The most popular privacy reduction script is “arkenfox user.js”.
> canvasblocker
LOL, even the arkenfox instructions tell you not to do that (they are correct as far as that is concerned):
https://github.com/arkenfox/user.js/wiki/4.1-Extensions#small_orange_diamond-%EF%B8%8F-anti-fingerprinting-extensions-fk-no
> a completely amateurish approach
Yes, no doubt.
> some specific examples
Start with WebGL and DRM.
> In another answer here, you state that you need weeks to provide a list of the impact of tweaks on fingerprint.
Conducting a complete comparison between Brave’s and Firefox’s defaults (takes days, possibly weeks) ≠installing a user.js in Firefox (1 – 2 minutes). What are you even talking about?
> your two-minute test results
LOL, all I was saying was that installing a user.js file into Firefox takes like two minutes, then go to some fingerprint test suit and lo and behold, you’ll have a unique fingerprint.
> Brave will have slightly over 100 million
Doesn’t matter. In terms of web compatibility, Brave would do fine even it it had only one user, due to being based on Chromium. If it works in Chrome, it will work in Brave. Web devs test for Chrome, and thus automatically also cover Brave, no matter how many users the Brave Browser actually has. In business terms, they need enough users to not go bankrupt, that is about all. 100 million users should do, easily.
Firefox needs actual market share in order for web devs to test for their engine. User numbers matter for Firefox on a technical level, whereas they don’t matter for Brave as long as other Chromium-based browsers remain strong. In terms of business, Google’s handouts to Mozilla will get smaller as they downsize.
> complete uncontested Chromotopia.
In theory, competition helps progress. However, Mozilla is not “competition”, neither technically nor in terms of relevance. They are playing catchup with Chromium, copying its features. They will always be behind and aren’t driving anything. When they eventually exit the market, they have nobody but themselves to blame. Mozilla’s decline is based on technical inferiority, horrible management, on having no clear vision, on being too politicized for their own good, on eroding reputation in the privacy community based on past actions and so on and so forth. When they exit the market like Presto did some years ago, WebKit will still be competing with Blink (Chromium), by the way.
I don’t know why you are harassing my comments, to be honest. The product you are defending is doomed to fail, you know it and I know it. In a few years, my exchanges with the usual suspects will be a distant memory because Firefox won’t exist as a competitive product anymore (perhaps it will be maintained by some rag tag crew like it is with Pale Moon, PERHAPS, but I am talking about “competitive” here). And even before that inevitably happens, you should really ask yourself if supporting an anti-human rights company (free speech is a very basic human right, and is not exactly dependent on whom you like or dislike) is worth your time and effort. They are willing vassals of the very monopolistic entities who fund them, and that’s an objective fact. Their commitment to privacy is lip service, not least because the default configuration of Firefox is not very private and that’s likely how 90%++ of all FF users use the product. So my question would be: Why is defending these guys so important to you? Do you see some saving grace here which I somehow fail to see?
@Iron Heart
> I am writing these replies for others – you aren’t worth my time.
My favorite punchline about your worthy time. Good boy, you can type a few hundred more useless words with zero proofs, continue to demonstrate your incompetence instead of educate yourself a little. Oh yes, you have no time to education, all day is busy writing the same things about your FF obsession in different ways.
> IH: The popular Firefox script(s) are in fact reducing privacy.
No, the original statement was different. You twist everything and lie, as usual, while the initial comment is available to everyone. I don’t blame you for this, because in an internal discussion with yourself, you must always have the best possible appearance in mirror.
/*Just stop here and imagine writing fictional dialogues about one sentence written a few messages ago*/
> canvasblocker LOL, even the arkenfox instructions tell you not to do that:
Oh, you don’t even understand that it says not to use 1. a couple of APIs 2. *together* with RFP. I just said I don’t even use RFP, and you still copypaste undigested arkenwisdoms. If you’re playing mommy’s support worker, at least try read the sentences you cite to the end.
> Start with WebGL and DRM
Specific tweaks and facts, as usual = 0, like the rest of the empty logorrhea from you.
WebGL is randomized and tampered with canvasblocker, I don’t need tweaks to disable this.
And how does DRM used in fingerprinting? Do you have any links in your deep pocket with examples about this?
> LOL/moronic/LOL/moronic
This is the whole essence of your messages. In fact, you could just copypaste this in various lengths.
> you’ll have a unique fingerprint.
Of course, this is the idea, to have an unique fingerprint, in each container on each session. I already noticed that you don’t even understand what the technique is.
> Mozilla is not “competitionâ€
> anti-human rights company
> willing vassals of the very monopolistic entities
Oh, man, I clearly found your logorrhea G-spot. I haven’t laughed like that on technical forums for a long time. What a cute little freedom fighter we have here:3
> I don’t know why you are harassing my comments
I don’t blame you for taking my admiration and endless respect for harassment. They have ridiculed you for so many years, and now of course you are afraid of any tenderness. I just want to be a kind and caring friend and have long nights of expert talks about the future of browser engines with an equally understanding specialist, am I asking a lot?
> Why is defending these guys so important to you?
Where did I defend some guys, my friend, show me? During these years of lonely insanity, you are so used to arguing with your imaginary opponents that even now you continue to speak with your fantasies. Don’t be afraid, we’ll overcome all this together with our common passion for privacy, competition and patience. Please, I beg you, just stop trolling me by constantly changing the subject and rewriting your own statements. Sometimes I’m even afraid of you, assuming that your tons of repeated nonsense are written not by a living person, but by Martin’s bot for traffic… Just concentrate on topic and be polite. Here is my hand and open heart…
@Carl Gustav
> incompetence
Would you call proven experts like Daniel Micay or the Whonix devs “incompetent” as well? They are not in favor of using any privacy reduction script in FF:
https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
https://old.reddit.com/r/GrapheneOS/comments/ciizae/vanadium_and_bromium_privacy/ev6m2ot/
> No, the original statement was different.
100 points to Slytherin!
The original statement was “by applying such scripts, FF users are only fingerprinting themselves”. Fingerprinting is a part of privacy, genius. When you fingerprint yourself, you are reducing privacy, hence:
“The popular Firefox script(s) are in fact reducing privacy.”
You give sophistry a shot to prove me wrong, unfortunately you suck at it. My statements do not contradict each other, word choices are only relevant when the basic meaning is being altered. You have much to learn in this field, it seems.
> undigested arkenwisdoms
While I disagree with Pants on many occasions, she is not wrong there. Such extensions create a unique fingerprint by altering the output in very special ways. Better stick with the built-in defenses. Even better, use a browser that has the built-in defenses enabled by default (such as the Tor Browser), so that you do not stick out by enabling them.
> And how does DRM used in fingerprinting?
https://smitop.com/post/reddit-whiteops/
> LOL/moronic
Words befitting for your comments, not my usual message.
> this is the idea, to have an unique fingerprint
This is not the idea of the internal fingerprinting protections of FF at all(the idea there is to make everyone look the same in general), if you use an extension with another approach on top of FF (with or without RFP, doesn’t matter in this case), you are making yourself more unique, not less.
> freedom fighter
No, just making you aware of whom you support, denying you any possibility of denying it later on.
> the rest / blah blah
Don’t care.
@Iron Heart
> Would you call proven experts
You take particular examples that experts give and pass them off as a universal generalization as the ten commandments. This is what I call specially constructed lies.
In fact, apart from your links, you don’t know *anything* about the particular effects of specific extensions on the fingerprint, so you throw general words, hiding behind your mighty experts.
(However, now I understand that you may not even always lie, but this is just illiteracy!)
> Fingerprinting is a part of privacy
> When you fingerprint yourself
Your microcircuits already seem to have completely melted. Now I see that you don’t even know what fingerprinting is. In general, I’m not surprised. Or maybe you wanted to say “when you fingering yourself�
> Such extensions create a unique fingerprint by altering the output in very special ways.
Which and how, besides the privacy badger? You don’t know anything except your copypaste, sorry.
You just mindlessly repeat some pieces from the internet and also advise someone to learn, it’s funny.
> https://smitop.com/post/reddit-whiteops/
Well, how does this affect the fingerprint, what’s the difference if I disable DRM in the settings or just close this the pop-up?
Judging by your comments, you really understand very badly what you copypaste. Perhaps this is popular among your sockpuppets, but not very convincing for those who can understand the meaning of what they read.
