Anti-Tracking extension Privacy Badger 2.0 is out
The Electronic Frontier Foundation released their anti-tracking extension Privacy Badger 2.0 for Firefox, Chrome and Opera yesterday.
The extension is designed to prevent online tracking which is fundamentally different from how ad blockers operate.
Instead of blocking scripts outright, Privacy Badger 2.0 will only block trackers. This means that ads may still be displayed, but that the extension puts an end to techniques that sites use to "follow" users around the web.
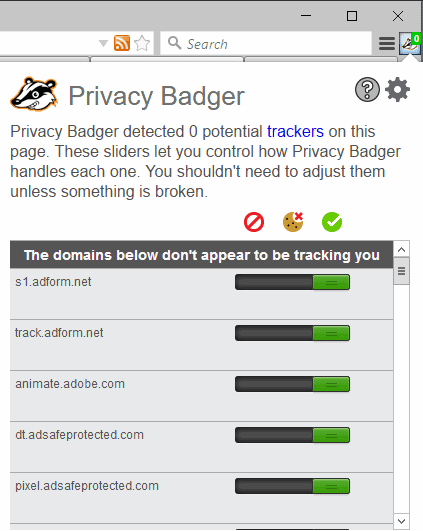
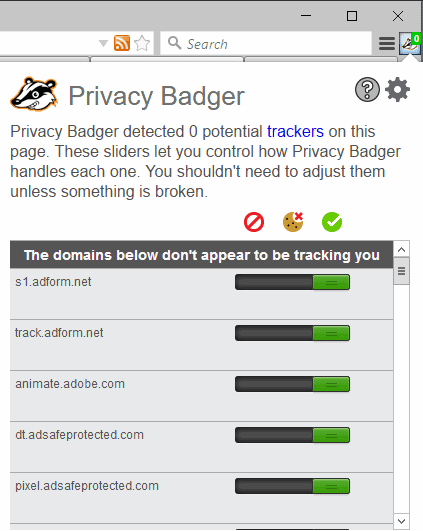
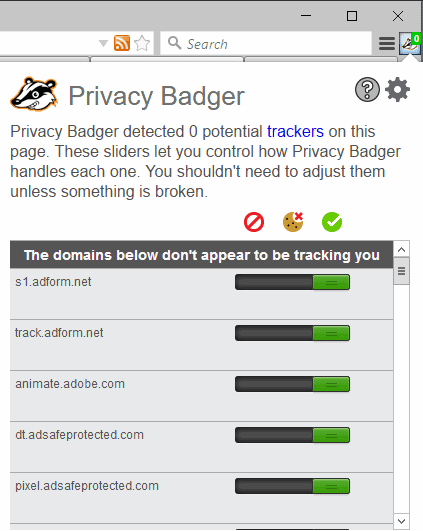
The add-on places an icon in the browser's main toolbar that you interact with. It highlights the number of trackers that it blocked on a site, and displays options to allow individual trackers, or block domains that the extension did not detect as trackers.
Privacy Badger 2.0
You are probably wondering how Privacy Badger 2.0 differs from the initial Privacy Badger released in 2014, and Privacy Badger 1.0 released in 2015.
To find out, we have to dig deep as the EFF's own press release does not shed details on that.
We have to look at the add-on stores to find out about the changes. Support for Firefox's multi-process architecture E10s is probably the biggest improvement over previous versions.
Mozilla is still rolling out the feature to devices running the stable version of the Firefox web browser. Compatibility means that you can run Privacy Badger 2.0 alongside multi-process Firefox without major issues.
Privacy Badger 2.0 may also be installed on Firefox Mobile for Android.
This goes hand in hand with Privacy Badger sharing a code base now.
Existing users of the extension may also notice performance improvements, the EFF refers to them as "huge", but mileage may vary. At least on my system, it is still not super fast.
But there is more. Privacy Badget 2.0 may block WebRTC from leaking local IP addresses. Please note that this feature appears to be only available in the Chrome / Opera version of Privacy Badget 2.0, and not in the Firefox version.
You find the option under "general settings" in the Privacy Badger options.
