LastPass introduces Account Recovery on Mobile
LastPass launched a new feature in the mobile versions of the password manager LastPass today that allows customers to recover their account under certain circumstances.
Password managers help users when it comes to password use on the Internet. They provide users with tools to create and use unique passwords everywhere. The database is usually protected by a master password that the user needs to enter to decrypt the password database and access stored passwords and other information.
Password managers may support other authentication options. KeePass, a popular free password manager supports key files or Windows user accounts.
Users who forget the master password are in a precarious situation as it is the only option to unlock the database unless recovery options are available.
LastPass Mobile Account Recovery
LastPass launched a new feature called LastPass Mobile Account Recovery today that introduces an option to recovery a LastPass account in case the master password is not accepted anymore by the service.
The feature is only available in the mobile LastPass applications for Android and iOS. Mobile account recovery requires a mobile device with fingerprint or Face ID authentication support.
Basically, what it does is unlock an option to recover a LastPass account using the authentication method. While LastPass makes no mention how the feature works, it appears that it links biometric authentication to the LastPass account so that users of the service may reset the master password using it.
It should be clear that LastPass users need to configure the feature before it becomes available.
The company notes that the account recovery feature is device-specific. If you want it to be available on all devices, you need to enable it on all of them.
If you are using LastPass on an Android device, you need to configure fingerprint authentication first; if you use it on an iOS device, you need to set up Face ID instead.
Setup is identical afterwards: sign in to the LastPass application on the mobile device. LastPass should display a notification about the new account recovery option; if it does not, go to Menu > Settings > Security and enable the unlock feature (called Use Fingerprint to Unlock on Android, and Use Face ID on iOS), and toggle the account recovery feature afterward.
Here is a video by LastPass that demonstrates the feature.
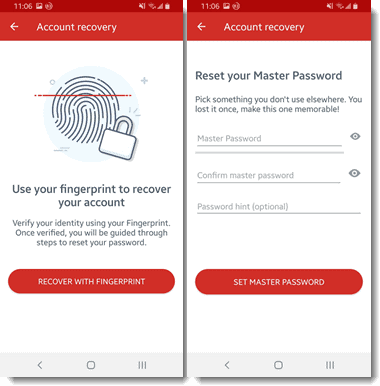
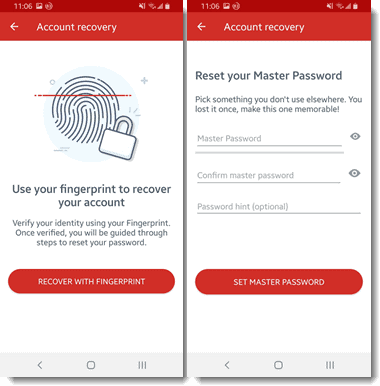
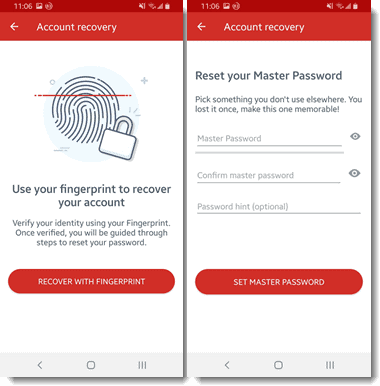
If you need to reset your LastPass master password, select "forgot password" when you get to the login screen. From there, select "Recovery with Fingerprint" or "Recovery with Face ID" and authenticate using the biometric authentication option.
LastPass will prompt you for a new master password that you may enter directly. You may also add a password hint. The selection of "set master password" completes the process.
Closing Words
LastPass recommends that customers enable the new account recovery option on their mobile devices even if they only use the desktop version of the password manager.
The new option is certainly helpful in restoring an account if the master password cannot be remembered; users should take note, however, that it could also open up a new option for third-parties to gain unauthorized access to the account through coercion.
Cautious users might want to stick to using the password hint option as the only resort when it comes to account recovery.
Now You: What is your take on the new account recovery option?




















Can we trust iPhone/Android systems for not leaking, having backdoor or being crackable so that someone could access the biometrics info saved in the phone and the access Lastpass (and more)?
@Clairvaux
Actually smartphones hold other more valuable information in the most cases already. The ability of locally secured recovery is so great because it actually increases security in practice. You are the only one in control, but you are in control no matter whether you forget your password.
Some time ago I found an iPhone, and because it wasn’t completely locked I saw all the incoming messages and could make calls, which made it very easy for me to contact the owner. A security and privacy conscious person would have probably made the entire phone inaccessible.
Every password recovery that relies on a smartphone is extremely secure in practice – the quality of security is limited by how the person secures the phone itself, or by the phone quality.
