Google Play Store malware installed on 1.5 million Android devices

Google's Play Store is the go-to store for most Android users when it comes to installing new apps and games for the operating system.
Like Google's Chrome Web Store, which is the place to install Chrome extensions, Google's Play Store has had its fair share of malicious apps and games that were offered to users.
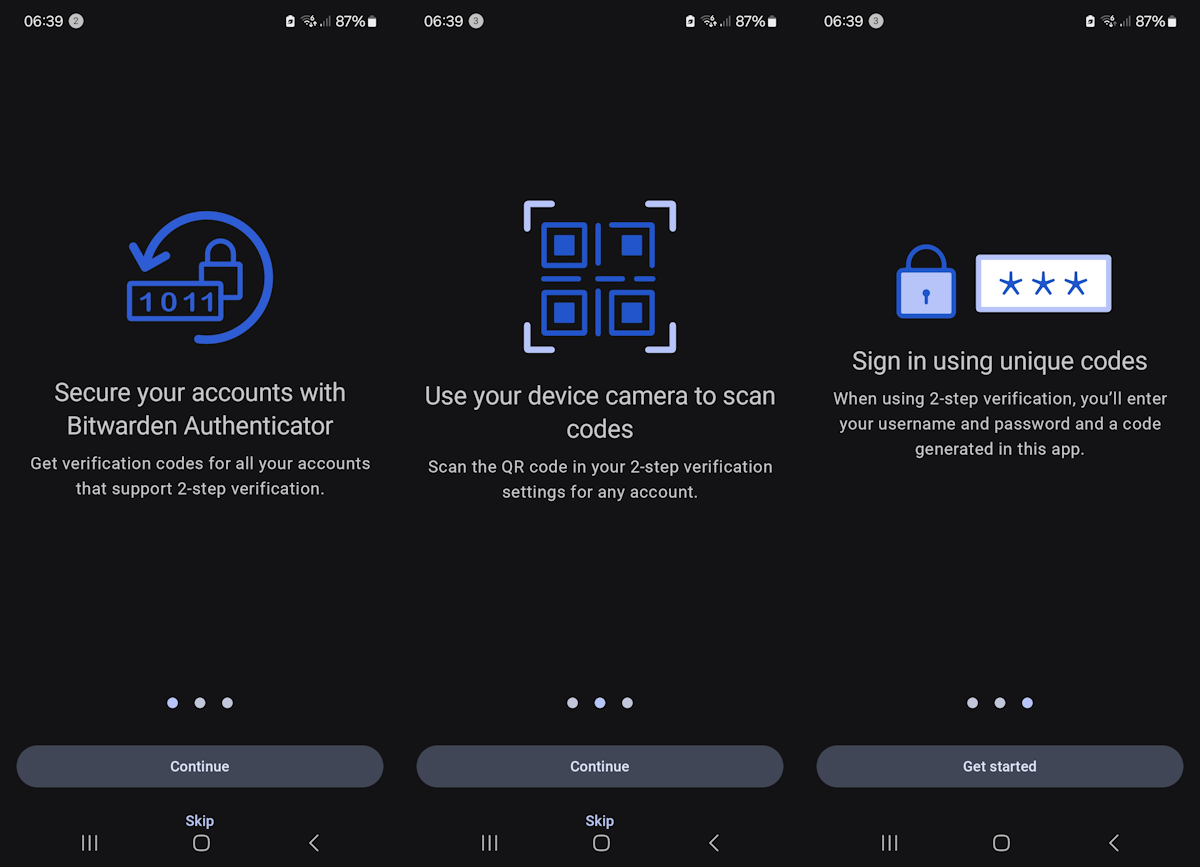
Just recently, it became known that malicious authenticator apps were listed on the official store. Back in 2022, researchers discovered apps with malware that were downloaded 500,000 times by users, and just last month, security researchers discovered a malicious SDK in a number of apps.
Security researchers at Pradeo have discovered two spyware applications on Google Play that were downloaded more than 1.5 million times by Android users. The applications, File Recovery & Data Recovery (com.spot.music.filedatecom.spot.music.filedate) and File Manager (com.file.box.master.gkd), disguised themselves as file management applications. Their main purpose of them was to send as much user data as possible to servers in China.
File Recovery & Data Recovery was downloaded more than 1 million times from Google Play, File Manager more than 500,000 times. Both applications listed fake Data Safety information on Google Play, claiming that they were not collecting any data.
Data Safety is mandatory information that app developers need to provide about their apps. The information that developers submit is not verified manually by Google.
Both applications had a relatively large number of downloads but no reviews. The researchers suggest that the developers of the app could have enhanced downloads artificially, for example, by using installation farms or mobile device emulators.
Pradeo researchers discovered that the two applications were busy as a bee collecting data from devices they were installed on. Data included:
- The contact lists from the device and from connected accounts, e.g., email accounts, social networking accounts.
- Media, such as pictures, audio or video.
- Real-time user location data.
- Mobile country code.
- Network provider name.
- Network code of the SIM provider.
- Version of the operating system.
- Device brand and model
The installed applications performed "more than a hundred transmissions of the collected data", which, the researchers write, is "so large it is rarely observed".
The applications in question are no longer listed on Google Play at the time of writing. Android users may want to check the list of installed programs to uninstall the apps, if they are still installed on their devices.
Pradeo notes that both applications hid their application icon on the home screen to make the uninstallation difficult. Android users have to open Settings > Apps to get a list of all installed applications and uninstallation options.
Now You: do you vet apps before you install them?




















@Martin Brinkmann
OT: Google is removing the NewPipe homepage from its search results due to a DMCA takedown, might be worth an article:
https://newpipe.net/blog/pinned/announcement/newpipe-net-dmca-google-search/
Protect all my webs and apps
“Google Play Store malware installed on 1.5 million Android devices”
Only 1.5 million ? Isn’t the play store installed by default on every device ?
If you consider GPlay as a malware (which sometimes is) then yes.
The report said 1.5 million downloaded malicious apps from Google and a crap-ton of data was sent back to Chinese servers.
Are the Chinese copying Google’s tracking schemes, and double-crossing both the 5-eyes and Google?
The Chinese are copying the 5-eyes/Google data collection scheme?
If android came with a proper file manager by default instead of manipulating you into using google services people wouldn’t need to search for third party apps to do basic OS functions.
Makes you wonder about the Firefox browser about:config setting “browser.safebrowsing.enabled which is set to True by default” along with “browser.safebrowsing.downloads.remote.enabled also set to True”. How can Google be trusted to get it right when they can’t even protect their own Store.
@TelV
Yeah man, malware problem in Google Play Store which relies on developers sending their apps to Google so users can download those apps is somehow linked to safebrowsing used for detecting malicious websites and somehow Mozilla is responsible for all that.
Go touch some grass man.
It would be great if you could post a jpeg of the icons for the dubious android apps so I can quickly see if I’ve downloaded them. There are so many apps called File Manager that I have no idea if I have the malicious one or not. Or is there is an easy way I can see the apk name of the file manager I have installed?
Use apps from F-Droid. File manager, app installer apps on F-Droid aren’t constrained by Google API limit and hence are much more powerful and feature rich. Infact you only need Play Store apps for games or to use services of a particular service provider which has its own exclusive app. For other tasks open source is the way.
Google claims to have stringent requirements for apps on Play Store, but look at all of the malware that has been uploaded to the platform.
Google needs to start actually reviewing all code of all apps initally place, and when updated on the Play Store.