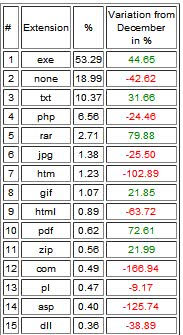
Avira Malware File-Extension Statistics
Malware is a generic term for trojans, viruses, worms, keyloggers, rootkits and other malicious program code.
Avira posted on the official company blog interesting statistics about malware that gets distributed using url, for instance as email messages, on websites, or in chat rooms. The company analyzed data gathered by its security products for the statistic.
Most computer users probably associate file types like exe with being dangerous when they encounter them on websites or in emails. Many may be surprised when they hear that those files only make up 53% of file extensions of malicious files.
The file extension that is used the second most has none at all which may come as a surprise (this includes links to root folders or directories), followed by txt files with 10.37%, and php files with 6.56%.
This requires some explanation. Most users would probably agree that text files are harmless. This is not always the case however especially when it comes to links, as links can be redirected easily.
A link may point to a text file directly, but if the web server is configured to redirect users opening that link to another location, then this is one option how text files can be problematic.
But attackers can also rename an executable to txt and use malicious code on a website to run the file.
The statistics point out that while standard executable files make up more than 50% of all attacks, it is of equal importance to understand that harmless looking files and links can be malicious as well.
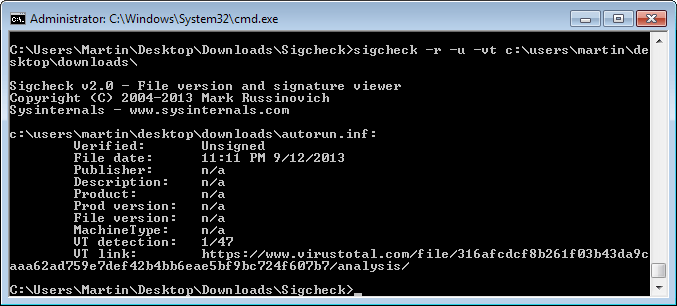
