Security Update MS16-023 installs new "Get Windows 10" functionality
Mixing security updates with non-security content is never a good idea, but it is particularly worrisome when Microsoft pushes new "get Windows 10" functionality on Windows 7 and 8.1 systems that one cannot get rid of without removing the security update itself as well.
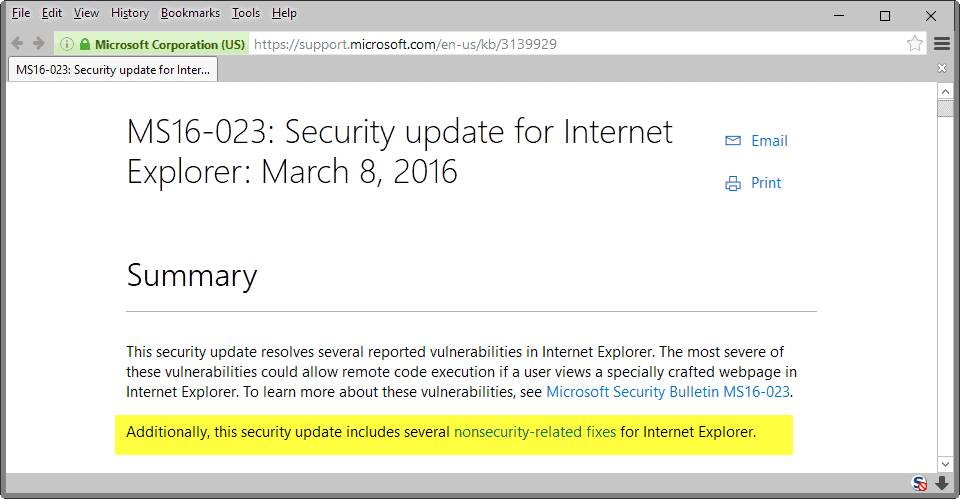
Security update MS16-023, released as part of the March 2016 Microsoft Patch Day, looks on first flance like any other security update Microsoft released for one of its operating systems.
In its summary, Microsoft notes that it "resolves several reported vulnerabilities in Internet Explorer", of which the most severe "could allow remote code execution" if users open web pages that were created to exploit the vulnerabilities.
If you read on, you will notice that the patch includes non-security fixes as well.
This security update resolves several reported vulnerabilities in Internet Explorer. The most severe of these vulnerabilities could allow remote code execution if a user views a specially crafted webpage in Internet Explorer. To learn more about these vulnerabilities, see Microsoft Security Bulletin MS16-023.
Additionally, this security update includes several nonsecurity-related fixes for Internet Explorer.
To find out more about these non-security related fixes, one needs to scroll down on the page where they are all listed:
- 3144816 XSS filter breaks submission of token for ADAL authentication in Internet Explorer 11
- 3144520 Poor performance in Internet Explorer 11 when you enter characters in text field
- 3144521 Internet Explorer 11 is closed when you use F12 Developer Tools
- 3144522 Users can't access Internet because proxy settings are overwritten in Internet Explorer 11
- 3144523 Empty textarea loses its closing tag in Internet Explorer 11 after conversion from XML to HTML
- 3146449 Updated Internet Explorer 11 capabilities to upgrade Windows 8.1 and Windows 7
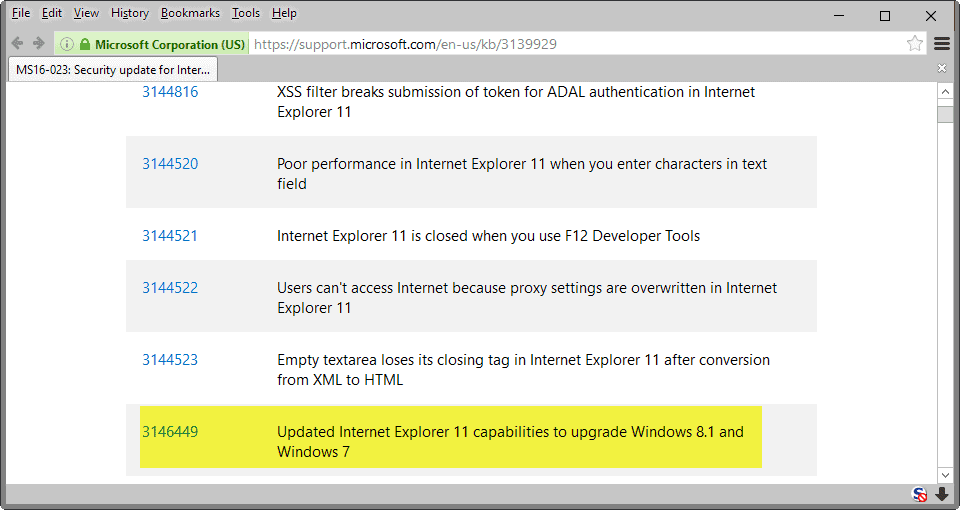
Of specific interest is KB3146449, which as it happens is the only KB entry of the six that is linked improperly.
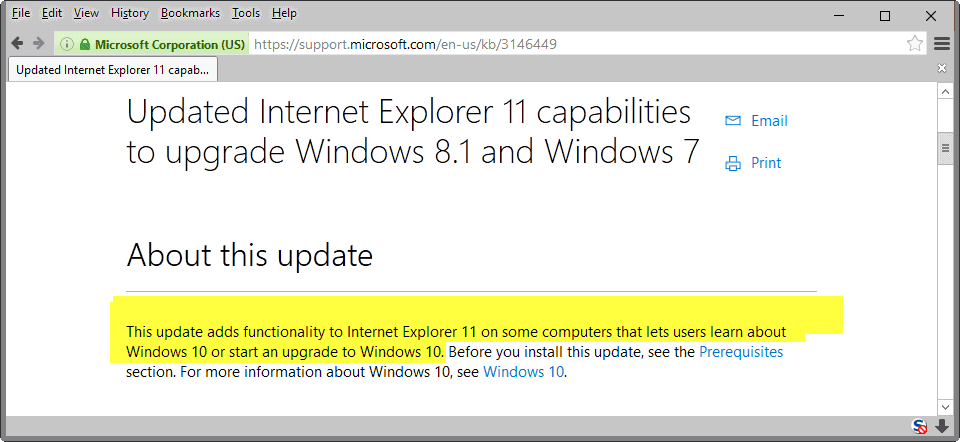
When you open the right page, you find the following information:
This update adds functionality to Internet Explorer 11 on some computers that lets users learn about Windows 10 or start an upgrade to Windows 10.
Microsoft does not reveal what this means, or what this has to do with Internet Explorer. According to Woody Leonhard over at Infoworld, the update pushes a banner on Internet Explorer 11's New Tab Page advertising the company's new operating system Windows 10.
This appears to be only the case for non-domain joined machines, and the banner is not displayed on all systems the update is installed on.
The big, big problem
The main issue with pushing Windows 10 offers this way is that users cannot remove them from their system as KB3146449 does not appear in the list of installed updates for the system as it is integrated into KB3139929.