> This is not the idea of the internal fingerprinting protections of FF
I don’t care much what FF’s idea is, and even more so what is your creepled misinterpretation of it. I use my setup where I know exactly what works and how. I’ve already noticed that something other than someone else’s instructions is inaccessible to your understanding.
> Don’t care.
I asked where and who I support. I’m talking here only about your lies and technical details. Since you don’t understand the technical aspects, for some reason you decided to invent that I support someone.
I understand that Firefox fanboys are under your bed, and you fight them tirelessly every day in your hallucinatory world, but this has nothing to do with this “discussion.†All that I offer is strong male friendship and productive cooperation.
@Carl Gustav
The experts cited do not offer “generalizations”, they actually explain why applying any so called privacy script is making yourself more unique. You just choose not to listen. Extensions altering the FP are even worse because you are sticking out in an extreme fashion, by altering the default output in ways that not even the internal RFP setting would cause. You are most unique with fingerprint-altering extensions, hence why even arkengem recommends against them.
Fingerprinting is modern tracking, hence a part of privacy. Don’t know what you want to hear from me there. It is what it is. Your attempt at sophistry failed spectacularly, again.
The extension you use randomizes Canvas and this randomization is detectable. However, it randomizes differently compared to the internal RFP, hence why you are fairly unique with it enabled. By using such an extension, you prove that you have no clue, that you are even worse than the people applying any privacy reduction script (at least those scripts make use of the internal defenses, however this too can be detected – it’s still better than using an even more unique extension, however).
Carl Gustav, stop annoying me. Please. Don’t know why the moderator allows this BS to occur, guess he has his reasons.
@Iron Heart
> The experts cited do not offer “generalizationsâ€
Experts do not offer generalizations, I said it’s you who make generalizations based on their distorted quotes. Why are you twisting my words so dumbly? * [Editor: removed, please keep it polite]?
> Fingerprinting is modern tracking, hence a part of privacy.
Another gibberish for a piggy bank of golden quotes. It seems that you barely understand the words from which you construct phrases that are meaningful at first glance. You were probably trying to say that this *technique* can be a privacy *threat*, * [Editor: removed, please keep it polite]
> Don’t know what you want to hear from me there
I don’t want to hear anything from you, the value of your answers tends to negative infinity and it can easily be seen by anyone with an education above kindergarten. I just wonder how much you can keep disgracing yourself and write compulsively the same meaningless “explanations†about what you don’t know over and over again. Any of your comments is just an endless river of technical illiteracy.
> randomization is detectable
As usual, not a single proof or example. CanvasBlocker’s work is not detectable. For some reason you decided that you can just talk some baloney out of your buns and then say “prove it yourself,†but it only works in your looking glass universe, sorry.
> You are most unique with fingerprint-altering extensions
> hence why you are fairly unique with it enabled
Its uniqueness is constantly changing, which is the task of the extension, as I already said before. Given the fact that you’re not even able to understand this simple concept, your mentor tone is specially hilarious. Moreover, there are different modes of operation, which you have no idea about. You can only repeat some cliches about “sticking out in an extreme fashion†out of context and without understanding, like a parrot.
—-
Anyway, I remind you that nobody asked for your delirious fables on extensions that you have no idea how they work. My humble remark was about the wrong generalization about tweaks.
You also ignored the DRM tweak question (of course, because you have nothing to answer):
> Well, how does this affect the fingerprint, what’s the difference if I disable DRM in the settings or just close the pop-up?
And all you can answer to simple direct questions is a bunch of pathetic LOLs, “sophistry,†“BS†and cry for the mods.
Summing up, I would translate your original statement to human language this way:
“By tweaking Firefox as proofless ignorants like IH understand it, by applying unmodified premade magic scripts, you can make your fingerprint more unique.â€
It’s easy and pleasant to tell the truth, just try.
> stop annoying me
If something annoys you here, you can just leave * [Editor: removed, please keep it polite]
Gustav
> CanvasBlocker’s work is not detectable
Actually it is pretty much is. The goal of anti-FPing is to not reveal the real value. And in that it succeeds (so far). Anything that swallows a random value (poison pill) such as a naive script, is a bonus. It took me twenty or more posts to get IH to understand that ALL randomization can be detected and is ultimately (read that again: ultimately) no better than lowering entropy with static values when it comes to entropy
You can also tell if RFP is enabled, but even so, that’s no guarantee it’s RFP protection on canvas, since a site exception can be used
By using a known canvas result, you can tell if canvas is tampered with. **And** you can fingerprint the randomization characteristics of the extension or browser protection: e.g.
– RFP is random per execution, alters every pixel, randomizes all four channels (r,g,b,a), and chooses values randomly from 0 to 255
– Brave is random per eTLD+1 per session (i.e not per execution), and uses a subtle randomization of approx 25% of pixels, and alters only 1 channel (from r,g,b) and only moves the value plus or minus 1. The channel is per eTLD+1 per browser session: so once you know it, you can bypass it and return one of three possible fingeprints: r+g, r+b, g+a. A new patch recently decides a random channel to change in the 25% of pixels it alters. Using a monochrome result you can easily reverse that. The entropy in a monochrome canvas is not much less than a color one, if indeed, it actually is less.
– CanvasBlocker has it’s own characteristics as well: but does allow some changes in options, such as alpha channel
But long story short, you cannot hide that canvas is fake, and you cannot hide if an extension does it (e.g. detection of prototype lies among others)
@Pants
Wow, what a revelation! Thanks a lot for the clarification!
But muh tests… https://canvasblocker.kkapsner.de/test/detectionTest.html
> twenty or more posts to get IH to understand
Poor IH:(
– then go to some fingerprint test suit and lo and behold, you’ll have a unique fingerprint
haha so silly and dumb. do you ever read your own links?
https://github.com/arkenfox/user.js/wiki/4.1-Extensions#small_orange_diamond-%EF%B8%8F-anti-fingerprinting-extensions-fk-no
“And don’t rely on entropy figures from test sites. The datasets are not real world, very small, and tainted by both the type of visitors, and by their constant tweaking and re-visits which further poison the results and artificially inflate rare results”
that pants is very smart. expert on fingerprinting. even proved it to martin. iron heart not understand fingerprinting or entropy
i also want to make joke, hope it ok in english. iron heart make vast quantity of comments but quality is very bad. this prove quantity does not equal quality. haha, i should be comedian
@Anonymous
Also, when you use various fingerprinting test suites and you have a unique fingerprint every single time, you can hardly discuss it away. Not even Pants would.
For example, WebGL being disabled in FF can be detected by nearly any testing suite. It being disabled is highly unique because Firefox would have it enabled by default. When you disable it, and the test suite of course then subsequently shows that it is disabled, which objectively makes you more unique, then there is nothing left to discuss here. Such a result is accurate.
@Anonymous
> do you ever read your own links
Yes, it is advisable to not use such extensions. I do not disagree with the link. Learn to read.
> expert on fingerprinting
That’s why users of the script are now more unique than before. :D Pants’ opinion is in crass conflict with the opinions of other experts like the devs of Whonix.
> even proved it to martin
I have never seen any proof and I don’t even care.
> iron heart not understand fingerprinting or entropy
Apparently neither do the Whonix devs, that is these guys:
https://www.whonix.org/
I am literally getting the points I am raising against such scripts from them:
https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
Also read this, you fool:
https://old.reddit.com/r/privacytoolsIO/comments/iepjwh/wont_reducing_your_browser_fingerprint_have_the/g2ijvl0/
Be careful whose boots you lick.
* [Editor: removed, please avoid personal attacks]
– I do not disagree with the link – good. pants is very smart fingerprint expert. you should listen to her. she already show brave only beat dum dum scripts. she already show firefox resist fingerprint beat same dum dums. she already show brave and firefox already unique for smart script. she very clever cookie. haha. i make more joke. i should become comedian
@Iron Heart
you say “By using a browser with shitty defaults, like, say, Firefox”, but can you please list all the different defaults that ungoogled chromium and brave have that firefox does not. please don’t link to a marketing article, I want you to list them all, because you keep saying this. is it five things, or fifty things. please elaborate
@Anonymous
> I want you to list them all
Not going to happen. Not because I don’t want to, but rather because
1) It’s off-topic.
2) It would take 4 – 5 pages, easily. You demand me to do instantly what would take weeks to compile. Knowing that I can’t do it instantaneously, you can then say: “See, IH was wrong.” – when in actuality you ask something of me that clearly can’t be done instantaneously.
