KeePass audit: no critical security vulnerabilities found
We reported back in June 2016 that KeePass, a popular password manager, was getting a security audit by the European Commission's EU Free and Open Source Software Auditing project (EU-FOSSA).
EU-FOSSA is a pilot project to create a formal process for contributing software security reviews to open source communities.
The project created an inventory of open source solutions used by the Commission, published studies into the security practices of 14 open source communities, and reviewed two popular open source solutions.
KeePass is a password manager created for Windows -- also working on Linux -- that uses a locally stored encrypted database.
The program ships with an impressive list of options. You can enable a global login shortcut for instance, or improve security of KeePass by modifying settings.
The password manager supports plugins and forks thanks to its open source nature. Plugins enable users to extend the program's functionality, for instance by integrating it in web browsers or synchronizing the database using online storage providers.
KeePass audit
The research team audited the code of KeePass 1.31, and not of KeePass 2.34. While KeePass 2.34 is not mentioned anywhere in the report, it appears reasonable that KeePass 2.34 would fare similarly in a code audit.
KeePass 1.x is the legacy version of the password manager. The version does not require Microsoft .NET but lacks features that only KeePass 2.x ships with. It does not support linking KeePass to the Windows user account or one-time passwords for instance. You find a full edition comparison table here.
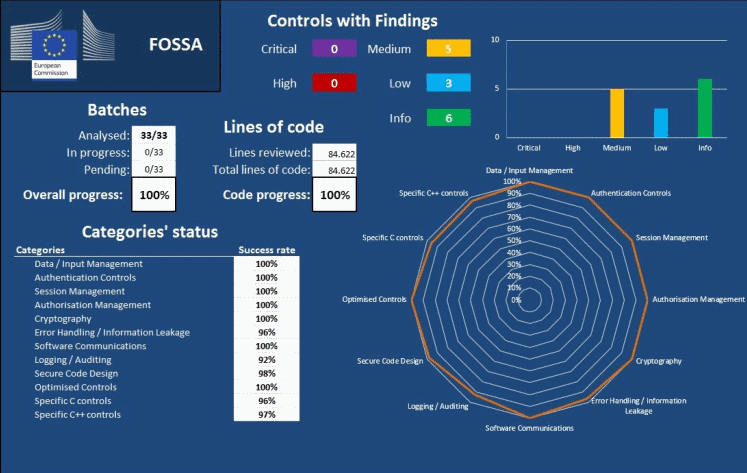
The KeePass audit went through all 84622 lines of code and found no critical or high-risk issues in the code. It did find five medium rated, three low rated, and six information only rated issues however.
No critical or high-risk findings were detected. Among the remaining findings, five medium and three low risk results were detected. The remaining six were of an informative nature.
The issues that were found by the researchers are detailed in the audit report which you can download from the project deliveries page on the EU-Fossa website. There you find listed the Apache security audit as well (look under WP6: sample code review near the bottom of the page).
Closing Words
KeePass is an excellent, secure, password manager for Windows. The results of the code audit suggest that it is a well designed program with no critical or high risk issues.
Now You: Which password manager are you using and why?

















The problem is everything is “unofficial” when it comes to Keepass so an audit today is worthless. Unofficial ports, unofficial plugins, unofficial extensions, unofficial mobile apps. I bet they just audited the database file and stopped there.
I just can’t stand Keepass. Even the site tells you a lot. It looks crusty. Not modern, hosted on a shi**y site which doesn’t really lend to being a user-friendly forum, and all of the features that can compromise my security (i.e. plugins, browser add-ons, mobile ports) are not officially endorsed.
“Took a look at a kdbx file. Yep. It’s a database. Everything looks good here, folks.” A million dollar audit to audit nothing. That drives me nuts. Waste of money.
Keepass needs to leave SourceForge for something better. They need to actually integrate plugins into the app so they get audited. Makes no effing sense. They need to officially host and support a mobile app.
Let these people who contributed unofficially contribute officially for God’s sake.
By not supporting the whole platform an audit is pointless. It’s probably the most vulnerable app for it’s extra, unsupported feature mechanism and unofficial ports.
Will 2.x undergo an audit too?
KeePass 1.x for years for personal usage, and Password Safe at work.
To speculate why they chose to audit 1.x and not include 2.x, it’s probably for the same reason I choose to forgo the added features of 2.x, which is because those features come bundled with all the baggage of .NET. I’d venture that would add significant difficulty to the audit process. Why bother with 2.x if 1.x meets the needs of the EC?
I’ve used Keepass for many years on my desktop, never had any issues. I use the Keepass2Android app on my phone with Onedrive, no issues there either. Keepass is really a terrific password manager.