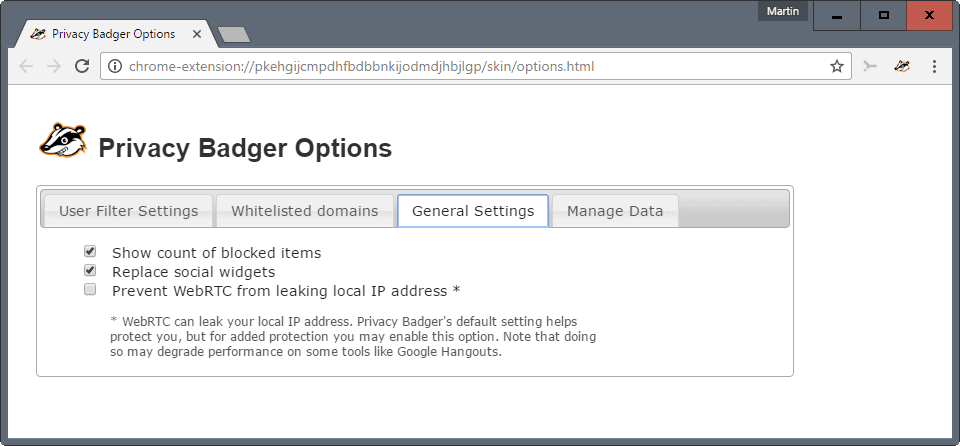
You find the new "manage data" option in the settings as well. This enables you to import or export user data that includes whitelisted domains and filter settings.
Privacy Badger 2.0 blocks so-called HTML5 pings as well in the new version, and will break fewer sites according to the EFF.
Last but not least, it will also forget data when private browsing mode or incognito mode are used by the user.
Firefox users reported that the extension breaks Google Docs for them, and there specifically Google Sheets.
Closing Words
Privacy Badger 2.0 is a major release, but it has its issues right now on Firefox. Google Sheets crashing, and WebRTC missing are just two of the reported issues right now that plague the Firefox version of the privacy add-on.
If you do use it on Firefox, you better wait until those issues are sorted out before you upgrade to the new version.




















With EFF Privacy Badger version 2018.2.5 at least on my latest version of win10 x64 Home and latest Chrome x64 beta, Privacy Badger works more strictly than prior versions in my experience. The failing site window will give no message indication of a problem, but some of the site may not be visible, or a function such as a mouse click may not work at all.
The stricter blocking problem can be circumvented by opening the problem URL in an incognito window which disables all extensions (unless you have expressly allowed the extension to run in incognito mode). Another way is to manage extensions manually by disabling Privacy Badger .
Probably the easiest, fastest, most granular way to make the problem URL work the way you want it to is to click on the Chrome Privacy Badger extension icon to disable Privacy Badger for the problem URL, or selectively play with the Privacy Badger sliders to resolve the problem.
Martin, This is an excerpt from your stated privacy policy:
Third Party Advertising:
We use third-party advertising companies to serve ads when you visit our website. These companies may use information (not including your name, address, email address, or telephone number) about your visits to this and other websites in order to provide advertisements about goods and services of interest to you. If you would like more information about this practice and to know your choices about not having this information used by these companies, click the links below.
Included in the links you referenced are well known trackers. I have requested that I not be tracked via a header sent by my browser (DNT). If and when you commit to honor do not track requests, I will gladly whitelist your site.
Would be handy if it would block Windows 10 tracking and telemetry.
I wish it would bake cookies too!
Does Privacy Badger 2.0 still override your cookie settings to allow cookies? One thing I hated about Privacy Badger which led me to no longer use it was that it made Firefox accept cookies even when you set Firefox not to.
No, it doesn’t override cookie settings to allow cookies.
In Firefox, PB version is reported as 2016.12.8, so I guess they changed their versioning too and it’s not really called 2.0 now.
As for changes in 2.0, the major one for firefox is the shift to webextension, thus making it a universal codebase across all platforms now, and making it work nicely with e10s in the process.(previously, you had a separate repisitory for firefox on github)
Seamonkey 2.46
“The Addon downloaded from unknown host could not be installed because it appears to be corrupt.”
Gave up after 6 attempts.
Installation of several add-ons on Seamonkey (2.40) seems problematic lately.
uBlock Origin, thankfully, installs on it without a problem.
I don’t use Privacy Badger, but based on the premise “Block trackers but allow ad”, this can only give a false sense of security, which is worse than a true sense of insecurity.
Even if you block all trackers, ads themselves are trackers. An ad network only needs a network request to track people across all sites. It doesn’t actually need fancy JS analytics.
There is some confusion here:
“based on the premise “Block trackers but allow ad”…â€
This is a false premise, concerning Privacy Badger. Privacy Badger doesn’t claim this; it says it is designed to block all trackers, including ads which track.
