LastPass Hacked: what this means for you
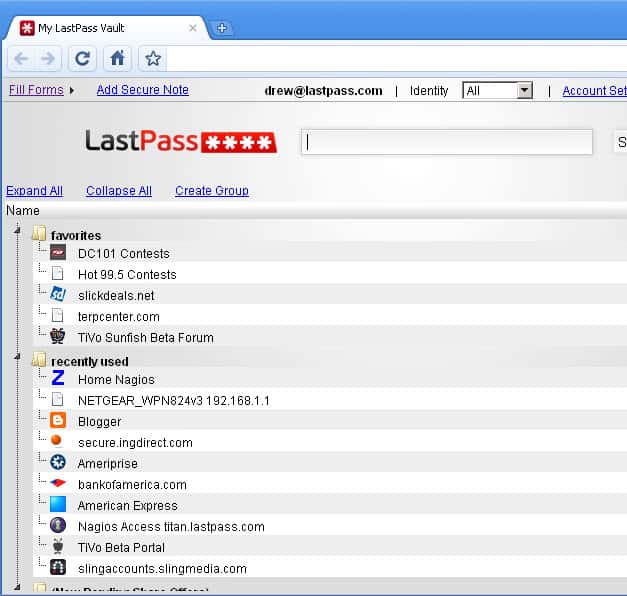
Online security company LastPass published an announcement yesterday on the official company blog that it detected and blocked suspicious activity on the company network.
According to the information posted on the blog, the company did not find evidence that LastPass user accounts were accessed or user vault data was downloaded. The company did not mention when it first noticed the breach but some users reported that they started to receive spam to email addresses used exclusively for the password manager account on June 8th.
LastPass' investigation confirmed that account email addresses, password reminders, server per user salts and authentication hashes were compromised.
The company, confident in the service's protective features, enabled additional security measures for the majority of accounts.
For instance, it requires all users to verify the account by email again if a new device or IP address is used to access the account. This is not the case for log ins on known devices or from known IP addresses, and also only the case if multi-factor authentication is not used.
In addition to that, users will receive prompts to update their master password.
The company is forthcoming with information. It sent emails to all users informing them about the security incident.
Since encrypted user data was not stolen, LastPass does not require users to change passwords for sites and services stored by the service in the cloud.
The information that were stolen may be used by the attackers to decrypt master passwords, especially if weak passwords were selected by users.
What you should do
Even though you may not receive prompts to change your master password, you may want to change it regardless of that. This can be done directly on the LastPass website for instance.
In addition, it is recommended to enable multifactor authentication for accounts to add a second layer of protection to them.
LastPass supports a variety of software and hardware based authentication options of which some are only available for premium users.
Once you enable the security feature, log ins require a second authentication step that is independent of the data stored by LastPass. For instance, you may use Google Authenticator, an application by Google, to create codes for the second login phase. Attackers would need access to your phone or mobile device Google Authenticator is running on to complete that step.
Apart from that, you need to make sure that you did not re-use your master password. If you did, it is recommended to change it immediately as well.
Last but not least, since attackers got hold of email addresses, you may receive spam emails or social engineering attacks that try to steal data from you directly.
Closing Words
The service suffered a breach back in 2011 as well which I was affected by. I made the decision back then to switch to the local password manager KeePass after changing hundreds of account passwords on the Internet.
Online password services are high profile targets for attackers as they store accounts for thousands or even millions of users.
Now You: Are you affected by the breach?
















I have been using Lastpass for about a year now (paid) and personally I like it. For me I weigh up the Risk / threat / vulnerability. I use 2 factor Authentication, super long master password, and check my logins everyday. Is Keepass more secure? If it’s set up right, of course. But everyone I know uses dropbox to sync the DB, so, for me, it’s a moot point. And for those people who never trust anything to the cloud, guess what, it’s too late. Medical records, personally identifiable information, SSN, Phone Numbers, mothers maiden name, bank accounts. They are all up there. You don’t have choice (unless you live completely of the grid). It’s about taking personal responsibility for your own information, knowing and understanding the risks, and making informed choices.
Keepass Portable. One copy on laptop, one on my tablet, one on a pendrive. Easily backed up by simple copying, along with the data file. Nothing in Cloud, as to me Cloud and security are a contradiction in terms – sooner or later you have to trust people you don’t know.
Almost all my passwords are long – the Keepass one is always 16 – 20 characters. I change the most important every few weeks, including the KeePass one. I don’t write that down, but I can recover it using the sentence-from-a-book method I use to generate it. Nothing is ever 100% infallible, and I suppose nothing will defeat a determined hacker – but I’ve yet to find a better method or application.
The only passwords I’ve had compromised to date (he says, touching wood frantically) were lost by online services who clearly thought they were far too clever to be vulnerable.
Was gonna change my LP Master PW but then I read that some who changed their LP Master PW couldn’t login or return to their previous Master PW. So I have not done anything about it.
I am not affected beacuse I never trusted cloud to store my sensitive things like password. ;)
One thing to bear in mind is that the thieves apparently got the password hints. If your password hint was such that it would give someone a real chance of guessing your password, you could be at risk. If your password was a strong one and your hint (if you left one at all) would be utterly meaningless to anyone else, you have little to worry about.
Can you port information from LastPass to KeyPass, within KeyPass?
Not sure, but you can import it to Sticky Password, they have oflfine solution and WiFi sync.
You can export LastPass vault contents to a clear .csv file on your system which makes its contents only as secure as your system is for the duration of its existence. KeyPass must be able to import that .csv file for you to be able to do this and with all this undeserved FUD about LastPass this week they would certainly be stupid not to permit that.
