Microsoft Sees Huge Increase In Java Exploit Attempts, Surpassing Adobe
Regular readers of Ghacks know that browser plugins have become one of the biggest security risks for today's Internet users.
Keeping the plugins up to date is therefor essential to protect systems from exploits targeting known vulnerabilities.
Among the plugins that are exploited the most are Adobe plugins and Java.
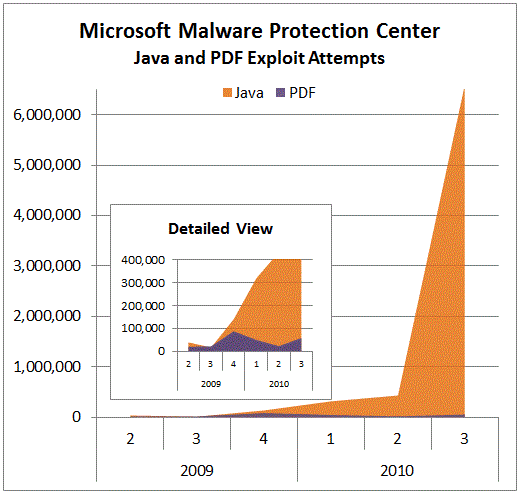
Recent findings in Microsoft's latest Security Intelligence Report suggest that Java exploits have increased steadily and caused a huge spike in the second quarter of 2010, rising from under 500,000 to more than 6 million in quarter 3.
In comparison, pdf exploits stayed well below the 100,000 mark in that time.
Holly Stewart analyzed the causes of the spike and came to the conclusion that the attacks were driven by three vulnerabilities.
Interestingly enough, patches are available for some time for those vulnerabilities. This suggests that many users do not update Java on their computer system regularly, or at all.
Those exploit attempts pale in comparison to other threats on the Internet. Malware trends of the report show exploits making up less than 5% of all infected computers. Still, exploits have risen from less than 2% in the third quarter of 2009 to almost 5% in the second quarter of 2010.
Why is Java that dominant in the exploits category? The main cause seems to be because people do not update Java as frequently as other browser plugins. Up until recently, researchers and reporters did not mention Java nearly as often as Adobe Flash or Adobe Reader when it came to third party plugins being exploited. This may be the core reason, but there are others.
Java, which usually means the Java Runtime Environment, is installed on the majority of computer systems. Coupled with the fact that Java is barely used by most Internet users, and that update notifications are non-existent make it a prime target for attackers.
Some browser developers have started to add plugin checks either during updates of the browser or in the plugin listing.
So what can you do to protect your system? First, if you do not need Java you can simply disable it in the web browser. This protects the browser from possible exploits. You may also want to consider uninstalling Java completely, considering that there is no good reason to keep it on the system if it is not needed.
Users who need to work with Java need to monitor JRE updates. They can do this manually, by reading news sites that report on security updates, or by installing a third party software like Secunia PSI that will inform them of updates.
Advertisement



















Both Java and Adobe suck big time maybe they should follow Symantec’s approach of remaking the whole application just like they did in Norton AV,Norton IS 2011.
Regards
Java just plain sucks in security. I only install it on machines that requires it – usually students. Colleges are retarded when it comes to computer security. They use cheap student labor to run their computer labs and won’t hire real professionals. So most school websites requires Java and Flash to work. And even then, it never works well with their amateur implementation.
As a security precaution, I have been giving schools my Social Security number with one digit off. College security is as tight as Apple’s.