This means that one would have to remove the security updates as well to get rid of the advertisement for Windows 10 on the computer.
Obviously, not using Internet Explorer would resolve the issue as well, but this may not always be possible and only a temporary solution as Microsoft may be inclined to push Windows 10 offers to other programs or tools of the operating system in the future.
What now?
Apart from regularly updating updates so that they are pushed anew to user systems to bring along with them the dreaded "Get Windows 10" offer again, Microsoft seems to have made the decision to tighten the screws even more by pushing the offer to its Internet Explorer browser as well.
If you think that this is the end of it you are probably mistaken.
There is nothing that you can do about it right now. While you could block KB3139929 on your system, you'd prevent security patches from being installed on it, and if you allow it, you have no option to remove the KB3146449 update individually which pushes the ads to Internet Explorer 11.
Maybe someone will figure out a way to get around this, by blocking the ads or somehow installing the security updates without the added fixes.
Now You: What's your take on this?

















Dedoimedo made an article referencing this one. See, Linux guys like your site. ;-)
http://www.dedoimedo.com/computers/windows-security-updates-with-ads.html
They certainly have crossed the line b. MS certainly does not have boundaries anymore in their desperation to push 10 to all users.
I am under the impression though that KB 3146449, which is baked into the IE security update KB 3139929, is not as bad as it sounds. It is a banner which appears on IE 11 browser, which advertises 10. Am I right?
I certainly do not use IE so as we need to patch the IE 11 browser as it is also used for other purposes on our MS OS’s . So I am inclined to download it.
Hi Tom Hawack, Pants & Kerframil
Thank you so much for all the comments and tips. I really appriciate.
Caschys Blog claims, that the nag-screen only appears, when msn.com is the startpage of the IE:
http://stadt-bremerhaven.de/microsoft-kb3139929-warum-ein-sicherheitsupdate-nicht-immer-ein-sicherheitsupdate-ist-oder-doch/
While I disagree with Microsoft’s decision to do this. I will say however that Windows 10 is a WONDERFUL OS. So glad I upgraded from 7. If you have not upgraded yet I highly recommend it. Especially while it is still free. Everything about Windows 10 is better in my opinion. VERY stable. And VERY fast. I love it personally. Although, as I stated before the decision to do this kind of upgrade thing in a security patch is pretty ridiculous.
Ive been testing out Windows 10 for compatibility with an eye towards rolling it out to around 300 seats.
Today Windows 10 applied an update while my workstation was on with work up on all three of my monitors… spreadsheets, email open, you name it. Apparently while I was away from my desk, it applied that update and forced several restarts, closing all of the programs I had open and losing all of my work (I had saved, but its the point).
It also seemed to have not just uninstalled the ENTIRE Windows Administrative Tools suite, but it went so far as to deactivate it within the ‘Turn Windows features on or off’ menu in Programs and Features.
Great work, Microsoft!
Im pushing out a Group Policy now to get rid of the upgrade icon and make it impossible to update. I usually wait a year after a Microsoft release to roll it out, and it looks like thats going to be the case again.
Personally I use Slackware, but the learning curve would be too great to roll out a Linux distro… not to mention compatibility issues with existing software. Ah well, you win this round Bill Gates!
Martin, It seems that your earlier advice for when somebody who does no want to update to Windows 10 to disable the Microsoft® – Upgrade function by using this preference (DisableOSUpgrade) is stile working fine.
This mount M$ attempt and earlier M$ attempts mentioned by you in outer articles are still not downloaded and installed because of your fix and because of your fix you are keeping me away from a Windows 10 “upgrade”.
It seem that the fix your explained in your January 8, 2016 article is still working fine because like i wrought here before all “upgrade” downloads where all not uploaded by main Windows 7 system.
https://www.ghacks.net/2016/01/08/disableosupgrade-prevents-the-upgrade-to-windows-10/
Great to read the article and everybody’s comments. I’m writing on Debian (8.3 Stable version) Linux, 64 bit, have been using for about 3 months on a 6 year old desktop machine. I was a longtime Windows 7 fan until the Windows 10 goofiness. I have found Linux to be easy to set up, faster, far quicker to install updates. It communicates well with my Android phone. I still keep Windows 7 to run my old scanner and it’s software, offline. My tech skills are low to moderate. I just want a quiet OS that lets me do websurfing, file a few .pdf articles, writing, email, edit/listen to music, edit pictures, keep track of passwords. I have found Debian to be rock solid reliable, easy to customize, lots of online knowledge from other users. I will probably replace the old scanner at some point rather than my new OS. Those who feel stuck with MS may not realize how easy it is to try something else.
What irritates me most is that I have a couple of older Win 7 systems that by Microsoft’s own determination, can not support Win 10 and the upgrade fails. Even so, these same systems are being bombarded with the Win 10 upgrade advertising. GWX, Win10 icon, Win 10 banner, etc. yet the systems cannot support it.
then turn automatic updates off, whats the big deal?
To all of you Microsoft bots. I didn’t have any idea how to use Linux, yet I installed Zorin with no issues whatsoever. It works like charm and looks the same like Windows 7.
I dual booted a laptop for several years with one hdd in it with Win XP booting GRUB. Never had an issue. I have run Linux on one hdd and Win XP and 7 on another hdd for as long as I can remember on my desktop. As in 2 hdd’s where bootloaders do not fight and overwrite each other. I set the boot drive in BIOS. I boot GRUB because it reads all other OS’s and boots them when selected. I can install multiple Linux distro’s on the hdd I run GRUB in the MBR on, and do. Granted there are some tricks there but not overly complicated. I run Windows on it’s own smaller ssd by itself. No bootloader fights and you can always boot an OS.
First thing I do is turn off any and all auto update features in every Linux distro I try to run. Most distro’s I have gravitated to over the years run apt as the package manager. It is a real good idea to let apt manage all updates not a baked in auto update manager made by the distro devs. Not saying they don’t know what they are doing. Saying that auto update on Linux is a bad idea in any form. Stable distros this is not so bad an issue. Testing or Unstable it is a very big issue. When update can break the system with one pkg looking for a lib that is not there yet it can render the system unbootable. Albeit, Stable variety distro’s should not have this problem. Auto Update features are driven by a couple of things. One of the biggest is the ease of use by former Windows users. My auto update is apt-get update/upgrade on the command line once or twice a week.
I have no Linux I have ever run that will not allow me to stop it phoning home if it was set to do so at install. I learned to use debootstrap several years ago so I do not suffer installers much anymore as long as it’s a Debian or Ubuntu distro. Nothing gets installed I don’t specify myself. I run Arch from time to time and it gets installed from scratch also. I can imagine the howls the Arch user base would produce if it installed anything besides what it needed to get to a plain old desktop gui at boot.
