WinAntiRansom Review
WinAntiRansom is a commercial program for the Windows operating system that is been designed to protect PCs against ransomware attacks.
Ransomware comes in two main flavors: programs that lock the PC down, and programs that encrypt files. Both have in common that they ask you to pay a ransom, usually in form of Bitcoin, to regain access to the PC or the files (with no guarantee whatsoever that you will get an unlock code after making the payment).
WinAntiRansom is one of the few programs available currently designed to deal with all ransomware threats on PCs running Windows.
This sets it apart from the majority of anti-ransomware tools out there that may protect you against specific types of ransomware only.
WinAntiRansom
Installation of the program should not raise any issues on 32-bit or 64-bit versions of Windows. Please note that the program requires the Microsoft .NET Framework 4.0, and that it is compatible with all versions of Windows starting with Windows XP SP3.
It will start to discover programs on the system on first start to add those to a whitelist. Whitelisting plays a major part in defending the system against ransomware. Naturally, you may review the list of programs discovered and remove them from being added to the whitelist.
New programs that you run on the system are picked up by WinAntiRansom automatically, and depending on how you have set up the program, added to the whitelist automatically if they were not blocked by the program's defense systems.
You may change the default behavior to get more control over the process but you will spend time whitelisting programs manually then. Whitelisted programs are allowed to access content protected by the program's defense layers.
Advanced mode enables you to define the layers a program has access to. You may for instance allow a program to access the SafeZone folder and its files, but not the Windows Registry.
You find an option in the system tray menu of the program to run any program as whitelisted, without whitelisting it. This can be useful to run a seldom used program once with whitelisting privileges.
Other helpful tools allow you to open a program's properties dialog and to display details about it.
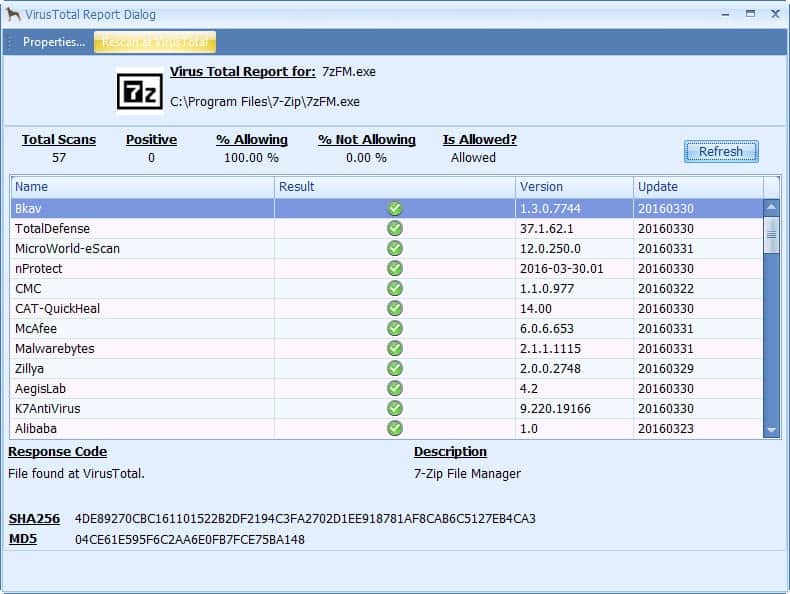
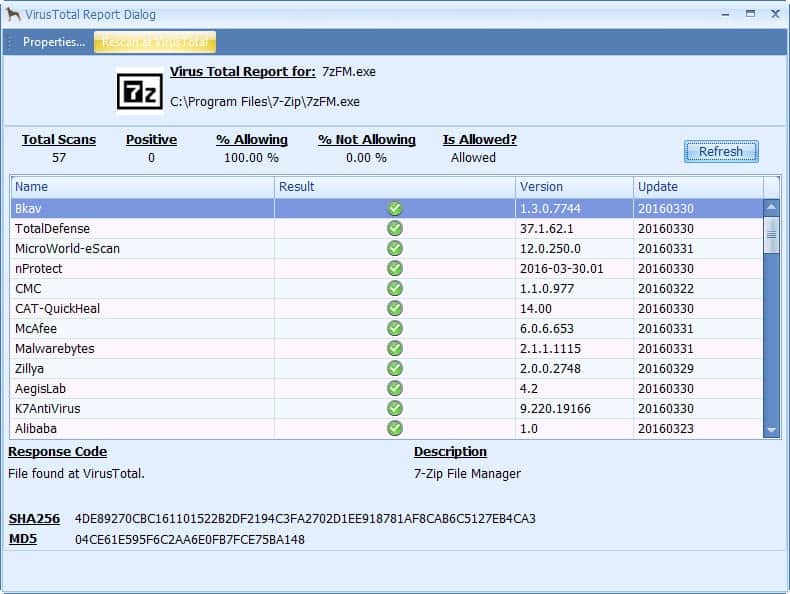
The details provided include MD5 and SHA256 hash values, signature and Windows Protected file information, and customer statistics which highlights how many WinAntiRansom customers are allowing or blocking the file. In addition, there is a "is allowed" suggestion displayed as well.
The main program view lists some of the information directly, for instance if a program listed there is signed or a Windows Protected file.
You may block any program from running on the system using the block feature, and check the access history which lists the last 500 times files or folders were accessed, and by which program.
WinAntiRansom: The layered approach
WinAntiRansom uses a layered approach in its fight to keep the PC clean from ransomware. There are four main layers of protection that the program uses to keep the PC clean:
