Azure vulnerability allowed hackers to manipulate Bing results and take over accounts

BingBang, that is the name that security researchers at Wiz gave the Azure platform vulnerability that allowed them to change Bing search results and access Microsoft user data, including emails and work documents.
Good news is that Microsoft patched all of the vulnerabilities, and has promised to improve customer guidance and change some Azure Active Directory functionality.
Bad news is that anyone with knowledge of the issue could have exploited it for months. Wiz, which describes itself as the world's largest cybersecurity unicorn, explains in a blog post how it discovered the Azure Active Directory vulnerability and discovered through scans that about "25% of multi-tenant applications" are vulnerable to it.
Among the applications were several major Microsoft applications. One was a content management system for Bing, which allowed its users to modify Bing search results. Wiz describes how it used the CMS to replace one of Bing's award-winning soundtrack carousel suggestions with its own suggestion.
Next to the direct manipulation of Bing search results, it gave Wiz the ability to launch "high-impact XSS attacks on Bing users". These attacks could be used to gain access to a user's personal data or work documents, depending on the services used. Access to Outlook emails or SharePoint documents were possible through these attacks.
Security researchers at Wiz discovered the vulnerability in January in Microsoft's cloud computing platform. The researchers found a misconfiguration in Azure that enabled them to compromise the content management system and other applications on Azure.
The main issue affected multi-tenant applications only. This type of application allows "any Azure tenant to issue an OAuth token for them" and the developers of the application need to inspect these to allow or deny access. If developers fail to implement proper access validation, any Azure user may be able to sign-in to that application.
Wiz notes: "This complicated architecture is not always evident to developers, and the responsibility to validate the end-users’ tokens is unclear. As a result, configuration and validation mistakes are quite prevalent."
The company decided to focus on Microsoft's own applications, as it found too many vulnerable ones during its scan. It stumbled upon the Bing Trivia application, and discovered quickly, that the application could control certain results on Bing. One of the sections was Carousels, but there were others, including background images and quizzes.
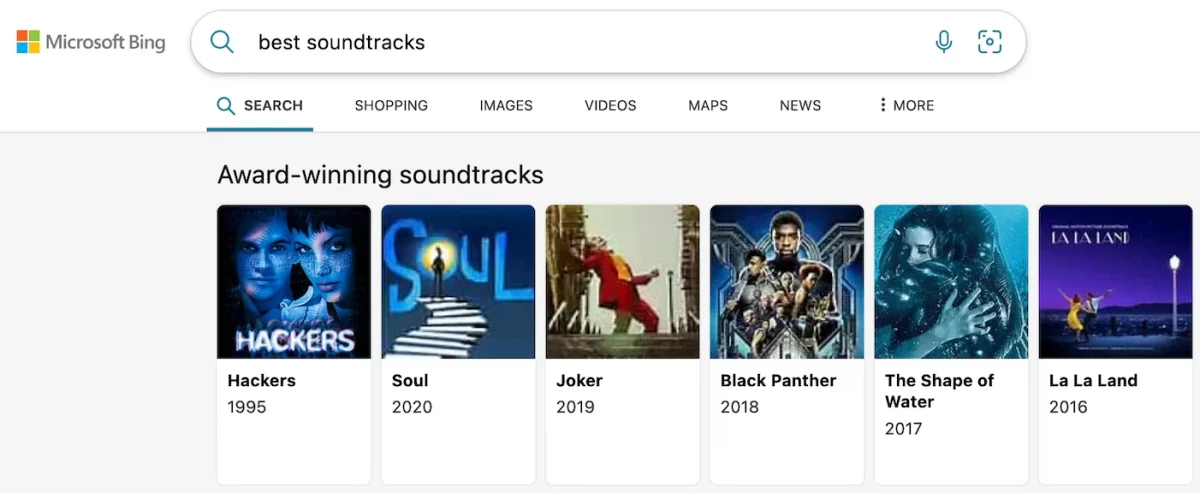
The researchers were surprised that the changing of content in the CMS had a direct effect on Bing. The changed content was displayed immediately on Bing for the linked search query.
Direct manipulation of content on search engines opens a can of worms. Threat actors could have used this to replace legitimate content with malicious one, e.g., by sending users to fake websites.
The security researchers dug deeper and discovered that they could also inject XSS payloads. They used a dummy account to "fetch the victim's Office 365 data including Outlook emails, calendars, Teams messages, SharePoint documents and OneDrive files".
Wiz notes: "A malicious actor with the same access could’ve hijacked the most popular search results with the same payload and leak sensitive data from millions of users. According to SimilarWeb, Bing is the 27th most visited website in the world, with over a billion pageviews per month – in other words, millions of users could’ve been exposed to malicious search results and Office 365 data theft."
Wiz discovered other vulnerable Microsoft applications, including a MSN Newsletter, which they could have used to send out emails to all recipients, CNS API, an internal notification service to send notifications to Microsoft Developers, a similar API for Call Center agents, access to a file management system with over 4 exabytes of internal Microsoft files, or full access to a Microsoft WordPress blog.
Wiz recommends that administrators run a query to find out if any applications are configured to allow multi-tenant access. Admins may also run a command from Azure CLI. Details are found on the Wiz website about this.
