Nobody spying on me, nobody pushing stuff down my throat, no ads, no phoning home. I run Win 7 for gaming only. My daily desktop atm is LMDE. I still wish they were pulling pkgs from Testing but I can’t have it all. I could however boot my Debian Testing anytime I get ready because it lives 1 partition away from my LMDE. 2 partitions away from an Ubuntu install too. In a nutshell I control my box, not Windows or any other OS I run. Been a Linux user for near 15 years. Linux is easy now compared to 15 years ago. The move from Windows can be done if you want to, you just have to want to.
It’s all easier to me than going an digging through the kb’s at MS every time I run an update to see what they are trying to put on me I don’t want. I can look at my network monitor and see no activity and not have wonder who’s collecting what from my box. Keeps my blood pressure down. I will move to 10 but I will move to 10 when I am ready to do so not because MS is trying to force me into it. If most of the games I run weren’t so taxing on the system resources I would use Play on Linux for all games and never look at an MS bootscreen again.
@BobbyPhoenix
No dear boy (retaliatory sarcasm), we are cynical, realistic and aware of MS wanting to monetize us with telemetry.
I use Win 7 and have no intention of changing.
As far as your comment re Win 10 being superior to Win 7, some factual input would be good instead of your generalized, unverifiable, comment.
So, you like Win 10 because it:
– removes original drivers and replaces them with generic drivers which do not work.
– deletes users applications.
– causes BSODs and system freezes.
– will not install OS updates and crashes systems.
– uses excessive telemetry for future user monetization.
– is at beta development stage and requires a lot of work to become stable.
– has a browser, Edge, which has no extensions or add-ons and is worse than IE 6 to 11.
So, if you like using intrusive software which is behaving like malware, carry on.
To improve your knowledge of Win 10, read Alan Robertson’s post above. That IS factual input !
All these people crying that they will switch to Linux instead of 10 really makes me laugh. So they’d rather switch to a completely different OS that doesn’t run all Windows software (or even the software it can run, but not as well), is a completely different style and learning curve, and is hardly comparable to Windows in terms of overall usability in the “real world”, just to avoid installing the next OS from Microsoft for free which has been ten fold better than 7 for me. You all are a special kind of smart aren’t you?
@BobbyPhoenix, If people are going to have to go through a learning curve anyway, and there’s no doubting that either Linux or Windows 10 is going to take some relearning, if people have to go through that learning curve why would they choose Windows 10, yes Linux may not be comparable to Windows in terms of overall usability but what are you giving up for that usability? Do you really think that little extra bit of usability is worth giving up so much?
Yes, it’s hardly comparable to Windows overall usability because Linux is actually usable. You just set it up, use it and occasionally click “OK” to updates. And the user-friendliness can’t even be compared… Did you get tabs in your file explorer yet? Or you still need to have to open 10 folders in separate windows? Troll harder.
Whatever your skills you are expressing them as a fool, one that laughs when others consider him with an educated smile.
All these people as you say include far more than common unskilled users, they include well known bloggers, engineers, security & privacy experts. Whatever, it is one matter to discuss about the virtues and vices of an OS, it is another to elaborate on a non-security related + advertisement update included in a cumulative security update. Concerning the latter I’ve read several Win10 aficionados criticize the method. So there’s hope for you, my friend.
Just copy and paste this into an elevated Powershell prompt and reboot.
New-Item -Path HKLM:\SOFTWARE\Policies\Microsoft\Windows -Name Gwx -Force
New-ItemProperty “HKLM:\SOFTWARE\Policies\Microsoft\Windows\Gwx” -Name “DisableGwx” -Value 1 -PropertyType “DWord”
Problem solved
I have these settings in my Registry which perform as your Powershell lines (even more), and still don’t know if this why KB3139929 failed to install …
—
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\OSUpgrade]
“AllowOSUpgrade”=dword:00000000
“ReservationsAllowed”=dword:00000000
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\GWX]
“DisableGWX”=dword:00000001
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate]
“DisableOSUpgrade”=dword:00000001
—
I finally made up my mind:I will switch to linux ubuntu any time soon. found a community in the city, where I live.I jpopped over to see and liked it. they meet twice a month and offer support to install. All I have to do is bring along my laptop, and a “superuser” will sit next to me and guide me through the entire process of uninstalling windows 7 and install ubuntu instead. It’s a new world to me. I’m busy searching for vpn providers, critical stuff about the amazon icon by default etc. However I do worry about ubuntus abillity to run foobar and EAC. Any music lovers around who know about compatible programs ?
DeaDBeeF is the closest thing to foobar2000 but is a pale imitation thereof (say goodbye to the vibrant plugin ecosystem of the latter). As far as ripping applications are concerned, morituri is the one and only ripping tool available for Linux that has AccurateRip support. Again, don’t expect it to be on a par with established and well maintained applications such as EAC and dbPowerAmp.
Incidentally, I heard a rumour from a developer who is well known in the Hydrogen Audio scene that Peter Pawlowski is open to the idea of porting foobar2000 to OS X, as a result of his experiences in developing for iOS. Even if that should come to pass, I wouldn’t hold my breath waiting for a Linux port.
The reality is that Windows has a more vibrant application ecosystem. That’s what keeps me using it, despite the fact that Microsoft’s conduct of late has been sickening. That said, if you can keep your expectations in check, the above-mentioned applications may suffice for your needs.
Way to go b. Almost anything you want to do on a Linux distro can be done – there are tons of music rippers, tons of mp3 tag editors, tons of music players etc. I know, i know … you want a specific program because of x, y and z reasons.
I have 350+ portable software programs; take away a heap of Win10 tools (like Nirsoft, and no, I don’t have all of his) and it’s around the 250 mark. The best of the best of the best. I have a Linux machine next to me (I use Synergy to use just one mouse/ keyboard), and it’s going to be a long and painful, but insightful, experience to “migrate” them or find alternatives.
For example: for music, among other programs, I have foobar for quickly renaming files, checking bitrates, and the occasional cd rip to flac. I have mp3 tag (for all tagging purposes), I have freac for ripping or re-encoding from flac, I have mp3 Trim Pro (for removing leading and trailing silence), I have mp3 Validator (for checking for any header errors and removing any garbage in the headers and missing header info such as VBR seek times), I have LyricsFinder for grabbing and inserting lyrics id3tag, I have BMP Analyzer to insert the Beats Per Minute id3tag, and some other tools I won’t mention but which alert me to tracks that need splitting (eg last track+silence+hiddentrack) or alert me to an album put together from dodgy sources (such as different bitrates/stereo-settings) .. and so on. And then I have a pimped out WinAmp to really kick the llamas ass ….
Like I said, it’s going to be a painful, slow, long, drawn out experience – but the learning will be fun. A lot of these programs already come in Linux packages. Basically ALL of my portable software is free, a lot is open source, and a lot were made by “like minded people” (i.e into free/open source) who naturally gravitated to Linux int he first place – cogito ergo sum – Linux versions abound. And then there’s the ability to run Windows programs under WINE etc. What I can’t port or run on Linux, I will find an alternative. In fact, it’s a great chance to find even better software that isn’t available for the windows platform.
