GNU/Linux Security: A look at QubesOS
Using GNU/Linux is by default more secure than using Microsoft Windows, this is common knowledge; however just because you use GNU/Linux, does not mean that your system is secure, and that is why some distributions have been created in order to maximize security; such as QubesOS.
QubesOS is very different from your typical run of the mill distro, such as Ubuntu or even the more hardcore like Arch Linux and Gentoo. QubesOS runs multiple virtual machines linked together under a single user-interface, to form a container based / compartmentalized operating system.
The purpose of this, is hypothetically speaking if an adversary were to gain remote access into your machine, they would be bound to only having access to the compartment they broke into.
To give a real example: Let's say that you have two 'compartments' running, and you visit a website with malicious code injected into it with your Firefox browser from compartment1, all your banking information, photos of your children, and that surprise anniversary gift ideas text document list you've been working on for your wife; is hypothetically safe from those prying eyes, tucked away in compartment2.
QubesOS
QubesOS utilizes three different distributions simultaneously, Debian, Fedora, and one that some of you may not have knowledge of; Whonix.
Whonix is a GNU/Linux distribution that routes all Internet traffic through the TOR network for the purpose of privacy and anonymity.
The machine I used for this has the following specs:
- Intel Core i5-4210U
- 8GB DDR3
- SSD
- Running QubesOS installed to it's own partition, NOT LiveUSB or in a VM.
The Installation
I was unable to snap screenshots of the installation, so you will have to trust in my word that the installation of QubesOS was surprisingly straightforward and very easy to figure out. Granted, I've installed countless distributions in my life using both graphical environments and command line interfaces alike, but I would say that unless QubesOS is your first delve into the GNU/Linux world which I DO NOT RECOMMEND, you should be able to manage.
The installer gave the option for automatic installation as well as manual partitioning (which was what I opted to do), and was no different than setting up any other GNU/Linux operating system.
Something that is obvious for a distribution like this to include, but that I thought was worth mentioning, was that by default QubesOS opts to use DM-LUKS full disc encryption for the installation, meaning that your entire setup (minus the /boot partition) is encrypted; something I support highly and tend to do with my installs on any system anyways.
The installation did take considerably longer than most do, but given the complexity of the operating system, it was no surprise to me really; taking around 30-45 minutes before it was fully finished and I was able to reboot into the system.
Note: QubesOS is NOT recommended for Dual-Boot situations. Although it's possible, it does leave security holes, and therefore the QubesOS team does not recommend it.
Working within QubesOS
QubesOS when I first booted in, greeted me with a standard encryption lock screen with the Q logo. Nothing fancy, but no need for there to be really. After that I was taken to a post-installation setup screen where I was asked to check/uncheck boxes about how I wanted QubesOS to handle certain things such as USB devices.
I checked that I wanted them to be handled by a system called usb-sys; as I wanted to make sure that I was protected against physical attacks using USB devices, not just attacks from external sources; I do a large number of server related tasks, my personal banking, my Ghacks articles and my schoolwork all from one singular laptop, I'd rather have more security than less.
