Google Chrome 108 update patches 28 security issues
Google released a new stable version of its Chrome web browser for all supported desktop operating systems, Android and iOS. The update addresses 28 different security issues in the browser and introduces some new features.
Chrome 108 is the last major stable version update of the browser in 2022.
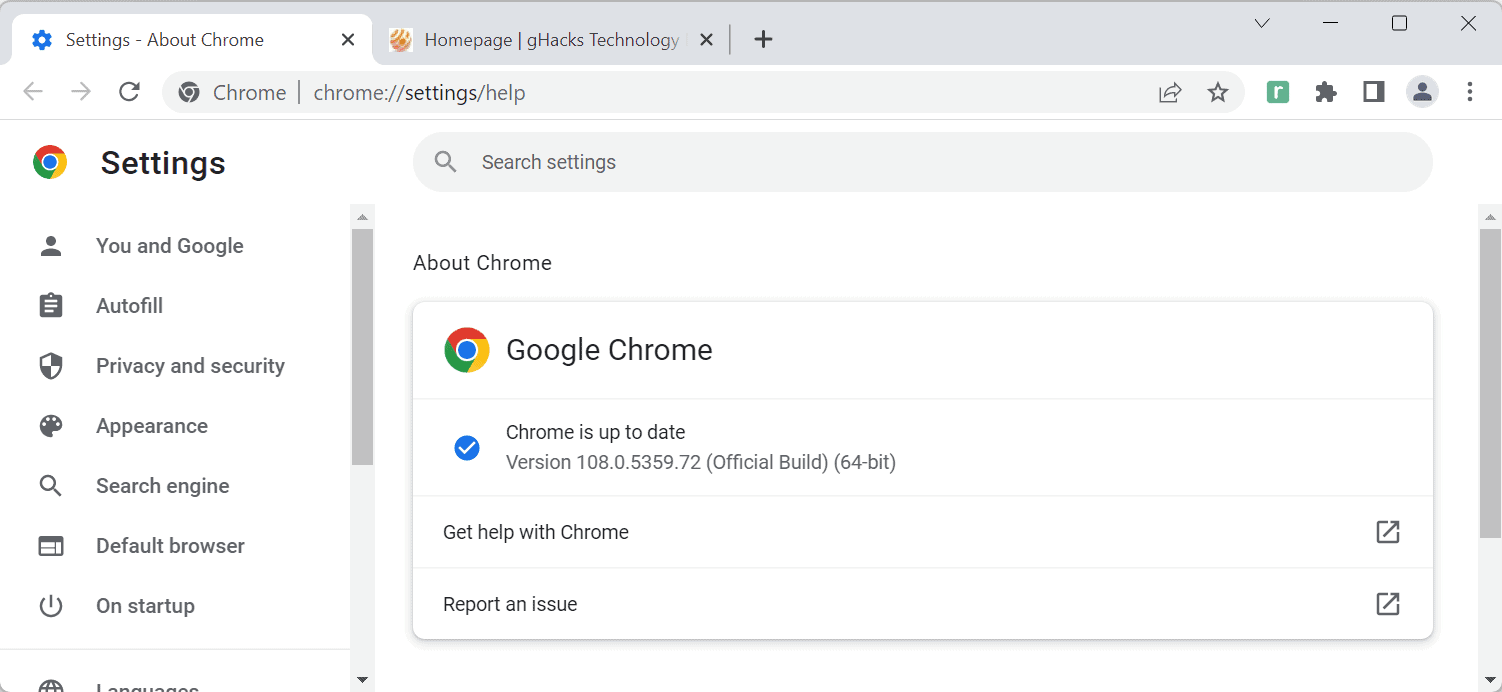
The security update is already available and should be installed on most Chrome installations automatically. Chrome users may speed up the process of installation by selecting Menu > Help > About Google Chrome.
Chrome has the version 108.0.5359.71 on Mac and Linux devices, 108.0.5359.71/72 on Windows, and 108.0.5359.61 on Android after the update.
