Is Torrent-live's dynamic blocklist worth the €30 it costs?
Blocking dangerous, privacy-invasive or unwanted IP addresses is not an entirely new concept.
Programs like PeerBlock or PeerGuardian (which PeerBlock is based on), are standalone applications that block certain IP addresses from connecting to your computer to increase your privacy when your devices are connected to peer to peer networks.
The main idea behind these applications is to block IP addresses and ranges that can be associated with certain organizations, trackers or malware so that they cannot do harm or monitor activity.
Torrent-live's dynamic blocklist is the result of the "Monitoring and blocking the bittorrent monitoring spies" study which focused on tracking and blocking monitoring stations using BitTorrent's peer and DHT system only.
The main issue with BitTorrent from a privacy perspective is that anybody can monitor peers in the network.
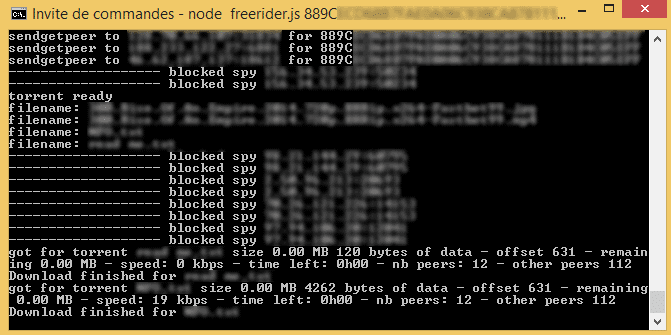
The researchers have created a tool to detect, follow and block spies, and one of the results of the operation is the dynamic blocklist that is updated by the project every 15 milliseconds.
The study discovered two types of spies with only one of them being dangerous from a privacy perspective.
The blocklist is being sold on the Peersm website for €30 which gives you one year of access to it. It is provided as a p2p file which you can either integrate directly in BitTorrent clients supporting the format or in programs like PeerBlock which run on a system-wide level.
In qBitTorrent for instance, you'd click on Tools > Options > Connection, enable IP filtering and select the p2p blocklist file on your system to integrate it in the client.
The dynamic blocklist lists more than 17800 IP addresses currently that spy on users.
The revenue is used for maintaining the service and for Torrent-live, an open source Torrent client utilizing the findings in the study.
Is it worth it?
The main question is whether integrating the blocklist is worth the money it costs. The answer depends on several factors including your current setup, your activity and whether you trust the findings of the study.
For instance, if you are using a VPN service you may not require the blocklist on top of that if the service keeps no logs of your activity.
Access to the full study is not provided on the project website which makes it impossible to find out whether the methodology used is as effective as claimed by the project.
The best course of action right now seems to be to use it as a complementing strategy instead of relying on it solely to keep you safe online.
Now You: How do you protect your privacy while online/using P2P?



















My country doesn’t care about P2P or any kind of online piracy, so for now I download without a care in the world…
I download my Linux isos only from P2P because it’s faster, with vpn it’s way too slow.
What country doesn’t care about P2P or online piracy?
Also, don’t most VPNs (Betternet, ipinator, tigervpn, tunnelbear, etc) have strict terms and conditions regarding P2P / Torrent usage?
China doesn’t care about P2P or online piracy. Plenty of VPN services have P2P friendly servers. BlackVPN for example, is situated in Hong Kong and has P2P friendly servers located in Canada, Netherlands, Switzerland, Luxembourg, Estonia, Lithuania, Romania, Russia, Ukraine.
> Is it worth it?
tl;dr: no, it’s just stupid.
https://torrentfreak.com/thousands-of-spies-are-watching-trackerless-torrents-151004/
Blocklists just don’t work. These are sophisticated companies its naive to think you’ll be blocking them with some list, regardless of how often its ‘updated’
Using blocklists (for torrent tracking purposes) is f***kin useless. “Bandaids don’t fix bullet holes” – Taylor Swift. Listen to Swiftie there – if you wish to remain anonymous, then you need an anonymizing service such as a VPN, as a bare minimum (note: you could still be ID’ed (unlikely) but there are other steps you could take (anonymized account-email-bitcoin and vpn-chaining/mobile-data-sticks/open-wifi/war-driving etc – anything that ultimately doesn’t link to an IP associated with your name/address – but this would only be to thwart a VPN provider logging you due to law enforcement/warrant etc).
Don’t get me wrong, blocklists can be used for other things. But this torrent tracking protection bulls**t is up there with defragging your registry – all it takes is for you to miss one (and they have an awful lot of dynamic addresses they can use) and they have the IP. Don’t delude yourselves.
Me thinks the reason Aymes charges €30 is because of that crowdfunded project no one cared about ;)
I’ve created a solution called the “torrent ninja guide” that uses free blocklists from iblocklist and self-updates them every 24 hours to the latest version. Google for it, it is a short article with a few links.
I find it odd when people develop business models around a demographic that inherently doesn’t pay for stuff.
Don’t be surprised at all. From pre-flashed XBOX360 game consoles, which cost 5 times as much as a regular machine, to DirecTV CUCARDs, to Nintendo 3DS R4 carts, to XBMC/Kodi spins centered around TV piracy the market has shown time and time again that people will pay substantial amounts of money for piracy related products they believe will save them money in the long run.
Of course, in all of these cases, the amount of time, skill, and technical expertise to acquire, maintain, and support pirated equipment is usually more costly than purchasing the legal version of the product from the start.
I find it funny when people won’t pay $6 for a game but will drop $20 for in-game items that make the free games easier….
Quite true. Once again it’s less the bill than the opportunity cost which seems to lead the openness of a wallet. We often agree to pay (money) for a product/service which enforces our ego, our domination, be it for cheating (still don’t know how one can be proud of having cheated unless his sens of dignity is all between his legs).
https://gist.github.com/Ayms/077b114a27450f773939
https://gist.github.com/Ayms/f2da9f860775ead2066e