Once that was done, I was able to exit that screen and was then taken to the LightDM-GTK login screen (the typical Xfce login screen). Entering my password took me to my default desktop.
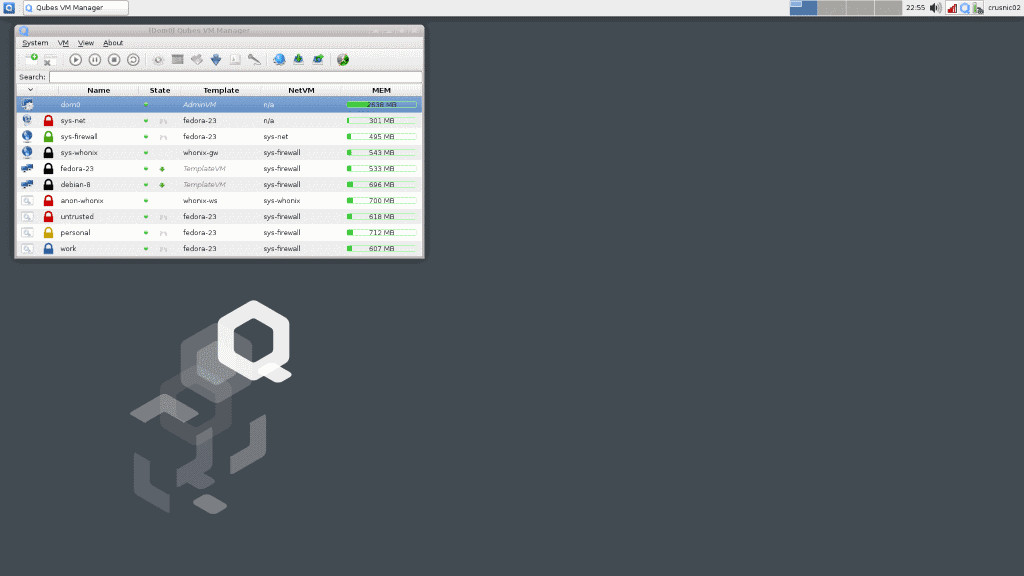
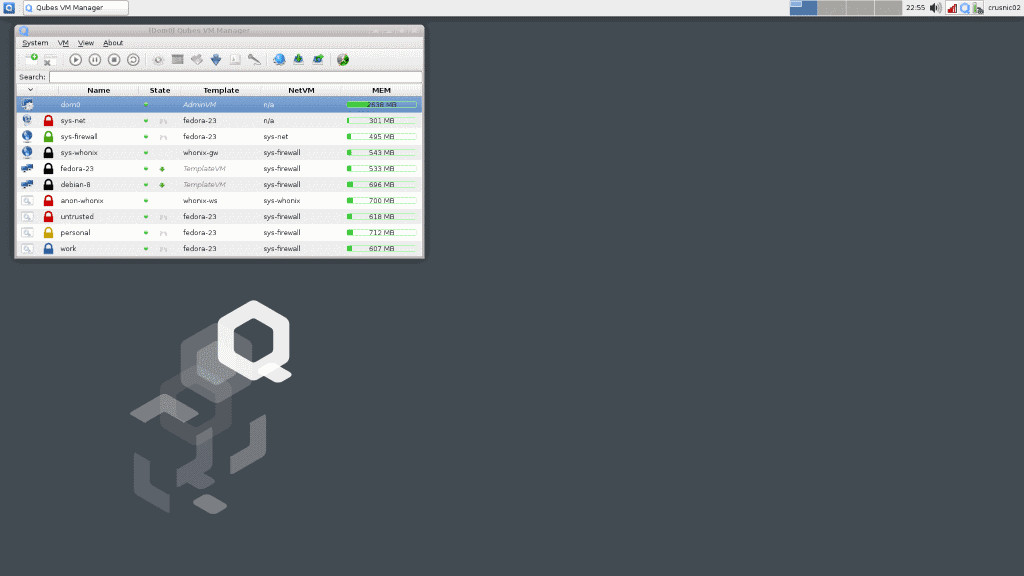
QubesOS uses Xfce as its Desktop Environment, and it suits it well, looking very professional and no frills, but pretty enough to look 'modern' if you will. The only thing I had on my screen by default besides my top panel, was what's called the “Qubes VM Manager,†which you can see in the screenshot above. This VM Manager, shows all the core details for all of the various virtual machines running, like memory usage. This is where you'll refer to if you need to reboot a VM for any reason, or which to make new ones.
During the installation, I opted to use the default VM setup, so I have quite a number of VM's running, however you might (and I might if I decide to use QubesOS long term) want to select less / customize your own for your own purposes.
The defaults are
- Disposable VM – A complete throwaway, where once the software you run is shut down, the VM is also destroyed until you make a new one.
- Anon-Whonix – A Whonix VM where all traffic is routed through the TOR network.
- Personal – Used for your own personal files and activities.
- Untrusted – Probably the VM you should be using anytime you aren't visiting a trusted website or downloading totally trusted files. This is where I'd imagine a user will do most of their web browsing.
- Vault – Probably where you want to be running applications or downloading files you definitely want to keep safe. Going to do online banking? Storing photos of your family? Do it here.
- Work – Self explanatory.
Now, some explanation is needed. Something to point out to you is that if you download a photo of a dog while using your web browser from the 'Personal' Qube, and then you enter your file manager from your 'Work' Qube, you will not find that dog photo.
It's a separate VM, you could almost think of it like having multiple computers themselves, all in your one screen. However, thankfully, you can transfer files between Qubes very easily by right clicking the files you want, and selecting either “Move to other AppVM†or “Copy to other AppVM†and then entering the name of the Qube you wish to transfer the file to, such as “Vault†or “Work.â€
Another thing to point out, is that on top of these “Domains†they are called by QubesOS, there are also menu items for “Templates.â€
The above Qubes, are all created from “Templates†of distribution such as Fedora, Debian or Whonix. All of mine were based off of Fedora or Whonix, although I did have a Debian-8 Jesse template as well. You do not install software into your “Domainsâ€, but rather into the “Templates†in QubesOS, and then the software becomes available into the “Domains.†A little confusing at first, but it became relatively straight forward fairly quickly as I messed around with it.
There is more to it, but this is the basis of QubesOS and how it functions. This overview is not meant as a full tutorial. If you have installed QubesOS and need documentation on how to do something, more information can be found on the QubesOS doc page.
Applications
QubesOS does come with the usual software, music players, photo management, file manager, Firefox web browser etc. However, I did note that it did not come with LibreOffice for example, and I had to install that myself.
By default, with the setup that I have described, all of my main VM's (Personal, Work etc) are using the Fedora Template system, and so in order to install LibreOffice, I had to go into my panel menu, access the Fedora-23 template, and install LibreOffice, and then restart the VM, and the associated VM's as well using the VM Manager. After that, I had LibreOffice available to me, and began working on this article.
