Twitter starts to roll out two-factor login verification
Two-factor authentication is one of the best ways to increase the security of online accounts.
Companies and services like Google, PayPal or Valve are already making use of the feature to provide their users with an additional layer of security. A second code needs to be entered after the usual username and password combination has been accepted to complete the authentication process.
Twitter has been working on adding login verification to its service for some time now. On May 22, 2013, the company started to roll out the feature to all of its users.
Twitter uses a SMS-based system that sends codes to verified phone numbers during the login process. This is different from many other services that use authenticator apps, hardware devices or email to generate codes.
Take a look at the following video to see how the new login verification is activated on Twitter.
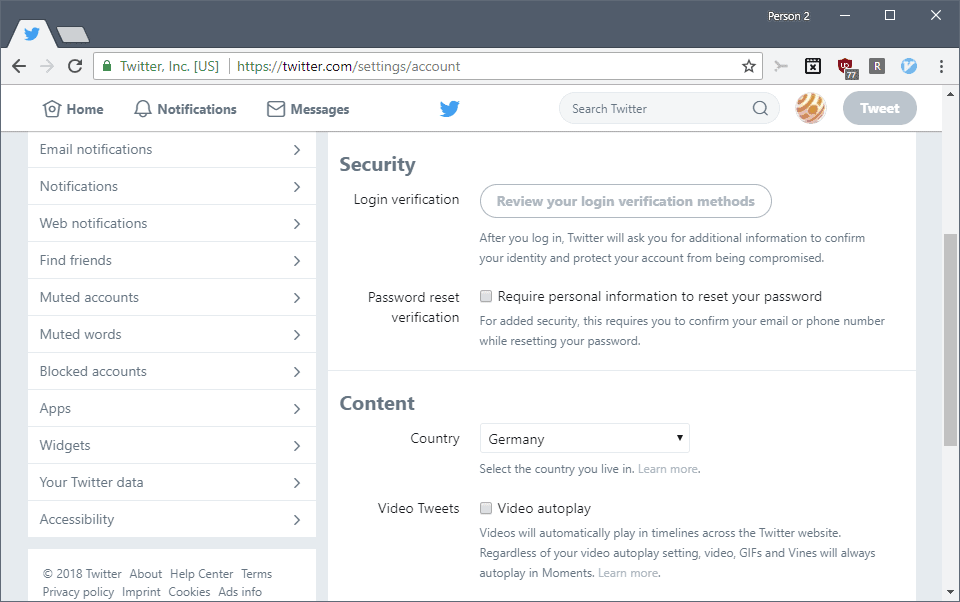
Here is how to set it up for your account:
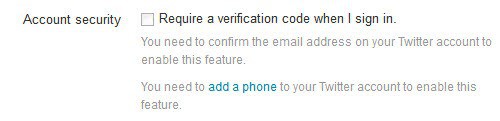
- You need to verify a phone number before you can start to enable two-factor authentication for your account.
- Go to the Mobile page of the Twitter Settings and verify that a phone number is listed on the page. If it is not, add a phone to the account.
- Twitter displays whether you need to verify phone number, or if that has been done previously already.
- Select "set up login verification" and read the instructions. Click on Start once you are done.
- Type your password and select verify.
- Click on the "send code" button to have Twitter send a code to your verified mobile device.
- Type the verification code that is included in the message sent to the phone on Twitter to verify ownership.
- Click "get backup code" to save a code. The code is for emergencies, for instance, when you don't have access to your device anymore.
- Next time you log in to Twitter you enter your username and password like usual, and the verification code that Twitter sent to your phone on the second page. You can only sign in successfully if both checks are correct.
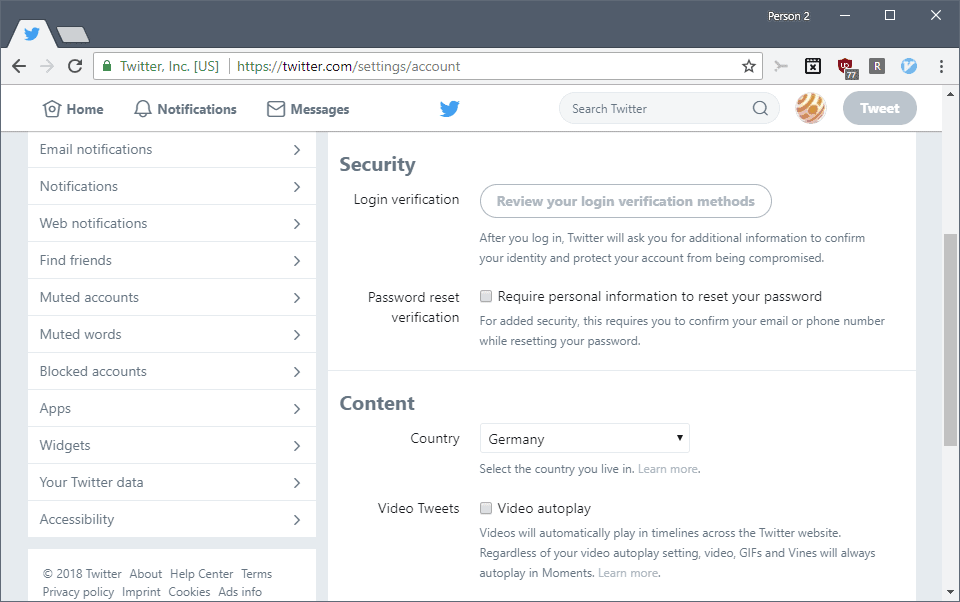
You can authorize third party applications on the applications page that do not support the two-factor authentication scheme yet.
Check out Twitter's instructions on setting up two-factor authentication on the site for additional information.
Closing Words
Two-factor authentication is an important step in improving the overall security of Twitter accounts. What feels a bit strange is that you cannot use Twitter's apps to verify your phone.





















I’m pretty sure I said it on here about Google’s two factor verification and I’ll say the same to twitter as others above have done, there is no way in hell am I giving any software based company my phone number.
Dot Com says i own security patent
http://torrentfreak.com/kim-dotcom-to-google-twitter-facebook-i-own-security-patent-work-with-me-130523/?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+Torrentfreak+%28Torrentfreak%29&utm_content=Google+Reader
Yeah, I trust no one in the Internet with my phone number.
Make something like Grid from lastpass or google authenticator, there are so many options…
Sorry Twitter but not giving you my mobile number – use an app like others are starting to do. You don’t even have to write one as Google have one already, even Dropbox/App.Net use it.