For example, if the smartphone itself is secured by a safe password, or biometrics (as in iphones), it is already unbreakable in practice.
Everyone in fear of law enforcement obviously choses other solutions, but this is nothing the majority cares about.
When it comes to the security of the fingerprint on modern iPhones, someone would require an exceptional quality copy of the fingerprint, and that is extremely difficult to get. So we are talking about a direct, sophisticated attack which always implies that the attacker wants to get something that is worth the risk of breaking in.
Don’t forget that in case of noticing a attack, the owner just needs to quickly access his masterpassword to reset the masterpassword itself, which renders the entire attack unusable.
In the case of being vulnerable to direct targeted attacks it is usually self-explanatory to seek more secure solutions, although if you are a target on that level and the attacker isn’t able to get hold of your information, you might simply get kidnapped.
@user17843: “A security and privacy conscious person would have probably made the entire phone inaccessible.”
I do this.
However, the lock screen on my phone provides my email address, specifically to allow someone a way to contact me in case I lose it.
But, if I’ve lost it, I probably already know where it is because of the “find my phone” autoresponder I run. It lets me text a code phrase to the phone, and the phone will reply with GPS coordinates and a picture from both the front and rear cameras. (And yes, a different code phrase will erase all data on the phone).
@ user17843
Actually, my reading on the dubious value of fingerprints for security probably relates to Android, since that’s what I use. I wasn’t aware there was a radical difference between both systems in that respect.
However, the problem of one’s actual fingerprints, in the XIXth century, Bertillon sense, remains. They are all over your phone, and there have been successful proof-of-concept experiments replicating greasy fingerprints and turning them into digital ones.
Granted, unless you’re a company exec with valuable industrial secrets, a high-viz journalist with secrets of interest to a government, a politician with powerful enemies, or a downright spy, there’s little chance such an attack will be conducted against you. For the time being. With the current state of tech.
When you say that the owner just needs to quickly access his masterpassword to reset the masterpassword itself, does it relate to Last Pass specifically, or is it a general remark ?
It’s quite possible that a whole day might go by before you noticing that you lost your phone — more than enough for a thief to attack an unprotected device.
Also, yes, you need to protect your phones with passwords, and that’s extremely inconvenient. Any security procedure involving my phone (say, 2FA) adds 2 passwords to anything. Username + password on the desktop + phone password + phone PIN (that’s a password by another name) + check your fingerprint on the phone (I didn’t count this one) + finally enter your blasted 2FA code. That’s 6 freaking identification steps to access a single site. Plus the delay to start the phone.
And yes, I’m an exception, because the default state of my phone is off.
That’s why we won’t have real security before hardware USB keys with FIDO and one-factor login become standard with websites.
A feature requested by Law Enforcement?
Since courts have recently decided that Biometrics are not Protected in the United States…
When I hear the word “recovery” associated with a security program, I reach for my revolver.
Especially on a smartphone, which is more vulnerable than a desktop.
Especially if the recovery is done through biometrics. All serious advice I’ve read about biometrics on a phone is that you shouldn’t rely on them alone to replace passwords.
Also, your fingerprints are all over your smartphone. If someone really wants to target you specifically, and he gets hold of your phone, then he’s a child in a candy store. Of course, this is rather for high-value targets. But that race to convenience…
To be fair, it is opt in. It also has some good intentions, but not for us. I would rather have them use spaced repetition with Master Password reminders where it forces you to enter it.
Basically, password reuse is a bigger issue, so the more people who use it the better. But, if novice users switch to it and forget the master password, then they can’t access anything at all. So, they can enable it and I guess later disable it once they are sure they can remember the password.
I quit using LastPass when I realized that the extensions for Firefox, Chrome, and Edge were causing the browsers to slow down the longer they were left open.
I moved my entire password database to Bitwarden and haven’t looked back.
If you want to test this for yourself just go into your addons/extensions and disable Lastpass then use your browser for a while. It’s a pretty night and day experience which bothers me because I’ve always loved Lastpass.
Nice.
I recommended LastPass to a friend who was always losing all of his passwords.
Basically he had all passwords either written down somewhere, or only stored in his memory. So when it turned it he had forgotten a password, he often tried to reset it.
But that meant he had to access his email-address, and unfortunately most of the time he had also forgotten the email-address password. That in turn involved telephone calls with the mail service. So he was resetting passwords all the time, and also used insecure short passwords.
At one point, he forgot his Phone passphrase, and due to being so fearful, he had chosen total encryption, so it couldn’t be reset.
He also thought saving passwords in his browser is dangerous, so it was all a big mess.
Nevertheless, he’s using LastPass now and it seems everything is working great. This account recovery is certainly an excellent idea for users who tend to lose their masterpasswords.