Time to patch: Chrome 120 fixes a 0-day security issue

Google released an update for its Chrome web browser a moment ago that fixes four security issues in all desktop versions and in Chrome for Android. One of the patched security issues is exploited in the wild.
Chrome users on desktop systems may update Chrome to the new version already. This is done automatically by Chrome, but some users may want to update the browser immediately to protect it against the 0-day vulnerability that is targeted in the wild.
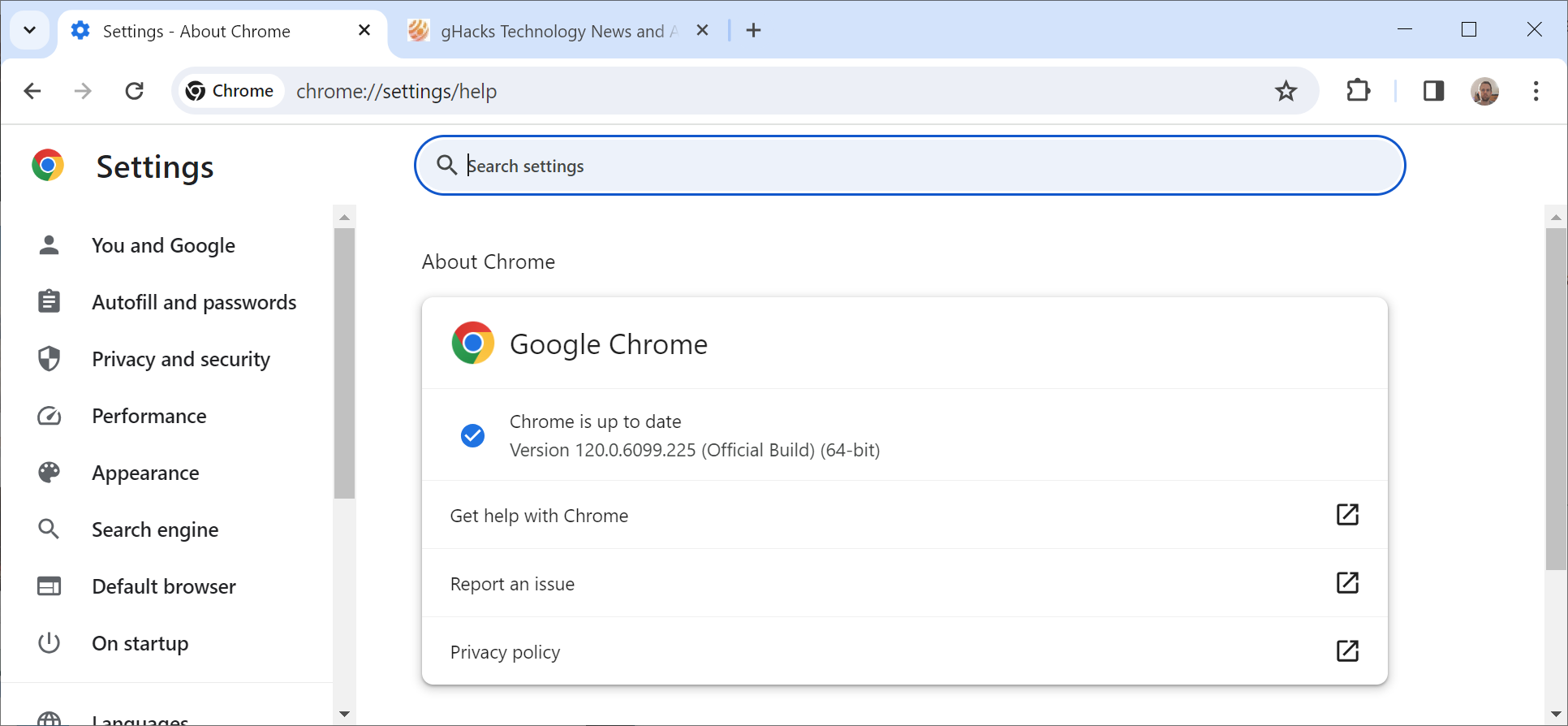
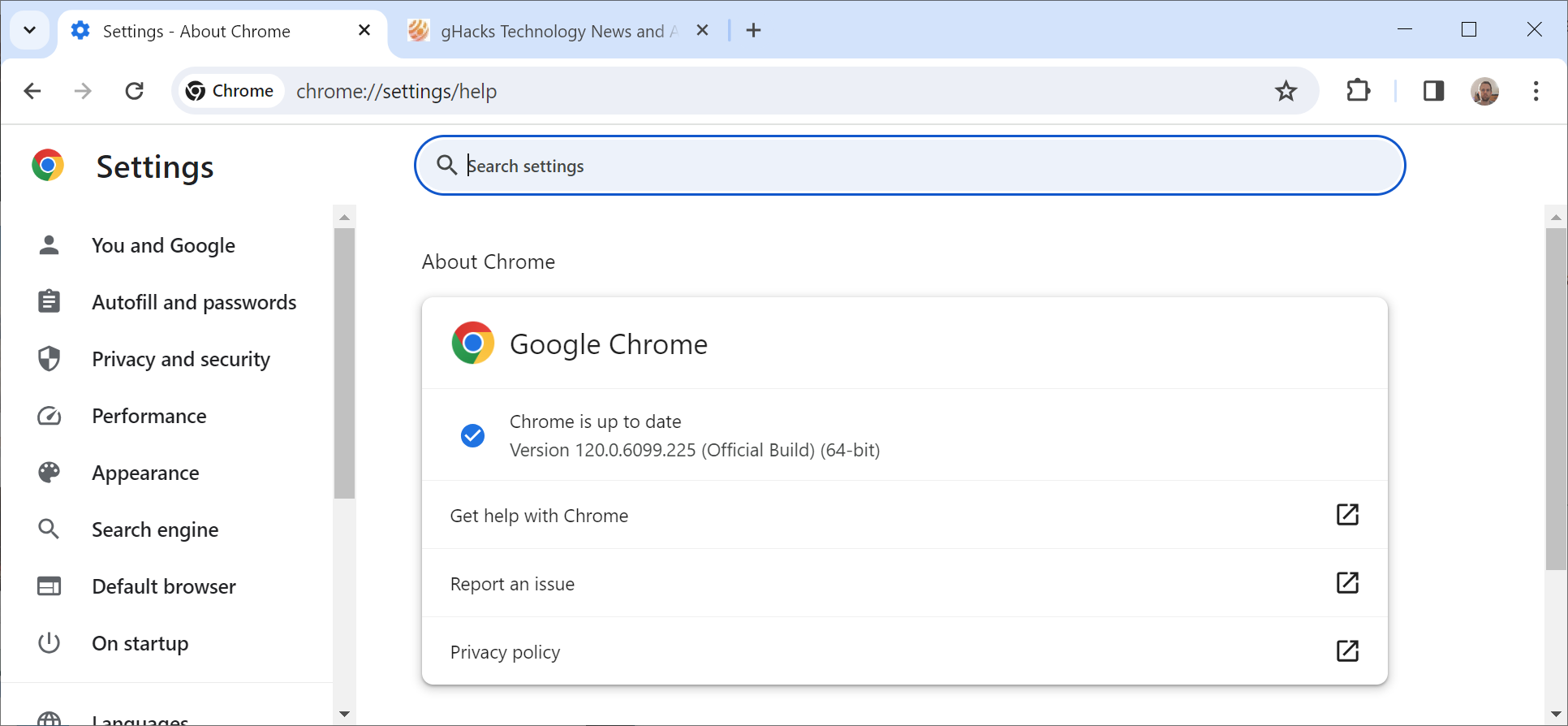
Load chrome://settings/help in the browser's address bar or select Menu > Help > About Google Chrome to open the same page. Google Chrome runs a check for updates and will download and install the security update at this point. A restart of the web browser is required to complete the installation of the update.
The Help page should list one of the following Chrome versions after instalation:
- Chrome for Mac: 120.0.6099.234
- Chrome for Linux: 120.0.6099.224
- Chrome for Windows: 120.0.6099.224 or 120.0.6099.225
- Chrome Extended Stable Channel for Mac: 120.0.6099.234
- Chrome Extended Stable Channel for Windows: 120.0.6099.225
Chrome 120 patches a 0-day vulnerability
The official Google Chrome releases blog lists three of the four security issues that Google addressed in the update on the page. Google does not reveal information about internally discovered security issues on the blog.
The three listed issues include the 0-day vulnerability that is exploited in the wild:
- [$16000][1515930] High CVE-2024-0517: Out of bounds write in V8. Reported by Toan (suto) Pham of Qrious Secure on 2024-01-06
- [$1000][1507412] High CVE-2024-0518: Type Confusion in V8. Reported by Ganjiang Zhou(@refrain_areu) of ChaMd5-H1 team on 2023-12-03
- [$TBD][1517354] High CVE-2024-0519: Out of bounds memory access in V8. Reported by Anonymous on 2024-01-11
Google confirms that CVE-2025-0519 is exploited in the wild: "Google is aware of reports that an exploit for CVE-2024-0519 exists in the wild."