Here is what it says on the PB site which Martin links to above: “Privacy Badger is a browser add-on that stops advertisers and other third-party trackers from secretly tracking where you go and what pages you look at on the web.â€
And further down on the page: “It just so happens that most (but not all) of these third party trackers are advertisements. When you see an ad, the ad sees you, and can track you. Privacy Badger is here to stop that.â€
This additional explanation below from the same page may be helpful for people who don’t understand precisely what PB is or what precisely it does:
“How does Privacy Badger work?
When you view a webpage, that page will often be made up of content from many different sources. (For example, a news webpage might load the actual article from the news company, ads from an ad company, and the comments section from a different company that’s been contracted out to provide that service.) Privacy Badger keeps track of all of this. If as you browse the web, the same source seems to be tracking your browser across different websites, then Privacy Badger springs into action, telling your browser not to load any more content from that source. And when your browser stops loading content from a source, that source can no longer track you. Voila!
At a more technical level, Privacy Badger keeps note of the “third party” domains that embed images, scripts and advertising in the pages you visit. If a third party server appears to be tracking you without permission, by using uniquely identifying cookies (and, as of version 1.0, local storage super cookies and canvas fingerprinting as well) to collect a record of the pages you visit across multiple sites, Privacy Badger will automatically disallow content from that third party tracker.â€
To be fair, the concept of blocking third parties based on algorithms is interesting and could fit pretty well within uBlockOrigin as a companion feature. (Because it cannot be used safely without a more thorough and granular content blocker.)
The problem here is that PB’s rules as they’ve been described are way too lax and can’t live up to the claims made and EFF’s reputation.
That’s almost what I meant yes.
More precisely, I meant to say that Privacy Badger’s claims as I understand them are misleading. It claims to identify 3rd parties that track you across the web and block them.
Sounds good. Sounds like if I install Privacy Badger, after a while all I will be left with are non-tracking ads, if any.
But that’s not what happens, not with the rules they describe. “Identifying” tracking 3rd parties implies setting up rules that define what they do, and that’s where PB is misleading because the rules they talk about are not targetted at tracking 3rd parties, they are targetted at *some* tracking third parties that use *Canvas*, *uniquely identifying* cookies, and I guess a couple other things. These rules are LAX. EFF has a reputation and Privacy Badger has a meaningful name; this gives people a sense of security and trustworthiness. Their extension using such lax rules is misleading.
I used to love EFF, but then I realized they are actually the ones who democratized fingerprinting techniques, they published research and proofs of concept on this long before fingerprinting was being used in the wild. Recently I found that some large site used an open source fingerprinting library made by someone who built it based on…EFF’s work.
So, while I’m still going to believe they are pro-privacy actors, I no longer consider them to be the privacy champions that they are made out to be. What I’ve seen of this Privacy Badger extension so far deepens my concern instead of alleviating it. In the end, EFF are probably pro-privacy middle-grounders, which would be fair enough if that corresponded to their public image.
@Meh: “Thanks for sharing more details.†You’re very welcome!
The catch here may perhaps be a conflation of “trackers†and “tracking.â€
Privacy Badger says it is “a browser add-on that stops advertisers and other third-party trackers from secretly tracking where you go and what pages you look at on the web.†And further from their website:
“What is a third party tracker?
When you visit a webpage parts of the page may come from domains and servers other than the one you asked to visit. This is an essential feature of hypertext, but it has also come to be a serious privacy problem. On the modern Web, embedded images and code often use cookies and other methods to track your browsing habits — often to display advertisements. The domains that do this are called “third party trackers”…â€
So Privacy Badger doesn’t claim to block ALL possible forms of tracking; it says it’s designed to stop third-party trackers (domains), and it says it does so by blocking the domains which it identifies as such “trackers.â€
As you rightly point out, though–and as does the EFF, the makers of PB–there are numerous other methods of tracking. And as you rightly point out, blocking other methods of tracking can be beyond the scope of any single browser add-on. To my knowledge no single browser add-on by itself–not PB, UBO, ABP, Ghostery, NoScript, etc.–is capable of blocking ALL forms of tracking, and it wouldn’t be fair or realistic to expect one browser add-on on its own to do so.
I think if a user is concerned about privacy it is important to first do a thorough threat assessment and then go from there addressing each specific type of threat. For example: I wouldn’t try to use a browser add-on such as PB or uBO to address potential IP address tracking; I’d use a VPN.
I agree about blocking ad networks altogether, and I block hundreds or thousands of ad networks, and other domains known to track, in a variety of ways: at browser level, system level, firewall level, router level, etc..