- PreEmptive Actions: This layer attempts to identify ransomware directly by blocking programs from running on the system if they show signs of malware or ransomware behavior.
- SafeZone Actions: WinAntiRansom allows you to select a folder on your system that you want protected specifically. The program blocks program access to the folder except for applications that you whitelist specifically. The feature is a bit limited, as you may select only one folder, and cannot select a root folder of a drive.
- Network Lockdown Actions: The layer prevents programs from accessing the computer network if they are not whitelisted.
- Protected Registry Actions: The fourth and final layer protects important Registry keys from being altered by programs that are not whitelisted. You may add custom Registry keys to the program.
Layers two to four are designed to detect ransomware that slips by the preemptive layer. They increase the chance that ransomware will be stopped in its tracks depending on its actions on the system. For instance, a program that is not whitelisted may attempt to encrypt files protected by the SafeZone, or may alter important Registry keys.
If that is the case, it is stopped from doing so as it is not whitelisted. You can then review the access, and either whitelist it, or block it.
Some demos
So how good is the program and how does it stack up against other anti-ransomware programs?
Here are a couple of YouTube videos that demonstrate the program's capabilities:
Winlock Ransomware
Petya MBR Encryption
Verdict
WinAntiRansom is an excellent program that provides better protection against ransomware than any of the other programs designed for that purpose.
With better functionality comes more complexity often, but this is not the case here as everything is handled automatically for the user. This does not mean that you have to give up control though, as you can monitor and manage the activity at any time, and enable advanced mode for more control.
The program has been designed to block ransomware, but there is little reason why it won't stop other malware as well dead in its tracks, especially those malicious programs that share similarities with ransomware.
It is a complementary security tool all in all that runs well alongside traditional antivirus software.
The price is more than fair, considering that you can run the program on five of your own devices and pay once for lifetime access.

























I like WinPatrol programs. There approach is “Only allow programs that are white-listed (preferably with signatur certification), otherwise block the program and ask”. It is simply effective with low resource requirements.
I rather ask new persons for ID and/or “references” before let them into to my home. It is simpler than whatching for suspicious behaviour after I have let them in.
Against burglars and forced entrys I use “firewalls” to block and “security personell” (=antivirus programs) to throw the intruder.