So I hear ya b, you want foobar and EAC, but seriously – they would be no big loss. There is always a solution. Good luck, buddy, and enjoy the ride :)
PS: Software replacements: google “software name linux” without the quotes, eg “foobar linux” and you’ll immediately hit a linux forum. Or google something like “top linux cd music rippers ” (without the quotes) and you’ll probably get a few links to respected magazine/tech sites “best of” articles. If you’re not searching from the search bar, the google suggestions are handy “top 10 linux ….”
Great! Any OS other than Windows is a new world for most of us, that is those who are not technically aware of computers. This also proves if needed how deeply Microsoft is associated with computer and Web. I’ve read that some users (none here!) believe Google IS the Web and so believing Windows IS the computer is a similar intoxication.
Happy for you, b (Let it be, let it be …. lol), you’ve made an intention a decision and that decision a fact : GOOD!
Hmmm. I’m on that path as well… at the decision level here, only. But, but, but ..
So how big of a security threat is this? I decided to just install it, but somehow my computer failed to install one of the updates and I have no idea what to do. I don’t use the GWX or whatever, but I did tamper around using Google before and don’t remember anymore how to fiddle with it.
My computer failed to install KB3139929 as well : is that the update you mention? You may have a look at your Windows Update / History of updates page to see the denomination of the failed update.
If we’re on common grounds the fact you “don’t use the GWX or whatever” is interesting because I believed the failure of the KB3139929 install was related to my “Anti-Win10” settings.
@James Andrews
You are entitled to write your opinions in this forum.
What you are NOT ENTITLED to do is to criticize Martin Brinkman and the hard work which he puts in to write beneficial articles and to make fair comment about the underhand and devious methods used by MS to force Win 10 down our throats.
I quote “This is a clear violation of editorial and journalistic standards that one does not come across in other news categories”.
I suppose that you read and agree with everything that Ed Bott writes in his paid role of MS troll/shill when he uses vitriolic criticism to flame other columnists.
Read Alan Robertson’s post above very carefully and digest its contents.
I make mine your comment/reaction, Gary D
There have always been minds to criticize information they consider biased and incentive, promotional.
Moreover a journalist is entitled to state his very personal opinion when the context deliberately reflects an editorial line. But Martin does not even take advantage of this opportunity (most bloggers do) when the content of his articles are descriptive and reflect the users pluralist opinions, enthusiasms and fears as well as eagerness to learn.
I don’t know how long we will have to say and repeat that Martin’s work here at gHacks is excessively professional and that his objectivity is confirmed throughout an extensive lecture of all his contributions.
Hello James, your comments are well thought out and considered. However, the article is far from biased – Microsoft has changed recently and it’s not for end users benefits. Justifying Micosoft’s actions by giving examples of what other companies are doing does not make it right! It wasn’t that long ago that Microsoft ran a campaign “Don’t get Scroogled” where they themselves took a stance against Google’s invasive privacy practices. I consider what they are doing now to be worse than what Google would ever dream up. I mean, come on, a keylogger in Windows 10…. Isn’t that what we would have seen malware do in the past? Upgrade now / upgrade tonight. UEFI lock downs preventing alternative OS installs. Skylake only compatible with Win 10. Back porting Windows 10 spying onto Windows 7. Updating Windows 7 users with security fixes that break software but will still run fine on Windows 10 (Corel Videostudio etc.). Excessive telemetry gathering…. I could go on. Talk about 1984!
Now, if you could wind the clock back and remove all these outright abuses of power and produced Windows 10 without all the shady practices and spyware, and charged for the upgrade at a reasonable price, then most people would be singing Windows 10’s praises. Instead Microsoft annoyed the user base so much so that they are now suffering from the “strong negative reaction” that you comment on. We’re all fed up with it and, yes, I’m now using Linux as a result. Good luck trying to convince me otherwise now that I have switched.
I fail to understand why there is such a strong negative reaction. Certainly, mixing security updates with non-security ones is not in MS’ tradition because of the needs of corporate customers to have those separated. However:
1. Mac OS X updates always include new features together with security updates. You can’t separate the two. There is no way. It’s all or nothing. I haven’t read any outraged articles detailing how snicky Apple is.
2. I remember when I had OS X Lion or Mountain Lion, it upgraded to the next version either without asking me, or simply after I quickly dismissed a dialog. Again, no outrage, no angry article on the Net about this.
3. iOS updates combine security and non-security changes together. Nobody has ever complained. In fact users are pleased to have to apply just one update, instead of hundreds like with MS.
4. Android security updates hav been very few, rarely issued standalone and only when something very critical happens. Otherwise, again you get security updates together with new features. Some of these new features include new Google services, some of which you might need to pay for in order to enjoy at their fullest. E.g. I remember that when I first opened Google Play Music, it offered two buttons: one labeled “Standard” And the other “Continue” or something similar. Guess what the continue button signed you up for.
5. Android and iOS app updates install automatically without asking anyone by default. No outrage has ensued. Only plesure on the comvenience offered. They don’t offer app updates that have only security content. It’s all or nothing.
6. On Android, Google Play Services are often updated both with security and non-security features in a single combined update. If you don’t update your Play Services, accepting both the security and the non-security changes, you might not be able to install new apps, or updates to apps from Google itself.
7. Chrome updates every 6 weeks. There is no separation between security and non-security updates. Further, you have no choice but to upgrade, older versions quickly fall out of support. In fact, techies and other users alike love it this updating model.
8. Chrome’s New Tab page frequently advertises new Google services, such as search by voice and Docs. No outraged articles, telling people that Google is collecting their private conversations and their voice signitures have appeared. Firefox advertises their newsletter and their other Web campaigns on the Firefox’ start page. No complains as far as I know. “It’s for a good cause.”
9. Windows 10 is a free upgrade for now and so unlike previous versions of Windows there is no immediate financial benefit for MS to advertise to users to upgrade. In fact, users might feel that they are getting a favor of sorts, because everyone is busy and people do forget to upgrade. Not everyone reads techy sites and knows about Win 10 and that the free upgrade period is about to end. Unless commenters on this site don’t want users to learn about MS’ free upgrade offer.
10. All companies may try to nudge users towards their goal. This is a reasonable and expected business practice being carried out by all brand advertisements you see on Facebook, Twitter, YouTube and TV. For example, no articles showing outrage that Coke is trying to nudge consumers to buy its drinks have been written. No angry comments in the comments sections of such articles have been written. I bet that brand advertising in e.g. Gmail has had more effect on your brain without you realizing it over the last 24 hours, than any nudging that MS might put in IE.
11. This article by using the word “advert” is making it sound as if MS is putting a giant banner in IE that doesn’t go away unless you give in to MS’ wishes. The article portreis MS as a bully. However, this is not true. The banner on the New Tab page is not in your face.
In conclusion, yes they shouldn’t have done this. But by over reacting, this article and the comments show clear bias against a particular company, whilst being blind to common practices across the whole of the industry and beyond, in fact being blind to advertising practices common to most companies, from the private to the public sector, from the coffee shop at the corner to the public transportation system, that everyone is being treated to without realizing or getting angry about them.
