WinAuth Windows 2-factor Authentication app
WinAuth is a free open-source program for the Windows operating system that can be used to generate codes for various services offering 2-factor authentication.
2-factor authentication, sometimes also called 2-step verification, is an authentication scheme that adds a second verification step to authorization processes.
Companies started to add these options to improve account security. Basically, what it does when enabled is to require another code to be entered before access is granted.
This prevents many common attack forms such as phishing, brute forcing and even password dumping.
There are three core types of code generations for 2-factor authentication schemes: hardware-based, software-based, and remote-generation.
- Hardware-based: usually come in form of a simple gadget that you sync with an account. Once synced, you press a button to generate a code.
- Software-based: usually as an application that you install on a smartphone. Google Authenticator and Authy are two popular solutions, but there are more, and some companies have created their own authenticator application.
- Remote Generation: requires a mobile phone, with codes arriving via SMS.
WinAuth
WinAuth has been designed as a free program for Windows to give Windows users a tool at hand that they can use to generate codes for several popular services.
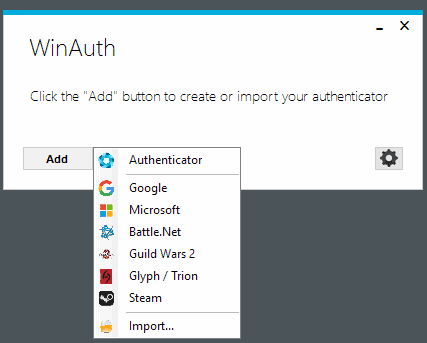
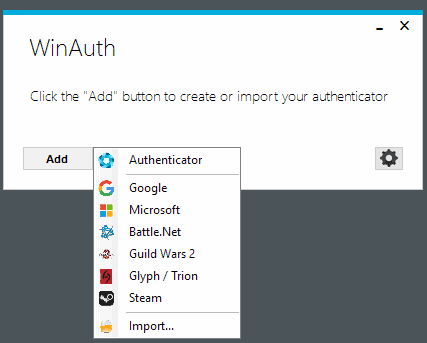
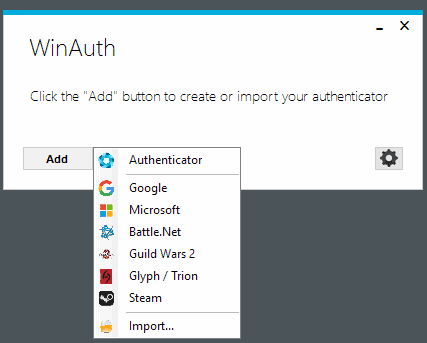
The program supports -- at the time of writing -- Google, Microsoft, and the gaming services or games Battle.net, Steam, Guild Wars 2, Glyph, SWTOR, RuneScape, and WildStar. WinAuth supports any service that uses Google Authenticator, Microsoft Authenticator, or RFC 6284 based authentication.
Note: WinAuth requires the Microsoft .Net Framework but not installation.
The program displays a basic dialog on first start which you use to add services to the program. Click on the add button and select one of the listed services or the generic "authenticator" option from the menu that opens up.
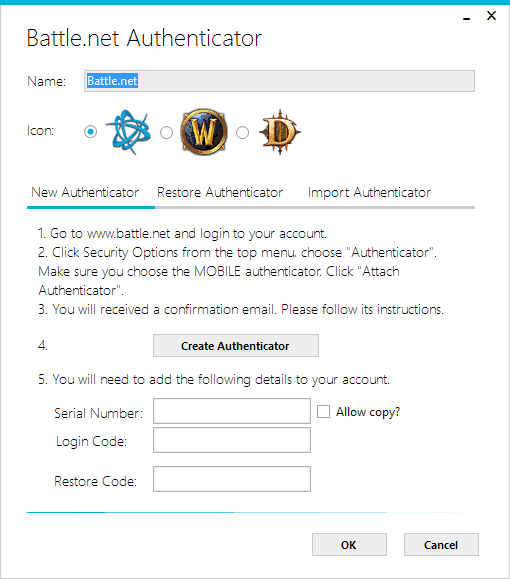
The process is usually the same regardless of service, but it is only explained in detail for the listed services and not the generic option.
