Known Issue Rollback is Microsoft's latest weapon against Windows update bugs
Known Issue Rollback is a fairly new capability of Microsoft's Windows 10 operating system that is designed as a tool to react to emerging bugs quickly that are introduced by updates.
There is always a chance that issues are introduced when regular updates or feature updates for Windows are installed. Some updates introduce major issues, such as boot problems or data loss, while others may introduce less serious issues. Most issues affect only part of the entire Windows population, and some needed to be throttled, stopped, or even pulled by Microsoft to fix issues.
Up until now, it was required to install another update to resolve a issue, or to uninstall the update that introduced it. Microsoft publishes workarounds for some issues, but not for all, and not directly after discovery, usually.
Known Issue Rollback was designed as a fast less disruptive alternative. Microsoft notes that about 80% of all fixes for Windows 10 version 2004 or later include Known Issue Rollback functionality already. The feature is only used with non-security fixes. Microsoft explains that updates retain the code when Known Issue Rollback is being used, and since it is "typically more vulnerable or exploitable", the feature is not used with security fixes currently.
Microsoft describes the purpose of Known Issue Rollback in the following way:
Known Issue Rollback is an important Windows servicing improvement to support non-security bug fixes, enabling us to quickly revert a single, targeted fix to a previously released behavior if a critical regression is discovered.
The main idea is simple: assign IDs to individual fixes and updates, and disable these if they are known to cause issues. A single Windows update may contain several bug fixes, and some or all of them may support Known Issue Rollback.
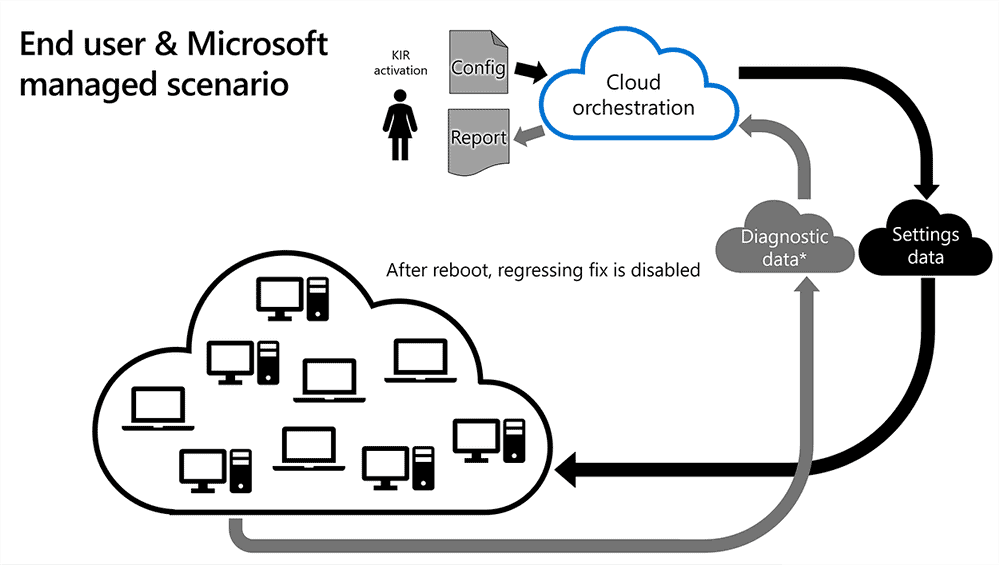
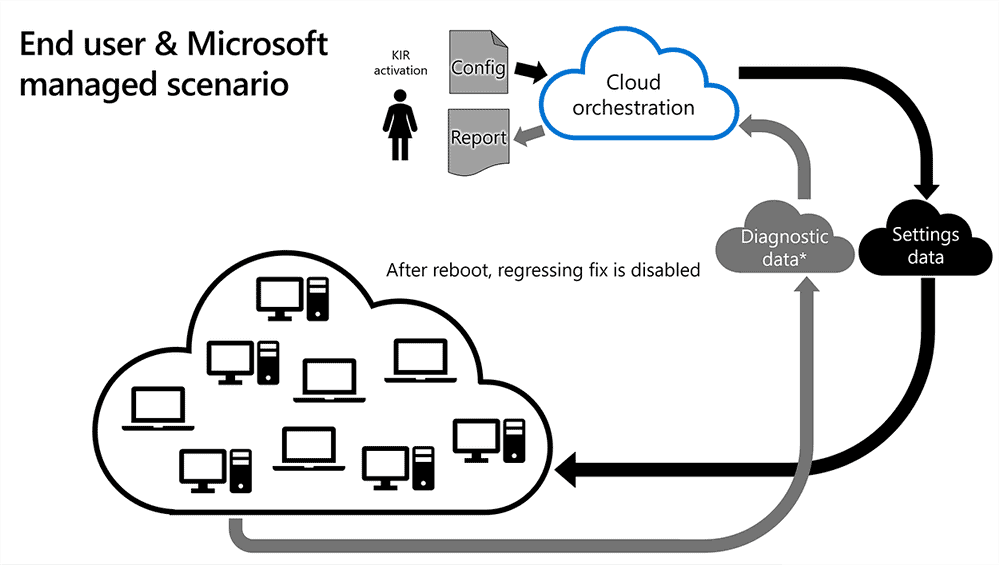
Microsoft uses Windows Update or Windows Update for Business for that, and informs the service running on Windows devices about a rollback. The change is applied automatically on the user side and live after the next restart, all without uninstalling an update or installing a patch.
