Tor on Linux/Mac may leak IP (update available)
Tor users who use the Tor browser on Linux or Mac OS X devices may want to update the program to version 7.0.9 as soon as possible to plug a potential IP leak in the client software.
Tor browser is a cross-platform browser based on Firefox code that integrates the anonymization network Tor in the browser. The browser features several privacy and security related tweaks, some of which are or have been integrated in Firefox recently as well (for instance Canvas use notifications).
Tor Browser users who use Mac or Linux on devices can download the new browser version from the official Tor Project website. Please note that version 7.0.9 has been released only for those operating systems; the Windows versions of Tor browser is still at version 7.0.8 as it is not affected by the potential IP leak issue.
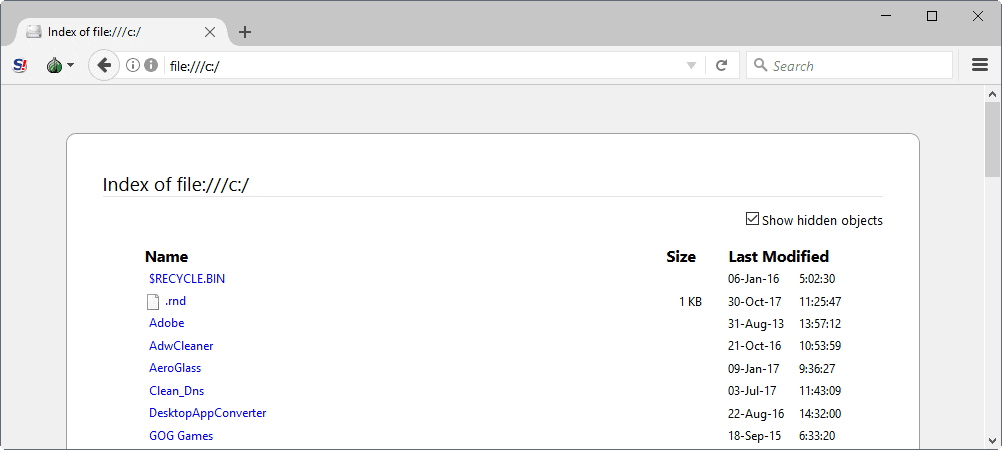
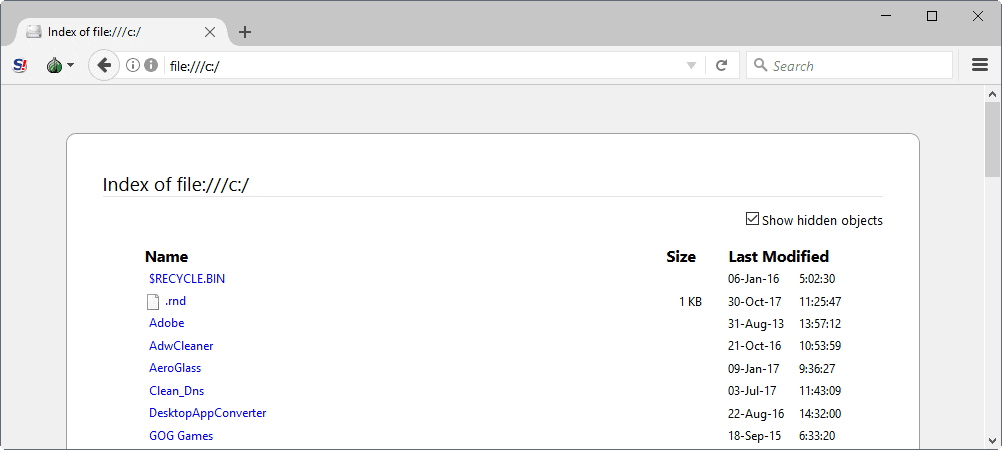
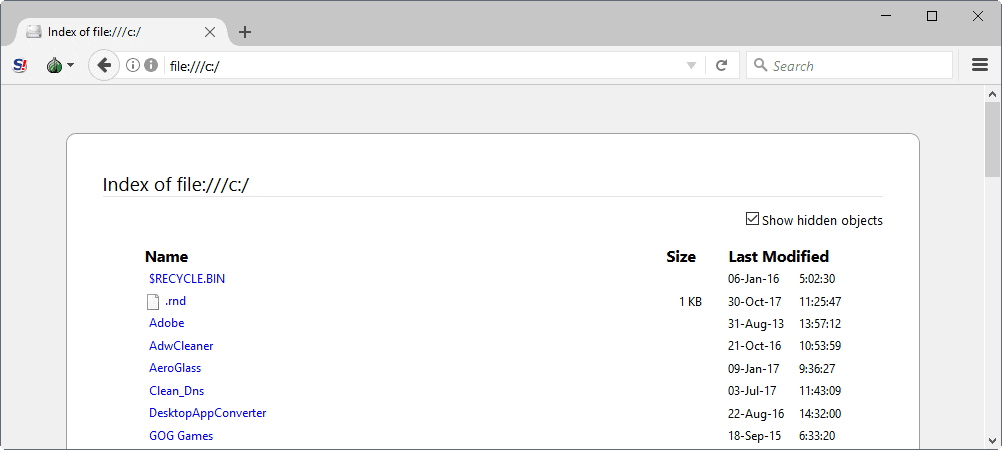
A new blog post on the official Tor Project blog reveals information about the issue. The issue is caused by a bug in Firefox's handling of file:// URLs according to the announcement.
This release features an important security update to Tor Browser for macOS and Linux users. Due to a Firefox bug in handling file:// URLs it is possible on both systems that users leak their IP address. Once an affected user navigates to a specially crafted URL the operating system may directly connect to the remote host, bypassing Tor Browser
Users of Tails and users of the sandboxed Tor browser are not affected by the issue.
The fix may impact file:// URL functionality in the Tor browser. The Tor development team notes that "entering file:// URLs in the URL bar and clicking on resulting links is broken" does not work anymore after the update is installed, and that opening those in a "new tab or new window" does not work anymore either. Affected users can drag the link into the URL bar or on a tab instead as a workaround.
