Microsoft updates Security Baseline: drops password expiration
Microsoft published a draft of the security baseline for Windows 10 version 1903, the May 2019 Update, and Windows Server 2019 (v1903).
While you can download the draft and go through it word by word, you may also head over to the Microsoft Security Guidance blog if you are just interested in the things that changed when compared to security baselines for previous versions of Windows.
The blog post highlights eight changes in particular, and at least one may make the life of computer users more convenient. Microsoft dropped password expiration policies that require frequent password changes from the security baselines for Windows 10 version 1903 and Windows Server 1903.
I worked in IT support for a large German financial organization more than 15 years ago. Security policies were set to very high standards and one of the most painful policies was the enforcement of regular password changes. I cannot remember the exact interval but it happened multiple times a year and rules dictated that you had to pick a secure password, could not re-use any of the parts of the existing password, and had to follow certain guidelines in regards to password selection.
This resulted in many support requests by employees who could not remember their passwords, and others writing their new passwords down because they could not remember them.
Microsoft explains the reason behind the dropping of the password expiration policies in the blog post. Microsoft mentions the same issues that I had when I worked in IT:
When humans pick their own passwords, too often they are easy to guess or predict. When humans are assigned or forced to create passwords that are hard to remember, too often they’ll write them down where others can see them. When humans are forced to change their passwords, too often they’ll make a small and predictable alteration to their existing passwords, and/or forget their new passwords.
Microsoft notes that password expiration policies help against a single scenario only: when passwords get compromised. If a password does not get compromised, there is no need to change passwords regularly.
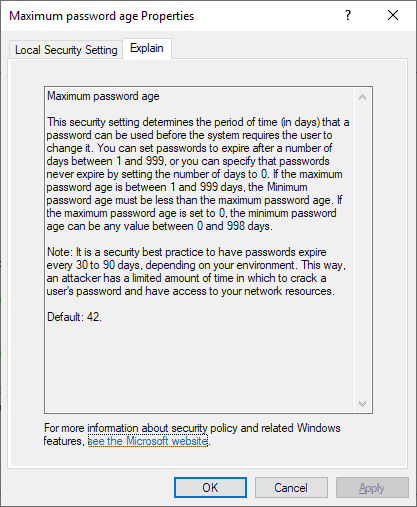
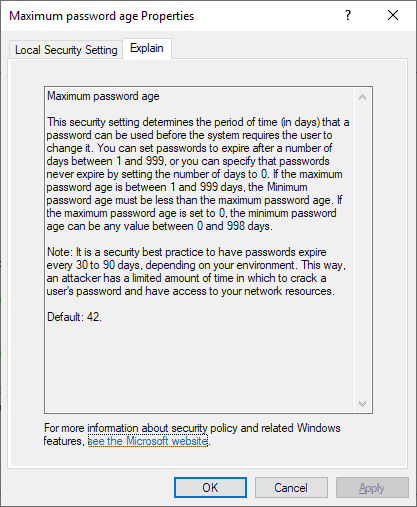
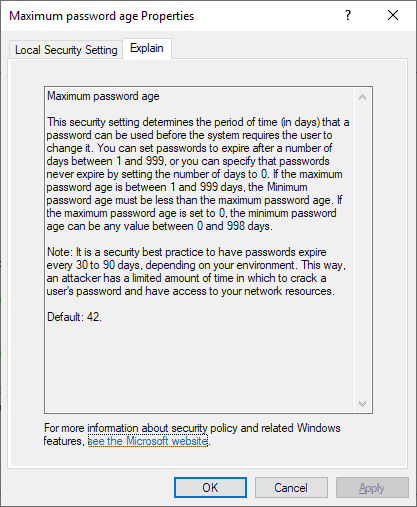
The default time period for the expiration of passwords was set to 60 days, and the Windows default is 42 days. It was 90 days in earlier baselines; that is a long time and not very effective either as a compromised password may not be changed for several weeks or even months so that an attacker may use it for that period.
Periodic password expiration is an ancient and obsolete mitigation of very low value, and we don’t believe it’s worthwhile for our baseline to enforce any specific value.
Microsoft notes that other security practices improve security significantly even though they are not in the baseline. Two-factor authentication, the monitoring of unusual login activity, or enforcing a blacklist of passwords are mentioned by Microsoft explicitly.
Other changes that are noteworthy:
- Dropping the enforced disabling of the built-in Windows administrator and Guest account.
- Dropping of specific BitLocker drive encryption methods and cipher strength settings.
- Disabling multicast name resolution.
- Configuring "Let Windows apps activate with voice while the system is locked".
- Enabling the "Enable svchost.exe mitigation options" policy.
- Dropping File Explorer "Turn off Data Execution Prevention for Explorer" and "Turn off heap termination on corruption".
- Restricting the NetBT NodeType to P-node, disallowing the use of broadcast to register or resolve names, also to mitigate server spoofing threats.
- Adding recommended auditing settings for Kerberos authentication service.
Now You: What is your take on password expiration policies?


















M$’s 42-days password expiration security policy imposed on the enterprises and their employees is like “throwing the baby out with the bath water” where the thrown-away baby is the employees’ secure and strong password. This foolish constant-changing-of-password policy by M$ resulted in many employees using weaker passwords that are more easily cracked by hackers.
This reversal of a long-held security policy proves that M$ is as dumb as a Donkey.
This foolish constant-changing-of-password policy is similar to M$’s 6-monthly forced auto-upgrade policy for Win 10.
.
Home-users should keep a written record of all their passwords and PINs, and store it safely and secretly because human memory can fail after a passage of time.
……. If a website has been compromised and log-in passwords have been stolen, then the home-users should change their password. They should beware of phishing attacks and online banking/shopping malware that steal log-in passwords or credit/debit card details.
Microsoft changed minimum storage requirement for 32&64 bit from 16GB/20GB to 32GB.
I think this is a good move, assuming that people do at least one thing — stop using the same password for multiple things.
Part of the issue os that if you make people change passwords regularly – especially across multiple systems, people will use a generic password across them all and will just change the digit when expiry time rolls around.
they will not, and changing the password will not help.
What also doesn’t help is that Microsoft does not allow passwords longer than 16 chars on their own site, which is really annoying as I cannot write memorable pass phrases because of that and have to fall back to randomly generated string.
By the way, trying to annoy users more will not result in them becoming more responsible, instead they will find more ways to work around the system. That’s why both Apple and Android develop creative methods to lock the devices (it’s where security matters) without passwords (because it’s not possible with passwords generally, passwords only work when the user is in the know).
@LogicDaemon: “trying to annoy users more will not result in them becoming more responsible, instead they will find more ways to work around the system.”
I agree, and that’s why I think dropping mandatory password expiration is a good move. It annoys users less and, considering the workarounds that users used in the face of password expiration, increases security at least a little.