3) It would be to no avail, because you are a Firefox fanboy. I would consider doing it for someone who asks in good faith, but in a manner that is not 1)
Okay, so let’s take a look at arkengem:
https://github.com/arkenfox/user.js/blob/master/user.js
Lists all the settings you need to you “need to change” in order to “improve your privacy” (while in actuality just creating a unique fingerprint if you follow some of the advice given there).
Now read this:
https://brave.com/privacy-updates-1/
https://brave.com/privacy-updates-2/
https://brave.com/privacy-updates-3/
https://brave.com/privacy-updates-4/
https://brave.com/privacy-updates-5/
https://brave.com/privacy-updates-6/
https://brave.com/privacy-updates-7/
And this:
https://github.com/brave/brave-browser/wiki/Deviations-from-Chromium-(features-we-disable-or-remove)
https://github.com/brave/brave-browser/wiki/Fingerprinting-Protections
https://github.com/brave/brave-browser/wiki/WebRTC-Custom-Settings
Obligatory as well:
https://www.scss.tcd.ie/Doug.Leith/pubs/browser_privacy.pdf
And most importantly, the “privacy” section of their GitHub, covering everything that was done so far in this respect and what is still in progress:
https://github.com/brave/brave-browser/issues?q=is%3Aissue+is%3Aopen+label%3Aprivacy
> please elaborate
I have done something much better here, I gave you an opportunity to explore and learn something yourself, by studying the original sources. If you are intellectually honest (and I know that you aren’t, you are clearly one-sided), you will find that Brave does many things by default for which Firefox’s default config would have to be altered – which is bad for obvious reasons.
@ Iron Heart
fanboy? I didn’t ask for some arkengem thing and what firefox can do, I asked for the default differences for privacy between your browsers ungoogled chromium and brave to firefox
update l and 2 is tracking protection and shims: firefox also has that
update 3 and 4 is some fingerprinting stuff: firefox has resist fingerprint from tor browser but its not on by default – the tor browser is very strong
update 5 seems mixed: query tracking parameters, referers, reporting api – firefox only has the reporting api in nightly the rest i dont know except changing referrer setting breaks everything for me
update 6 cname trickery – i do not know about firefox but everyone has ublock origins which does this
update 7 on feb 1st 2021 third party ephemeral site storage: it gives credit to safari and tor browser with its first party isolation: firefox is moving to dynamic first party isolation next release and it is for all parties not just third party
so is that it? that’s not much, referers that break things and some fingerprinting, where is all the rest you keep claiming
I do not understand why would it take weeks to compile and cover 4 or 5 pages, when you have claimed this for a long time. have you not already checked it and have a list or it seems you are making big statements of air
the pdf stuff is not about protecting me from websites
why can you not give me a list of the privacy differences from firefox you keep talking about please. the links do not give me a list
@Anonymous
I know that this will be a total waste of my time because you are not inquiring in good faith here, but anyway… I won’t list “everything” here because there is no point to that, just the some relevant things because the more irrelevant stuff won’t shift the balance given the following:
– Brave blocks 3rd party cookies by default (Firefox doesn’t)
– Brave has a sane cookie lifetime policy – 7 days for all cookies set by JS for Brave
– Brave has a saner referrer policy
– Brave blocks trackers by default (in ordinary, non-private windows, Firefox excludes what they call “tracking content” from their tracking protection)
– Brave’s default anti-tracking lists are not a sad joke (Firefox uses the weak Disconnect lists and on top doesn’t even block tracking scripts by default in non-private windows)
– Brave disables all prefetching (Firefox only disables prefetching on HTTPS websites, they do nothing against speculative connections caused by hovering over links or coming from the address bar, their predictor is enabled by default)
– Brave filters out eTags by introducing a size minimum for cached objects (Firefox needs extensions for that)
– HTTPS Alternative Services tracking doesn’t work in Brave (alive and well in Firefox by default)
– Brave filters out common tracking parameters from URLs (Firefox needs an extension for that)
– Brave avoids address bar leaks by default (Firefox doesn’t)
– Mobile only: Brave doesn’t come with built-in trackers (Firefox comes with hardcoded Google Analytics, Adjust, Leanplum trackers)
– No push client channel updates in Brave
– No domain service reliability / alternative suggestions in Brave by default
– Brave has no way to hijack the browser with experiments by default (Mozilla has this ability by default)
– Sync: Brave’s sync implementation doesn’t require any personal data like the E-Mail address
– Brave blocks all storage in third party frames (Firefox doesn’t)
– Brave has fingerprint protections on by default
– Brave does all of this by default, which is noteworthy because you have to alter the Firefox defaults in a way that affects the fingerprint to achieve some of this.
– SafeBrowsing remote download lookups avoid leaking URLs and file names in Brave by default
I’ll leave it at that, if you had read up on the “privacy” section of their GitHub, you would know all of this by now. Also read this, I sourced some of the things I said from this comment:
https://old.reddit.com/r/brave_browser/comments/i8rx92/why_use_brave_instead_of_fire_fox_or_water_fox/g1aqffl/
> do not know about firefox but everyone has ublock origins which does this
Perhaps you should make it clear how you want the browsers compared, I mean is it…
– Firefox (default) vs. Brave (default)
– Firefox (default) vs. Brave (default + extensions)
– Firefox (default) vs. Brave (modified)
– Firefox (default) vs. Brave (modified + extensions)
– Firefox (default + extensions) vs. Brave (default)
– Firefox (default + extensions) vs. Brave (default + extensions)
– Firefox (default + extensions) vs. Brave (modified)
– Firefox (default + extensions) vs. Brave (modified + extensions)
– Firefox (modified) vs. Brave (default)
– Firefox (modified) vs. Brave (default + extensions)
– Firefox (modified) vs. Brave (modified)
– Firefox (modified) vs. Brave (modified + extensions)
– Firefox (modified + extensions) vs. Brave (default)
– Firefox (modified + extensions) vs. Brave (default + extensions)
– Firefox (modified + extensions) vs. Brave (modified)
– Firefox (modified + extensions) vs. Brave (modified + extensions)
Which one is it? I think only Firefox (default) vs. Brave (default) is a meaningful comparison. So when you say “install uBlock Origin” to make up for Firefox’s weaknesses, you are shifting the goalposts unfairly because you are not willing to grant Brave the advantage of the included adblocker. By default, Brave blocks ads and trackers, Firefox doesn’t. uBlock Origin is not a part of Firefox, it’s an extension. Why should I accept Firefox (modified + extensions) vs. Brave (default) as some kind of fair comparison? Not that this would mean that Firefox would win in the end, even with the odds altered in its favor, I am just pointing out the unfairness.
> the pdf stuff is not about protecting me from websites
Much like @Pants, you are either ignorant of the fact that the paper covers more than just unsolicited requests, or you simply choose to ignore it, proving that this is not a discussion conducted in good faith. Which one is it?
I have made my point clear here, spoonfed you even. Satisfied now?
@ Iron Heart
– brave does this by default – is not an item to list it was the question
– cookie lifetime in brave is six months for cookies set through http which is most cookies
– cookie lifetime for js cookies is a joke as sites will just respawn within days if revisit or from http cookie. mozilla added this but removed it bugzilla 1621170 because they have better solution called dynamic first party isolation
– third party cookies – firefox has dynamic first party isolation next release which is better because it covers everyone and way more things
– blocks all storage in third party frames – storage access policy since 70: blocks cookies, dom storage, messaging and workers, dom cache, browser caches, referrers for trackers bugzilla 1547813 and dynamic first party isolation is better
– referrer policy – so strict-origin-when-cross-origin – this in in firefox 87 bugzilla 1589074
– prefetching – all my browsing is https, most of web is https, and all networking is partitioned
– https alternative service – all networking is partitioned
– etags – all networking is partitioned
– blocking lists – where is proof firefox lists are weak
– experiments – is not about web pages
– sync – is not about web pages
– pdf – i read it, it nothing about web pages tracking me
what is this? you need to explain otherwise just nonsense
– address bar leak
– domain service reliability / alternative suggestions
– push
this leaves
– fingerprint – you already listed this one: good default for brave: firefox block fingerprint scripts but nice to have. ublock origins blocks lots too
– tracking parameters – is good but is super small list and is limited
see https://github.com/brave/brave-core/blob/master/browser/net/brave_site_hacks_network_delegate_helper.cc#L29
see https://github.com/brave/brave-browser/wiki/Query-String-Filter
doesn’t seem like much to me, you need bigger list
what about all the things firefox does that brave doesnt? you supposed to be expert on brave and firefox. Why do you make me do all the work and only point to articles or lists of what brave did different to chromium code base
@Anonymous
> brave does this by default – is not an item to list it was the question
???