Note that the Android and iOS versions are updated through the official Google Play Store and App Store. The Android update for Chrome includes the same security fixes as the desktop version.
Chrome 108: a major security update
Google Chrome 108 is a security update first and foremost. Google lists 28 different security issues that it addressed in the new version. The company lists all externally reported security issues on the official Releases blog.
All listed security issues have a severity rating of high or medium, which are the second and third highest ratings after critical.
Google makes no mention of exploits in the wild; this is good news as the company does not appear to be aware of attacks that target one of the fixed issues.
Security issues affect camera capture, extensions, audio, the popup blocker, autofill, and several other features and functions of the web browser.
The platform status page for Chrome 108 lists mostly behind the scenes changes that Google highlights. The majority of these affect web developers and extension developers only, e.g., wildcard support in Permissions Policy Origins.
The next Chrome release, Chrome 109 Stable, is scheduled for January 10, 2023.
Since the majority of security issues that Google fixed in Chrome 108 are Chromium-based, users of other Chromium-based browsers, such as Vivaldi, Edge, Brave or Opera, should expect updates for these browsers as well soon that address the issues. This may take a few hours to days or even weeks, depending on the browser.
Now You: when was the last time your primary browser was updated?


















So I’ve been waiting for a day to comment under this article, wanting to see whether or not we get the same complete nonsense again from the Firefox community, and lo and behold, here we are.
The shills and fanboys posting under this article, which discusses a product they don’t use, continue to overlook the market share imbalance between Chromium (80% market share) and Firefox (4% market share). No hacker gives a single shit about Firefox as any potential exploit would only cover 4% of all website visitors, statistically speaking. This, however, does not mean that Firefox can be described in terms of the code. Firefox has no real site isolation and lacks sandboxing on various platforms, meaning in instances where you have to come up with an escape out of those in Chromium, you don’t even need such an escape in Firefox and you can compromise it more easily. This is not more secure, sorry Firefox shills.
The browser is one of the most attacked tools out there since, by definition, it interacts with internet. This is what browsers have in common with the historical Adobe Flash… except the browser is a far, far, far more complex peace of software encompassing a much wider range of functionality than Flash, but this surely doesn’t stop misguided comparisons being made here. If so much focus of hackers is on the browser, and if Chromium is the most used browser by far, you get what is described in the article, period. If Firefox had 80% market share instead of Chromium, considering that it doesn’t even feature some exploit mitigations that Chromium does have, you would get daily news of it having been compromised and the hacks would be more trivial in nature.
Tired of the heavy stupidity displayed in the comments, ignoring the actual code comparison of either browser and ignoring popularity, a factor that more or less determines whether any given software is a target, or not. All you get on this blog here is shilling and deliberate misinformation from the usual suspects, under every single article.
@Iron Heart – you’re not wrong, but I prefer Firefox for general use because more privacy, more control, and they’re not going to do a half hearted attempt at deprecating adblockers like Chrome is planning.
However – Chrome/Google have far more money & developers to throw at the project, most of the severe vulnerabilities in the past have been caused by insecure memory – why on earth are they not making a consolidated hard push to switching Chrome’s entire codebase to Rust?
@Guest
I mean, use whatever. I can’t influence that and I don’t want to influence it either.
All I want is to argue against provably false claims – the false claim being that Firefox is more secure. This can’t be proven via the actual code of the browser, as Firefox demonstrably lacks various exploit mitigations. It might nominally get hacked less, however this is not due to superior security, but rather due to the fact that it is fairly irrelevant compared to Chromium.
Google is a big corporation and has the funding, however the code is still written by human beings, meaning there will be errors which are not immediately noticed. Consider that modern browsers are as complex as operating systems, this is also true for Firefox. They are the most attacked piece of software on your PC as they interact with the internet and Chromium is the most popular / attractive to hack browser, so…
As for the memory-safe language, Google is discussing such a transition. Maybe they will choose Rust, maybe another memory-safe language (yes, there is more than one). This might help against a specific class of vulnerabilities but is not a silver bullet fixing everything. Firefox needs to make this transition as well seeing how none of the most attacked components of Firefox is actually written in Rust as of yet.
