Microsoft Security Updates April 2010
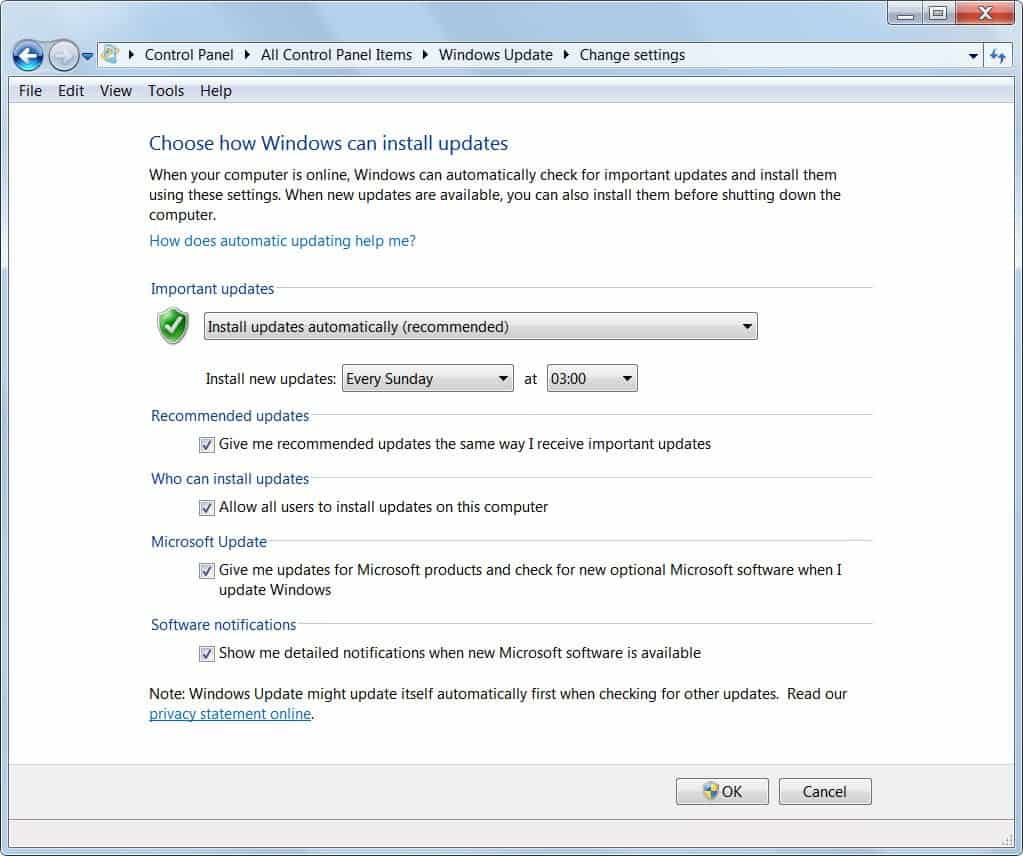
Microsoft has just added the security updates for April 2010 to Windows Update so that all Windows user can download and install them on their operating system automatically.
