Microsoft is testing an Automatic HTTPS Mode in the Edge web browser
Microsoft added support for a new browsing mode called Automatic HTTPS to its desktop Microsoft Edge web browser designed to enforce the use of HTTPS connections when connecting to sites and services.
Many Internet sites have switched to using HTTPs in recent years. HTTPS protects connections and it is also beneficial for sites as search engines such as Google may use it to determine a site's visibility in search engines. Some sites support HTTP and HTTPS connections side-by-side, others only HTTPS or only HTTP.
Microsoft Edge's Automatic HTTPS mode feature supports two modes. The default mode works similarly to the browser extension HTTPS Everywhere; it attempts to upgrade HTTP connections to HTTPS but does not enforce it. In other words: HTTP is still allowed and used in Edge if HTTPS is not an option.
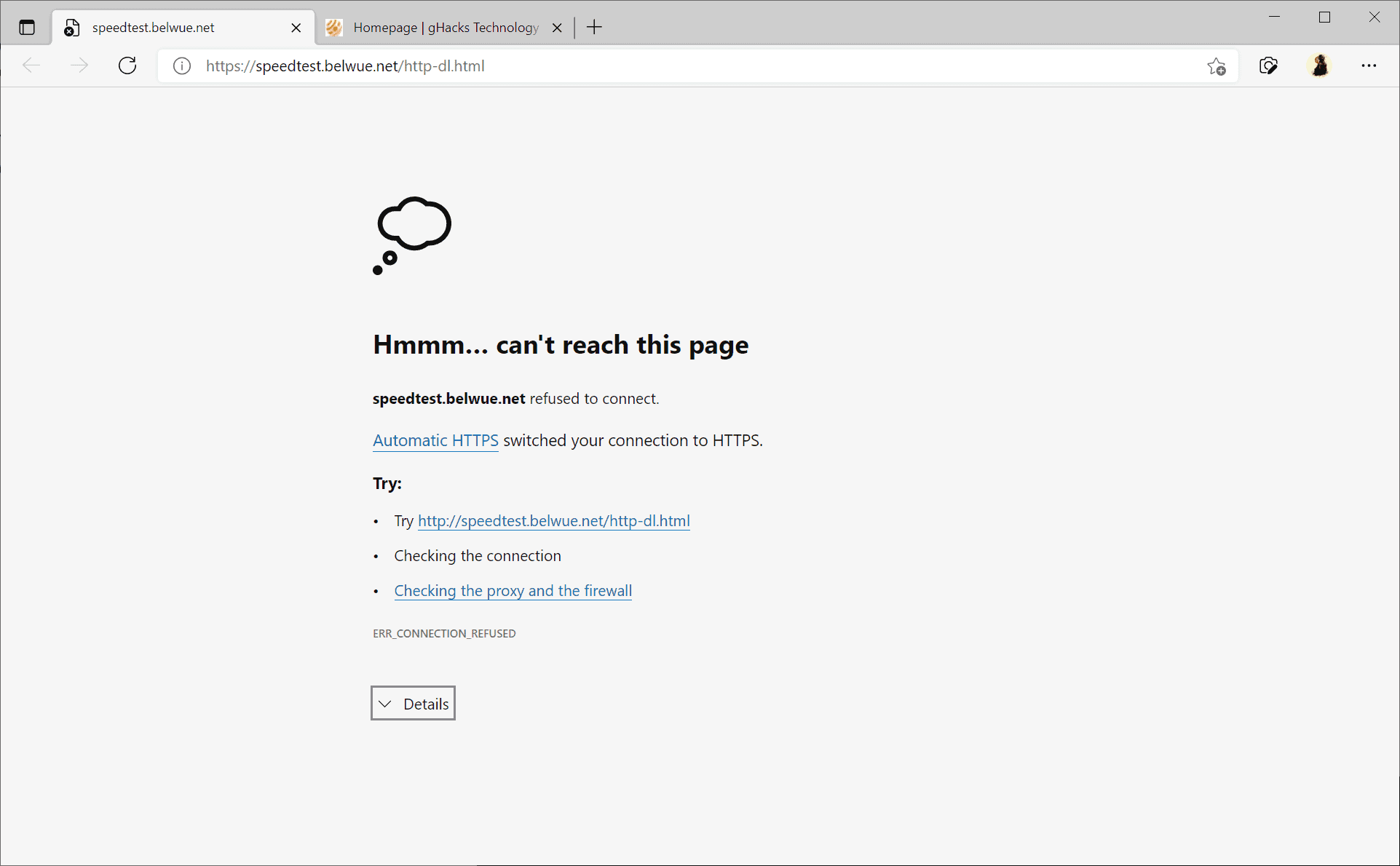
The second mode resembles Firefox's HTTPS Only Mode, but without the fallback option. When enabled, Edge will upgrade all connections to HTTPS, even those that don't support it. Errors are thrown if a site or resource cannot be loaded via HTTPS, but unlike in Firefox, Edge does not offer an option to make an exception and access the resource via HTTP.