The issue was reported on January 11, 2024 to Google. It affects V8, which is the JavaScript and WebAssembly engine that Google Chrome uses. All three listed security issues affect the engine in Chrome.
Other Chromium-based browsers are also affected by the issue. Look for security updates for these browsers as well to protect them against potential attacks on the web.
Chrome users are encouraged to install the update immediately to protect the browser against attacks.
Google released Chrome 120 Stable on December 6, 2023 to the public. The update included security updates but also password sharing improvements and introduced automatic safety checks in the browser. Additional point updates were released in the meantime, including on December 13, 2023.
Now You: do you run Chrome?


















every day is chromium patch day – just use Firefox
Best and fastest way of updating and fixing bugs and security issues ever! :]
Chrome is going to have to be entirely re-written in a memory safe programming language like Rust, or they will never get to the end of these kinds of vulnerabilities. Google programmers are just useless at writing proper code.
Maybe Google can hire Mozilla to re-write the whole browser for them.
“useless at writing proper code”
The majority of all functional code ever written out in the wild is not written in rust, rust is relatively new still and is not a silver bullet for all problems. Not only is it completely possible to write garbage code in rust (it is after all, just a language), but also I am pretty sure you can use methods to write code which isn’t memory safe at all, explicitly so. So just because rust is involved doesn’t mean you have 100% memory safety, that can only be verified by looking at the code…
Like you could do any better Bruh.
If you can prove it ? I don’t think you can ?
Oh good, another weekly security scare attacking Chrome and/or a Chromium based browser which is majority of browsers today. Why wouldn’t these hackers keep pounding on Chrome.