So why not just ask for the programs “ID-signatur” berfore you or your computer let it run.
(XP is old and not has not any real security updates. I suspect that many programs are not withe-listed for XP now-days and therfore are “blocked” until the user white-list the program)
A lot of problems on Windows XP with these programs like WAR, MBAE and Hitman Pro. I have here Xp on a quad core and everything works fine here until I try these progs. Have good security (ESET, Comodo FW, Emsisoft AM, keyscrambler, Bitdefender AR, Crystal Security and good browser defense but that list is to long for here but the above programs I get not to work. Are very buggy on XP at best and I would on W10 but that entire OS is buggy. How many times I not find that there are settings chanced, programs missing,… it is not fun anymore.
I like Bitdefender myself. Some commenting here didn’t like the requirement to register the free version of antivirus. I simply registered and have never been pestered by any pop ups or emails pushing me to upgrade. So with the news seen on this blog about the anti-ransomware I installed it also, and am pleased.
Now about security and privacy – you just can’t be absolutely secure and private if you access the internet. There is always an interplay between safety and interacting with the internet. The absolute first necessity to back up all other measures is regular backups to a drive that is only connected when backing up or recovering to a backup. Next, I use Bitdefender anti-virus and anti-ransomware, Malwarebytes anti-exploit (Microsoft’s EMET has broke my PC in the past), and a flash disable addon button while browsing ALWAYS using Sandboxie. Then regular scans with ProcessExplorer configured to run VirusTotal, Glary, Fsecure, and PatchmyPC . I am sure others have better security than I do, but this represents the compromise between convenience and safety that suits me. A surprising thing to me is that Glary and SuperAntiSpyware are always finding a lot of tracking cookies to erase even though I use both the Better Privacy and Privacy Badger extensions.
Oh, and one other key element of keeping up to date with security and convenience protocols: regular visits here to see what Martin and the other computer cognoscenti are saying. Occasionally I, though less astute than many here, toss out what works for me (and what has NOT) that may be of help to others.
Bitdefender Anti Ransom lost vs old TeslaCrypt2: https://www.youtube.com/watch?v=EBi0HfLb5Yk (2:24)
In view of this program’s setup and background, I would without a moment’s doubt prefer Malwarebytes’ heuristically-based Anti-Ransomware — even though that one is still in beta. At least it has a more professional research department behind it, and on my own computer it proved to be intelligent (somewhat).
This particular post left me incredulous, to say the least. Sure, I am enough of a realist to understand and even accept the need for occasional sponsored posts, because this practice can help to keep a blog like Ghacks on its feet. However, I also think such posts ought to come with a clear “Sponsored Content” tag.
@Henk, there are reviews about products we dislike and yet this leads us not to believe sponsoring is the explanation.
There is maybe a sequence of events which led you to believe — when doubt is hardly expressed so explicitly — that this article had not been deliberately chosen by its author. I’m thinking of yesterday when the article “Anti-Ransomware Software Overview” had three fans express their enthusiasm and the author state then that a review of their WinAntiRansom would take place the next day.
Such a sequence, such an announcement are not common here and a reader quickly picks up the deployment of a blog, the habits of its authors, maybe that much that his curiosity may be triggered when he spots something new, different in an attitude.
There may be a much simpler explanation. Some events impose themselves and a blog author is happy to comment and explain them, thing Martin does excellently. But sometimes there is no event and, as a novelist in front of a white page, he has to dig, search, wander and wonder about what he will possibly find to make his job, and that is not always obvious. So when he feels that several visitors expressed an enthusiasm over a product this is for him the answer to the white page.
This is what I believed happened, Henk.