This is a clear violation of editorial and journalistic standards that one doesn’t come across in other news categories.
Give it a rest. Microsoft has been pushing Windows 10 obnoxiously hard, including to users with paid licenses for earlier versions of Windows that are still years away from end of life. I and many others have decided that we’re not interested in installing Windows 10. We have a number of legitimate concerns, including loss of control over what locally stored data gets automatically uploaded where, loss of control over system settings, loss of control over the timing and type of updates, and incompatibility with important legacy apps. Personally, I have had to work harder to keep Windows 10 readiness analysis and telemetry (a real CPU hog at one point), Windows 10 upgrade prep, and Windows 10 adware off of my Windows 7 system than I have for all other types of adware and malware combined. Basta. If Microsoft were an individual, it would be found guilty of stalking and harassment and hit with a restraining order.
In the broader perspective, Microsoft is a publicly traded for-profit corporation with an affirmative legal obligation to maximize value for its shareholders. If it can successfully kill Windows 7 and Windows 8.1 four and seven years before their contractual ends of life, respectively, it may achieve that goal by reducing support costs, despite offering Windows 10 as a free upgrade. (And even if it doesn’t succeed in killing Win7 and Win8.1 completely, it can still reduce support costs by doing an underfunded, crappy support job, further accelerating the exodus. The fact that Satya Nadella fired half of Microsoft’s testing and quality-assurance staff lends credence to this hypothesis.) Anyway, once Microsoft has achieved that goal to its satisfaction, either people will have to start ponying up for Windows 10, and/or Microsoft will be replacing or supplementing Windows 10 licensing revenue with a more Google-like revenue stream: trafficking in user data and meta-data. The difference, of course, is that (on a non-Chromebook PC, at least) Google gets only your online activity. With Windows 10, Microsoft will potentially have access to your offline activity and data as well. This is problematic for large classes of users, including lawyers, healthcare professionals, coders working on proprietary software, investigative journalists, and political activists, none of whom would feel comfortable or legally secure having, for example, their encryption keys and passwords uploaded to a remote server somewhere.
Finally, Linux doesn’t scare me. I used PCLinuxOS exclusively for a year around eight years ago, and I had zero problems. (Even the learning curve, switching from XP, was pretty easy.) I’ve used Linux Mint in VirtualBox more recently, and by far the biggest problems I had were VirtualBox-related. As far as learning curves go, I figure switching from Windows 7 to Linux Mint or Ubuntu won’t be a whole lot more difficult than switching from Windows 7 to Windows 10. Application-wise, I already switched from MS Office to LibreOffice a couple of years ago in anticipation of this eventuality. (Windows 8 was my wake-up call.) But if I really, really had to use MS Office, Office 2010 (which I have a license for) got a gold-star rating in Wine (free) in Linux Mint over a year ago, and it reportedly runs perfectly in CrossOver ($$). In fact, I can’t think of a single Windows-only program that I’d really miss. Well, maybe IrfanView … but I just saw that IrfanView gets a platinum rating in Wine in both Linux Mint and Ubuntu. So yeah, it will be different, and I’ll probably run into a problem here and there along the way, but you can say the same thing about upgrading to Windows 10. So, as I said, Linux doesn’t scare me. For now, I’m happy sticking with Windows 7 through end of life or until Microsoft starts borking my system with buggy patches. At that point, I will be jumping ship to Linux. Or what the hell, maybe even before then. I’m getting tired of having to vet Windows updates before I install them.
“This is a clear violation of editorial and journalistic standards that one doesn’t come across in other news categories.”
Sorry, but if something is nonsense it should be called it that way. And your last sentence is pure nonsense. Wondering why you get so upset about an article that does nothing else than keeping interested people informed about MS updates and what is hidden in it.
And if other companies behave as bad as MS this still does not justify MS or the others practices which are getting more and more deceptive. So we need people like Martin who keeps us informed about what they try to pull on the user. I am very greatful for his work it has saved me a lot of trouble, gave me excellent advice and extended my knowledge about computer, etc. in general.
I am sure Martin would be the first one to report and write about if MS would come out with more honesty, clarity and customer respect. He is not looking for the bad, it is just there. By the way, are you in any way connected to MS ?
1. “Techies” or any reasonable people dont use Mac.
2. Same as above.
3.Only clueless mindless sheep buy/use iOS devices
4.Theres is no good mobile OS, you pick the one thats least shite (Android) and yes people complain about android all the time.
5.Dont know what android you have been using or that you havent configured it at all, but no it doesnt, iOS see mindless zombies above.
6.See 4.
7.”Techies” or any reasonable people dont joint the google botnet.
8.Chromes is a “major” browser with no option to configure new tab, which is of course unacceptable, which people have been complaining since chrome came out. I dont know any firefox users who havent configured their start page to their liking and disabled said thing.
9.If you arent following things what happens with your computer, you are right to get into all kinds of trouble for yourself.
10. Puh-pleeeease.
11.You seem not to understand anything that relates around computers and security, like someone said this is new low and a thing that should have never happened.
@James Andrews, TBH I didn’t read the rest of your rather long list as you answered your own question in your opening sentence “mixing security updates with non-security ones is not in MS’ tradition”
If I were still using Windows this would infuriate me. I’d start start calling and emailing MS.
Make it known that this is not acceptable.
I agree with everyone that Microsoft is getting underhanded with its Get Windows 10 advertising. It almost tastes like a gov’t conspiracy! The shameful part of it is that we need to be careful of Microsoft just like any other malware.
I installed the update KB 3139929 and found a Windows Update in Manage Add On’s under All Add-Ons. I simply disabled it and haven’t had any issues.
This is all so Microsoft and the NSA can conduct espionage. Pushing this upgrade in a corporate environment wrapped in a faux IE security update is the last straw for me. I’ve been holding off on venturing into the Linux world, but this has pushed me over the edge. I will be running Mint as my primary OS tomorrow, also going to look into specializing in non-Microsoft areas as to distance myself from Microsoft. This will only spell disaster for M$, I am not going to jeopardize my career over it. Looks like lots of youtube training videos in my future.
@Wayfarer
You can download Win 7 Iso from MS legally :)
Please read Martin’s article “Download Windows 7 and 8.1 ISO images from Microsoft”
Martin published the article on February 17, 2016.
I used Chrome for the download.
Make sure that you use the RAW data from Pastebin.
I hope this helps you with your laptop.
NB read the posts from seeprime and zabouca.
I have – in essence – 3 computers if I don’t include the 2 Android tablets in the household (and I don’t include them for anything like serious work.)
My wife’s desktop runs WinXP – she likes it and as it isn’t connected to the internet, I see no reason to worry. She runs standard wp and dp packages that work well and have worked well for years. In fact it successfull runs more useful applications than my Win10 laptop.
My own desktop dual boots between Ubuntu and Win7. Despite MS besieging it with Win10 ‘updates’ – even they inform me that my Win7 desktop isn’t up to running Win10 (for reasons I don’t at all understand.) Fair enough – I don’t particularly want Win10 on my desktop – I just wish MS themselves would accept that. Thing is that my use of Win7/Linux started off at 80/20%. Currently it stands at 40-60 – in linux favour – and that includes one of the most useful uses of Ubuntu – repairing Windows.