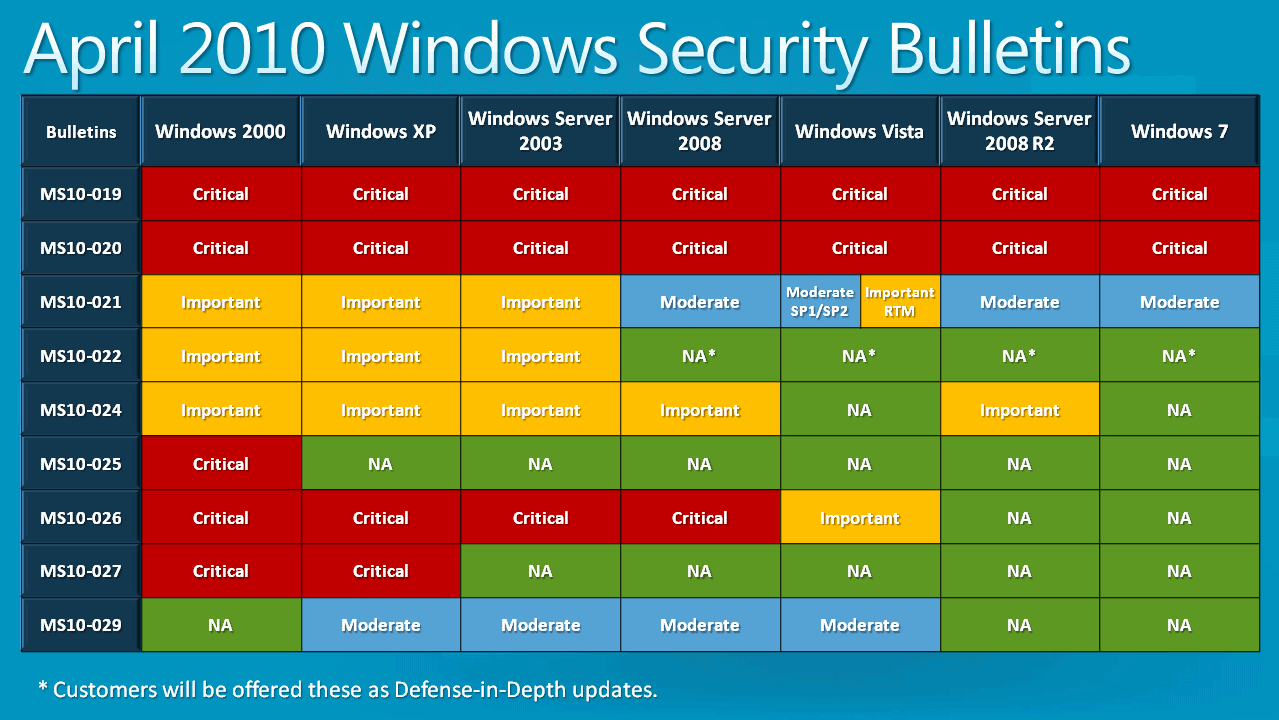
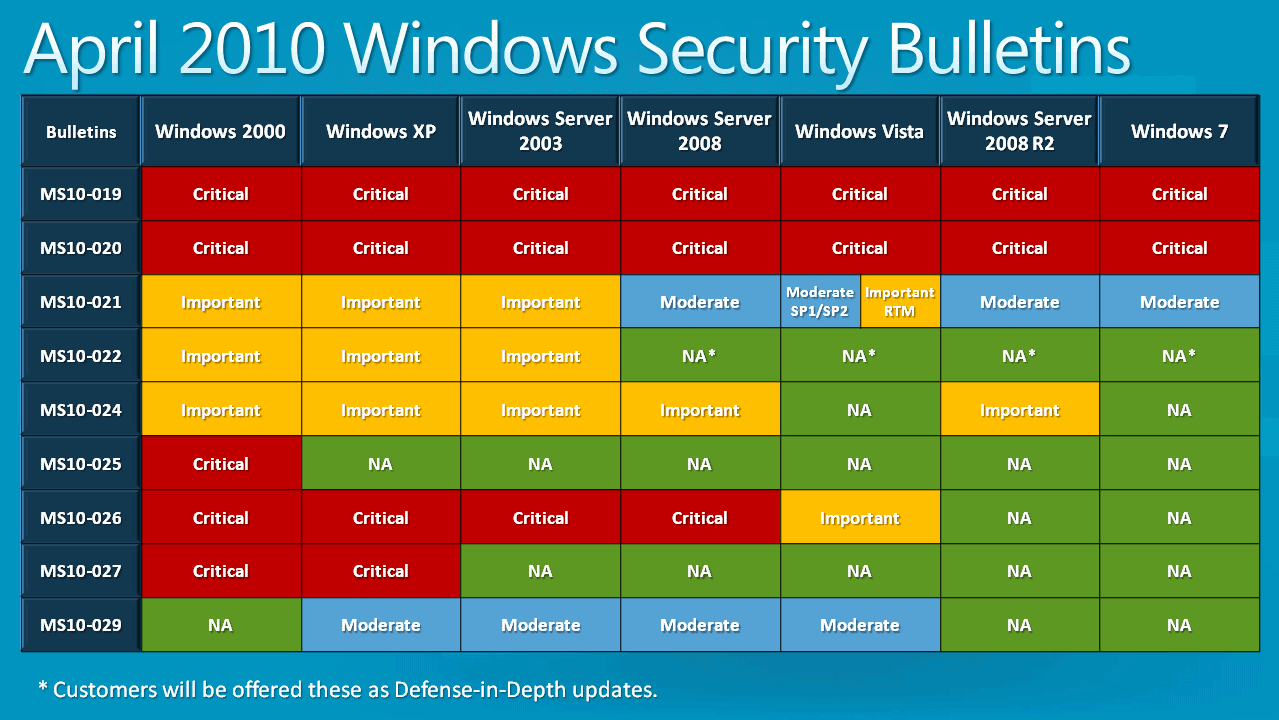
A total of eleven security bulletins have been released that update various versions of Windows as well as other Microsoft software like Microsoft Office.