Edge displays an error message if the upgrading from HTTP to HTTPS failed, but no option to circumvent it. A toggle is not provided, and the only recourse at this time is to click on the settings link to switch the feature to the lighter mode or to disable it entirely for the time being.
Since it is in development right now, it is possible that a circumvent feature or a allow/disallow list feature is implemented before it reaches the stable version of the Edge browser.
Automatic HTTPS
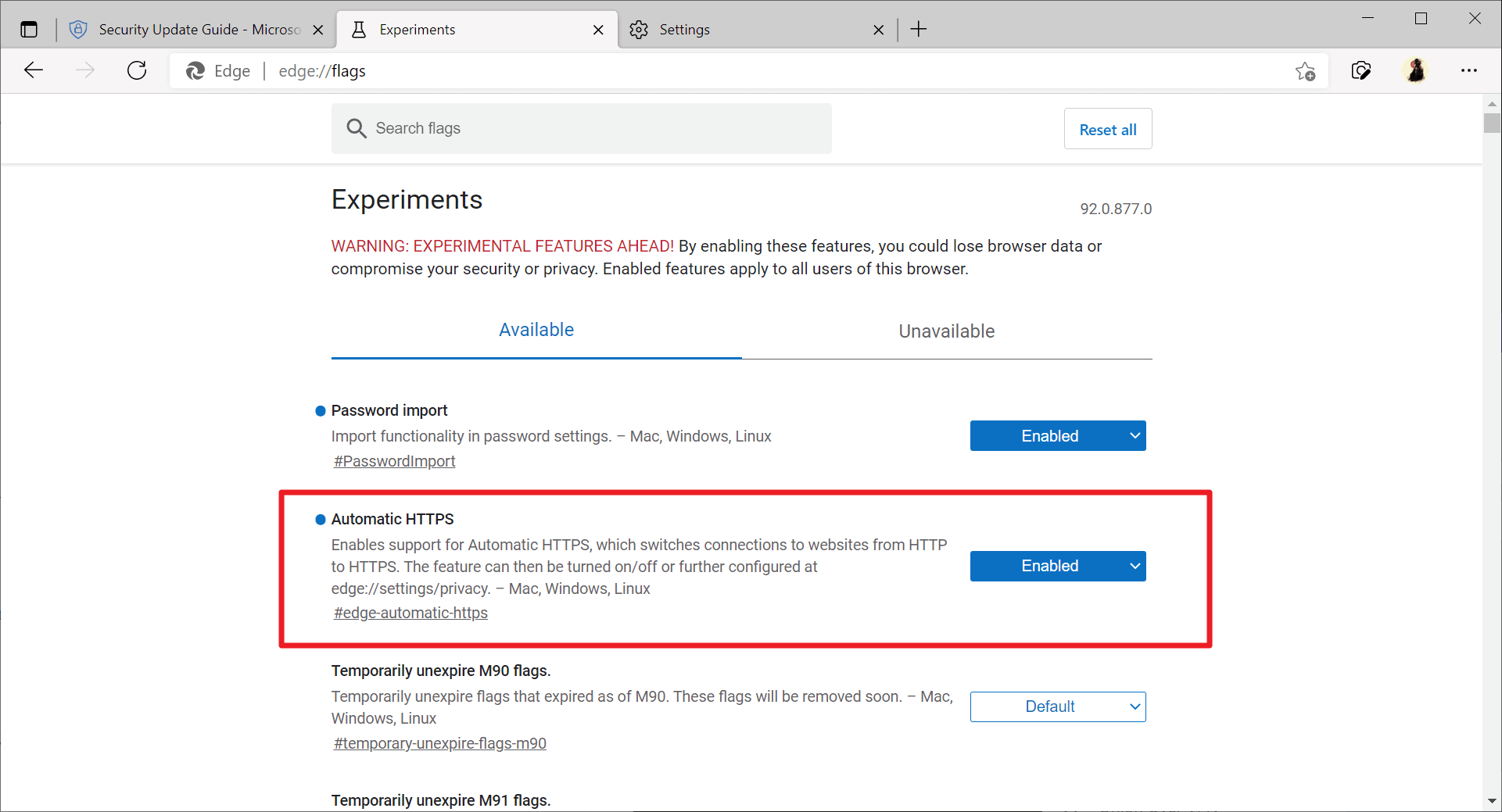
Automatic HTTPS is an experimental feature that is available in Microsoft Edge Canary, version 92.0.877.0, at the time of writing. You can verify the version of the browser by loading edge://settings/help in the address bar.