Keepass. Used it for years, see no reason to ever change – does everything I need and (as important) very little I don’t need.
I use the portable version on a separate partition. That way I can lose, and have to rebuild, my OS – but my passwords are safe. Multiply backed up of course, so it would take a major disaster to lose everything.
Long KP password changed every month. Pick a page and a line in Shakespeare, Dickens, whatever you like, and use the initials with perhaps a number or symbol mixed in and/or at the end. My current password is 18 characters and I have no trouble remembering it (and very little trouble rebuilding it if I forget.)
To date (touch wood) I’m unable to understand why anyone (talking ordinary people here rather than businesses or corporations) might ever need to use anything else.
I use KeePass from the initial versions and I do not change it for anything. I did not like version 2.x, I found it too full of functions that are not useful.
Thanks for that reassuring piece of news concering my password manager.
However, how stupid is it bothering to do an audit of an old version of the software ? And if the EU is, indeed, using KeePass v.1 internally, how bone-headed is that ?
Version 1 does not have the crucial security feature Enter Master Key on Secure Desktop (which is optional on v.2 : it should be the default choice). This means that if a keylogger has been dropped by some malware on your PC, a hacker can capture your master password ! That’s absolutely the worst accident waiting to happen !
Does anyone believe that the European Union’s offices are not under constant attack by various countries spies, Russia being on the forefront, and having a long record of successful cyber-attacks ?
Nothing bone-headed about it. The version numbers don’t mean much in terms of functionality or oldness, but that the codebase was rewritten in a different language. That means they’re almost different programs, not an obsolete and new version of the same thing.
The 1.x codebase keep getting updates, and could possibly be more secure than the .net version, particularly if a comprehensive auditing required audit of the underlying .NET library code too.
The Secure Desktop feature isn’t as secure as you’d like to think too – its already been found to be bypassed. You should always encrypt the DB with a file as well as password, and keep that file on a network or USB stick.
https://www.trustwave.com/Resources/Security-Advisories/Advisories/TWSL2014-011/?fid=3730
So: v1 is just as good as v2, there’s no reason not to use it.
There’s nothing that says they don’t have an important series of patches and tweaks for their custom version of 1.31. Those patches and tweaks could be more important in their eyes than whatever 2.x provides. Perhaps they don’t even need 2.x at all. Who knows.
Either way, for a software acquired along with its source it’s quite natural that an in-house version will be derived from it to fit more specific needs. At some point it can become undesirable to import updates from the third-party. It happens on its own over time but can be done with intent too: Get the software so you won’t have to reinvent the wheel, and from there care for yourself.
Can’t say that it’s the case here, but they seem to have a reason to want to stay on 1.31 if they:
– Paid for that audit recently, and
– v2.x is clearly older than the administrative time needed to setup and pay for an audit
—–
@Martin: It seems that we need to allow JS from googleusercontent.com for certain comment features to work. (e.g. to reply to a specific comment)
If possible, could the feature(s) be duplicated as Ghacks code that has nothing to do with Google ?
been using Password Safe for years. I believe its almost like keepass. Put out by
Bruce Schneier…a longtime security guru of sorts. Never a problem. I stay away from anything using the “cloud”….just someone elses computer. When using copy and paste to enter info on sites, i like that the clipboard is cleared when minimizing the program.
Just to be clear – in case someone reading your post infers something that is not true – KeePass, in and of itself, DOES NOT employ the cloud. KeePass encrypts your database with a 256-bit key using AES or ChaCha20. For extra security (in addition to your master password – never in place of it), you can also require a master key file derived with either AES-KDF or Argon2 to be present to unlock your encrypted KeePass database. Moreover, your master key file can be any file you want (a .doc, a .jpg, .mp3, whatever) as long as it is never altered or lost. And by default, KeePass inherently stores everything locally. It does not require, offer, or operate cloud storage for your encrypted database and/or master key file. You have every ability to move and store your encrypted database and master key file however and wherever you choose. It is recommended to not store them in the same folder, or even on the same drive. But with this setup, you are good to go with KeePass.
Now there are optional KeePass plugins available that add sync functionality to any number of cloud storage providers with whom you might have an account (Dropbox, S3, OneDrive, Google Drive et al.). Just as with your local storage, your remote database is still completely encrypted with that 256-bit key. It is strongly advised to not keep the master key file in an easily-recognizable fashion with either your local or remote and fully-encrypted databases. Without both the master password AND the master key file, the encrypted cloud database by itself is fairly useless to anyone who might breach your account and snatch it.
I think of it this way: I am far more concerned about the sheer number of my still unencrypted, unsalted and/or poorly hashed passwords sitting in far too many web databases around the internet than all of my passwords sitting in one 256-bit AES-encrypted file behind a 30-character master password and a clandestine master key file that could be any (or none) of the files in that same cloud account.