The updates fix security vulnerabilities in Microsoft applications and it is generally recommended to update the operating systems and applications as soon as possible to close the security holes and protect the systems from malicious attacks exploiting these vulnerabilities.
Five of the vulnerabilities have received a critical rating, the highest and most severe rating that vulnerabilities can get. This means that at least one application or service is affected by it that way while others may be affected in the same way, to a lesser degree or not at all.
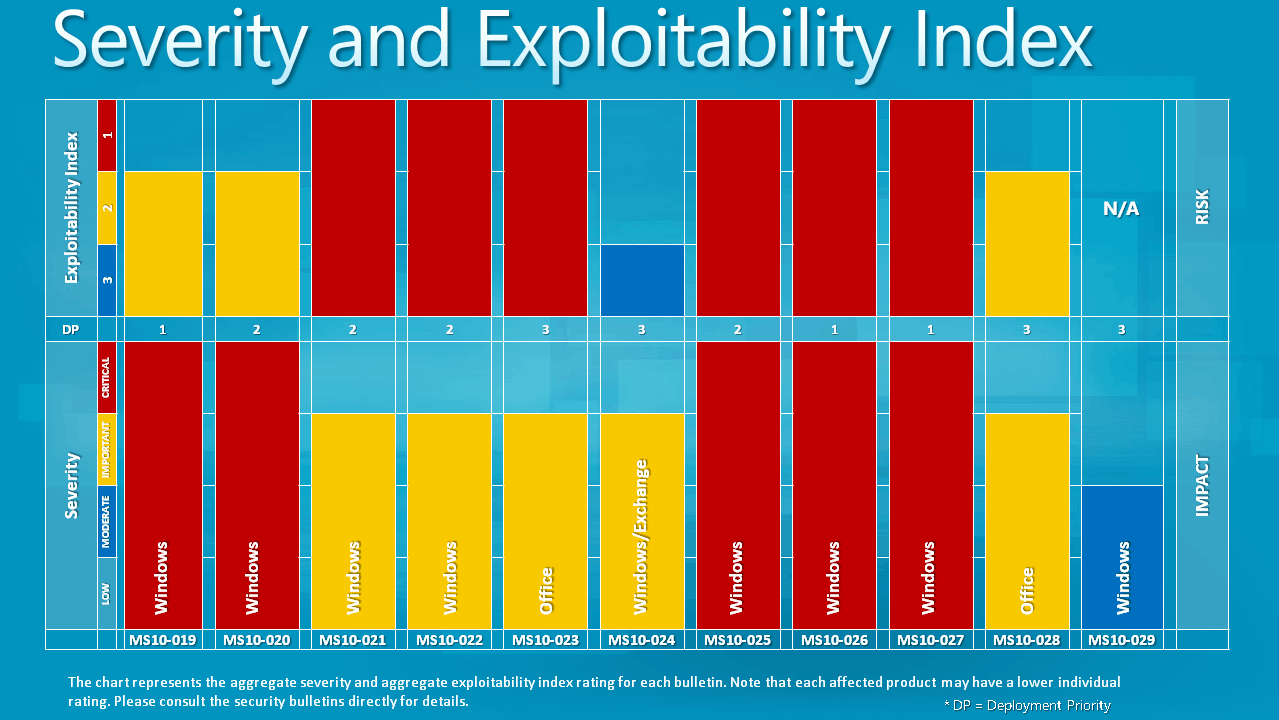
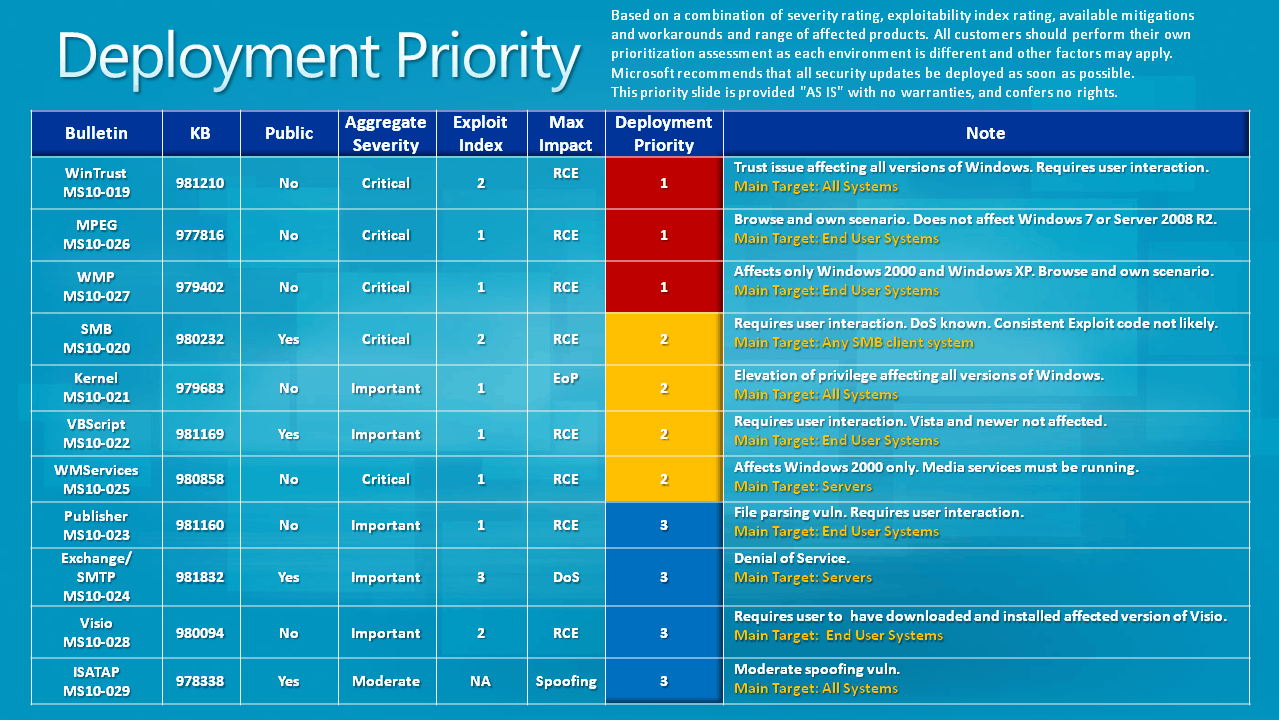
- MS10-019 - Vulnerabilities in Windows Could Allow Remote Code Execution (981210) - This security update resolves two privately reported vulnerabilities in Windows Authenticode Verification that could allow remote code execution. An attacker who successfully exploited either vulnerability could take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
- MS10-020 - Vulnerabilities in SMB Client Could Allow Remote Code Execution (980232) - This security update resolves one publicly disclosed and several privately reported vulnerabilities in Microsoft Windows. The vulnerabilities could allow remote code execution if an attacker sent a specially crafted SMB response to a client-initiated SMB request. To exploit these vulnerabilities, an attacker must convince the user to initiate an SMB connection to a specially crafted SMB server.
- MS10-025 - Vulnerability in Microsoft Windows Media Services Could Allow Remote Code Execution (980858) - This security update resolves a privately reported vulnerability in Windows Media Services running on Microsoft Windows 2000 Server. The vulnerability could allow remote code execution if an attacker sent a specially crafted transport information packet to a Microsoft Windows 2000 Server system running