Troubleshoot networking problems with GNOME's Nettools
How many times have you had networking issues and not known exactly where to start? With Linux there are so many tools you can choose from. Add to that the choice between console and GUI and you have the making for a rather confusing start.
Most new Linux users (and many of those who have used Linux for a while) have no idea how to use the whois, finger, Port Scanning, and other helpful networking tools. But it doesn't have to be that way.
With the help of the GNOME Nettools you can have a sweet collection of powerful tools that will help you to troubleshoot your network in no time. And this collection of tools is all wrapped up into a user-friendly graphical interface. So without any further adieu, let's take a look at this powerful suite of tools.
Features
The GNOME Nettools includes the following tools:
- Devices: Have all information about your networking devices at your fingertips.
- Ping: Get detailed information using the ping tool.
- Netstat: Get detailed information about your routing table, active network services, and multicast information about your machine.
- Traceroute: Trace the path to a network host.
- Port scan: Scan for open ports on servers and desktops.
- Lookup: Get detailed information about a server.
- Finger: Lookup a users finger entry.
- Whois: Lookup a whois entry for a domain.
GNOME Nettools also features:
- Copy information to text report.
- Help system.
- Drop downs for previously entered addresses/domains.
- Easy to use GUI.
Now let's take a look and see how this tool is used.
Usage
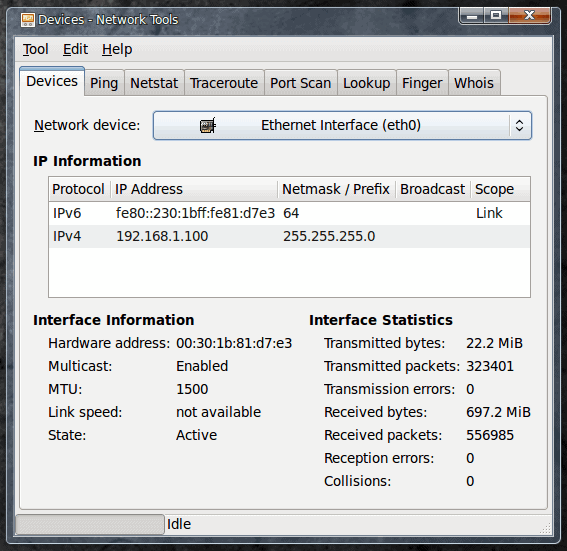
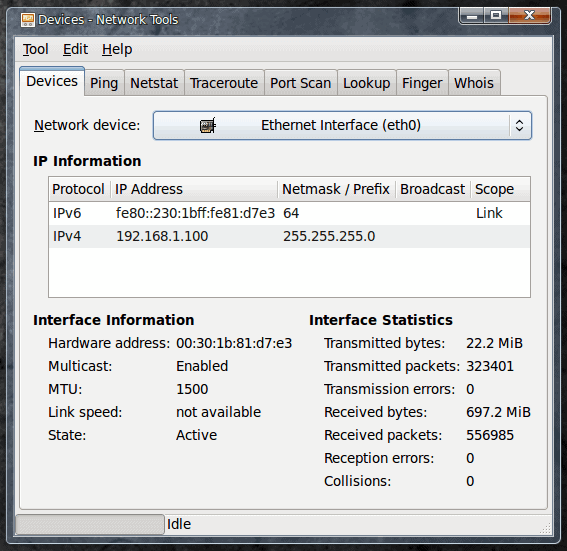
As you can see there has been no mention of installation. That is because GNOME Nettools is installed by default. In order to start up the tool you only have to go to the Administration sub-menu of the System menu. Once you have fired up the tool you will be greeted with main window at the Devices tab. This tab is where you gather the information about your installed networking devices. As you can see (In Figure 1) there is plenty of detailed information about my default eth0 interface. You can switch this to display information about any connected internet device you have on the machine by using the Interface drop-down.
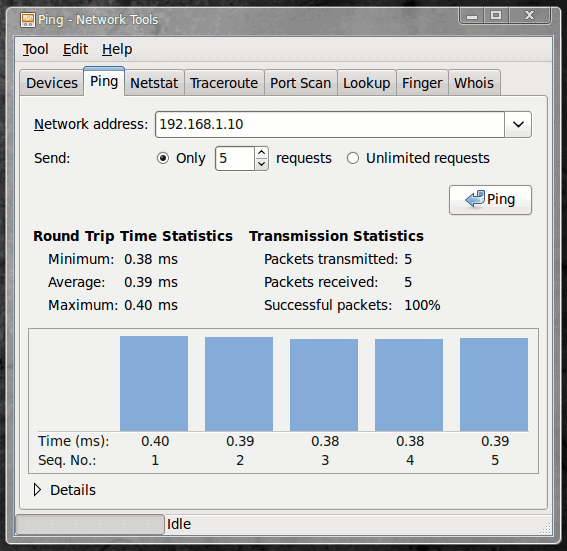
The next tab, Ping, is where you can actually start troubleshooting networking issues. Ping is almost always one of the first tools I use, but I generally use it in command line form. Since most new Linux users prefer to not use the command line - you can still get your ping on with Nettools. Click on the Ping tab to reveal how the Ping tool works (see Figure 2).