Why do you think Firefox accepting 3rd party cookies by default while Brave doesn’t can be easily dismissed.
> storage access policy since 70: blocks cookies, dom storage, messaging and workers, dom cache, browser caches, referrers for trackers bugzilla 1547813 and dynamic first party isolation is better
“Brave by default blocks all storage in third party frames (i.e. iframes). Firefox allows all storage in 3rd party frames unless all the following are true a) the origin is on disconnect, b) this is the 6th time the origin has appeared as a third party iframe (the first 5 times are always allowed)”
source: https://old.reddit.com/r/brave_browser/comments/i8rx92/why_use_brave_instead_of_fire_fox_or_water_fox/g1aqffl/
AFAIK, this policy of Firefox hasn’t changed and is weaker than that of Brave. Dynamic FPI has just come out of alpha, don’t know why you are citing something that is still not even in the stable channel as an advantage. Isolation is a cross browser development, by the way, all browsers are moving in this direction. Chromium has isolated cache since v.86 and will isolate more things in the future, don’t pretend that this is a Firefox-only thing please.
> this in in firefox 87 bugzilla 1589074
Good to hear that Firefox now has a stricter referrer policy matching that of Brave, I guess. Firefox 87 is still in alpha and subject to change, we will see whether or not it releases with a stricter referrer policy. Please don’t list beta or alpha changes of Firefox, I am comparing the stable releases here.
> prefetching – all my browsing is https, most of web is https, and all networking is partitioned
The type of prefetching you talk about is not the only type of unsolicited connection Firefox establishes. Read my prior comment again. Firefox by default has speculative connections when you hover over links and also speculative connections when you type something into he address bar. Their predictor is also enabled by default. That they now don’t do one type of prefetching on HTTPS means very little. There are many more.
> https alternative service – all networking is partitioned
You realize that this is primarily about your re-identification by first party, right? partitioning does nothing to solve this. Please just grant Brave then win here, “partitioning” is not the answer here.
> etags – all networking is partitioned
You realize that this is primarily about your re-identification by first party, right? partitioning does nothing to solve this. Please just grant Brave then win here, “partitioning” is not the answer here. The first party has access to its own cached files with or without partitioning.
> blocking lists – where is proof firefox lists are weak
That’s what I call a weak blocklist, friend:
https://github.com/disconnectme/disconnect-tracking-protection/blob/master/entities.json
It’s pathetic compared to EasyList and EasyPrivacy (which Brave uses by default). Also, remember that Firefox by default doesn’t even use its weak anti-tracking list to block tracking scripts in non-private windows.
> experiments – is not about web pages
No, but clearly it’s an aspect of privacy. You are wrong to just dismiss this. Or do you think a backdoor into your browser is OK? It has been abused already:
https://www.zdnet.com/article/firefox-tests-cliqz-engine-which-slurps-user-browsing-data/
> sync – is not about web pages
Sync is used by many people. Again, you are wrong to dismiss it. Not having to hand over personal info here is a clear advantage of Brave.
> pdf – i read it, it nothing about web pages tracking me
What about the always open Push socket, then?
> address bar leak
Firefox leaks whatever you type to Google before you hit enter – to provide useless suggestions to you. It acts like a key logger, but it should only send queries to Google after the user hits “enter”. Not saying that you should be using Google, but this leak is concerning.
> domain service reliability / alternative suggestions
Quoting from the arkengem user.js will do here, I think:
“domain guessing intercepts DNS “hostname not found errors” and resends a request (e.g. by adding www or .com). This is inconsistent use (e.g. FQDNs), does not work via Proxy Servers (different error), is a flawed use of DNS (TLDs: why treat .com as the 411 for DNS errors?), privacy issues (why connect to sites you didn’t intend to), can leak sensitive data (e.g. query strings: e.g. Princeton attack), and is a security risk (e.g. common typos & malicious sites set up to exploit this)”
source: https://github.com/arkenfox/user.js/blob/master/user.js
Firefox does this by default (hence why the user.js recommends changing that), Brave doesn’t.
> push
“Firefox also maintains an open websocket for push notifications that is linked to a unique identifier and so potentially can also be used for tracking and which cannot be easily disabledâ€
source: https://www.scss.tcd.ie/Doug.Leith/pubs/browser_privacy.pdf (page 2)
> firefox block fingerprint scripts
This is being hampered by the weak Disconnect list and hardly blocks anything. Moreover, this is not the same as Brave having fingerprinting defenses on by default. I am not talking about the ad- and tracker blocker here.
> you need bigger list
Are you of the opinion that more minor stuff needs to be discussed? This won’t do anything to shift the balance, and as I said, a complete comparison is 4 – 5 pages minimum in size. Maybe I’ll do it in the future, but certainly not in the comment section of this article just to prove anything to you. I have mentioned relevant aspects already.
> what about all the things firefox does that brave doesnt?
Like, for example? Isolation? That’s a cross browser development and will eventually be standard in all browsers. By the way, Safari pioneered this, not FF (just mentioning because people here pretend that Mozilla came up with it).
> you supposed to be expert on brave and firefox.
I never claimed that. The experts are the people writing the respective applications and those should be the ones you should approach first. They know their stuff best, because they have created it in the first place. I am merely a commenter with an opinion, an opinion for which I can and do provide sources when requested.
> Why do you make me do all the work and only point to articles or lists of what brave did different to chromium code base
Because they a) provide more details on GitHub regarding basically anything I’ve listed, I am merely mentioning it here without further discussing it and b) because more minor aspects are also being discussed by the devs themselves(!) there. It’s more meaningful than anything I can type into a medium-sized comment.
@ Iron Heart
– You realize that this is primarily about your re-identification by first party, right – no browser has ever tried to hide repeat first party not even tor browser, no browser claims to do this. it has already been about cross domain tracking. all networking is partitioned in firefox for many more things than any other browser
– What about the always open Push socket, then – every firefox user has it and it is only used for the push service provided by mozilla – you make it sound like anyone can jack it and get id and they cant – the id is needed because that’s how ids work otherwise they cannot send push message to person
– Dynamic FPI has just come out of alpha, don’t know why you are citing something that is still not even in the stable channel as an advantage – it is in stable in six days time so needs to be included
– It’s pathetic compared to EasyList and EasyPrivacy – i dont want to look at a list, show proof that it does not block anywhere near as many trackers as brave one. firefox is a tracker blocker not an adblocker
– This is being hampered by the weak Disconnect list – so no proof here either just your say so. firefox uses the world class and world first openwpm as well
– domain service reliability / alternative suggestions – so thats what you mean – that arkengem knows its stuff
– address bar leak – ok why not just say that – real time suggestions not for everyone but most of the time user means to go there with those words – a bit overblown – people care about privacy should use better search engine. no tears for them from me
– Please don’t list beta or alpha changes of Firefox, I am comparing the stable releases here – why not? it is relevant because changes are a thing and they are only weeks away
– Are you of the opinion that more minor stuff needs to be discussed – ok you know this is minor then so why you already scream about brave defaults so offen, seems you angry about something
my last count we are at four minor things brave does that firefox doesnt. where is the rest
@Anonymous
> no browser has ever tried to hide repeat first party not even tor browser,
I stopped reading there. Why would you want a first party to identify you (or repeat visits of you) when you can prevent it? Makes no sense. Brave prevents this by not allowing eTags and HTTP Alternative Services.
> every firefox user has it and it is only used for the push service provided by mozilla
And you think Push should be opt-out instead of opt-in, right? There is no need for the Push socket to remain active at all times. It allows Mozilla to track your activities as well.
> it is in stable in six days time so needs to be included
1) Let’s see if it works as intended when it reaches stable.
2) Please don’t bring up beta or even alpha features.
And then again, it doesn’t matter. This type of isolation is a cross-browser development(!), Mozilla neither pioneered this nor are they the only one doing it.