Windows Media Services. Firewall best practices and standard default firewall configurations can help protect networks from attacks that originate from outside the enterprise perimeter. Best practices recommend that systems that are connected to the Internet have a minimal number of ports exposed. On Microsoft Windows 2000 Server, Windows Media Services is an optional component and is not installed by default.
- MS10-026 - Vulnerability in Microsoft MPEG Layer-3 Codecs Could Allow Remote Code Execution (977816) -
This security update resolves a privately reported vulnerability in Microsoft MPEG Layer-3 audio codecs. The vulnerability could allow remote code execution if a user opened a specially crafted AVI file containing an MPEG Layer-3 audio stream. If a user is logged on with administrative user rights, an attacker who successfully exploited this vulnerability could take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. - MS10-027 - Vulnerability in Windows Media Player Could Allow Remote Code Execution (979402) - This security update resolves a privately reported vulnerability in Windows Media Player. The vulnerability could allow remote code execution if Windows Media Player opened specially crafted media content hosted on a malicious Web site. An attacker who successfully exploited this vulnerability could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS10-021 - Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (979683) - This security update resolves several privately reported vulnerabilities in Microsoft Windows. The most severe of these vulnerabilities could allow elevation of privilege if an attacker logged on locally and ran a specially crafted application. An attacker must have valid logon credentials and be able to log on locally to exploit these vulnerabilities. The vulnerabilities could not be exploited remotely or by anonymous users.