What you need to do usually is open the service on the web to start the 2-factor authentication setup. How that is done depends on the service in question. Generally speaking, you will get an email or SMS first to verify the setup, and need to copy a secret key that is displayed on the site into the WinAuth application.
Since it does not support the scanning of QR codes, it is a required step to make the program the code generator for the selected account.
You can then hit the verification button in WinAuth to generate a verification code that you entert on the service's website to complete the sync process.
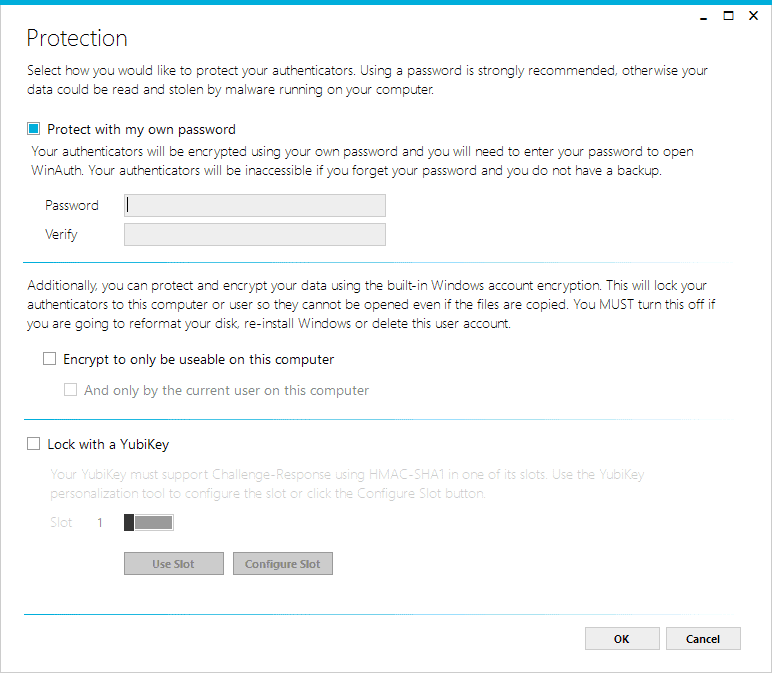
The program displays protection options once the syncing completes. You may protect the data using a custom password, or may use Windows account encryption to protect it so that it cannot be used on another computer, or even another user on the computer.
Last but not least, if you own a Yubikey device, you may use it for protection as well.
Once done, you will be asked to enter the code when you sign in to the service. Some services request a code all the time while others allow you to define a device as secure so that codes are requested only occasionally when you are using them.
When a code is requested open WinAuth to get the code that you need to complete the authentication process. Each generator can be set up to generate codes automatically when the program is open, or only on request.
As far as security is concerned, the developers have this to say:
All private authenticator data is encrypted with your own personal password, salted and enhanced with key strengthening to reduce the ability for brute force attacks. The data can also be protected using Windows in-built Data Protection API, which will “lock†the data to a single computer or account, making it completely unusable if copied to another computer.
WinAuth saves the data to c:\Users\<username>\AppData\Roaming\WinAuth\winauth.x by default
Closing Words
WinAuth is a handy program for Windows users who want to use 2-factor authentication without using a mobile device to do so. Doing so may limit mobility, but that may not be a requirement.


























from my experience, Winauth works indeed like a charm regarding steam’s new market policy.
I need such a program, but for Windows Phone, for use with Steam, as the authenticator of them does not exist for WP.
For Steam, check Unofficial Steam Authenticator: https://www.microsoft.com/fi-fi/store/apps/unofficial-steam-authenticator/9nblggh58psp
Source: https://github.com/Top-Cat/UnofficialSteamAuthenticator
Thank you
Finally a decent Windows 2-factor authentication app that my phone had. Thanks.