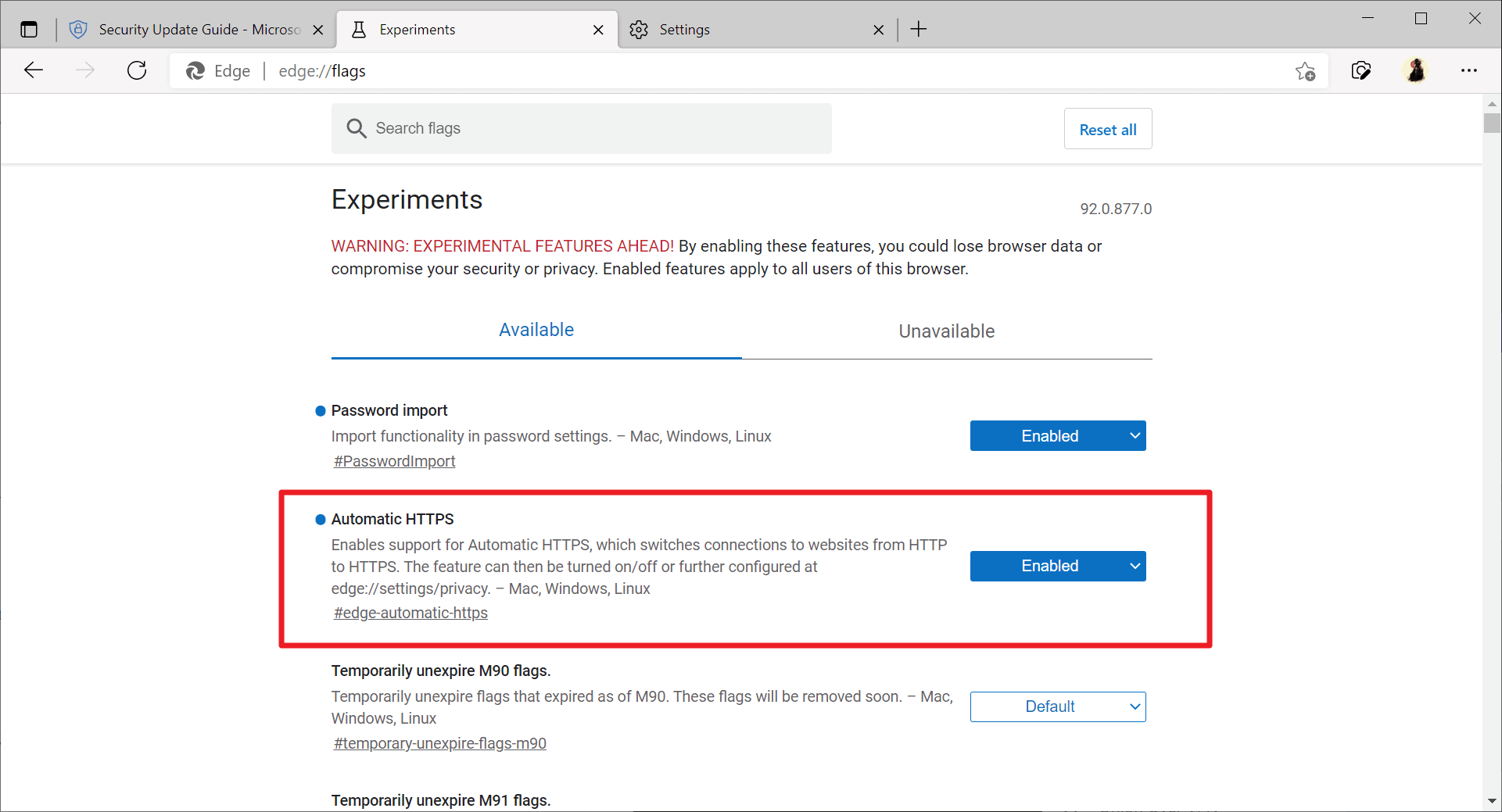
To configure Automatic HTTPS Mode, do the following:
- Load edge://flags/#edge-automatic-https in the browser's address bar.
