Full Last Pass 4.1.42 exploit discovered
Tavis Ormandy, a prolific member of Google's Project Zero initiative, revealed that he discovered a new security issue in LastPass 4.1.42 (and maybe earlier).
Ormandy revealed that he discovered an exploit, but did not reveal it. Project Zero discoveries are reported to the companies who produce the affected products. The companies have 90 days to react, usually by creating a new product version that they make available publicly to all customers.
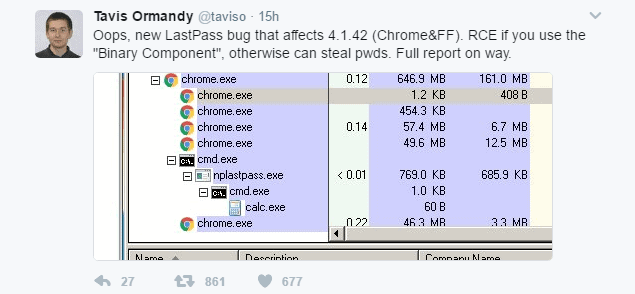
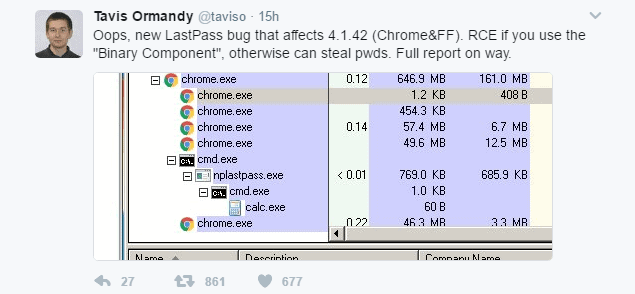
The information is scarce at this point in time, but it does paint a grim picture. On Twitter, he said the following:
Oops, new LastPass bug that affects 4.1.42 (Chrome&FF). RCE if you use the "Binary Component", otherwise can steal pwds. Full report on way.
He mentions the latest version of LastPass for Google Chrome and Firefox explicitly (version 4.1.42), and that the exploit can be used for remote code execution, or the stealing of passwords.
Later on he revealed that he has a full working exploit that works without any prompts on Windows, and is just two lines of code. Also, he noted that the exploit could also work on other platforms.
I have a full exploit working without any prompts on Windows, could be made to work on other platforms. Sent details to LastPass.
Full exploit is two lines of javascript. #sigh ¯\_(ツ)_/¯
LastPass posted a message on Twitter stating that it is aware of the reported issue, and that it is working on a solution, and has put a workaround in place.
We are aware of the report by @taviso and our team has put a workaround in place while we work on a resolution. Stay tuned for updates.
Soon thereafter, the company posted a second message that the reported issue was resolved.
The issue reported by Tavis Ormandy has been resolved. We will provide additional details on our blog soon.
According to the tweet, no user action is required at this point in time. Note: We will update the news article when the LastPass blog post goes live.
This new LastPass bug is not the first that Tavis Ormandy discovered. Ormandy discovered a remote compromise vulnerability in LastPass back in mid-2016.
In 2015, LastPass detected suspicious activity on the company network, and more recently, in 2017, issues were discovered in the password manager's mobile application for Android.
It is unclear how attackers may exploit the newly discovered security issue. LastPass customers who want to be on the safe side of things should consider disabling the password manager for the time being until the security issue is patched. Those who cannot do that should be very careful when it comes to the sites they visit on the Internet.
Update: LastPass has published its own security report on the issue. According to the company, no "sensitive user data was lost or compromised" to the company's knowledge. This means, that users don't need to change their master passwords, or any site credentials.
All extensions for browsers have been patched, and one issue was fixed on the server-side.
Now You: Do you use a password manager?

















I can never for the life of me understand why people insist on using a server based password manager.
I have used keepass x on linux for years with no issues and its all locally stored with no dependence on some server.
To all Keepass advocators: do you realize that if you are using any browser plugins you are in a much worse position security-wise to this types of attacks? Keepass “offline” security only works is you are (1) not using browser plugins and (2) don’t store you database online. Otherwise Lastpass is a better option for security because they have larger team responding to this threats and high bounties to attract researchers and motivate them to disclose vulnerabilities instead of selling them.
Also after Lastpass “reviewed and strengthened their code review and security processes†Tavis Ormandy discovered next critical vulnerability on march 27: https://blog.lastpass.com/2017/03/security-update-for-the-lastpass-extension.html/
The Kee Pass database is encrypted, so you can store safely it in the cloud if you really want to. You can even encrypt it a second time over, with VeraCrypt for instance, before uploading onto your cloud provider. Or, you could use a cloud provider with end-to-end encryption, such as Spider Oak, which does the encryption on your computer. Or, you could use a dedicated piece of software such as Box Cryptor, which stands between your files and your cloud service.