As you can see on the screenshot above, only .exe is a "real" executable file in the top 5 while the remaining file types are not. They can still be dangerous though even though many are quite rare if you look at their percentage value.
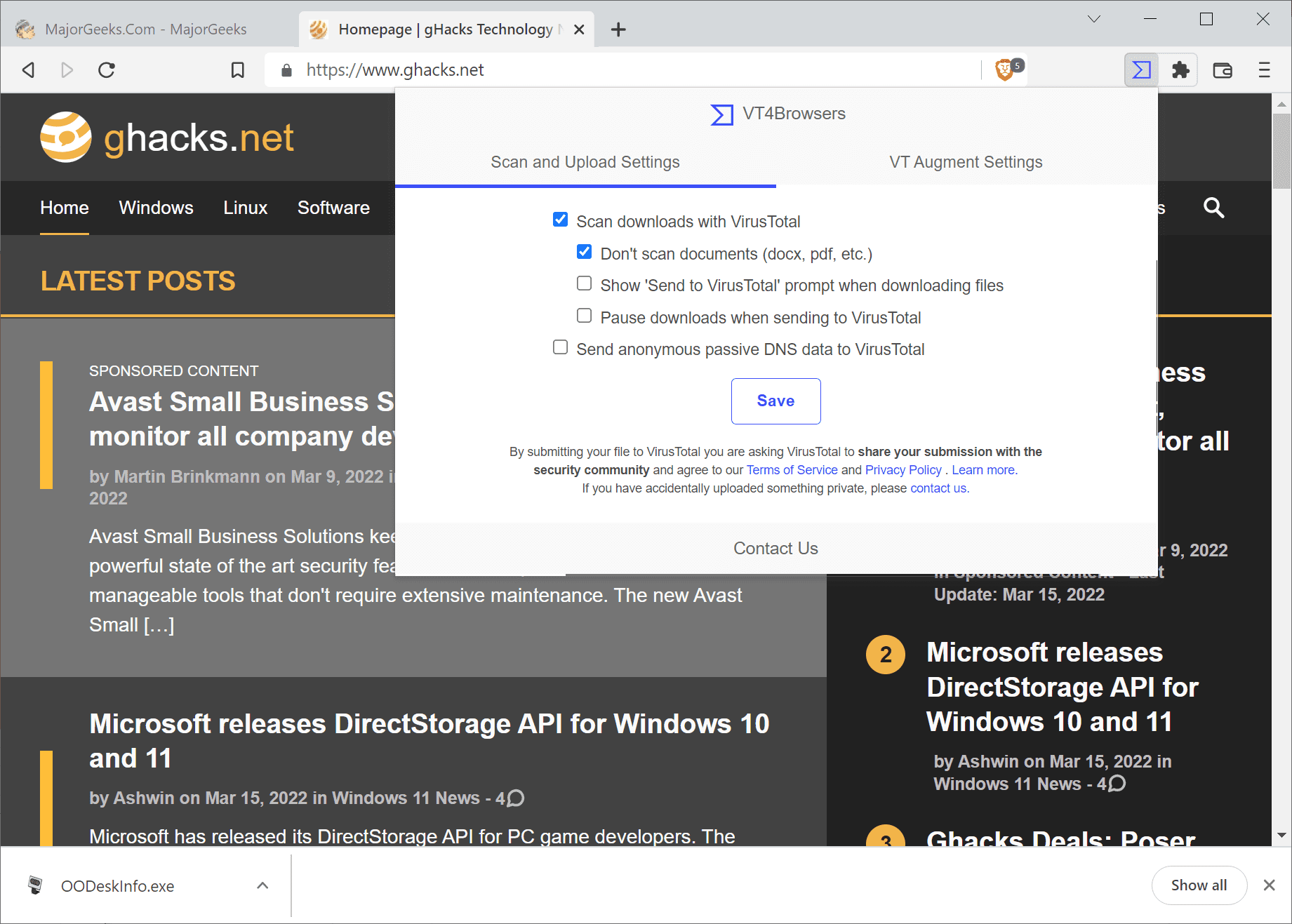
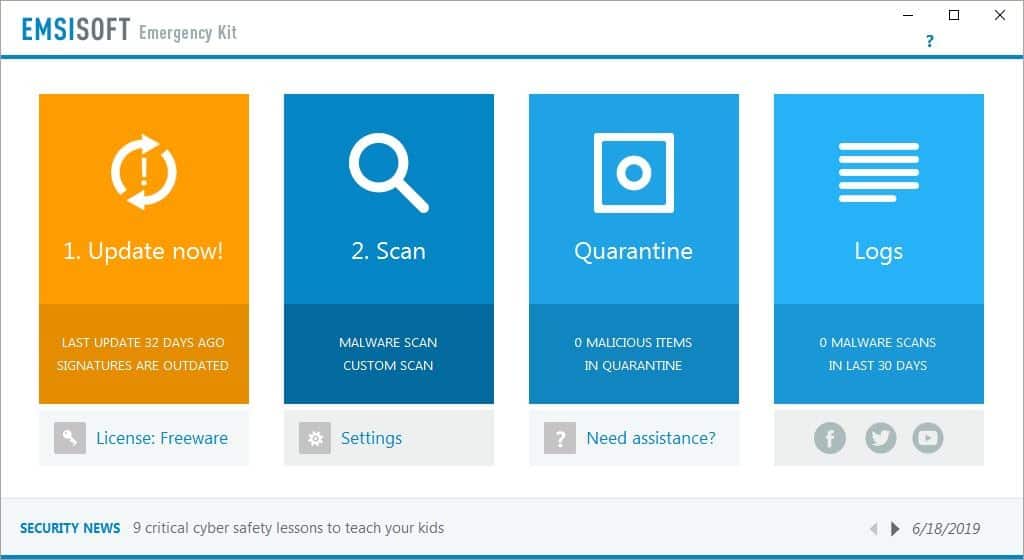
The safest bet is to avoid clicking on links or attachments in emails. A sandboxed environment or a virtual PC are two secure alternatives if the link needs to be clicked on, and it may also be analyzed first by a service like Virustotal to find out more about it before opening it.
Update: The blog post appears to be no longer available on the Avira blog.














It’s really difficult for us end-user to determine the real best antivirus without the necessary tools like the expert website has such as AV-Comparative, VB100. Fortunately we have the most powerful tool which they don’t have that is experience of using it on our computers.
Now each computers has differences of whatever software we install in them, and because of that it creates uniqueness and complexity for each of the antivirus. Some antivirus will fail in your system because of that complexities whereas others doing well. So based on that experience a belief grows to the point where you will think that particular antivirus software is best for your computer. And you will insist that you are using the best out there.
Despite of all that based on collective comments from user experience: I read Kaspersky or NOD32 is the top of them all with the least problems, high praise from users, and virus detection rates is superb