AChoir forensic script for Windows
AChoir is a free program for the Windows operating system that collects forensic information from a live system using popular tools created by Nirsoft, Sysinternals and others.
If you want to retrieve information from a PC, for instance about users, the browsing history or installed hardware, then you can run a bunch of free programs for that.
One of the issues that arises is that most programs are focused on a single task only. If you take Nirsoft applications for instance, you will notice that they return a single set of information, and that you will have to run several programs to dump all the information you require.
Scripts improve the process by letting you run all tools one after the other in an automated process.
AChoir
That's where AChoir comes into play. Designed for users who have not created their own scripts yet, it can be run with a default set of parameters to get a good rundown of a PC it is executed on, or customized to add or remove commands and programs from the analysis.
To get started, download the file AChoir-Inst.exe from the project's GitHub repository. Simply click on it, and select Raw view mode when it is opened on its own page on the site.
Run the program afterwards on your system. The installer does not install the file on the system but places it into a directory of your choosing.
It will download the programs that it is designed to use by default during that process, so make sure it is allowed to use the Internet.
You can save the data to a local directory or a removable drive depending on your needs.
Note: The dump and log that AChoir creates is usually quite large as the program will create a memory dump by default.
Once the data has been downloaded, run AChoir.exe or AChoir64.exe with elevated privileges (right-click and select run as administrator) whenever you want to dump data and generate a report.
AChoir runs all commands afterwards, usually one of the downloaded programs with certain parameters, and creates a subdirectory in the program's root folder where it places all data in.
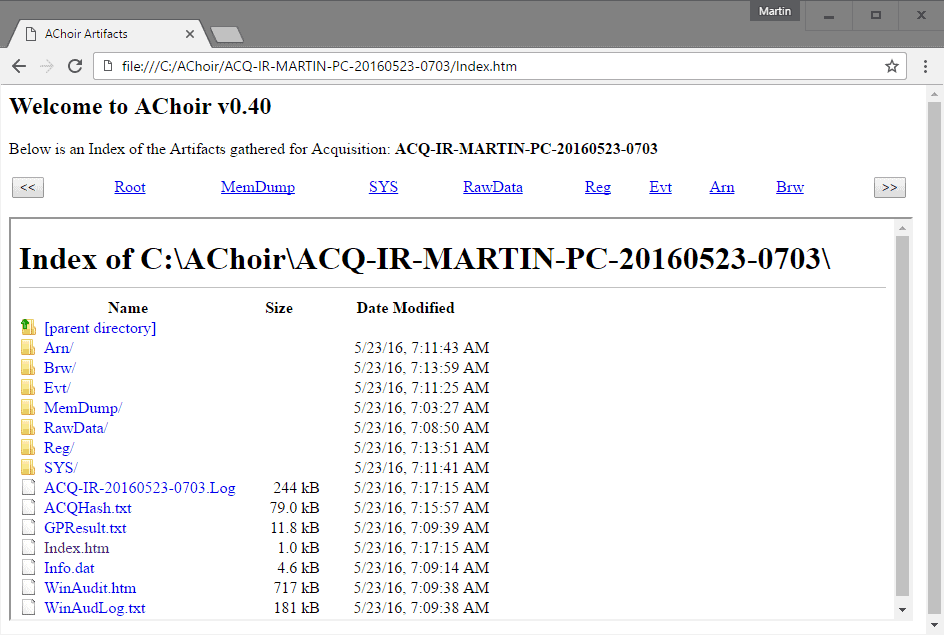
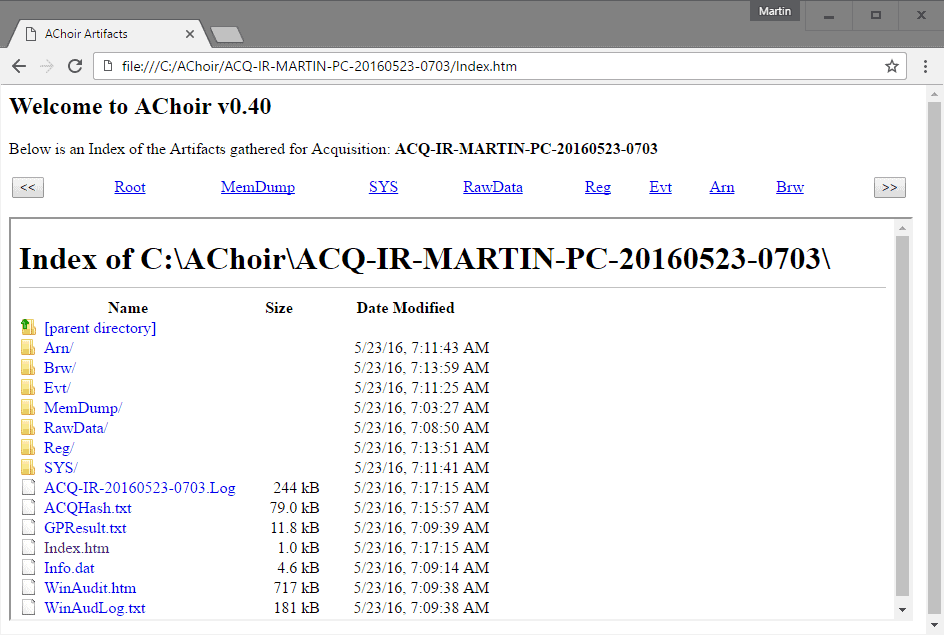
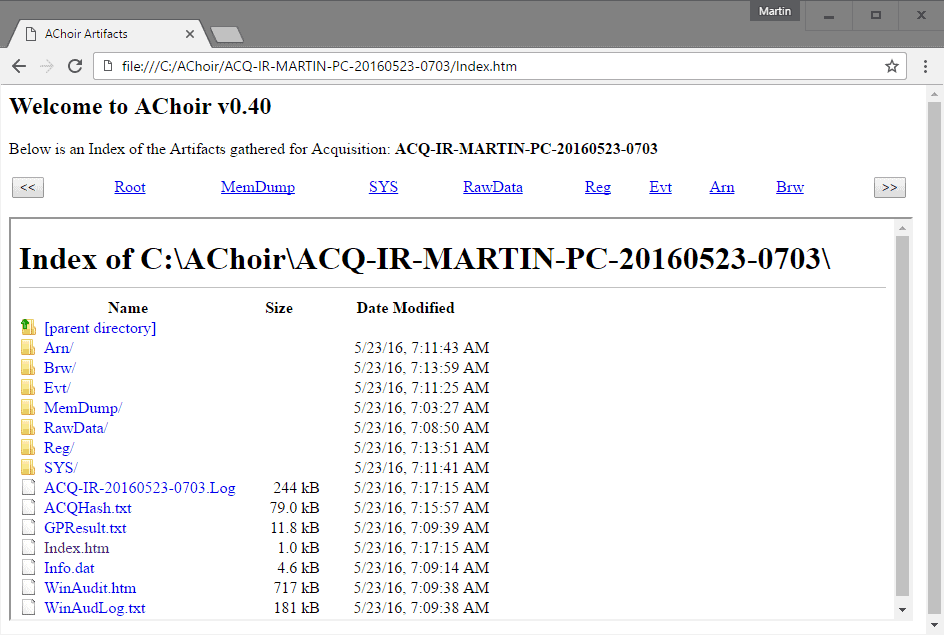
Data is dumped into folders there, but you may open the index.html file in a web browser to get started.