Maybe one day blogs will be written by AI (I’ve read that newspapers had tested this already) but until then a blogger is inevitably confronted to his preferences in the face of what he believes may be of interest for his readers more than for himself : we remain human! For instance it seems obvious that you, Martin, prefer GWX Control Panel to Never10, NoScript to uBlock, Firefox to Pale Moon yet you write on all, as a journalist. This is a major challenge for journalists, to remain impartial but at the same time committed to authenticity. Here in France there’s been a debate on whether or not political journalism should let the journalist express explicitly his orientations (implicitly is often obvious mainly with faithful readers) otherwise than in editorials only. French public seems to disagree on that. This is a true debate, not only in the political sphere.
I think you are both objective and authentic, Martin. You’re not the writer of anyone else but of yourself.
It is rather simple. Sometimes, when I write an article, I get comments that suggest another program. I will check out these programs, and if I like them, will review them. I don’t know every program available, and I appreciate it always when someone points out another program for a job.
This post has not been sponsored. I have received no monetary compensation for it.
If I would accept a sponsoring offer, it would be clearly marked as such.
@Martin, @Gabriel: If you want malware/ransomware samples for testing, you can locate here with Virustotal scan results: https://malwaretips.com/categories/malware-hub.103/
I question the validity of the videos, apparently the tester doesn’t share the “samples” with the other companies to validate her findings. So it’s entirely possible they have been modified to bypass to make her software look better.
https://forums.malwarebytes.org/topic/180897-new-ransomware-peyta/?do=findComment&comment=1029507
https://www.wilderssecurity.com/threads/emsisoft-anti-malware-emsisoft-internet-security-11-has-been-released.381438/page-5#post-2562552
Is this software written by just one woman?
If this is for 5 simultaneous devices then they’ve got a new customer :-). If it’s for the first 5 devices you install it on… I guess they haven’t. Which is it?
From the same folks behind WinPatrol, one of my must haves on every computer I own.
WinPatrol, you mean that thing with the barking dog, wouaf-wouaf? What a joke. I have a ‘WinPatrol Plus’ lifetime license I had bought in 2010 for a ridiculously low price, tried it once, removed it. That shouldn’t interfere in objectivity concerning WinRansomView, but subjectively it does. Anyway, good luck. I won’t even try it. This thing works with signatures, its not a behavioral analysis tool is it? Seems to me to have a rudimentary approach which can be effective but not sure it would be with sophisticated code attacking the Kernel for instance. Seems to manage top layers rather than deep ones. I may be wrong, advising nothing, don’t take my word, there ain’t any.
guess who, what was the purpose of that comment? just to waste time huh?
so why did you even comment? .. let alone, ask questions
@Tyrone, as I wrote above I’m not interested in WinAntiRansom, I did mention explicitly that this was not objective, implicitly meaning I hadn’t tested it. I added not to take my word, which was superfluous.
There are many, more and more anti-ransomware products on the market, and WinRansomView might be just fine, but I’m already equipped with this type of application.
Concerning your testing reference : you know, tests are to me less relevant than a deep-insight of the product together with users’ experiences. Take the “VolksWagen syndrome” for instance. ‘Wilder Security Forums’ has at this time 368 pages of debates concerning Hitmanpro.Alert, I’ve used the product ever since its version 2.x, it handles far more than the anti-ransomware feature itself, it is deeply integrated into my system, runs with Hitmanpro.Kickstart, both flawlessly.
Now, if I were searching for an anti-ransomware i’m not saying I’d put a veto on WinRansomView, maybe I’d try it. I’ll be frank : you have people you can’t stand in life without knowing how to say why. Same with certain companies I guess! I just don’t like WinPatrol, but because I have no valid reason I just write that I don’t like it and I do say : don’t take my word. I’m not stating, explicitly or implicitly, that WinRansomView is not ok, clear enough?
@Tom if you watch the video on Petya, the other products missed the detection totally. Regardless of methodology, WinAntiRansom did what it was supposed to do. Which makes me ask, what then is more important? the elegance of the solution or its effectivity? Just my two cents.
Hi Tom,
WinAntiRansom uses an artificial intelligence engine that leverages behavioral analysis, it does not use signatures.