- MS10-022 - Vulnerability in VBScript Could Allow Remote Code Execution (981169) - This security update resolves a publicly disclosed vulnerability in VBScript on Microsoft Windows that could allow remote code execution. This security update is rated Important for Microsoft Windows 2000, Windows XP, and Windows Server 2003. On Windows Server 2008, Windows Vista, Windows 7, and Windows Server 2008 R2, the vulnerable code is not exploitable, however, as the code is present, this update is provided as a defense-in-depth measure and has no severity rating.The vulnerability could allow remote code execution if a malicious Web site displayed a specially crafted dialog box on a Web page and a user pressed the F1 key, causing the Windows Help System to be started with a Windows Help File provided by the attacker. If a user is logged on with administrative user rights, an attacker who successfully exploited this vulnerability could take complete control of an affected system.
- MS10-023 - Vulnerability in Microsoft Office Publisher Could Allow Remote Code Execution (981160) - This security update resolves a privately reported vulnerability in Microsoft Office Publisher that could allow remote code execution if a user opens a specially crafted Publisher file. An attacker who successfully exploited this vulnerability could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS10-024 - Vulnerabilities in Microsoft Exchange and Windows SMTP Service Could Allow Denial of Service (981832) - This security update resolves one publicly disclosed vulnerability and one privately reported vulnerability in Microsoft Exchange and Windows SMTP Service. The more severe of these vulnerabilities could allow denial of service if an attacker sent a specially crafted DNS response to a computer running the SMTP service. By default, the SMTP component is not installed on Windows Server 2003, Windows Server 2003 x64 Edition, or Windows XP Professional x64 Edition.
- MS10-028 - Vulnerabilities in Microsoft Visio Could Allow Remote Code Execution (980094) - This security update resolves two privately reported vulnerabilities in Microsoft Office Visio. The vulnerabilities could allow remote code execution if a user opens a specially crafted Visio file. An attacker who successfully exploited these vulnerabilities could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS10-029 - Vulnerabilities in Windows ISATAP Component Could Allow Spoofing (978338) - This security update resolves one privately reported vulnerability in Microsoft Windows. This security update is rated Moderate for Windows XP, Windows Server 2003, Windows Vista, and Windows Server 2008. Windows 7 and Windows Server 2008 R2 are not vulnerable because these operating systems include the feature deployed by this security update.This vulnerability could allow an attacker to spoof an IPv4 address so that it may bypass filtering devices that rely on the source IPv4 address. The security update addresses the vulnerability by changing the manner in which the Windows TCP/IP stack checks the source IPv6 address in a tunneled ISATAP packet.
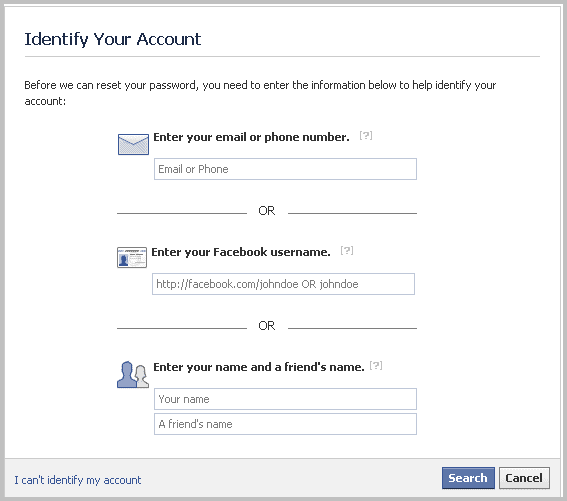
The security updates can be downloaded by following the links listed above or by launching Windows Update or Microsoft Update to download and install them automatically on the computer system.


















Leave the machine at the white desktop for as long as it needs (20 mins on one machine here) and it will finally break through to the proper desktop.
Thanks a million
Same deal, no sandboxie
madmurr:
Same deal on Win 7, it’s definitely KB979683 though (spent the day applying patch by patch and restoring for a known good image)
Are you guys running Sandboxie by chance?
No I am not running sandboxie
I just downloaded the 11 it told me to get for my XP Pro machine and now it won’t boot – be careful – I haven’t managed to figure out why but even all the safe modes and last known good configuration options don’t work …
Thanks a mil. Martin quit a list this time. Ferry handy that i can click on the pictures. Please keep up the good work.