VeraCrypt 1.18 fixes one TrueCrypt vulnerability
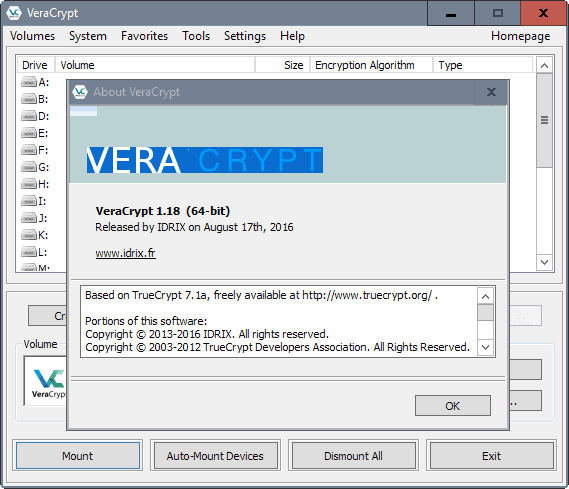
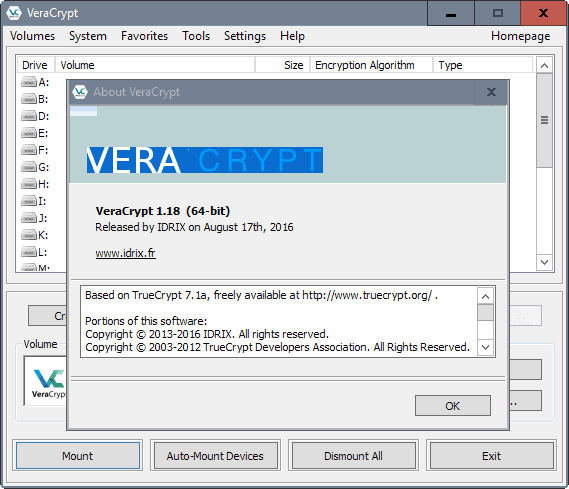
VeraCrypt 1.18 was released yesterday by the development team for all supported operating systems. The new version of the encryption program fixes one vulnerability affecting the application and TrueCrypt, the encryption software it uses code from.
VeraCrypt is one of several TrueCrypt alternatives that were published shortly after development on TrueCrypt ended under mysterious circumstances.
The encryption software is based on TrueCrypt code for the most part, but has been modified in the past two years of its existence to add, change or remove functionality.
While that is the case, it is still based on TrueCrypt code for the most part. The developers of the program fixed vulnerabilities that came to light after the TrueCrypt audit, and added interesting features to it such as PIM.
VeraCrypt 1.18
The most recent version of VeraCrypt fixes a vulnerability in TrueCrypt that allows attackers to detect the presence of hidden volumes on a device.
VeraCrypt, just like TrueCrypt, support hidden volumes that are put inside regular volumes. The idea is that if users of the software are coerced into handing out the password to the encrypted data, that it only reveals the regular volume and not the hidden volume inside.
The new version of VeraCrypt improves other features of the application. The new version supports the Japanese encryption standard Camelia for Windows system encryption (MBR and EFI), and the Russian encryption and hash standards Kuznyechik, Magma and Streebog for the Windows EFI system encryption.
On Windows, VeraCrypt 1.18 introduces support for EFI system encryption. The limitation at this point is that the feature does not support hidden operating systems or custom boot messages.
The new version ships with better protection against dll hijacks on Windows. VeraCrypt 1.18 fixes boot issues that were experienced on some machines, reduces CPU usage, and has a workaround for AES-NI support under Hyper-V on Windows Server 2008 R2.
The command line version supports a new command to pass smart card PINs via the /tokenpin option, and a command line switch to hide the waiting dialog the program displays normally.
Closing Words
TrueCrypt users won't get the vulnerability fixed as the program is no longer in active development. While the issue may not affect all users, as it only affects encryption setups that use hidden volumes, users that are affected may want to consider migrating to VeraCrypt instead.
The release is not the only good news about VeraCrypt. The encryption software will be audited thanks to OSTIF (Open Source Technology Improvement fund). You can read the announcement here. The audit will happen over the course of the next month, with results being released publicly after they have been patched.
Now You: Which encryption software do you use primarily?

