The development team tracks these regressions, and it seems likely that fixes will be released in a future version of the Tor browser to address those.




















@ Robert–One problem about the bad guys at NSA is that they are actually three or four or five levels higher than regular users because “The Onion Routing project, or TOR project, launched on 20 September 2002 was for and inherently by the Naval Research Laboratory.” The code for Onion Routing is open source; thus, there is always the possibility of a breach.
As Tor cannot encrypt the traffic between an exit node and the target server, any exit node is in a position to capture traffic passing through it that does not use end-to-end encryption. While this may not inherently breach the anonymity of the source, traffic intercepted in this way by self-selected third parties can expose information about the source in either or both of payload and protocol data.
Indeed, In September 2007, Dan Egerstad, a Swedish security consultant, revealed that he had intercepted usernames and passwords for e-mail accounts by operating and monitoring Tor exit nodes. Furthermore, Egerstad is circumspect about the possible subversion of Tor by intelligence agencies:
“If you actually look in to where these Tor nodes are hosted and how big they are, some of these nodes cost thousands of dollars each month just to host because they’re using lots of bandwidth, they’re heavy-duty servers and so on. Who would pay for this and be anonymous?”
Source: Wikipedia
If Tor is as secure and anonymous as people think, how was it so easy to bring down Silk Road? Born 2011; died 2013–and only because of some simple “off-duty research conducted by FBI tax agent.”
Tor Away
Linux users (and probably Mac and Windows users too) can update from within Tor if they already have an older version installed. Click on the onion icon on the top bar and then “Check For Tor Browser Update…â€
Tor will download and install the newest version automatically.
All of us who ethically use Tor thanks you for the update tip. The bad guys in the NSA are foiled again. Seems to be an endless battle!