> show proof that it does not block anywhere near as many trackers as brave one
Dude, how am I supposed to do that? Am I supposed to show you the top 10 most visited websites and compare the blocked trackers? Haha.
You can tell that the Disconnect lists are inferior by realizing that their entries are contained in other lists that are far more extensive. You can tell that is inferior because it is not among the uBlock Origin or Brave default lists, precisely because it offers nothing that is not already covered by much stronger lists. That’s all the proof you need.
> firefox uses the world class and world first openwpm as well
Nothing about Firefox is “world class”, dude. The default tracking protection is one of the most pathetic aspects of the “privacy browser”.
> so thats what you mean – that arkengem knows its stuff
No, I mean that Firefox allows this by default (which is bad), hence why arkengem intends to fix it. But we are comparing the default behavior here, right? Any other comparison is unfair and pointless. If you want to compare modified browsers, you need to say so beforehand.
> no tears for them from me
What does that have to do with an objective leak that shouldn’t be happening?
> why not?
Because beta or alpha features tend to be buggy, because almost nobody uses unstable versions (which is why such comparisons are irrelevant for others), because fairness dictates that it’s stable version vs. stable version and not alpha (modified) vs. stable version, which would make no objective sense… Need I go on?
> ok you know this is minor then so why you already scream about brave defaults so offen, seems you angry about something
You ignore and down talk evidence, you want to draw one-sided comparisons – surely it has to be me being angry for no reason, yeah. LOL.
> my last count we are at four minor things brave does that firefox doesnt.
Remove the rose-colored glasses, then re-count.
I have suspected this before my first reply to you and I am saying it again: You are not asking in good faith, you are a fanboy seeking validation for his choice. All this goalpost moving, ignoring evidence, coming up with silly notions (such as protection against first party tracking not being a thing) – all this tells me such. You are a time sink, use whatever you like. I have shown what needed to be shown here and I am not inclined to further feed the troll.
here proof of what partitioning for
https://bugzilla.mozilla.org/show_bug.cgi?id=1691728#c1
not silly idea about visit back to first party. you supposed to be expert but seems you do not understand
@Anonymous
Huh? I know what partitioning is for – but even with partitioning the first party caching files still has access to its own cached files (anything else wouldn’t make sense). You can still get identified as a repeat visitor, e.g. via eTags or HTTP Alternative Services. Stopping that is a good thing.
– Mozilla neither pioneered this nor are they the only one doing it – no ones cares if who made it firefox has it for many years as containers anyway firefox partitioning go way further than anyone else
– Because beta or alpha features tend to be buggy – not beta or alpha features when it reach stable in a few weeks
– Dude, how am I supposed to do that? – it called proof. do statistical analysis on big scale else you only guessing and make it up
– And you think Push – what is problem with single socket and push server to be standard compliant
– I stopped reading there – no browser hides repeat first party visits in session i forgot to say in session. Only tor browser try for new session. in a new session all other browser by default not hide return to first party – it called cookies and local storage – it always up to user to remove else. brave not remove cookies and first party storage by default so useless to talk about etag cache http alternatives. the reason partitioning exist is to isolate first party from each other. not your silly thinking
still only at four minor things and you have not listed what firefox has that brave not have. to be fairs and impartial why you not list the firefox things
@Anonymous
> no ones cares if who made it firefox has it for many years as containers anyway firefox partitioning go way further than anyone else
You realize that this is a cross browser development, right?
> not beta or alpha features when it reach stable in a few weeks
Then I will discuss them in a few weeks. Betas are subject to change, you don’t know whether or not it will hit the stable channel and be enabled by default there. Bringing in betas and alphas into the discussion is pointless.
> it called proof
It is demonstrable that the list is weak by the entry count alone, all its entries are part of far more extensive lists (lists that e.g. Brave uses by default). Believe what you want, I won’t write a half a PhD thesis here just to prove anything to you. Ask gorhill why Disconnect is not among the default lists of uBO, then ask the Brave devs the same thing. They’ll tell you the same thing I told you. Quite literally.
> what is problem with single socket and push server to be standard compliant
Why does it always have to be open? Why is it not opt-in? The study calls it problematic, are you arguing here that it is not? Seriously?
The Push implementation being standard compliant doesn’t mean that it has to be enabled by default (hence the socket).
> no browser hides repeat first party visits in session
Brave does this within the same session e.g. by blocking eTags.
> so useless to talk about etag cache http alternatives
Why should this be useless? Cookies (first party at least) need to be allowed for web compat reasons (e.g. logins), there is only so much you can do without making the experience horrible for your users.
> the reason partitioning exist is to isolate first party from each other. not your silly thinking
Partitioning does not protect you from the tracking of repeat visits by a first party – the first party has access to its own files even under a partitioning scheme. eTags and HTTP Alternative Services are methods to identify repeat visitors (Brave blocks both of these methods). So are first party cookies, but Brave has to allow first party cookies as to not break websites (mainly logins). Furthermore, websites can use eTags and / or HTTP Alternative Services as an alternative(!) to cookies, so blocking this is good because it could potentially be the sole method of re-identification on websites.
> firefox things
Such as? Firefox has the most extensive isolation so far, but it is really a cross browser development. All browsers already have that or will have it in the future. What’s the big deal here?
– You realize that this is a cross browser development – no one care. this is silly argument just like stupid one about who invent. firefox cover way more things than other browsers so not cross browser sameness
– Brave does this within the same session – does not cause it not auto remove all other normal tracking like cookies by default. no browser, not even tor browser, try to hide repeat first party visit in session. you make huge stretchy bad lies
– The study calls it problematic – listed as it use mozilla server with id which mean potential not proven tracking by mozilla. they not talk about anything to do with socket open. you maybe should read pdf
– It is demonstrable that the list is weak by the entry count alone – that really stupid talk. cannot take you serious anymore with silly argument that quantity is same as quality. firefox is a tracker blocker not adblocker. your answer is no good, it very dumb. brave catch ads so it can use it own crazy bats. firefox not care about the ads just the tracking part. so you no have proof then
– Bringing in betas and alphas into the discussion is pointless – dynamic first party isolation land in four days so not pointless. why you upset at major firefox thing in four days?
still at only four minor things, where all the other 4 or 5 pages? where the big things?
@Anonymous
> no one care.
LOL, you are hell bent to sell this as a Firefox feature, are you? OK, point taken, just to end this discussion.
It’s of course not a cross browser development that will be in all browsers in the end. /s
> does not cause it not auto remove all other normal tracking like cookies by default.
I told you why already – disallowing cookies breaks login forms hence why this is not done! Does that mean that you have to allow eTags and HTTP Alternative Services? No. Some websites use eTags and / or HTTP Alterntative Services INSTEAD of cookies, how about that? You are so unwilling to grant Brave a win, it’s ridiculous.
> potential not proven tracking by mozilla.
So not an issue that needs correction, then. LOL.
> cannot take you serious anymore with silly argument that quantity is same as quality.
My dude, ask the Brave devs or gorhill why the Disconnect lists are not part of Brave or uBlock Origin by default, what are you afraid of? Clearly those devs do not consider the Disconnect list good enough (and yes, in both instances pure anti-tracking lists are also being shipped by default), so why should I? Firefox’s default tracking protection (which does not even block tracking scripts in non-private windows unless you change that, lol) is a joke even compared to the EasyList alone. Get over it.
> brave catch ads so it can use it own crazy bats
Yeah you are unbiased and inquiring in good faith, obviously. Yeah, lol.
Listen, Firefox fanboi: Brave Rewards are not even enabled by default in Brave, the user can choose to activate it. Moreover, Pocket Stories in Firefox are based on the very same principle (a local algorithm picking from articles based on your browsing), but I don’t see you complaining about that, you hypocrite. Contrary to Brave, it’s enabled by default in Firefox.
> so you no have proof then
I have proof that you ignore. Not quite the same thing.
> so not pointless
If you say so.
> only four minor things
Count the number of things in my original reply to you again. You choose to be willfully ignorant of most, proving my point that you are not inquiring in good faith, meaning any further discussion with you is pointless and a waste of time.