That being said, I don’t know how practical, or safe, Kee Pass is for sharing passwords between devices. I don’t do that. Synchronising passwords is a major benefit of online password managers.
I presume your warning against plug-ins is only meant for Kee Pass plug-ins creating a link between Kee Pass and the Internet, not for other browser plug-ins. Even if one does prevail oneself of a plug-in to enhance ease of use, the fact that the password database stays on your computer makes it a much smaller target that LastPass types of password vaults.
Keepass offline.
Lastpass services has deteriorated significantely after its acquisition. That’s why i am moving to Enpass password manager
Now to your question: No I don’t use an freaking password manager. I just use the notepad on the removable drive.
Who uses password manager?
I can’t comprehend how people are still using LastPass after it got hacked the first time. I guess some dumb people can’t even use their brain to remember a password. Shame and sad.
@AAA
Here is one of my passwords; “GLm b8q7# siEZd22PU 2bTp 7GtU^3b.” Please explain to me how any human mind could possibly remember it?
I assume some of your passwords are similar to “123456” or “password”
I memorized a single 32 character long password like this I used very single day no problem. Now I’d like to see AAA memorize 100+ passwords like this especially when some of them are gonna be used very rarely.
@mike its called muscle memory you would be surprised how many long passwords like that you can remember by muscle memory. If you take the short time it takes to learn over being lazy it will also improve your short term and long term memory.
Given that you’re not meant to re-use passwords, they’re meant to be long and complex and often have requirements per site (E.G. specific lengths, combinations of upper and lowercase, special characters etc), saying people are dumb is a bit dumb in itself.
By all means, use the same, easy to guess password on ALL sites… I know which is more dumb.
This is why I avoid such solutions.
The rule of thumb: more comfort less security. Sorry.
Nobody knows how many exploists have been found which are not published.
That can be said for anything. Just going online puts you at risk no matter what you use, or don’t use. As soon as connect you put your info in the trusty hands of all the programs you use from the OS, to browsers, to AV software. If all things were 100% safe and secure there would never be any security updates. Just because something wasn’t published doesn’t mean someone somewhere didn’t find a hole, and now has your stuff. We all hope the code is as bulletproof as can be, but since it was programmed by humans, there’s bound to be an exploit somewhere. If you want to stay as safe as possible stay off the web. ;-)
I had been an early adopter of LP and championed it when it first had a security breach in 2011. But when a second breach happened in 2015, I returned to using Keepass. Keepass can be set up to function like LP, you just have to use an extension to integrate with the browser; and a cloud sync program for various devices (SpiderOne, Dropbox, Onedrive).
As for LP, I deleted all of my passwords there when I migrated to Keepass.
…”Keepass can be set up to function like LP, you just have to use an extension to integrate with the browser”.
Interesting.
Can you share with us the name of the Browser addon/extension?
Is it for Firefox?,
Passifox is easy to set up for Firefox. Google and download KeePassHttp.plgx and install it in the Keepass directory. Install Passifox. Then pair Passifox with Keepass. A Pop-up will appear. Just give a name to the pairing. Save Keepass database to save the pairing, and you’re good to go. Or you need to re-pair them everytime you need to use Passifox.
Clairvaux is correct that the plugins/extensions are generally not vetted. I’ve been using Passifox for many years, maybe a decade even. I don’t think my Keepass database has been compromised in that time.
I use Kee Pass, and I’m reluctant to “enhance” it with the browser plug-ins that are indeed on offer. I presume Kee Pass to be relatively safe, since it has been written by a security specialist, has been in active development for a long time and is open source.
However, we don’t have the same visibility on Kee Pass plug-ins. They are not vetted by Kee Pass. We don’t know the developers, we don’t know how actively the plug-ins are updated, we don’t know whether white hats are looking for vulnerabilities in their code, and they do create an added link with the browser which probably extends the surface attack.
You can experiment with Kee Pass plug-ins here : http://keepass.info/plugins.html
This gives us the opportunity to suspend the Google-bashing for just a minute. Normal activity will resume afterwards, of course.
“The issue reported by Tavis Ormandy has been resolved. We will provide additional details on our blog soon.” “According to the tweet, no user action is required at this point in time. Note: We will update the news article when the LastPass blog post goes live.” Good to see it was quickly fixed before someone leaked the actual detailed way to exploit it.
Sorry to see another exploit here. I have been a LP user since they first came out and use it across all my devices. After they were acquired, it did make me have second thoughts and this certainly will introduce more concerns. I haven’t seen any issues with Dashlane, does anyone know if they are a safer choice? I dont like KeePass so that’s not an option.
I believe the next phase in online security needs to be integrated seamless reissuing of tokens and password resetting between third-party websites and tier-1 services such as LastPass and SSO providers (e.g. Google, Facebook).