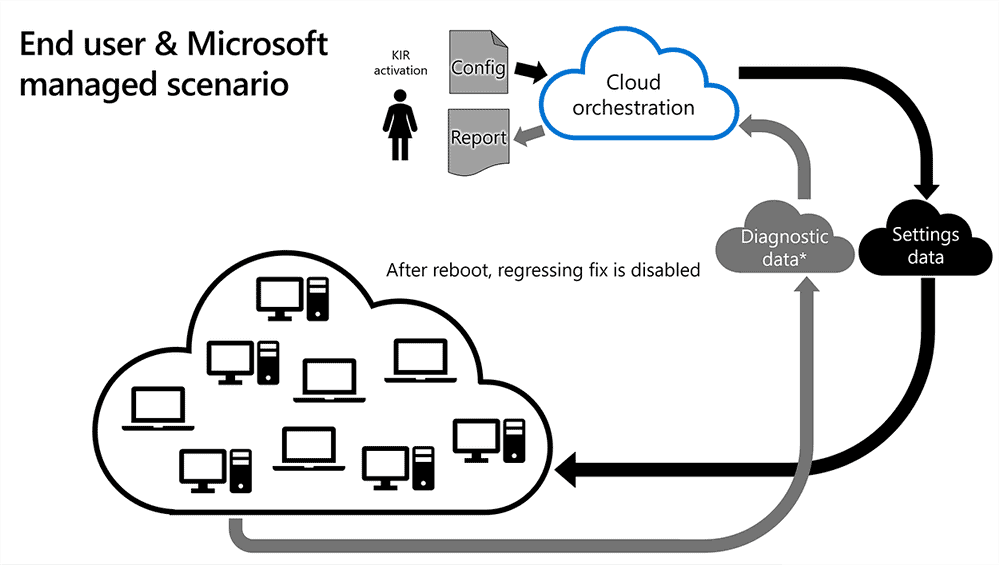
Some rollbacks are released before updates reach all user devices. While the patch in question will still be installed, the part of it that is causing the issue is disabled and therefore not causing the issue on the device.
Rollback scenarios change for Enterprise devices. Microsoft issues specific Group Policy on the Download Center for a rollback, and system administrators may configure and apply a policy to get the code rolled back on managed devices.
Known Issue Rollback configurations have a limited lifespan, usually a few months at the most, according to Microsoft. Most issues get fixed in the time period, and when that happens, the fix is re-issued.
Closing Words
Known Issue Rollback may prevent bugs on the majority of Windows devices, if Microsoft reacts quickly and uses a rollback before a particular update is installed on the majority of devices. In an example given, Microsoft states that it reacted to an issue after an update was installed on 170,000 devices, and that the use of Known Issue Rollback blocked the issue from appearing on hundreds of million devices.
Windows users who want to remain in control may disable or delay the installation of Windows Updates, but they have done so already, likely.
Now You: what is your opinion on this? (via Deskmodder)

















Does this also apply to companies that downloads updates from WSUS to CM and then release ?
So if i never installed the update (had pause updates on) is it now safe to install the update?
>libs included are bleeding edge (unstable alpha code)
you have no idea what you are talking about at all and its super cringe. rolling distros don’t grab the git master branch and compile it, the developers for each package you install have their own versioning and iirc the only way to get their development branches would be to compile it yourself manually. If you install a package from the official repos, you get the latest stable RELEASE build, and that’s determined by the developers of the software, not the maintainers of the repos (outside of them compiling the packages and putting them in the repos).