My laptop runs Win10 – I haven’t had much option in that – my Win8 system ran so poorly I just gave in to the upgrade. But I – very seriously – do NOT like Win10. Though I’m not that upset about the upgrade because – quite frankly – I thought Win8 was rubbish too. In both cases my feeling is that neither Win8 or Win10 are actually operating systems. IMHO an operating system does just that and nothing else – it runs your PC and everything else is your own decision – hardly the position with any MS OS of recent years.
I’m an inch away fro installing Ubuntu on my laptop too – not dual boot, just Linux 100%. Despite the naysayers I increasingly find it does most of what I want to do on my PC. And if that isn’t 100% of what I need, it seems – increasingly – rather nearer to anything that MS offers. Not to mention considerably less nonsense about activations, copyright and all of the other rubbish users simply should not have to worry about.
I think there are some common English words that MS increasingly fail to understand. And they are ‘goose’ and ‘golden egg.’
Honest question, how do you figure “that neither Win8 or Win10 are actually operating systems”?
Because of the metro apps? Microsoft has always bundled starter software with their OSs. Actually I think all OSs bundle software, except maybe a few barebone distros.
I almost NEVER use Internet Explorer – as in probably less than ten or twelve times a year. Otherwise I use Firefox (going all the way back to Netscape) as my primary browser and Pale Moon as a secondary backup.
Besides those two – there are many other viable options, starting with Chrome – so it’s just silly to be bothered by this. I have hidden the entire KB3139929 update and will carry on with my Windows 7 system.
For the record, I probably will buy a new system sometime this year, at which point I will be happy to have one with Windows 10 pre-installed; however I really don’t want to take the risks with my current machine, which is a few years old.
@Straspey, this is a bit off topic but useful info.
FYI, It is STILL possible to buy Laptops with Win 7 OEM or Win 8.1 installed. :)
HP, Lenovo, Fujitsu all sell these with Intel i3, i5, i7 and AMD processors.
They are not Retail Laptops. They are sold to Business users.
Search the Manufacturers or Retailers web sites.
In the UK, Currys/PCworld is one place which will happily accommodate you. I don’t know about other countries but I would think it is the same world wide.
All you need to do is to fib about your job (EG say you are a self employed IT consultant) and make sure that you are talking to the right sales person (not the staff wandering around the retail display area) when you buy.
NB, this way of getting Win 7/Win 8.1 will stop at the end of October 2016 !
Bespoke PC Builders can also install OEM Win7/Win 8.1
Windows 10 is finicky, so I think that’s a smart move to wait, because by then it should be more stable. Hopefully when Redstone comes out (June I think) it will be more stablish.
It happens, ever since Windows 8 came out Microsoft has gotten all crazy with their updates and codenames. I think after “blue” failed to impress me for what it originally expected to be, I stopped following as much.
Plus this whole insider build is making things more confusing for the general consumer imo haha
@Andrew, My bad IDK that the code names were Redstone & Redstone 2, it’s number 2 that’s been delayed, very sorry for the confusion. :)
@Carky huh… I thought that was redstone 2 (or something like that)…. man I can’t keep up with Microsofts update schedules anymore
@Andrew, If Mary Jo Foley is to be believed, and there’s no reason not to as out of all the authors at ZDnet shes probably the most honest and has mostly been correct with her information, anyway if shes correct Redstone isn’t going to be released until spring 2017, apparently around CES 2017.
It won’t be intalled, if you have the no-upgrade entry in the registry.
Yes, it seems you are right. I have GWX Control installed to block all the pesty MS trickeries and it must have blocked it in the reg. Thank you for this very helpful hint.
Shame on me for not realizing what this little program is capable of. Well, I am old, so what !
Thanks for sharing this critical piece of nfo, Helen.
I can confirm it to be true. No upgrade reg entries,
no upgrade nags in IE 11.
I’m sick and tired of of Microshaft abusing their powers . and so on.. words fail me. one day M§ your day is over !
Listen up. If you want to move to Linux art time or full time . I would offer any help need for free, I would go as far as making video tuts , via my YT channel. Ive made the move to Ubuntu 15.10 full time, Though I need to keep up with news on M§ because my partner won’t move to Linux !
funny how ubuntu has “spyware” as well…
Not Ubuntu, Unity. And it’s the most boring argument in the world. Just plain trolling by people who don’t know how to point and click “disable”. Ubuntu also has security patches on the day when they are released, while on Mint you just have to wait for the next Mint release.
It can be turned off and from 16.04 will be disabled by default.
Try again..
What Microsoft does (and did over the last year) to push Windows 10 down people’s throat is totally unacceptable. Period.
And yes, in theory this should be a golden chance for Linux systems to get more users. But I agree with some of the people here that a 100% switch to Linux isn’t always as easy as suggested. The main bump here is not Linux itself (I myself think Mint is great) but the lack, sometimes, of fully equivalent user software.
Just this week I made my daily Windows 8.1 PC dual-boot, so it’s now half-Linux Mint, half-Windows. For 80% of my daily things, Linux will probably do fine. The problem lies in the remaining 20%.
I also have a full-Linux PC, but my third computer must remain Windows 8.1. Just because none of the media alternatives available for Linux, such as Kodi, is able to handle smart-card tuners for European over-air encrypted pay TV channels (something that Windows Media Center can).
Perhaps the LInux crowd is still focused a little too much on making Linux itself a better OS. Isn’t it already good enough? What they should really focus on right now, is to stimulate the development of a much wider array of user software that feature-wise can compete with similar software on Windows. Like, why is there is still no good streamlined Paint.NET alternative for Linux? GIMP is a way-too-complicated UI mess, while other ones such as Pinta keep lacking essential features.
However bad Microsoft keeps behaving, Linux will become a serious alternative for larger groups of ordinary users only when we get more Linux user programs that can seriously compete with equivalent Windows user software, with both the same ease of use and the same set of features.
Once we get at that point, I will gladly dump (and be able to dump) all last shreds of Microsoft Windows.
@ Henk:
Agree with what you say.
I for one, have also switched over to Linux Mint with a Virtual Box to run some legacy programs. For instance, I use a very old but very good data base (circa Win XP) for keeping track of my patient’s records. I suppose I could migrate over to a more modern data base ala’ Linux but I’m stuck in my ways and have a lot of time invested in having developed the data base. And all my charts are tied to the data base as well.
Fortunately for me, I don’t play computer games ( I’m an old fart and cut my teeth playing “Crosswalk†– does anyone even remember it let alone know what the game was about? It was a video game where the object was to drive your car and hit stick figure pedestrians that were crossing the street. The more you hit the greater your score. It might have been an 8 bit video game. )
My take on Linux software programmers is that because it is driven by volunteers (God bless them) they program what interests them, which is as it should be. This has, to date, created “holes†in what software is available. But market forces being what they are, eventually some enterprising Linux programmers will write code to satisfy what people need. Whether they charge a nominal fee or keep it open source will be up to them. Either way, us Microsoft refugees will benefit. It will take time but I think it is inevitable.
