Acronis Ransomware Protection review
Acronis Ransomware Protection is a new security program for Windows designed to protect the system against ransomware attacks.
Users of Acronis True Image 2018 may notice that it looks similar to the built-in anti-ransomware protection of Acronis' backup solution. Acronis Ransomware Protection is a standalone version of the True Image 2018 component that is available for free.
Note: You need to sign in to an Acronis account or create a new one before you can start using the security program after installation. Account creation happens in the program, but the email address needs to be verified within five days of creation.
Acronis Ransomware Protection is compatible with Windows 7 Service Pack 1 and newer versions of Microsoft's Windows operating system.
Acronis Ransomware Protection
A wizard guides new users on the first start. The program's core concepts are explained in the tutorial, but it is mostly self-explanatory.
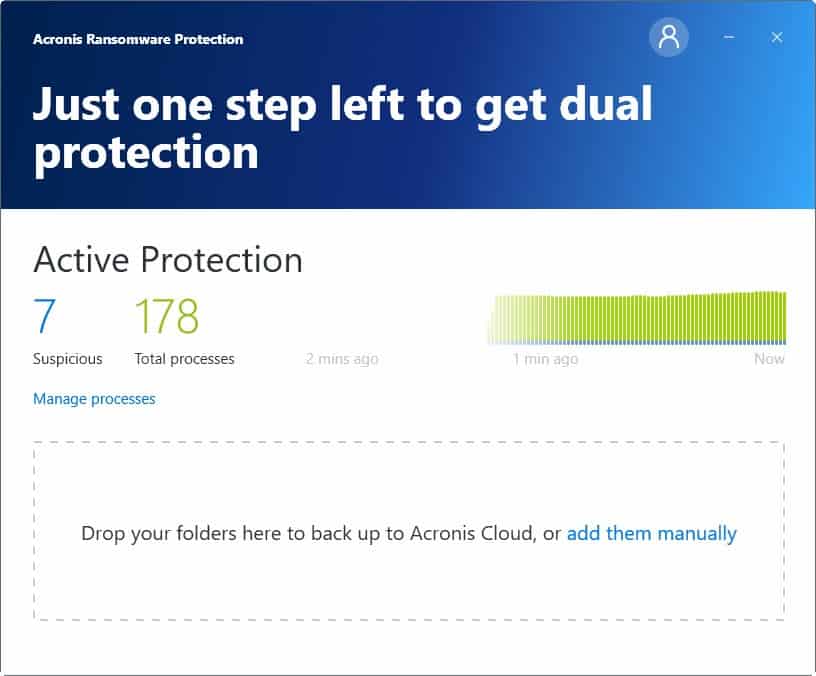
Acronis Ransomware Protection displays the number of total processes and suspicious processes in the interface. There is also a graph that shows changes over time, and an option to manage processes.
A click on manage processes lists all suspicious processes in the application's interface. QuiteRSS, Windows Firewall Control, Veeam Endpoint Backup and even rundll32.exe were listed on a test system.
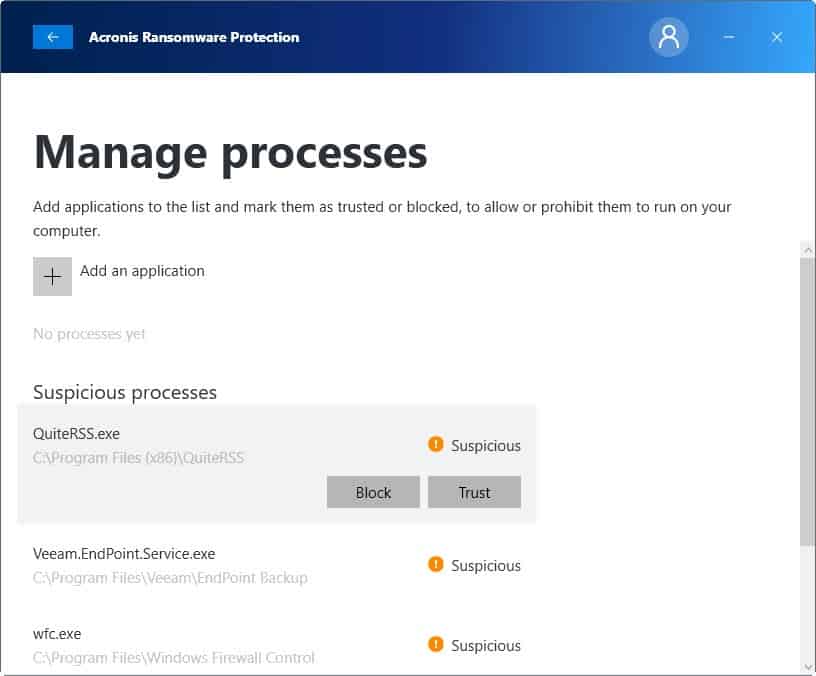
You can block or trust any process listed on the page, and add new applications to the list to either allow or block them from running on the computer.