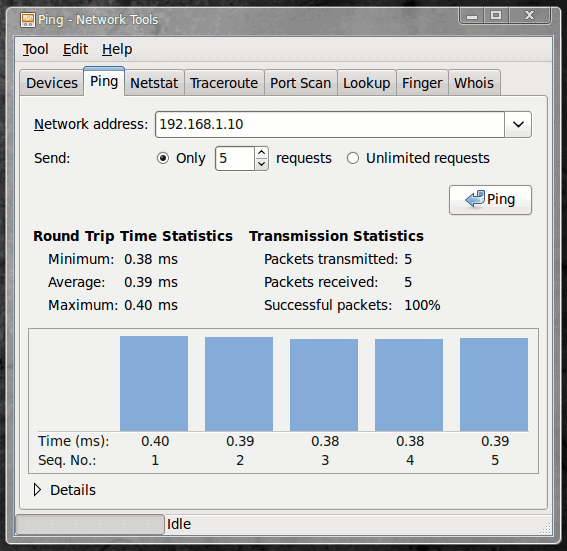
By default the Nettools Ping tool will be configured for a limited 5 requests. You can up that number or even change it to an unlimited number if you need. In Figure 2 I have sent 5 ping requests to an internal server and received 100% sucess on my packets. I know this server is at least responding.
The other tools will all work exactly as you would expect them. One thing that is nice is as a tool is working you can switch over to another tool without disrupting the original tools task. This is especially nice when running a traceroute that can take a while (see Figure 3).
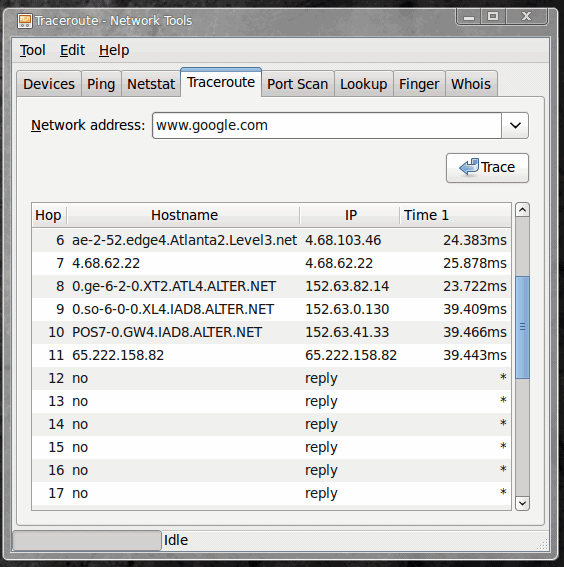
The traceroute tool will follow a path, hop for hop, to a destination you enter. In Figure 3 I ran a traceroute on www.google.com which ended before it reached its goal. This, of course, was only to show you the output of the traceroute (as there is not much I can personally do if my route to www.google.com is stopped outside of the boundaries of my network or my service providers network. But it gives you an idea of where the route stops. If this were a corporate issue, and the destination was one I had to reach, I would know precisely where the last known successful hop was (in the case of Figure 3 - after the 65.222.158.82 address).
I can then use the Whois tool to discover who is connected to that address. By clicking on the Whois tab and then entering the IP address above I receive the following information:
MCI Communications Services, Inc. d/b/a Verizon Business UUNET65 (NET-65-192-0-0-1)
65.192.0.0 - 65.223.255.255
SPLICE COMMUNICATIONS, INC. UU-65-222-158-80-D4 (NET-65-222-158-80-1)
65.222.158.80 - 65.222.158.87
If www.google.com were a critical address for me (and my company) to reach for work (or a host of my company's web site) I could at least contact the owner of this domain.
Final thoughts
As you would expect, the rest of the Nettools tools work in a very similar fashion than their command line counter parts. The only difference? You don't have to open up a terminal window to use them. No commands to remember, no commands to type. Just easy network analysis, with the help of a user-friendly GUI tool.