Are there no programmers here? You’ve never fixed multiple issues with one fix? Never had an error cascade on you? Paranoid much? I love some of the responses to this supposed issue here. “I removed IE”. And, I suppose if your finger nails grew too long you’d cut off your hand? “just use XP and you are safe”. Really? No hacker would target a now unsupported and newly vulnerable OS, would they? Oh, yes install Linux so you can browse the web and run some word processing program. It’s not like that isn’t something you could do on your phone. By all means build an 18 wheeler from scratch so you can drive around the corner for coffee.
I moved to Linux Mint 17 when M$ first started their windoze 10 nonsense and have never turned back. Everything I needed on windoze I can do on LM without issues.
Yes, linux takes a bit of getting used to, but once you’ve adjusted you’ll appreciate a world where freedom exists !
Join us, LM is free and has a great community to support new users.
Everything M$ does to annoy its users is strength to the linux community !
hahaha “M$” “Windoze” seriously?
Ever since Windows 10 was release, I have been seeing the absolutely lowest, nastiest side of Microsoft. Damn it Microsoft, who would have thought you could stoop so low.
Those of us who were around in the 90s know they’re not done strongarming the market yet.
Do you not know of the first browser war?
I did what I can do by not installing update #3139929. Considering mirco-crooks & others:
Guess this is the (not so) new way of treating customers. They all probably would like us will-less, moldable and without an opinion and rights. Well, they can eat my shorts.
I will keep my Win 8.1 and my eyes open when it comes to suckdates from “Them”.
Thank you, Martin, for keeping us informed about suckdates from “Them”.
If you can’t move to Linux immediately (or you did but need to keep a Windows boxen around) I would advise people to completely uninstall all versions of Internet Explorer and run the latest version of Aegis v1.16 (https://tiny.cc/aegisvoat) to protect your system from any further shenanigans from Microsoft. If you have any questions or feedback give us a shout on the main development thread on Voat. Good luck. :-)
Manjaro cinnamon come to me!!
Martin:
Now would be a perfect time for an article on the different versions of Linus.
I am ready to switch to Linux but do not know anything about the different versions.
I ran DOS before windows came out, so maybe I could learn Linus.
Thank you for your site!!
@Giddy: You can actually just run most Linux distributions from a USB stick without installing them. No need for virtual machines! Just download and test.
This might be helpful: http://www.phoronix.com/scan.php?page=article&item=15-way-linux&num=1
you are starting from wrong end, nobody should “use linux” or “learn linux”. it is OS, it is tool, it should run software.
gather list of software you use and check their availability or their equivalents for linux (.deb format). Check, whether remaining software could be run in “WINE” emulator. Then install some linux variant (“xubuntu” for example) in “vmware player” or “virtualbox”.
I would recommend starting up a VM and installing Mint or Ubuntu to get started. Once you get familiar with the whole linux method as a whole, then you can install it on your OS. After you get familiar with that, then you can start branching out to other not so popular distros.
I really wish there was a way I could see how many of you people actually switch to linux, especially those that have so much software on their windows system. I am not saying linux sucks, there’s a lot of good distros, but I think most of your comments are all BS unless you HAVE switched 100% to a linux distro.
Spoiler: Mac & most popular Linux distros also have upgrade notifications too.
One of those situation where every person has a breaking point. Where the advantages of Windows no longer outweigh the disadvantages of using Windows and being jerked around by MS. Beside tech people and like minded people who visit sites like Ghacks, I think despite the crap MS is pulling, the general computing public is no where near breaking point. Even if they are near breaking point there will be hesitation, if for example their work or schooling require Windows then they will put up with MS regardless of whether they hate Windows or not and not go through the trouble of dual booting or whatever.
My girlfriend for example just ignores the Windows 10 update prompt, I asked here if she wants me to remove the prompt, but it hasn’t bothered here enough for her to want me to intervene. She uses her computer for work and play and as long as it works she has a very high tolerance for MS antics. IF for example MS moves the “optional” update into the security section and the computer updates itself to Windows 10 without her knowing and prevents her from doing work (her hospital web system is based on Win7) then all heck will break loose.
@Andrew:
Ok, so by your logic we can agree that my comments are NOT BS since I have switched to Linux 100%. :)
But I agree with you that some people are prone to making idle threats without taking action. Still, from the comments I see here, it seems that many of the Linux-related commenters have already made the switch. (e.g. I take it at face value that Kevin, who commented on Blender rendering, has actually made the switch as he claims.)
Pretty much. If someone wasn’t 100% on windows and they already are using Linux (or OS X) exclusively, then I don’t think they would complain that much about what Microsoft is doing, because they aren’t reliant on their OS. It’s amazing how many people on the internet have said “When Windows 7 reaches EOL, i’m switching to Linux”. But for the people that said they would switch, and actually do, I commend them.
//Spoiler: Mac & most popular Linux distros also have upgrade notifications too.
I know nothing about macs, and never will. :O — But the updates in Ubuntu at least, can be set, auto, on or off. When turned on, each individual update can be selected BEFORE downloading. Plus they give a useful description of what and where the update is aimed. Just un-check the box if you don’t want it. AND these updates will not have hidden agendas as they are all in a secure and open source repository.
Not sure why you think the majority of Linux advocates here aren’t using Linux of some flavor. Any statistics to validate that opinion?
My problem isn’t linux users, it’s people who mouth off that they will move to linux like it’s nothing. Majority of these people don’t know anything outside of windows and their fone OS, so if they move to linux, they will most likely get frustrated and move back. Learning a new OS and how to utilize it takes a lot of time and patience, especially for an OS that’s not as consumer oriented as Windows or OS X
@Andrew, Macs have almost always historically taken a position of a fully controlled by Apple operating system with limited choice in what a user is allowed to do, they make any decisions for their customers so it’s understandable that Apple would have upgrade notifications.
As for your claim that “most popular Linux distros also have upgrade notifications too” would you happen to have any evidence to backup such a claim as i find it incredulous that more than a single Linux distro behaves in such a pernicious manner as Microsoft have been acting.
> Macs have almost always historically taken a position of a fully controlled by Apple operating system with limited choice in what a user is allowed to do, they make any decisions for their customers so it’s understandable that Apple would have upgrade notifications.
They do? Weird. Can’t say I’ve noticed that, as a Mac user. I think it’s true that Apple are very good at punishing you sometimes for not treading the golden path which they have so carefully designed for you to walk (iTunes and iCloud features spring to mind), but you certainly have options; OS X is simply an x86-64-based Unix-like operating system that actually works for normal people and runs commercial software, that runs especially well on Apple’s hardware (like Linux or Windows, the latter of which is supported by Apple), and can (and should) be treated accordingly. I wish more people would try it instead of trotting out the same old prejudiced nonsense. It might actually fit your needs, you know, and you’re the only one that loses out if you don’t learn for yourself one way or the other.