- Set the experimental feature to Enabled.
- Restart Microsoft Edge.
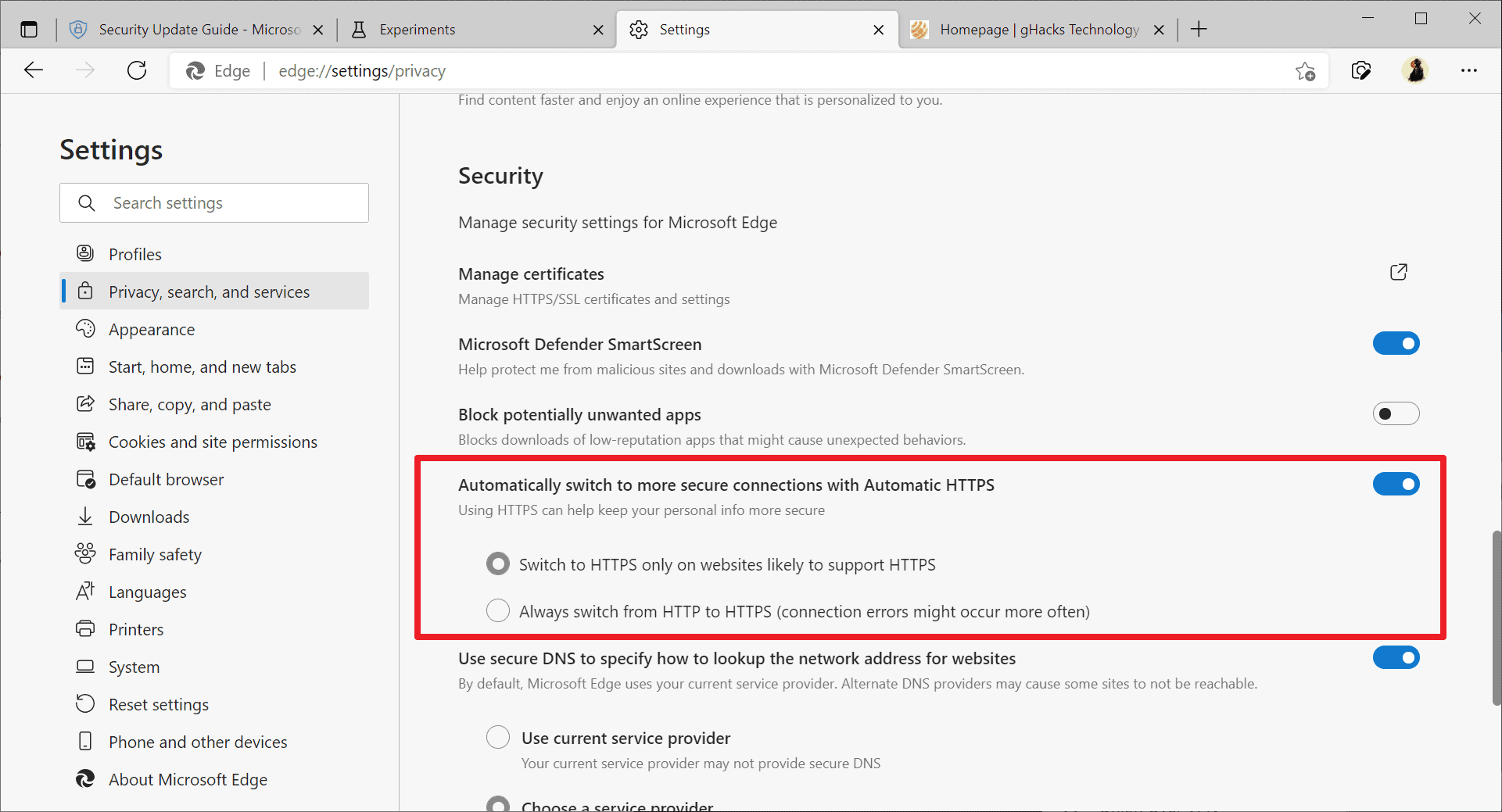
The lighter version of Automatic HTTPS is enabled by default. Open edge://settings/privacy in Edge and scroll down to the new Automatically switch to more secure connections with Automatic HTTPS section to turn it off or switch to the mode that enforces HTTPS without fallback.
How useful is Automatic HTTPS in Edge?