– OK, point taken – good you now realize who invent and who did part of it first not matter, only how well they do it and for what
– Brave Rewards are not even enabled by default in Brave – you so silly. if brave not detect ad then they cannot put in own ad for crazy bat for those who want crazy bats. it not about default. it all about detecting ads. firefox not an adblocker, it a tracker blocker. as for local algorithm no one asked and is not relevant. you trying to hide with words instead of answering question
– I told you why already – I not need to be told. you try claim brave protect from repeat first party visit. you tell giant fibbers. no one say you not allowed to have cookies. i say that brave not protect all the other tracking methods for repeat first party. no browser do that. only tor browser does it for new sessions by default. your argument nonsense and not relevant
– ask the Brave devs or gorhill – brave is adblocker, ublock origins is content blocker – not the same as firefox which is tracker blocker. why you not able to read? it up to you to prove with scientific tests and data else you telling whopper piggies
hypocrit? i never bring up pocket. why you talk other words to distract?
fanboi? why you so nasty rude to me? i never call you names
am still at 4 minor things. if every thing else is all minor things as you said, then it not really 5 pages. and no big things. i was expecting some big brave specialness, but not so. you are supposed to be expert and you not even able to make a list or get brave own stuff right. very disappointed and sad at you.
ah yes. almost forgot. did you like my joke. i repeat here in case you miss it
“i also want to make joke, hope it ok in english. iron heart make vast quantity of comments but quality is very bad. this prove quantity does not equal quality. haha, i should be comedian”
is even more funny second time, haha. very good. nice to see you end conversation and we agree only 4 minor things
> By tweaking ANY BROWSER, i.e. trying to reach the level of privacy which FIREFOX provides by default, you are only fingerprinting yourself, thereby ironically reducing your privacy
FTFY. The link says “browser” not specifically “Firefox”
—
> Study finds Brave to be the most private browser by default
NO IT DOES NOT
The paper analyzes “What Do Browsers Say When They Phone Home” – it’s right there in the title. It does not cover actual web tracking or real life usage, like, you know, browsing loads of sites, or addressing hundreds of other parameters.
It is very narrowly focused on connections to back-end browser “services”. It also only states a POTENTIAL privacy issue with Firefox’s telemetry due to the temp logging of IP address. Wear a VPN if you can’t socially distance.. or you know, like, if telemetry is freaking you out, turn 99.999% it off with a single click in preferences.
> These observations regarding use of identifiers are consistent with Firefox telemetry documentation and it is clear that these are used to link together telemetry requests from the same browser instance. As already noted, it is not the content of these requests which is the concern but rather that they carry the client IP address (and so rough location) as metadata
What really matters is how your privacy is being protected as you visit hundreds, thousands of websites and pages a day. Such as blocking redirect referrers, blocking known trackers (ETP is for tracking, not ad blocking), clearing windows.name on eTLD+1 changes, mitigating history sniffing, and dozens of other measures not present in other browsers. And networking partitioning (and soon dFPI isolation for persistent web storage).
The truth is that Firefox is the most private browser by default. But here’s the real kicker… when configured by, you know, internet savvy smart knowledgeable people, Firefox gets even more private: doing yet dozens more things other browsers can’t
tl;dr:
– best privacy browser by default: Firefox
– best privacy browser ability: Firefox: exhibit A: tor browser
@Pants:
As a regular user of a modified (i.e., tweaked) Firefox Nightly, fortified with additional privacy extensions, I agree — from lengthy experience and, constant daily checking for leaks and breaches of anonymity — that such combination provides superior privacy in comparison to what other browsers’ offer; even Brave and ungoogled-chromium.
> the pdf & “phoning home”
paper: https://www.scss.tcd.ie/Doug.Leith/pubs/browser_privacy.pdf
IH claims the pdf says “Brave is the most private browser by default”
ME: LIES by omission of the “phoning home” part
– it specifically says it only looks at a very narrow range of “phoning home” (their term)
– it also found zero proof, only potential, in Firefox on some of these matters: i.e it does NOT say that Firefox invades your privacy
– because it does not look outside it’s very narrow range: then it is clearly not looking at the overall privacy of a browser: nothing about 3rd parties on web pages, persistence web storage, caching, partitioning/isolation, referers, redirection trackers, trackers in general, windows.name, etags, fingerprinting … and 100+ other things
IH: says I’m wrong. Says something about a websocket, push services, search autocomplete
ME: RTFM
– search autocompete
– PDF (caps mine): “This happens via the search autocomplete feature… FIREFOX SENDS NO IDENTIFIERS alongside the web addresses”. This is still in their narrow range of what they call “phoning home” as search autocomplete ultimately involves subsequently connecting to the search website and chrome for example abuses that
– PDF: “Firefox includes identifiers in its telemetry transmissions to Mozilla that are used to link these over time”. AFAIK, Firefox search autocomplete is aggregated as a count per engine for telemetry. There is NO evidence of Firefox doing anything dodgy here, and of course, you can disable telemetry. That’s not the point. The point is that this is still in their narrow range of “phoning home”
– websocket: used for the push service: PDF: “Firefox also maintains an open websocket for push notifications that is
linked to a unique identifier and so potentially can also be used for tracking”: note the word “POTENTIAL”
– push services are required for push notifications: there has to be a server somewhere and you require a UUID to use it (otherwise how can a server know who to send it to). The server here is a mozilla domain
The pdf does NOT claim Brave is the most private browser by default, it only claims that it SEEMS (because there is no proof otherwise of anything untoward in Firefox) to be so WHEN IT COMES TO “phoning home” (which is their words, not mine) in a very narrow range of connections/purposes
AN IH EPIC FAILURE on how to comprehend technical papers. Q.E.D
@Pants
Stop misrepresenting the paper. While it says that it covers “phoning home” in the title, the open Push socket can also be used as an identifier as far as web tracking is concerned. Likewise the address bar leak a.k.a. search autocomplete, that is not phoning home, that is leakage. Both appear in the paper in spite of the title.
That push can have beneficial uses was not denied by me or the paper, what is being criticized is that the Push socket remains open in Firefox at all times – push should be opt-in, not opt-out, if privacy were a concern for Mozilla. Likewise telemetry, should be opt-in, but isn’t.
Your refutations are speculative and give Mozilla the benefit of the doubt in all cases (hence why I do not trust you to hold Mozilla under “scrutiny”, point in case: https://www.ghacks.net/2021/02/01/firefox-85-for-android-released-with-drm-stream-support-and-usability-improvements/#comment-4485061 ) You would be the last people I trust with that, when there is a privacy issue with Firefox, give Mozilla the benefit of the doubt, if there is one with Brave (good luck with finding one, you haven’t yet), then scream blue murder.
Funny sight to behold, by the way, your dancing around the fact that the paper declared Brave the most private browser (concerning the aspects it studies), in your words, Brave is only “potentially” the most private browser in the study, whereas the problems with Firefox are also only “theoretical” or “potential” in nature. It’s like the devil and the holy water – you can’t let Brave win, when it happens, it has to be a “potential” (not actual) win. If Firefox had won anything there, it would be the “hard facts” and “obvious”, I am sure of it. And you wonder why people (including myself) call you a shill? Wonder no more.
> Q.E.D
Sweet. Is that meant to add an appearance of credibility or conclusiveness to your irrelevant and speculative ramblings? I thought so…
“best privacy browser by default: Firefox”
Pants is a Mozilla * [Editor: removed, please stay polite] like Iron Heart is a Brave * [Editor: removed, please stay polite], he doesn’t place either user interests first, he defends the company first:
https://www.ghacks.net/2021/02/01/firefox-85-for-android-released-with-drm-stream-support-and-usability-improvements/#comment-4485061
It’s why there are usable and secure browser forks that disable Firefox’s default data collection, third-party trackers and ads like Waterfox or Fennec F-Droid and he acts like they don’t exist.
@Pants: you said
Huh? If FF is the best privacy browser by default and ability, the moment you make 1 tweak through that ability, you stand out for fingerprinting. So, aren’t you contradicting yourself?
Another point: Brave does not have to be tweaked for privacy so all Brave browser users look alike.
As for Tor, you present it as if FF = Tor. Tor is FF-based, but from a privacy point of few they are different, with Tor being better privacy-wise, I should think?
@Pants
> FTFY. The link says “browser†not specifically “Firefoxâ€
Yeah, however Firefox in theory needs to be “tweaked” for things which Brave already protects by default – and users are more easily detectable by virtue of their “tweaking”.
> NO IT DOES NOT
Yes it does.
> The paper analyzes “What Do Browsers Say When They Phone Home†– it’s right there in the title. It does not cover actual web tracking or real life usage, like, you know, browsing loads of sites, or addressing hundreds of other parameters.