@not-a-paranoid-looney
>Okay.
Good choice of yours tryuly.
Being wise is the best you can do.
Kind regards, Laren Mc Malcolm
I don’t know whether to laugh or cry at this increasingly common idea that the NSA is capable of what can only be described as omnipresence. Apparently, every piece of software and encryption method is backdoored, you’re being spied on 24/7 and there’s absolutely nothing you can do to stop them. Okay.
The toughest and wisest choice is to neither laugh nor cry. Exercise caution but do not distress yourself with imaginings. Human nature often needs certitudes when doubt is most often the only truth we can rely on. Aggregate information but avoid conclusions without absolute evidence. We are tightrope walkers rolling from one thesis to it’s antithesis and choosing either is like falling. You have to doubt to make the best of information. Because information is the matter, that’s what it’s all about, right?
Personally each time I feel a conclusion tempting me I tell myself to find the counter-arguments. I read papers and visit sites that are opposite to my beliefs, temporary for some is always possible and I’ve changed my mind here and there. No one is obliged to remain faithful to convictions when the only matter that counts is an eternal quest for truth knowing it’s hardly ever met.
Good luck.
OK. I’d like to stay awake and vigilant.
Vigilant asleep is tough :)
@ Mr. Hawack, Intelligenica, Panama Kid
I’m not a scaremonger. Mr. Hawack, I told that some interpretations lead to pressures to the Developer. I’d like to put into your attention a similar story with a similar security application: PRETTY GOOD PRIVACY.
Phil Zimmermann told that no backdoors were ever present… but then PGP was acquired by Symantec. Can you trust Symantec?
https://web.archive.org/web/20120204044317/http://www.philzimmermann.com/index.html
VeraCrypt is still independent. It is being audited, of which some of the email communications with the other companies disappeared mysteriously. But VC & its partner audit firms have further tightened the encryption, so that should take care of snooping. Why panic when there is a report about some irregularities that can easily be fixed? I call that scaremongering.
Not sure anyone/everyone is panicking. May also be coherence, that of using an adequate application, the right application, at least not the wrong one. Panicking, as i see it, is more likely when your computer has been blocked by cryptoware and you’ve got a 100 bucks left on your bank account and years of pictures, email, videos of your kids on the computer … not my story neither that of my life but thinking of it, yes: there I could panic.
http://truecrypt.sourceforge.net/ has a guide to decrypt it and then use bitlocker. Not sure if this is helpful or not.
sorry i dont think this will help.Not sure it can be done from what i read. Maybe this will help but i have no idea http://www.addictivetips.com/windows-tips/quickly-find-hidden-or-disguised-truecrypt-container-using-tchunt/
addictivetips.com hahahaha…. what a domain!
I am looking for an easy guide to recover a lost TrueCrypt partition on my HDD. If someone has any info, please let me know :)
Hello you can try Testcrypt:
http://testcrypt.sourceforge.net/
maybe this helps
Thanks. I will read into it.
the truecrypt website has a guide
List of vulnerabities:
https://musalbas.com/2016/08/16/equation-group-firewall-operations-catalogue.html
Guys!
I DON’T LIKE WHAT I AM READING/HEARING!
Your warnings (as stated above) are Definitely an Eye-Opener!!!
I will re-think (using) my Beloved VeraCrypt – – YIKES!!!
I think after this I am going back to version 17.1
i
You are being panicked by scaremongering. Do you really think the NSA is going to come after you if you have not been involved in criminal activity, or suspected to have done so?
VeraCrypt is keeping you safe from prying eyes of those around you. If you have enemies who are very computer-savvy, then you probably need stronger software than VC or TC 7.1a.
And if it is the NSA you’re scared of, best to ditch your computer & say goodbye to internet.
How much you pay for enemies cyber weapons?
5 days ago a group called shadowbrokers announced an auction for undisclosed vulnerabilities:
http://pastebin.com/NDTU5kJQ
At first it appeared as a scam, as this group is unknown while equation group is responsible for hyper-advanced malware like Stuxnet, Duqu/Flame, and Strider/Project Sauron.
Now, Cisco’s confirms that EPICBANANA and EXTRABACON vulnerabilities listed in the auction were real. It had fixed one in 2011, and the other, a new SNMP bug, is on the to-do list with Snort rules providing temporary protection. So, the shadowbrokers are releasing real, hot tools.
