Malwarebytes releases Telecrypt ransomware Decrypter
Malwarebytes Telecrypt Decryptor is a free program for devices running Microsoft Windows to decrypt files that are encrypted by the ransomware Telecrypt.
Telecrypt is a rather troubling piece of ransomware that is distributed through various means including emails, exploits, and drive by downloads.
What makes Telecrypt special is that it uses the API of the popular messaging service TeleGram for communication, and not a control server or servers on the Internet.
TeleGram communication is encrypted and the team behind the service has released an open API and protocol for anyone to use.
TeleCrypt will encrypt files on the system, and launches a program which informs users about the encryption. The ransomware looks for more than hundred different file types including jpg, xlsx, docx, mp3, 7z, torrent or ppt.
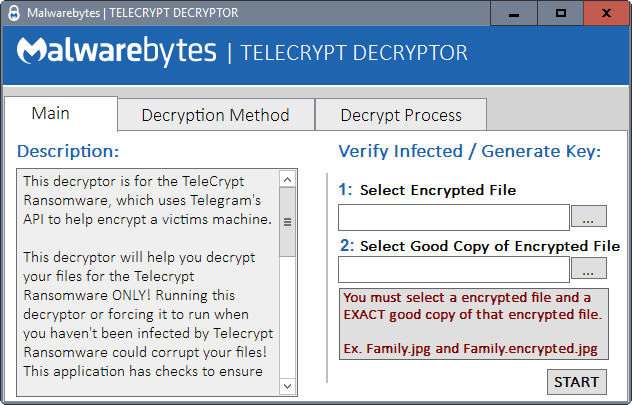
Malwarebytes Telecrypt Decryptor
The decrypter has been developed by Malwarebytes. It requires that you have access to a good copy of one of the encrypted files. The file type does not matter at all.
Your best chances are backups, online cloud storage used by sync software, or any other form of back up space that you may have access to. A suggestion that Malwarebytes has is to use sample photos that Windows ships with, as they are usually easy to get hold of. You may also re-download email attachments if email is kept on a mail server.
You need to load the encrypted file, and the good copy, on the screen that opens. Once you have done so, click the start button and follow the process.
Telecrypt Decryptor verifies the files that you have supplied. If the files match and are encrypted by the encryption scheme that Telecrypt uses, you are taken to the second page of the program interface.
Here you may either add the list of files that the ransomware has encrypted on the device, or may point the program to a single folder containing encrypted files.
You may copy any encrypted files to a single folder location, and pick the folder decrypt option to decrypt all files copied to the folder at once.
It is suggested that you work with backup files and not the original files to avoid any issues that may arise during the process.
You find additional instructions and screenshots on the Malwarebytes blog.
Now You: Have you ever been the victim of a ransomware attack?


















Well, you were complaining about a missing signature. Never mentioned you also had to speak white…
Indeed it does.
According to Malwarebytes: “Infections with this ransomware can be recognized by the note left on the Desktop named: База зашифр файлов.txt. It contains the list of all the encrypted files.”
Right, but for a non-Russian reader that does not mean anything, or could mean anything, i.e.Telecrypt is not too useful for non-Russians.
With so much ransomware about, how does one know it is Telecrypt that got hold of your files? I assume it does not leave a signature behind.