It took me a little while to get used to the whole 'everything is compartmentalized and not accessible between Qubes by default' way of doing things, but after a few hours of installing things, poking and prodding around, I got the hang of it.
One thing on the topic of applications to point out, is that 3D gaming will not be happening on QubesOS, because OpenGL opens up many potential avenues for threats, as well as would need to have the QubesOS team drastically alter many aspects of the OS. So, if you're a gamer, QubesOS is not for you.
Final Thoughts
QubesOS is pretty advanced. I wouldn't recommend it if you're not quite comfortable and knowledgeable with GNU/Linux, package managers, and if you are not ready to give up the traditional way of looking at your Operating System. However, if you are serious about security, and you want to take the next step, QubesOS is a great way to do things.

















Thanks for covering this distro, Mike. Qubes is pretty intimidating to newbies like me, and it helps to have this kind of general intro.
It’s an interesting concept indeed, better than normally running another operating system with its own vulnerabilities and exploits available stacking on another system with another set of not-so-pretty stuff. I also like the supported hardware list, very useful. Sadly IT security still has a long way through, perhaps grsec going subscriptions-only will give some space to devs building properly written code, among many other things.
Unlike Tails Qubes can’t run on read-only devices loading everything to RAM, if I remember correctly? That was a good thing of the former, given the hardware is not “apparently” compromised and the image is trusted.
You’re right that it can’t load everything into RAM, which is useful in some cases. However, the Qubes OS website says, “Booting your computer from a live CD (or DVD) when you need to perform sensitive activities can certainly be more secure than simply using your main OS, but this method still preserves many of the risks of conventional OSes. For example, popular live OSes (such as Tails and other Linux distributions) are still monolithic in the sense that all software is still running in the same OS. This means, once again, that if your session is compromised, then all the data and activities performed within that same session are also potentially compromised.”
Which is a great point really. If you’re doing something short and sweet, TAILS and others are great! But the more you do, the more risk there is nonetheless.
Qubes OS is not a GNU/Linux distribution, if you want to call it a distribution then it’s a “Xen distribution” (Source: qubes-os.org official FAQ)
“If you really want to call it a distribution, then it’s more of a “Xen distribution†than a Linux one. But Qubes is much more than just Xen packaging. It has its own VM management infrastructure, with support for template VMs, centralized VM updating, etc. It also has a very unique GUI virtualization infrastructure.”
Taken directly word for word from the Qubes OS FAQ; which does not deny it as a Linux Distribution, but states that it’s not pure. ;)
> Taken directly word for word from the Qubes OS FAQ; which does not deny it as a Linux Distribution, but states that it’s not pure. ;)
It comes with Fedora for dom0 and that’s it, labeling it as a not-pure Linus distribution is misleading since it’s mainly based on Xen, whereas other OS use a monolithic kernel with all of its problems,
Second, all mainstream desktop OSes, such as Windows, Linux, BSD, even OSX, are all based on a monolithic kernels, which present a significant security problem. This is because a typical monolithic kernel of a contemporary desktop OS contains tens of millions of lines of code, and to make it worse, most of this code is reachable from (untrusted) applications via all sorts of APIs, making the attack surface on the kernel huge. And it requires just one successful kernel exploit to own the whole system, bypassing any security mechanisms that might have been built on top of it, such as SELinux, LXC, etc.
Additionally, all the various drivers, networking and USB stacks, are also hosted in the kernel, making attacks via buggy networking (e.g. via buggy 802.11 stacksor buggy firmware) or USB stacks a practical possibility. And there is essentially nothing one can do about it, when using an OS based on a monolithic kernel.
In Qubes, on the other hand, we use Xen hypervisor to provide security isolation between domains, and Xen is just a few hundred of thousands lines of code. It also doesn’t need to provide all sorts of APIs to applications, because the Xen hypervisor is essentially only interested in CPU scheduling, memory management and power management, and very few things beyond that. Most notably, the Xen hypervisor knows nothing about networking, disk storage, filesystems, USB stacks, etc, as all those tasks are delegated to (often untrusted) service VMs.
https://blog.invisiblethings.org/2012/09/12/how-is-qubes-os-different-from.html
The OS is called “Qubes”
“What is Qubes OS?
Qubes OS is a security-oriented operating system (OS).”
The website refers to it as both Qubes OS in many, many locations, but then also shortens it to Qubes in many as well. I figured for continuity sake, it was better to just refer to it with the full name.
Last time I checked, Qubes OS was very picky about what hardware it could run on. My motherboard is not supported.
Yeah, it has issues with nVidia as well, apparently.
One can pretty much have the same amount of protection by just installing a virtual machine into any distro and using that VM for “risky” stuff, like surfing the net, downloading, etc.
I recommend reading the section about Qubes OS vs regular VM’s, on their website. While granted, you’re right to a point, not all VM’s are made equal and secure.
https://www.qubes-os.org/intro/