If I understood your initial concern correctly, though: if someone installs Privacy Badger and mistakenly thinks that it blocks ALL possible forms of tracking, then they might then have a false sense of security, and that’s certainly true, of course. But I think your posts and mine on here have by now probably shed enough light to have all-but-extirpated any such false sense of security remaining out there… :)
By browsing patterns I mean the websites we visit. Even with a dynamic IP we can be tracked just from IP in a given session. Should we browse according to our habits later, with another IP, the fact that we are visiting the same sites and not in a random order helps identifying us and linking previous sessions together. Sometimes it helps a LOT.
Over time your available IP ranges could be then be narrowed down to further reduce the privacy advantage that it represents.
Thanks for sharing more details.
The catch is here:
” If a third party server appears to be tracking you without permission, by using uniquely identifying cookies (and, as of version 1.0, local storage super cookies and canvas fingerprinting as well) to collect a record of the pages you visit across multiple sites”
You don’t need a uniquely identifying cookie and you don’t need canvas to track people across multiple sites. Any plain network request will do: It transmits a bare minimum of IP address and a number of HTTP headers ( https://en.wikipedia.org/wiki/List_of_HTTP_header_fields ). Most people have a fixed IP, which means IP alone is enough to uniquely identify them and follow them month after month. For those with dynamic IP, HTTP headers are varied enough that, coupled with IP, makes for quite an interesting tracking mechanism already. But that is not accounting for browsing patterns from page to page and site to site, which can be very revealing.
That’s still not all, because Privacy Badger apparently (?) allows 3rd party Javascript except Canvas and I assume a couple of other things they’re not talking about, like maybe timing APIs. If that’s what they do, it will never be enough unless they also block XHR so scripts don’t phone home when they’re done spying on you.
So:
– Blacklisting some JS features is false security because you can still be tracked thoroughly
– Blocking XHR may secure the JS leaks assuming there’s no clever workaround, which is something I would not bet a sandwich on
– Forbidding all JS still leaks your IP and many HTTP headers, along with your browsing patterns
– Only tampering with cookies leaves a number of identifying bytes in HTTP headers that can be coupled with IP and patterns. But Privacy Badger apparently only deals with cookies deemed “uniquely identifying”, which possibly allows sneaking in a couple more identifying bytes in seemingly innocuous cookies
I’m sorry to say but when all is said and done, what other solution is there but to uncompromisingly block ad networks altogether ? I have nothing against ads that behave, but once they can’t be dissociated from tracking as I’m trying to show, there’s no saving them.
The only ad I accept is the one served from the 1st party site. But this is STILL assuming the website’s server doesn’t just forward my data to ad networks, so there is trust involved, which is fine until 1st party sites are forced by ad networks to host 3rd party libraries on their own servers to do the forwarding without user knowledge. (This can’t be detected since it occurs from server to server)
Nothing uBlock Origin isn’t able
to do. Including the WebRTC part.
“Nothing uBlock Origin isn’t able to do.â€
Good to know! I’m not completely versed in UBO–can you say how to block cookies and local storage super cookies and canvas fingerprinting in UBO, like Privacy Badger does? Thanks!
uBlock origin is great (probably greatest) at blocking ads and domains. But yes, things can slip through – it either blocks everything from a domain or nothing. For more protection there’s uMatrix which can, for example, block a cookie or a script, but allow an image from the same domain. So there is an extra level for those with a lot of spare time to configure it. ;-)
That was assuming you enabled privacy-related lists in uBO. I don’t remember if they are selected by default…I think yes ?
Without privacy lists, uBO will miss more trackers.
Not possible with uBO. But it is not a problem, when ad networks are blocked completely they can’t store crap or fingerprint you.
That said, unless you run uBO on nazi-mode, filter lists may miss some offenders or whitelist others on certain sites for compatibility. Their ability to track you is limited to a few websites in the latter case, and missing offenders seem rare.
To cover those cases you’d have to use a cookie manager add-on or, without addon, just forbid third-party cookies while allowing first-party in Firefox options. That alone should work better than Privacy Badger’s cookie handling since (if I understand correctly) PB filters suspicious third-party cookies, not all 3rd party cookies. (Note that blocking those cookies doesn’t cause compatibility issues with websites. Also web storage is included in that definition of cookies.)
Canvas fingerprinting is only an issue when you allow JS. JS allows extensive fingerprinting, so the canvas focus is almost a meme unless you’re running Tor Browser, which has had JS patched up like a pirate with three wooden legs, seven hooks and an artificial eye. I think there’s a separate extension for that though.
