Introduction to iptables
If you've been around Linux long enough you know there are many ways to secure your box. What you may or may not know is that a number of those means are simply front-ends for the all-mighty iptables tool. IPtables is a very powerful, complicated system which can control packet traffic on your system. It can deny, reject, allow, route, and do just about anything else you want to do with that traffic...all from the command line. Of course, along with this power, comes some serious complexity.
That complexity is what an introductory article is needed. I have seen plenty of users try to just jump into the heart and soul of iptables, only to see them fail miserably. To fully understand iptables one must first understand how iptables is actually used. In this article I will help you to understand the fundamentals of iptables so later on we can further that knowledge with more in-depth scripts and commands.
What IS iptables?
As I mentioned earlier, iptables is a powerful way to control packet traffic to and from your Linux box. But how does it manage this? Â It does so by creating TABLES made up of CHAINS. There are three types of chains:
- INPUT: Controls packets coming in.
- OUTPUT: Controls packets going out.
- FORWARD: Controls packets that are forwarded.
These are also applied to the default policies. When you install a Linux operating system it will have three pre-defined iptables chains (one for each of the above).
Now each chain can handle the packet traffic in one of four different ways (actions):
- ACCEPT: Allow the packet in/out.
- REJECT: The target device will reject the packet.
- DROP: The packet is immediately dropped and the target device never sees said packet.
- RETURN: Go to another chain in your table as if it never saw the rejecting chain.
So now you have a TABLE made up of CHAINS that use ACTIONS to route traffic. Is this getting any easier? Now, you can also have more than one TABLE on a machine - but that is far too complex for an introductory article. Your machine will also have a default POLICY for each chain (INPUT, OUTPUT, FORWARD). By default these POLICIES are typically set to the action ACCEPT.
You must also understand that when a packet arrives on a machine it must traverse the iptables CHAIN until it either matches a CHAIN rule or it passes through all rules unscathed. Because of this you want to create your chains carefully. If you do not you can wind up with traffic you want to ACCEPT getting REJECTed because of a poorly ordered chain. For example:
Let's say you want to ACCEPT all ssh traffic within your internal network safe passage to your machines. But what if you have a CHAIN rule that REJECTS ssh traffic in place before that internal rule? If you do this all internal ssh traffic will be REJECTed as well. In this case you would want your TABLE chain order like so:
CHAIN ACCEPTing incoming LAN ssh traffic
CHAIN REJECTing incoming WAN ssh traffic
Let's take a look at how you use itables as a command to create or change POLICY chains.
Usage
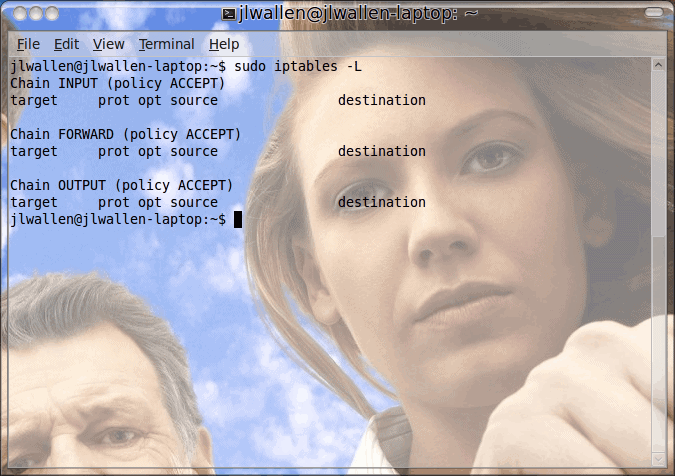
If you issue the command iptables -L all of your current chains will be listed like what you see in Figure 1. NOTE: The iptables command MUST be run as either the root user or with the help of sudo.
As you can see, in my output, my TABLE consists of the three default policy CHAINS and each is currently set to the action ACCEPT. Â What if I want to change my INPUT policy to DROP? After all, do you want incoming traffic to have total access to your machine? You can set the input POLICY to DROP with the following command:
sudo iptables -P INPUT DROP
What you have effectively done above is set your default INPUT POLICY to REJECT. So without creating any new CHAINS all incoming traffic to that machine will be REJECTED. Here's the problem with that...say, for instance, you want to allow ssh traffic into that machine? If you leave it as is this will not happen. Because you have the INPUT POLICY set to REJECT and you have no other CHAINS in place, no incoming traffic will work. Remember, though, what I said about creating CHAINS in the right order to ensure needed traffic can find safe passage.