Obvious lie. I am quoting from the paper:
“The search autocomplete functionality can be disabled by users, but in all three browsers [Chrome, Firefox, Safari] is silently enabled by default. Chrome sets a persistent cookie on first startup that is transmitted to Google upon browser restart. Firefox includes identifiers in its telemetry transmissions to Mozilla that are used to link these over time. Telemetry can be disabled, but again is silently enabled by default. Firefox also maintains an open websocket for push notifications that is linked to a unique identifier and so potentially can also be used for tracking and which cannot be easily disabled”
source: https://www.scss.tcd.ie/Doug.Leith/pubs/browser_privacy.pdf (page 2)
Search autocomplete and the open push socket are not only about phoning home, especially the open push socket is detectable by adversaries.
> Wear a VPN if you can’t socially distance..
I need a VPN to anonymize the telemetry that goes out of “the” privacy browser? How come?
> turn 99.999% it off with a single click in preferences.
Why can’t I turn off 100%? Also, it’s more than a single click, and requires knowledge about hidden by default(!) preferences:
https://www.ghacks.net/2018/09/21/mozilla-wants-to-estimate-firefoxs-telemetry-off-population/
> What really matters is how your privacy is being protected as you visit hundreds, thousands of websites and pages a day.
Are you saying here that protection from the browser developer is irrelevant? Is that your new stance after Mozilla started using connections for which there are about:config controls? Doesn’t matter all of a sudden because you can no longer fix it? LOL.
By the way, Brave has far better protections in relation to websites. Just saying.
> The truth is that Firefox is the most private browser by default.
By default? Ahahahahahahaha, then why does the arkengem script exist? Isn’t that meant to “fix” Firefox’s lax privacy standards (more on that below, and what it really means for naive users)? Are you calling yourself irrelevant here?
> But here’s the real kicker… when configured by, you know, internet savvy smart knowledgeable people, Firefox gets even more private:
“Smart people” (such as the Whonix devs) call out your shit for what it is:
“You cannot configure your browser to prevent tracking either. Everyone will configure their browser differently so when you change a bunch of about:config settings such as privacy.resistFingerprinting and pile on browser extensions like Privacy Badger, you’re making yourself stand out and are effectively reducing privacy.â€
“The only real approach to preventing browser tracking/fingerprinting is by using a browser that is designed to prevent this by default and the users do not change it. The most effective browser that does this is the Tor Browser.â€
source: https://madaidans-insecurities.github.io/browser-tracking.html#configuring-the-browser
Usage of your irrelevant script presupposes that people do not realize that any website-related change to the default config is detectable and can be used to fingerprint them. As I said, I can detect that you are “the guy who cared”.
One practical example? Firefox allows WebGL by default, I can detect whether or not it’s enabled by letting Firefox render some canvas. Your script recommends disabling it, I can immediately detect that it’s not enabled – the browser fails to render the Canvas. Tor Browser behaves like your script, but I can tell that you are not using Tor at the network level, even if you opt for Firefox ESR (on which Tor is based), and if you use the regular stable release instead of Firefox ESR, I can just do some more feature detection and thus separate different versions of FF from each other, and thus can tell that you are not using Tor just based on the version of your browser.
In summary, users of your script make themselves more unique by differentiating themselves from the default behavior (not just in case of WebGL, there are many more examples). I’d have a field day with your users. Truly, the arkengem privacy reduction script in all its undeserved glory.
> best privacy browser by default: Firefox
Evidently false.
> best privacy browser ability: Firefox: exhibit A: tor browser
Tor Browser is a Firefox fork with higher privacy standards BY DEFAULT (implying that Firefox is lacking in that department). Due to the fact that they enable these privacy protections by default, users don’t have to fingerprint themselves to enable them, as they would have with arkengem (and thus make themselves more unique).
> fingerprinting
You have gone off topic. You made false claims about containers and Firefox’s isolation of Origin Attributes and seemed to delight in setting up hundreds of profiles..
… and now you want to debate fingerprinting? Not going to happen: you have already shown previously that you do not understand fingerprinting, entropy or how linkability of traffic works. It’s pointless trying to have a discussion with you, as you severely lack knowledge: you’re a waste of time: examples below
—
Link: https://www.ghacks.net/2020/12/28/are-you-protected-against-online-tracking-the-effs-cover-your-tracks-site-has-the-answer/#comments
– Me: as evidenced by your previous claims that a site can correctly, 100% guaranteed, correlate or linkify traffic on their site to a single user just because, **unknown** to them, there was only ever one person with that FP who repeatedly visits them … [snip] … User with fingerprint X visits site Y several times a month. Site Y sees 10 visits from fingerprint X and claims it is the same user. That’s not how it works
– IH: if there is only ever one person with e.g. your setup visiting a website, then the website can 100% it is the same user
Just read my comment at January 2, 2021 at 5:22 pm : https://www.ghacks.net/2020/12/28/are-you-protected-against-online-tracking-the-effs-cover-your-tracks-site-has-the-answer/#comment-4481985
tl;dr: Randomizing is detected and returns a static value for those metrics)
– site X: ten Brave users with fingerprint B visit once each
– site X: one Tor Browser user with fingerprint T visits ten times
– what does the site see?: it sees 10 visits each from fingerprints B and T. It cannot tell any other differences between them
– IH claims Tor Browser fails and you are linked, but Brave is fine
– flip it (one brave user visits ten times) and apparently Brave is still safe: because Brave is magical
– in the link we are talking about Tor Browser, which lowers entropy and has numbers of substantial users in each FP. There is no confusion here about a Tor Browser user having a unique FP. The debate was about randomizing vs lowering entropy, and this isn’t the only time
Also: me: all randomizing can be detected and rendered to a static value, and is ultimately no better than lowering entropy. IH: argues for ten posts. Me: yes it can. IH: you can’t link Brave users via FPing because it’s farbled, see panopticlick. Me: panopticlick is returning a static value :facepalm:
When it takes twenty posts over two or three threads to get you to understand that all randomizing can be rendered to a static value, then it’s not worth debating FPing with you any more.
> Firefox in theory needs to be “tweaked†for things which Brave already protects by default
You keep saying this: and then usually list about four or five things: like “sane” referrers etc. Is that it? Four or five things? Is that it? Give us a real list, go on
Brave in reality, cannot be “tweaked” via flags for things which Firefox already protects by default which have a huge impact on web tracking: e.g. superior network partitioning… and, wait for it … dFPI (rolling out next release: https://bugzilla.mozilla.org/1686296). Then there’s window.name protection, timing mitigations, history sniffing mitigations, sanitizing of redirect trackers, third party tracking shims e.g. google ones (does Brave have that?), and dozens and dozens more.
Brave also, in reality, cannot be “tweaked” for many things which Firefox can do if prefs are flipped.
The reality is that Firefox has far more built-in privacy ability and impact than any other browser. I don’t give a shit about defaults, I only care about what the browser is capable of doing. You go stick to your 200 profiles inferior chromium setup or whatever, lols
—
> [pants] like, you know, browsing loads of sites, or addressing hundreds of other parameters
IH: but search autocomplete…
Me: RTFPaper. Show me where the paper looked at any web site tracking tech: such as persistent web site storage, caching, referrers, fingerprinting, etc
Your claim that the paper says the Brave is the best browser for privacy by default is pure bullshit: They concluded that Brave seemed to be the best browser for privacy, on appearance, for “phoning home”
Here: https://www.zdnet.com/article/brave-deemed-most-private-browser-in-terms-of-phoning-home/ .. read the title
– … IN TERMS OF PHONING HOME
Stop making up BS claims. If Brave was truly what you said it was, then you wouldn’t need to lie, would you
@Pants
Also, since I am apparently unworthy of the attention of Your Serene and Royal Highness, would Your Highness at least care to address what @Klaas Vaak has said:
https://www.ghacks.net/2021/02/10/brave-browser-adds-native-support-for-ublock-and-fanboy-annoyances-lists-and-social-list/#comment-4485743
He raises the same (valid) point of an alteration of the default setting being great for others trying to fingerprint your users, and he wasn’t blessed yet by the attention and so-called expertise of Your Majesty.
If you fail to address my point because of my inherent and totally proven unworthiness (and not because you don’t have any refutation to offer, lol), then would Your Majesty at least be so kind to reply there, so that the all-encompassing knowledge of Your Serene and Royal Highness may guide us foolish sinners the way?