Acronis notes that it stops suspicious processes that try to encrypt files or inject malicious code into the system, and that users are notified about that immediately.
The program assists users in recovering files if the ransomware encrypted data before the security program could put a stop to the attack. Acronis notes that it supports recovering file copies from caches, temporary files or backups.
Acronis Ransomware Protection comes with built-in backup functionality. Users get 5 Gigabytes of online storage space which they may use to back up important files. Additional space starts at €9.99 per year for 250 Gigabytes and goes up to €39.99 for 1 Terabyte of space.
Simply drag and drop files or folders to upload them to Acronis servers.
The program checks for changes in 15-minute intervals and uploads new data to the cloud. It uploads only changed data and not the entire file.
Acronis Ransomware Protection retains some file versions and not all of them to save disk space. The following versions remain in storage while all others are deleted automatically:
- The last four backups.
- The first version of every hour for the last 24 hours.
- The first version of every day for the last week.
- The first version of every week for the last month.
- The first version of every month.
Users can sign in to the cloud storage to manage their files online. Files can be deleted online, and there is even an option to delete an entire backup.
The ransomware protection
The built-in ransomware protection uses a heuristic approach.
Based on a heuristic approach, this technology monitors processes running on your computer by using the real-time mode. When it detects a third-party process that tries to encrypt your files or inject malicious code into a healthy process, it informs you about it and asks if you want to allow the process to modify your files or block the process
Heuristics is a two-edged sword. While it may pick up altered ransomware strains, it is prone to false positives as well.
The application requires Internet access to communicate with Acronis servers to function properly.
Closing Words
Acronis Ransomware Protection is a new anti-ransomware software for Windows. The core differentiating factor is the built-in backup module which users may use to store files safely in the cloud. Five Gigabytes are enough for securing important files and the price of extra storage does not break the bank either.
You cannot exit the program while it runs. This is a bad design decision in my opinion. While you can disable protection, you cannot terminate the program using built-in controls.
Related articles
- Anti-Ransomware Software Overview
- Bitdefender Anti-Ransomware released
- Bitdefender Ransomware Recognition Tool
- CyberSight RansomStopper anti-ransomware for Windows
- SBGuard Anti-Ransomware hardens Windows
- TrendMicro Ransom Buster: Windows ransomware protection

























Great article, I used Acronis for a long time until I found Avitres.com Snapshot Backup. Much easier to use and more cost effective. I still like Acronis they just are a little to much cash I feel like. The priced out a lot of the SMB
LOL! “Ransomware Protection” – another fancy name for baiting users into purchasing a standard incremental backup plan.
just looked at ransomstopper and read their deal. they want to collect all info on your computer and then share it with anyone they wish. not for me. i will stick with good backups and sandboxing.
I prefer RansomStopper (Cybersight company). Completelly Free to home and personal users and paid version to business.
Worked there. I’ve seen how programmers amused to themself why their algorithm for some reason is locking system files. Pretty amazing company.
Forced Registration, no go. instantly uninstalled.