Final thoughts
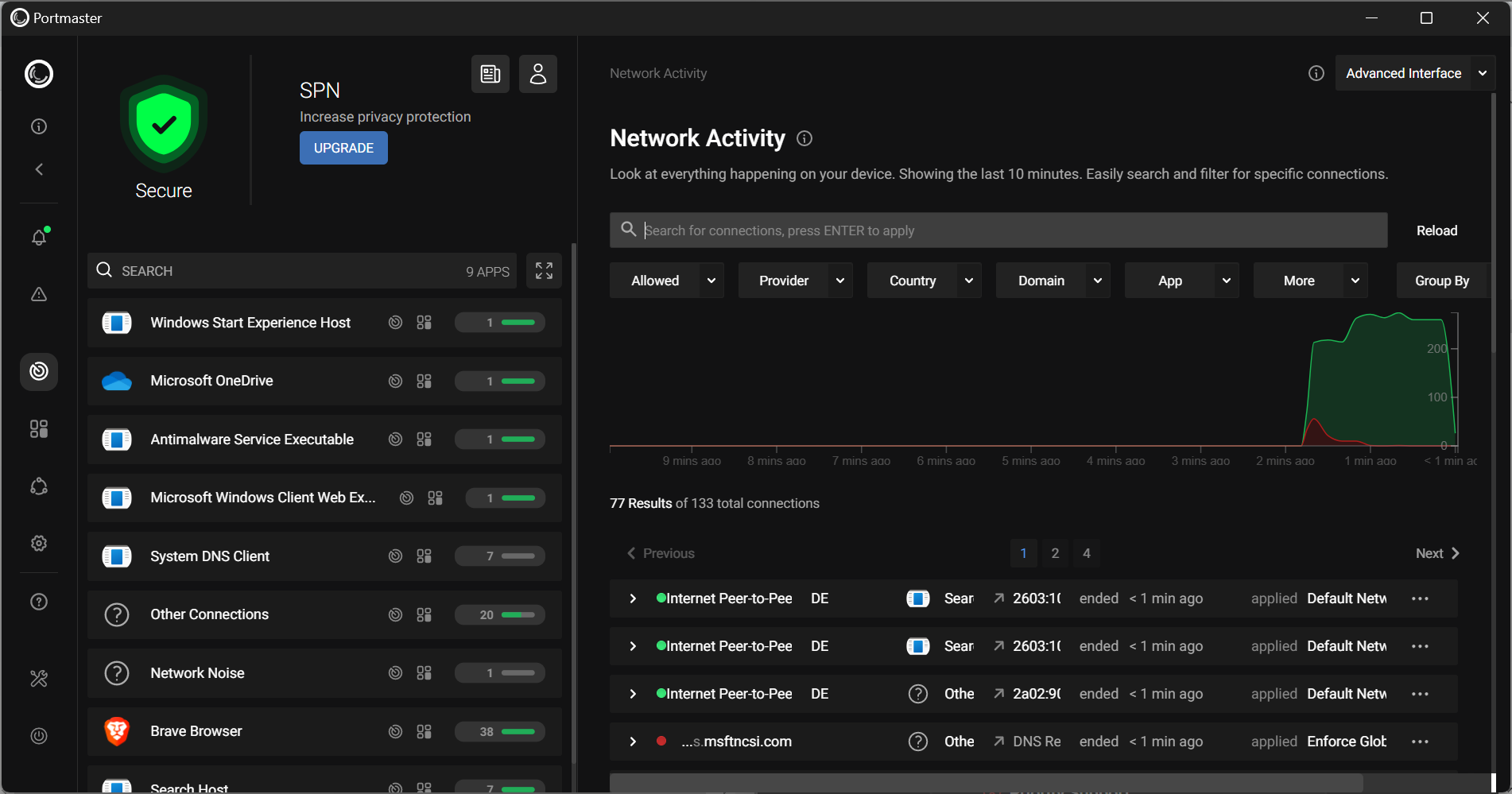
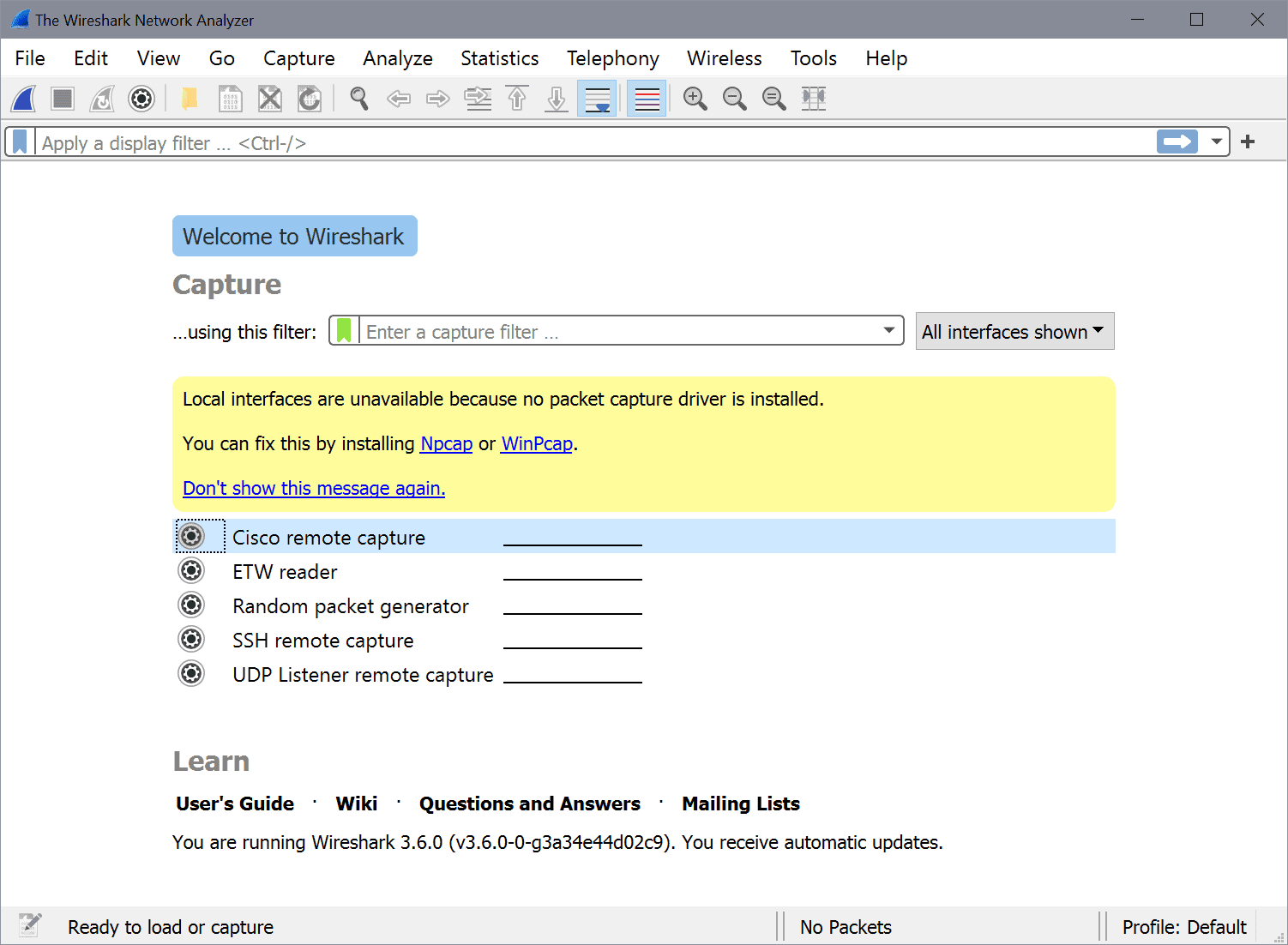
Thus begins our journey with iptables. It's not the most simple system to employ, but it certainly is powerful. Â Is it worth the time and effort when there are so many GUI tools to choose from? That depends upon your needs. If you are working on nothing more than a desktop - then the GUI front-end will more than likely be enough. If, however, you have a server with mission-critical or sensitive data you might need the extra power and flexibility that iptables brings to the table.
Advertisement














Great read! Thank you! Simple en clear…. :D
Thanks Jack for your Great Articles in Linux I really enjoy reading them.
Thanks you All at GHACKS.NET for a one stop place of quality information :)