@Pants
You have not comprehensively compared Firefox or Brave either, despite claiming superior expertise in that area, but you expect me to do it? Come on… Nevertheless, you still fail to understand that defaults matter:
> I don’t give a shit about defaults, I only care about what the browser is capable of doing.
…which is grotesque, because by suggesting that users should alter the default settings in areas that concern the fingerprint, they are fingerprinting themselves, namely by not sticking to the default settings. Again, I can detect that you altered things, that you are the “guy who cared”, and you stick out because of that, in a fairly extreme manner.
> You go stick to your 200 profiles inferior chromium setup or whatever, lols
Do I need to reply to that kind of trolling, or…? Being based on Chromium is a good thing (security / performance / web compatibility).
> but search autocomplete…
OK, why do you ignore the open push socket, which would be the far more interesting topic to discuss? Was that deliberate?
> They concluded that Brave seemed to be the best browser for privacy, on appearance, for “phoning homeâ€
While “phoning home” would be an aspect of privacy, and while the paper chose this for a title, it also discussed other things, like the aforementioned always open push socket of Firefox. It’s hilarious that you ignore that, riding to death the title of the paper (as if people can’t read any further), without once addressing the actual content, even when I specifically quoted it.
> If Brave was truly what you said it was, then you wouldn’t need to lie, would you
No, I wouldn’t, and I didn’t. Your point being?
I don’t know why you are always implying that I have no idea of fingerprinting!? I mean, I can be wrong at times, and so can you (and you were, repeatedly). You are constantly, and I mean CONSTANTLY, misrepresenting some of the stuff I have said. Please stop, this should be beneath you, but apparently it isn’t…
> … and now you want to debate fingerprinting? Not going to happen:
Proceeds to discuss fingerprinting, and my trumped up “errors”.
> **unknown** to them, there was only ever one person with that FP who repeatedly visits them
Again, as I’ve told you – it’s NOT unknown to them. They identify users at the network level (IP address, which is unique). I also stated, and I continue to maintain that, maintaining Tor’s uniform fingerprint is difficult for users because of the breakage it causes. When I encounter breakage and really want to to a website, I have to relax settings, destroying the common (canonical) fingerprint. A fingerprint altered in this way is more unique and that is a weakness of the approach of “making everyone look the same” – this approach requires a kind of discipline that is unlikely to be maintained for web compat reasons.
> IH claims Tor Browser fails and you are linked, but Brave is fine
Again, we were 1) not discussing the Tor browser there, merely Tor’s concept of fingerprinting which is borrowed by Firefox and vice versa (improvements are being handed over in both directions). With Firefox, you have no protection at the network level, so what good is a static canonical fingerprint if your IP address leaks? Anyhow, the way you represent, or rather misrepresent, our dialogue, fails to account for the fact that I have pointed out again and again, and still do, that Tor’s static fingerprint is not a bad idea as a concept(!) for a laboratory, but unlikely to realistically work in real world environments where users more than just occasionally have to relax settings to unbreak websites!! Brave is not “magical”, randomization just tends to cause fewer breakage, meaning it’s easier for its fingerprinting protections to remain enabled and stay intact.
> which lowers entropy and has numbers of substantial users in each FP
Contrary to the users of your irrelevant script, Tor users are indeed relatively many in number, and Tor protects privacy by default, so that users do not have to fingerprint themselves to achieve “better privacy” (while ironically reducing their privacy in the process). Since you do not even understand that destroying the default configuration makes your users more unique, I don’t think you have the right to challenge anyone else’s understanding of fingerprinting – you do not even get that one right. The Whonix developers (proven experts in the realm of privacy and anonymity, more so than a non-coder like you will ever be) are very negative towards random user.js scripts meant to “improve” the privacy of Firefox while achieving the plain contrary in reality.
You are massively lying about me here by strongly misrepresenting my points, putting words in my mouth (your usual tactic), and you also lie by omission when it suits you. Tired of that. I sometimes wonder why I am even replying to you when you have to actively alter what was said, in order to supposedly prove a “lack of understanding” on my part (Again, I can be wrong, but you should cease lying about me for once, wait for the moment when it really happens, at least.). Why am I even addressing those falsehoods? The only explanation I have to offer here is some kind of masochism on my part, I guess.
I tried using Firefox today, it was horrible.
I recently started experiencing troubles watching YouTube videos on PC Chromium-based browsers, I think it might be related to nVidia drivers as AMD users seem to not be affected even with Chromium browsers.
So as a last resort I decided to try use Firefox for a day. Sure, the same problem with YouTube videos was not present in Firefox, but in turn there were a whole plethora of other problems, specific to Firefox.
1. I could not find a decent Autoplay Blocker extension on their Extension store, the ones there did not work and the built-in Autoplay Block function did not work either, hence why I started looking for an extension.
2. Many websites that work flawlessly in Chromium browsers as well as loading in lightning fast speeds were slightly broken and loaded visibly slower in Firefox. One of them was Steam, another one was YouTube – while the playback problem was not there, the whole page took 4-5 seconds to load, whereas in Chromium it loads in 1 second.
I have been saying Firefox has been a joke since 2008 when Chrome launched. On a few occasions I tried to go back to using it only to reassure myself that Firefox is still an even bigger joke.
The problem I have with YouTube on PC + Chromium is only YouTube specific – Google messed something up big time as no other website with videos causes me any trouble. So I’d much rather live with YouTube’s problems on Chromium and have the rest of the internet work flawlessly and load at lightning fast speeds than deal with Firefox’s crap on 8 websites out of 10.
1. It’s literally in settings:
https://support.mozilla.org/en-US/kb/block-autoplay
2. That’s a good thing. Means no sites are being visited without your action. Nothing gets preloaded, and some pages load slower as a result.
“Slightly broken” is very vague. How were they broken, and how do you know it wasn’t the other way around (broken in Chrome, but since you’re used to the broken way you consider the correctly displayed ones in Firefox to be broken)? FWIW both Steam and Youtube show fine in Firefox for me. Youtube funnily enough is snappier on Firefox too.
Soon you will be able to ad your own list like “https://myFilter.com/Badware.txt .
It’s on the Roadmap.
Adding the uBlock and Fanboy lists is a good move as they are well maintained (and Fanboy = ryanbr is part of the Brave team, btw.).
However, the possibility to add custom lists would be a questionable decision right now. Experience tells that many users would add more and more lists – and would ultimately run into problems on many sites because of false positives. And since Brave doesn’t have a logger like the excellent one in uBlock Origin it’s virtually impossible to find what’s causing those problems.
So if Brave really lets you add your own filter lists they should also implement a good logger. Otherwise they will be confronted with countless support issues.
“But the add-on does more than that and supports custom lists, filters, and elements, so you may want to keep it anyway. That’s what I would do.”
Instead of bundling ublock origin without this costing them any bucks, they spent money to make a version where users are denied the freedom to add the filters that they choose, and with various other handicaps.
Bathing in Google and other ad and surveillance money sources to pay developers -> castrated nuisance blocking like above (or none at all). The same rule applies to all browsers with such malware deals to make money (hello Mozilla !).
Ublock origin developed by one person as a hobby without even accepting donations -> proactively pro-user nuisance blocking (alas with the only exception of Mozilla ads, of which the removal was denied).
As for the “Brave did it partly for us, not just for themselves” argument of linuxfan, no, if a user is advanced enough to add filters himself, it’s his responsability to be able to unbreak false positives by disabling what he added, depriving all users of this freedom just because of this “risk” is anti-user and a rationalization for badly motivated corporate behavior. Besides, if community lists can accept that alleged load of “countless support issues” for free (like ublock origin filters, and easylist filter lists before they sold out to Brave), why could not those lists under corporate control with lots of money ?
It is similar to the excuse given by Mozilla to reject bundling ublock origin, “but false positives bad for you !”, when blocking ads would still do far more good than bad for the users, and if they really cared about this problem they could very easily contribute to the unbreaking effort in the community lists. The real dirty reason of these businesses, that they sometimes more honestly give when they feel comfortable enough to speak their heart, is that they don’t want to risk losing the friendship of the surveillance industry which pays their salaries. Like Google paying them to direct users to their search result pages with unblocked ads, or Scroll paying them to direct users to their partner sites with their unblocked trackers…
for now i only use uBlock origin for better element blocker.