You will also find a log file in the folder, and a winaudit.htm file which you can run.
The subfolders contain valuable information which you may need to process further. The Reg folder lists exported Registry hubs for instance, the memdump folder an image of the memory at the time of running the program.
While several of the data dumps require further analysis and programs to display the data in a readable format, others can be accessed right away. The Brw folder for instance lists a csv and htm file that returns the browsing history when opened in a browser of choice.
If you want to know what the program does before you run it, open AChoir64.acq (or AChoir.acq for 32-bit) in a plain text editor of choice.
There you find all commands that it executes when you run it. Since the commands are all there, it is easy enough to add, remove or modify the script.
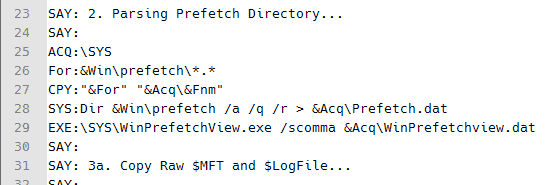
You find information about the scripting language in a text file that ships with the application. Basically, it is using a command in the beginning of a line that determine what is done. Say for instance echoes text on the screen while exe will run an executable file.
Closing Words
AChoir does not reinvent the wheel, but it is quite the powerful framework when it comes to running forensic tools (and others as it is not limited to those).
The main advantage that it offers over programs like OS Forensics is that you can customize it to suite your needs.

























“The dump and log that AChoir creates is usually quite large as the program will create a memory dump by default.”
This is a big understatement. My Achoir dir went to 17.1 GB (and counting). Beware those with SSD’s and/or smaller C: partitions.
Yet again an fail script like this one? -> https://www.ghacks.net/2016/05/14/last-audit-pc-software/.
No thanks I’m done with this. It’s okay that the source is open but from what I can see msinfo32 does more or less the same. So why I need this?
Well I think this one gives you more control over the process as it uses scripts that you can edit.
So, theoretically you can run any program you want that supports command line parameters using it.
https://www.ghacks.net/2016/05/14/last-audit-pc-software/