Known Issue Rollback (KIR) does not apply or does not seem to work if a 2004/20H2/21H1 update is manually installed from MS catalog though. KIR only works if an update is installed either thru WSUS or windows update.
> Once or twice a year I do a completely new install
I used to suffer from this affliction myself, then I discovered Linux and rolling releases. Imagine doing one install and never doing a clean install again. Windows is garbage. Always has been and always will be.
> and lock everything down using simplewall.
Except you have no proof you are “locking” everything down. The Operating System itself is proprietary, you cannot audit the source and you cannot create reproducible builds!
> Windows is garbage. Always has been and always will be. <
Garbage huh? Yet Windows OS currently has a worldwide market share of around 76%, while Linux is less than 2%.
And Windows is used in the vast majority of businesses / ofiices and hospitals etc, around the world – Wndows is the main driver of business and commerce, as well as home PC use.
Linux on desktops and laptops is basically for the geeks among us who dont mind spending their time on forums trying to find the latest workaround, or fix, or driver, for the teeming multitude of Linux variants out there.
Must try harder! ;-)
Because windows is for the normie stupid ppl, which is the majority of the world, and linux is for the uber leet smart dudes.
No point feeding the trolls, Ron. :)
>then I discovered Linux and rolling releases
Rolling releases are not what you think they are, You probably mean Arch Linux and in case you dont know, all libs included are bleeding edge (unstable alpha code), which makes this far more unpredictable for running some basic softwares and devices, often resulting in delving under the bonnet or recompiling packages because the whole dependency system on Linux is baked in. This requires skills that most users who just found Linux dont have and most are too lazy to learn as it involves reading documentation.
Overall, not a good switch cosidering, also if you know what you’re doing with Windows, you never have to reinstall either, the trick lies in delay feature upgrades for a full 365 days and make backups of system with independent software (disabling Windows native recovery) and knowing not to install all manners of software trash.
TL;DR; Out of the frying pan into the fire as its said.
You beat me to it. This “feature” means they can silently tinker with your system.
Wow, you guys really don’t care about demonstrating publicly just how idiotic and clueless you are, do you? Amazing!
Well you are right, could be an entry point for supply chain attacks even. No surprise if this nifty tool is one huge CVE palooza, considering the poor quality of coding by M$ to begin with, and knowing the possibility, and doubting any security audit of the code has taken place, because indeed, its more important to appear to care about bad coding and practices by releasing this utter waste of bits, then it is to spend the time on something useful like fixing the dammed issues.
Once or twice a year I do a completely new install and lock everything down using simplewall.
Occasionally Windows still connects somehow (Microsoft Rewards has recently been “rewarded” to me), but that’s about my opinion on updates and diagnostics, whichever company.
Yes, but unlike you, not everybody pirates an Enterprise edition of Windows.
Some people buy a computer with Windows already installed, to be able to just plug it and use it.
Although more in-house testing is required, no amount of automated testing in a lab can ever possibly replicate the gazillion unique setups and environments encountered in the wild. So this is a welcome feature to reduce disruption and disable only those specific parts of the updates that are causing issues for some.
It worked out fine for Windows 7 with gazillion unique setups and environments. Never had such issues then. Windows 10 is just purely trash with no QA.
So Win7 had ZERO updates that caused issues for certain sets of users? Stop lying, ok? Pathetic.
Please, Microsoft, just release better quality updates instead! :(
@John G
Exactly, if the issues are known, fix them instead of this half baked attempt at then catching some percentage of updates/upgrades due to them being buggy from inception.
What drugs are you kids on these days I wonder.
* [Editor: removed] The issues with the fixes are obviously not known in advance, or else it means they’re deliberately releasing known bad updates which is clearly not the case. The KIR feature is simply a fallback nature to quickly disable only the defective part of an update and leave the remaining working patches alone. Got it now?
This is quite scary. Microsoft can disable or remove anything from your computer remotely. This is why I still use Windows 7 with all telemetry updates removed.
How about, you know, reinstating robust QA processes instead of relying on automation and telemetry?
Convoluted nonsense. LTSC has none of those issues, nor it needs any workaround to just work.
More Yuliya lies. Now apparently updates for LTSC never cause ANY issues for ANY users at all. Lol!