From the Article “The research team audited the code of KeePass 1.31, and not of KeePass 2.34”
Uhm, what’s the point of that? When they audit Libre Office, are they just going to do ‘Base’ and ‘Draw’, whilst conveniently leaving out all the other programs that make up Libre Office suite such as ‘Writer’, etc.? Talk about half a job… utterly pointless especially as most people probably use Keepass 2 anyway.
The audit is apparently for the European Commission’s benefit. I guess they use 1.31 internally, perhaps a modified version that they are now going to fix.
Whoops, that response was meant for Janice, sorry.
Err, yes. You should read up on the matter. LP has been successfully compromised at least twice, which they have admitted.
They noticed suspicious activity and took precautions. No passwords were ever breached.
https://blog.lastpass.com/2015/06/lastpass-security-notice.html/
Yes. If you read my post above, I never said passwords were compromised. And suspicious activity is just business-speak for “we’ve been breached” without actually admitting so.
I use the official and the unofficial KeePass Chrome extension and both working, but they both sending statistic stuff back. You can opt-out it’s in the options but they will still send a request back. You can see this with the internal debugger or uBlocks/adblocks logging. But this is to improve the extension because they may report login problems. I not really inspected every aspect I only know the GET method is okay.
Yeah I trust KeePass and I’m using it since the beginning, I was sure they not will find much and even if I have faith in the developer that he would fix it asap.
From what I know the random key generation was already changed/improved in the last two release.
Keep rocking ! :)
That is why I ditched LP, deleted my passwords there, and returned to KP. LP has been targeted by attacks, twice successfully.
> twice successfully
Er, no.
I have read the executive summary of the audit, and I notice that two of the medium risk vulnerabilities are related to generating pseudorandom numbers. Specifically, the audit notes that Keepass uses rand() and std::rand(), which do not provide cryptographically secure PRNG.
The summary says that “The issue in this case does not affect the security of the code because is not related to the main functionality of the software (encryption)”, which I disagree with because, as a cryptographic primitive, the quality of the PRNG has bearing on its primary function (encryption). You need to feed good PRNG for Keepass to encrypt securely.
Keepass also generates passwords, which while not primary, is a major secondary use for the software. I had used it to generate some of my passwords, but I am glad that I shifted to using PWGen for Windows. Hopefully future versions of Keepass will fix their source for PRNG.
I tried dashlane, lastpass and roboform. Keepass is always my favorite. I was wondering if you have tried CKP-Keepass integration chrome extension. Does it use similar security settings?
I have never used any KeePass browser extensions, sorry. Maybe someone else can chime in?
I use ChromeIPass on Chrome, and Passifox on Firefox. Seems secure but I haven’t really vetted it.
Any news about the KeePass audit?
You can check the progress here
https://joinup.ec.europa.eu/community/eu-fossa/og_page/project-deliveries
Thanks !
No word on that yet. I post the findings once they become available.
Thanks Martin !
keepass needs a massive audit 1pass needs one too
I would suggest to have also IrfanView being scrutinized
IMHO the only thing missing from KeePass is an auto-updater exactly like the one built into Firefox.
It could also use a server component that could keep disparate clients up to date without forcing a reload/merge (it queries the DB with every entry examination rather than loading everything on launch and keeping it resident), and much better non-Windows clients, but that’s just my specific use case.
For unknown reason, I’ve been served with mobile version of the site on my desktop.
If that is the case, scroll to the very bottom and click on the desktop button there.
I’ve used KeePass for years – portable edition with a password as long as my arm. Does everything I need and (so far) admirably unbloated. To the point I’ve yet to find anything that remotely approaches it for both efficiency and simplicity.
As with any security app – an audit always welcome, just for peace of mind.
Hmm, I wonder if they will look at any plugin’s for Keepass.
The word “euro” as a currency should not be capitalized in English.
KeePass v1 or v2?
My guess is version 2, but I don’t know for sure.
Linux? How would that work? By the time the audit is finished, we’d be two full kernel versions further along the line.
Probably by concentrating on important parts.
I wouldn’t have picked FF, as I think it’s already well funded and scrutinized, and it’s such a dynamic area, that an audit would probably quickly fall out of date (but could well pick up something useful). It’s just too big. A narrow linux aspect could have been feasible, but again, I think it’s well scrutinized at this point, but I’m not an expert.
I like the idea of back-end applications getting an audit, as this will directly benefit more people. I probably definitely have pumped for Apache. And probably MySQL as second pick.
“probably definitely” … I think I need to drink more beer .. what a(n) (oxy)moron I am