I’m using the latest versions of uBlock Origin and Privacy Badger together on Chrome, my primary browser. No problems to date, until I whitelist Ghacks. This is most unfortunate, as I want to support the site, but don’t know of a non-paypal solution.
I am still using Ghostery despite also having uBlock origin on my PC because it seems Ghostery is still catching some stuff that passes uBlock. At this time I will not touch Privacy Badger, it does not seem to be reliable.
Just wondering if Ghostery is collecting data despite me checking the box to not to participate in their data collection. Guess I am getting a bit paranoid about these privacy issues but what does it help. As long as I am profiled as a 30 year old lesbian male, bald and divorced 4 times, IT pro with 66 years of experience, interest in stepdance, crochet work and skydiving without a parachute I am not too concerned.
Thanks for the info, I’m sticking with my tweaked uBlock Origin (I allow ads that don’t track me).
Martin, can you add a link to programs/extensions like this? I’m always having a hard time finding a link in the article text itself, but I can’t find it this time. I think the Summary section is a good place for it, as well as when initially mentioning the ‘product’ in the article body.
Sure, sorry for that. it is in the article now. you can grab it here: https://www.eff.org/privacybadger
So I use Ublock Origin and PB 1.0. So basically are they the same?. Do I need just need one of them?.
Thanks.
@wybo: “So I use Ublock Origin and PB 1.0. So basically are they the same?. Do I need just need one of them?â€
UBO and PB can do some similar things, but they are not basically the same. They can be thought of as complementary and can be used side-by-side, as it says on gorhill’s UBO page on github, and also on the Privacy Badger page which Martin links to above.
You can configure uBlock to block these trackers as well. Privacy Tracker is not designed to be an ad blocker however. It blocks tracking, but keeps ads enabled (which support sites like mine).
Do you get the same benefit from ads when you block trackers? Or do the ads just get displayed then, but without the benefits for you because the ad seller can’t track usage?
Can you even block ads separately from ad usage trackers?
I’m not 100% sure how Privacy Badger works. It does let some ads through but not others. Any ad that is displayed earns revenue, so if some are displayed, that is still helping out.
Ads without tracking work, but they pay less, I assume. I’m no expert on the topic. I think in this case it depends on whether the ad provider honors the do not track header.
Or we can just white list YOUR site in uBlock Origin, we we want to support you :p
I have whitelisted Ghacks (in NoScript and Adblock Plus + Firefox), and it works a charm for me. The site is very fast in this configuration. But maybe there are some ads I don’t get to see, on top of those I do see ?
When sites offer good information for free, plus navigation is fast and ads are well behaved, and the site owner asks nicely, whitelisting is a no-brainer.
Thanks!
I used to whitelist ghacks, but the ads were often so intrusive and slowed the site down to such inconvenient speeds, that in the end I decided to join Martin’s Patreon thing instead.
Thanks Dave. I really wish Patreon and Ghacks Deals would be able to support this site alone. I’d pull all ads immediately from the site to speed it up for all users. That’s unfortunately not the case.
I’m wondering : are all those privacy / anti-tracking / adblocking add-ons compatible with each other ?
From the Privacy Badger page which Martin links to above:
“Is Privacy Badger compatible with other extensions, including other adblockers?
Privacy Badger is compatible with most extensions. Whether it makes sense to run it with another adblocker varies. If you have customized your adblocker settings to block trackers as well, Privacy Badger may be partially redundant (though it may offer advantages like cookie blocking that other tracker blockers do not). However if you run extensions like Adblock Plus or Ghostery in their default configurations, Privacy Badger can significantly increase your privacy online. (Adblock does not block invisible trackers by default, Ghostery does not block anything by default.)
The only extensions known to be incompatible with Privacy Badger is the Avast antivirus extension, which blocks the installation of Privacy Badger and other extensions.”
Thanks, Hy. I had Avast antivirus add-on, and just added Privacy Badger. No apparent problem. Privacy Badger has an irritating bug, though : if you run it from within the hamburger menu as I do, the interface is halfway outside the screen. Real estate on the top of Firefox is rare, with all those oversized kiddy icons.
Crashes immediately on Chromium.
Thanks for the info.However, I’ll be sticking with uBlock Origin.
Someone should make a filter creation tool for uBlock. Or at least better documentation. The filter syntax is confusing and things like script contains:() rarely seem to work.
I know I could use and would really appreciate an article on/good clear guide to uBlock Origin and everything that it can do and how to use it to get the most out of it.