Automatic HTTPS mode in Edge attempts to upgrade HTTP connections to HTTPS. The first mode attempts to upgrade connections but does not enforce the use of HTTPS so that sites and resources will load if the upgrade fails.
The second mode enforces HTTPS and does not offer a fallback. While more secure, it may require manual interventions from time to time when sites or resources won't load because of missing HTTPS support.
The lighter version of Automatic HTTPS should be usable by all users of the browser, as it works similarly to HTTPS Everywhere. It tries to improve the security of connections in the browser. The stricter mode may be useful when it comes to tasks that benefit from higher security.
Now You: do you use extensions or browser features that upgrade HTTP connections?




















Reads like something from two or three years ago, why is MS so far behind?
Nevermind…
Perhaps you should read more then…
Lol
Very good news for Edge users.
Anonymous, Are you quite sure you should be happy about that? I am asking this because the duckduckgo privacy essentials are doing a better job.
That’s good, but I think Edge should block FLoC first and foremost. Not that I will ever use Edge, I have it uninstalled and have IE as a backup browser if some website doesn’t work due to content blockers in my main.
From another site:
“When building Chromium-based browsers, Google has enabled support for FLoC by default, as shown in Chromium’s source code.
This means that other companies who develop Chromium-based browsers, such as Microsoft Edge, will automatically have the component installed as well unless they specifically disable it.
Such is the case with Microsoft Edge, where FLoC has not been enabled, and the component is not available in the browser even if enabled via command-line arguments.”
That’s good, Google’s attempt might not succeed after all.
Perhaps, especially if more sites follow in the footsteps of MS-owned GitHub and set the appropriate http headers to disable FLoC at their end too.
Of course, Google will naturally retaliate with something else equally or more malignant, or maybe it won’t even need to. Simply having FLoC enabled in Chrome (and surely Android Webview etc. eventually) will mean the majority of browser and mobile users will be affected whether they like it or not. Unlike the other tech giants, Google is after all chiefly an ad company that also makes software to help it further spy on and target users better.
@Anon
And that’s the problem, in most Android devices shipped, Chrome and Android System Webview are defaults and so most of those people are already affected by this FLOC BS.
The best browser just keeps getting better!
While other browsers are on a downward spiral and are losing users and market share at an alarming rate, this browser is at an upward spiral.
God bless Microsoft!
Microsoft is also testing Reverse Image Search in the Bing sidebar:
https://www.reddit.com/r/MicrosoftEdge/comments/n3q7up/reverse_image_search_in_bing_sidebar/?utm_source=share&utm_medium=web2x&context=3
“Now You: do you use extensions or browser features that upgrade HTTP connections?”
Yes, Brave uses HTTPS Everywhere as a built-in component.
FYI, HTTPS Everywhere is being phased out by the EFF. Soon it’ll be using DDG’s algorithm, and shortly afterwards it’ll be retired. Brave are already considering what to replace the built-in extension with in future.
@Shintoplasm
I don’t want to compare Firefox and Brave right now but maybe Brave can eventually use dom.security.httpsonlymode from Firefox. Right now in Firefox, its kinda rough, if Brave can perfect it(read – show no warning on http sites but upgrade every http request to https if possible including css, frame, script than blocking them which is the current approach in Brave) then it wouln’t need any built-in extension.
And yes I’m aware that Brave uses Chromium but its a possibility.
@ShintoPlasm
Yes, I’m aware of that, thanks though.
@Yash
One of the approaches Brave’s team is considering is to stop using lists all together, which could possibly mean a similar option to Firefox’s HTTPS-only mode.
More information is to follow:
https://github.com/brave/brave-browser/issues/14442
Sorry for the off topic question.
Has anyone used adguard windows? Is it better to use an extension like ublock or trust adguard windows?
Yeah, it’s awesome. We use the system level (standalone) version, cheap multiple lifetime licenses, on all of our devices.
What’s detailed here is browser behavior, only concerns whether your browser allows loading http versions of sites if there’s no https version. AdGuard’s primarily an ad blocker/anti-tracker although it does other things, too. Essential to make phones bearable, IMO.
There’s a browser extension and a standalone program for computers and phones. The extension is similar to ublock; the standalone adds the ability to filter anything installed on a device, including in-app ads on phones (yay!) The extension, as expected, is slower than the standalone.
The standalone’s sold in the store here and goes on sale frequently.
Adguard is very good, though I prefer to turn it off for Browsers as I prefer uBlock Origin in Browsers.