Sources: http://www.theregister.co.uk/2016/08/18/fortinet_follows_cisco_in_confirming_shadow_broker_vuln/
http://pastebin.com/NLEMsYmz
Hi Mr.Hawack.
WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues
It’s a hint for some, also the page tells to use BitLocker© and looks like a hitman page with onion url…
See: http://truecrypt.sourceforge.net/
I call that an interpretation, not the understanding of a hint, not even of an implicit hint. Like the interpretation of dreams and even sometimes as bazaar psycho-analysis…
I read “Using TrueCrypt is not secure as it may contain unfixed security issues”. From that, theories, certitudes, conspiracy, agencies … this is a mad world and nuts are flourishing. I’m not saying that fantasy is the proof of a wrong direction I’m only reminding that when fantasist interpretations happen to reveal truth it’s plain luck.
I have no idea as I said. Who has any reliable facts, evidence? Maybe there is/was a conspiracy against TrueCrypt, maybe the developers were fed up for other reasons… how can anyone besides them and others than those concerned if applicable know anything about this TrueCrypt mystery? In doubt, with no substance, I maintain TrueCrypt.
I’ll bring my part to the Fantasy World : OSTIF would have deliberately put the pressure on state/nations interventions in order to enhance the legitimacy of VeraCrypt with the effect of running down TrueCrypt (logic : if VC is spied then VC is valuable then TC is/was not) … when in fact TC was, is the good application in this whole goddamed odyssey …
Fantasy, fantasies … with imagination you can build mountains with clouds (or make a bee think of honey just as the singer thinks of her). Marvelous, romantic, exciting, thrilling but… true?
Hi Intelligencia. As you know TrueCrypt 7.1a is the last full-working version before the 7.2 stripped down version that doesn’t encrypt anymore. The developer posted a warning message on sourceforge, hinting at the US agency known as NSA. Most probably he was requested to insert some backdoor or has been told to stop developing truecrypt, which he did.
So, Intelligencia, Veracrypt and the few other similar tools for windows are really under NSA (as other agenices) scrutinity.
“[…] hinting at the US agency known as NSA. ” You may be right but I’ve never heard of any hint, published anyway. Are we sure we’re not mistaking our suspicions with what was never published, not even as a hint?
Hello Everyone!
Simply Put . . .
I LOVE LOVE LOVE VeraCrypt!!!
(I trust Nothing else of its type)
i
I didn’t switch to a TrueCrypt alternative when the application’s development mysteriously ended.
I acknowledge that VeraCrypt now handles issues concerning encryption setups that use hidden volumes. I’m not concerned, no hidden volumes, should it be for the sole reason that if I should ever be forced to open a TrueCrypt or similar encrypted volume chances are the bad guy would be aware of the hidden volume option.
I’ve read an article about this Open Source Technology Improvement Fund (OSTIF) claiming intercepted emails (which appear to have been deleted by a 3rd party rather than simply intercepted) relative to its VeraCyypt audit.
VeraCrypt disk encryption team claims “emails intercepted†:
https://nakedsecurity.sophos.com/2016/08/17/veracrypt-disk-encryption-team-claims-emails-intercepted/
I’m not naturally inclined to conspiracy theories but we all know that the “TrueCrypt Affair” was never resolved. I don’t know. Anyway, no FDE (Full Disk Encryption) nor hidden encrypted volumes here, just a plain 10GB TC volume with backups of never published Snowden files (that is not true). Highly confidential data is absent of any digital support, here.
Exactly Tom, I stayed with TC 7.01 up until about a year back. I use it (no hidden files or containers) on all our tablets/PCs/etc just in case one gets stolen or lost, we are old, we forget stuff. :)
If anyone is worried about there-letter agencies prying for whatever reason, they are going to need a lot stronger stuff than TC or VeraCrypt. I use encryption to protect our credit-cards and banking stuff from the eyes of local miscreants should that ever occur.
I changed over to VC after testing it for a while and finding they have cleaned up a lot of little annoyances when using TC. Things like Favorites actually working the way intended but not quite coded completely. Format and Console combined etc.
I like that you link the software’s (subject of your article’s) official address right at the beginning.
VeraCrypt is a true little gem.