The white hats who have analyzed the situation give the probability of anyone decrypting a LastPass hashed master key to be not meaningfully above zero. With respect to that all important function the consensus is they did it right. All data encryption/decryption with your master key is done locally on your system. All they have and lost is a hash of your master key for the purpose of verification on your local system and that hash is considered by experts to be sufficiently hard that no one need worry (even if they don’t change it.)
my everyday passwords are vivid enough to be memorable so no need to look at a written reference every time. Less frequently used are also written down and referred to when needed. If a thief breaks in to your house they’re in and out in a minute or two, and they’ll lift the technology / valuables fast, but will they check every old book or magazine in a pile or on a shelf away from the computer area? it’s less likely to happen. Lists can be hidden in all sorts of places.
I keep my passwords in an encrypted text file under a red-herring name and extension so among all my other documents it looks like just one random fish swimming in a sea full of similar ones. Thanks to the VeraCrypt container method, this covering file’s NTFS date remains the same even when I update the password contents: meaning that should some intruder launch a quick search for all files that I used in the last few months, this innocent-looking “old” document file would not even come up.
My own (perhaps naive?) idea is that this might be safer than using any kind of password management software. For even if someone stole my computers, and even if they would be willing to try and break some seriously encrypted data, they still wouldn’t have a clue where to look for my passwords file in the first place.
I’ve chosen an offline approach for keeping my passwords secure and I think it was worth the effort and good decision. For years I’ve been keeping my passwords encrypted in the local database of Sticky Password (http://www.stickypassword.com) and if I want to sync, I use WiFi sync over my own secured WiFi. Thus I don’t care if they got hacked, I’m safe unless someone will guess my master password.
Frankly speaking I don’t understand this huge trust for all these cloud services. This is only a matter of time when any such service will be compromised or in any way cause the problem for users.
People are blind when they got something like that for free. Free cloud office, free store passes, etc. Somebody wise has said clearly “There is no such thing as a free lunch”. The server should be paid, salaries, energy, etc. So why some services are free? Marketing guys. First catch the customer then when he has no choice give him a high bill. Just remember what I have just said. You will see.
The second reason is usual people thinking: such server is safer then my own computer. It is a huge mistake. Attaker thinks about the target at the beginning on the level of advantages then difficulties. I know what I am talking about.
In another words, if any computer contains data of thousands people, more probably it will be attacked enough long to get the content then attacker will loose his time to fight with the firewall of the private computer with the data of one person.
So if you wanna be on the safe side, keep your sensitive data to yourself and never share them, no matter it is free or not. Remember also, you don’t know how such data are secured if they exist on the server xyz. It gives you the power to decide how to store them, how to secure them, how to back up them, etc.
Also you never know if your data stored in the cloud are safe or not.
And as I’ve said, I know what I am talking about.
If White House can be hacked, FED Employees Database can be hacked and alike, what is so big in the hacking of LastPass? Are our computers more secure than a professional company like LastPass? Just a contrarion view. Fortunately, KeyPass is not affected yet as they do not have any centralized system like Cloud etc. I am in a kind of fix if I should move to KeyPass. Is really KeyPass any safer? I’d appreciate your view as I also use far too many passwords to keep track of on my own.
It’s been two years since I closed my LP account, no more cloud for me since then.
My important data only leave the house with me, fully encrypted.
KeePass for anything important. Another older easy to use password manager for everything else.
Nothing in the cloud.
+1 Keepass is amazing and works great, though I do use dropbox to sync the db across computers and fone.
Mostly because you have to pay to use lastpass on your android fone. I tried using Lastpass, used it for a while but I couldn’t stand the lastpass extensions as they never seemed to work right and got in the way all the time when I try to log into a site. That and KeePass is easier imo to keep organized.
I couldn’t care less if my dropbox gets hacked, it’s only holding my keepass database file. The chances of someone hacking the password on my keepass is highly unlikely from what I seen and considering the length and complexity of it.
How is that any different than LastPass?
You have a locally encrypted password database (Keepass) uploaded and stored in the cloud (Dropbox).
Dropbox has also been hacked, multiple times: http://www.zdnet.com/article/dropbox-gets-hacked-again/
If they have info on how to decrypt the master passwords I don’t see how changing them will help?
Since they don’t have access to actual account data, they can only use the master password to sign in to accounts once they have decrypted them. At least that’s how I understand it.
From my understanding, password data was not compromised. It is only e-mail accounts & password reminders. Changing your master password is probably a good idea, but not really imperative.
I’ve come to rely upon LastPass, mainly out of convenience. I have far too many online passwords to keep track of without a manager, and I just haven’t found the time to move them all to KeePass (athough I do agree that a local password manager seems more secure). I don’t keep any banking or financial passwords in LP, however, as I don’t trust that it is truly invulnerable: for these, I use the old fashioned method of writing them down and changing them frequently. Still, if my LP account ever got compromised, I’d have a real problem on my hands.
We need devise a better system than passwords for verifying identity online.
“We need devise a better system than passwords for verifying identity online.”
Yeah, that’s kind of what Microsoft are planning to do with ‘Windows Hello’ and ‘Microsoft Passport’. You authenticate your local machine using biometrics/PIN combination, and then your machine authenticates you to websites.
Beyond their promotional video, details are still a bit scarce at the moment though, but certainly looks like one to keep an eye out for in the future and read up about when it gets closer to prime time.
https://www.youtube.com/watch?v=1AsoSnOmhvU
That’s a security risk however, as it allows a company (Microsoft in this case) to track you across multiple sites.
Few days back, one more indian company called “Gaana” was hacked by a hacker. He told that he is just noticing them to improve their security. Now hackers targets LastPass. “If you know something how to do it doesn’t mean you should do”. Hope they will recover soon.