Excuses, excuses, excuses.
Google is worth $100’s of BILLIONS. Hire enough competent people to write and test the code you put out instead of trying to squeak by with as low a spend as possible.
28 security issues in a browser with 108 prior releases is criminal. Heads should roll.
Google never was good, they don’t even know what their customers/products want. Every year you see dozens of axed Google products. I assume half their devs are working on projects to be culled just a year later.
[https://killedbygoogle.com/]
*described as such, piece
Good grief, this is getting ridiculous. I just updated ungoogled chromium yesterday to 107.0.5304.122. It will probably be 2-3 days before this new 108 version is released. But all of this is why I only use it as secondary browser and only for a few trusted web sites.
+1. Ungoogled Chromium as a secondary “vanilla” (no add-ons) browser for the few sites that need it, and Firefox ESR with uBO, NoScript, Cookie AutoDelete and a few more for daily use. Both in permanent private/incognito mode.
Fewer releases, with fewer bugs, would be welcome.
+1
Chromium should make a better effort to increase the security and debug all risky code as they would be able. There is no reason to maintain such a big amount of dangerous bugs month after month, and furthermore they should release “daily 0 patches” for the very risky ones. Every single day, not monthly!
I’m going to Opera permanently the other month, wish me luck.
I’m dumping Brave after this debacle. Going back to Firefox. I value my security, thank you.
@PokemonGirl
Welcome home… to fewer exploit mitigations! :…..D
_https://madaidans-insecurities.github.io/firefox-chromium.html_
A lot of yadda yadda linking to 2014 tier old twitter posts of dubious security researchers.
Not even relevant today with firefox rewritten in Rust.
@Frankel did you even read the article? It covers Rust. Only a small portion was re-written in Rust, and not the parts that could face potential vulnerabilities. I’m a Firefox #1 fan but this is concerning.
Hang on a sec. @Iron Heart – your article is from March 2022. That’s old!
See: https://hacks.mozilla.org/2022/05/improved-process-isolation-in-firefox-100/
@Guest
What Frankel says is provably false, the article has existed for a few years but is getting updated whenever something major moves at Mozilla, and it has been updated in 2022 already. madaidan is also far from dubious, he is a main developer of the Whonix project which is highly respected in the privacy community, being used by activists in oppressive regimes who rely on it for their safety. Very “dubious”, right? I guess comments like this happen when you have no argument to make, then you post shite like this, I guess.
And yeah, as for Rust, you have already correctly pointed out: Some minor parts of Firefox are written in Rust, yet none of the most attacked components currently is. This hardly improves anything, and Rust in general is no silver bullet for everything.
Process isolation – Firefox has defective / incomplete process isolation, they have hard-limited the content processes to eight (8), meaning different websites can still share the same content process, whereas in Chromium different websites can’t share the same content process. It should be obvious that Firefox’s implementation is not sufficiently secured yet by definition, and madaidan actually addresses this in his article. Win32k lockdown, this is / was buggy so that it was not enabled by default so far. Has that changed for all systems? If yes, then madaidan should update his article. If not, then he shouldn’t. It will be enabled by default if it’s no longer beta level code, and then the article will receive an update accordingly.
@PokemonGirl.
Welcome Home!
:)
I’m using Opera and Brave, they are really nice. Sometimes I use one browser for a few months, something pisses me off, I switch to the other and vice versa.
Opera is by far the fastest Chromium browser.
> Security issues affect camera capture, extensions, audio, the popup blocker, autofill, …
call it what it is, the whole browser engine is suspect and easily bypassed. We’re up to one security patch a day .. 28 (and a zero-day) since the last major release four weeks ago
outdoing adobe flash since 2018
Oh God, such a lot of bug and security fixes, it’s quite more than the latest half quarter. :[
But the clever people told me Chrome was good! Did they trick me? Anyway, still on fox.