As for upgrade notifications about chunky new “Releases” of the OS: you get told, once. You open the Mac App Store, find the banner in the Updates section, right-click it, and choose “Hide Update”. And it’s gone, just like that. :)
I’m only here because I still occasionally need Windows, and though my main Windows VM is XP, sometimes it can only be Win7 or better. In recent times, I have been more disposed to Windows because OS X is starting to lose its edge for advanced users (its graphical applications don’t really make up for the loss of functionality and lots of bugs), and it’s clearly being dumbed down to appeal to iOS users, commensurate with its growth. I’m fairly sure Apple would rather not maintain OS X at all, to be honest. I couldn’t have picked a worse time to think about going back to Windows, really. And Linux, sadly, is not an option because I need accessibility tools (screen readers) that Linux just doesn’t have outside of textmode (I run Linux on my servers).
From a business standpoint, it makes sense, as they want everyone to utilize their new universal app platform and make more reliance on the windows store (and mobile platforms)
That being said, it’s microsoft, they been fudging things up since they been trying to catch up with Apple on the mobile scene. I never said what microsoft was doing is smart, just from a business sense I can see why. In other words, their end result makes sense, but they are constantly tripping (screwing up) on the way.
I think mint and ubuntu has notifications, from my memory though it has been a while. But Android does have more of a nagging method.
@Andrew, I must be missing the business view making sense part as i fail to understand how strong arming people onto a single platform would make sense, especially when getting everyone onto a single platform is impossible until 2023 when Windows 8.1 is no longer being supported, it’s not a matter of numbers it’s a matter of a date.
I also wouldn’t class Android as most popular Linux distros, yes it’s a popular distro but it’s a single distro, most distros (afaik) don’t have upgrade notifications.
As much as Microsoft? not unless you include Android. But Microsoft IS trying to get everyone on the same platform because from a business view it makes more sense. Plus people will probably complain that they missed the free upgrade once it expires.
My problem is people blow their mouths off talking how they will change over to Linux like it’s a simple switch, or like Microsoft actually reads comments on this site. If they want to complain to Microsoft, they should complain directly to Microsoft. If they are so dedicated to switching to a Linux distro, then they should just go ahead and switch now, not wait until EOL of Windows 7 or whatever, they should just install it now. If you want to really learn an OS, you have to jump in the deep end, not put your toes in.
Did it 9 months ago, Xubuntu. No problems whatsoever after it took me 2 weeks to get used to it and learn how to do things. I can do some stuff I couldn’t before, better, safer (I still take safety as seriously as if I’m using Windows) better looking and more efficient, and of course I can’t do a few things I used to be able to. Thankfully I’m not a gamer. But when I try using Windows again it feels like going to war.
And I’m actually happy when I get updates. Getting all updates from the same place instead of manually checking, I feel like Ubuntu is spoiling me. :-)
@Andrew this is how some people show their disaffection
this should mean something
windows is not the future
the future is for open source
this is a fact
and I’m looking 4 the future
if I will have the same interests and still alive
I will be happy to see microsoft fall
MdN, and then in no means does my comment refer to you. I am glad xubuntu is working for you, and I do hope more people get on Linux.
Actually, in light of all the crap M$ is doing lately, I tried installing linux on an old win7 machine, for the first time ever. I wanted to have a dual boot machine, at least at first. The live CD worked great (Mint 17), but I ran into a lot of trouble installing it – too much for me. I was very disappointed. Worse: when I erased the linux partition, I couldn’t boot at all. Eventually I had to reinstall win7…
So that’s my linux experience for now. Not good :(
What happens is that Grub gets installed to the MBR. When Grub loads, it also loads some data from the Linux partition. When you delete the Linux partition, grub can’t find that data, so the system breaks. This is easy to solve by booting a Windows DVD, going to a command prompt and issuing a “bootrec /fixmbr”. No fresh installation is necessary to fix Windows.
Its kind of a bad design. I would prefer a bootloader that fits entirely in the MBR, but I guess they can’t fit support for all those file systems and stuff in such a small space.
yoav, I was on the same boat as you. For some reason the live CD (mint as well) worked great on my machine, but once I installed it, I could only use 2 of my 3 monitors. I tried everything from looking for a new driver to trying different configurations, but nothing worked. Shame too, I really wanted to try to use Linux more.
That’s the thing, people will say they will move to linux without ever doing it before, but they will run into something, being Gaming, driver/hardware issue, or a piece of software that they can’t find or isn’t good enough as their Windows counterpart.
What’s my take on this? I’m glad I’m on Linux, where the OS producer doesn’t play shady or underhanded tricks on me and I can render out a 12-hour project in Blender without fear of unwanted reboots, sans a power loss or legitimate software bug causing a crash.
It was bad enough when KB3035583 came back in spite of it being removed and told to stay gone. Some users really can not upgrade to Windows 10, because they use special software like a screen reader, which isn’t updated to run on W10 yet. Now in addition to dealing with the gwx pop-ups that most people do not understand how to get rid of, these users will get ads in IE.
“without fear of unwanted reboots” – to be fair, you can configure Windows to not do that
I knew this was gonna happen anytime soon as the 1 year free Windows 10 Spyware upgrade is about to end. And viola! Integrating Microsoft home baked valid malware into their own security patches. Just how desperate are they and I thought Windows 10 is installed on billions of computers worldwide or is that just an overexaggeration/hyping coming from Microsoft? Seems they are killing themselves even more nowadays rather than make a pure desktop os like Windows 7 with no Mobile junk integrated.
KB3139929 did not manage to install on my Windows 7. It is listed right now on my Windows Update History as “Echec” (failed, failure in English?).
First time I encountered such a problematic Patch Tuesday, system rebooted twice, couldn’t manage to install an update, which happens to be indeed KB3139929. No idea why it failed, maybe because of anti-Win10 upgrade Registry settings? This is getting confusing, complicated especially for non experts.
Therefor, no KB3146449 but no “valid” update of KB3139929 as well. Anyway I *never* run Internet Explorer, never, but some applications calling the Web, may. I just don’t know what to do with this insane company and its terrorist attitude.
Hmmm. I’ve set Windows Update to “notify but let me decide whether to download and install,” and I’m running … no, cancel that. I was going to say that I’m running GWX Control Panel. It’s installed, and it’s set to autostart at logon, but it wasn’t running! Well, I started it manually, and it’s running now. Now isn’t that curious. I guess “something” prevented it from autostarting and that from now on I might need to manually start it after each boot and check on it from time to time to make sure it’s still running.
At any rate, the cumulative IE11 “security” update installed just fine on my Win7 machine, but now I’m guessing GWX Control Panel wasn’t running at the time. As for the adware in IE11, it’s pretty sneaky and sleazy, but seeing as the only time I ever use Internet Explorer is to update Adobe Flash for IE and when a site absolutely will not load in Pale Moon or Firefox, I don’t really care. All any Windows 10 ads are going to do is make me dislike Microsoft even more than I already do … which is saying something.
By the way, I promptly installed the cumulative IE11 update (because it was billed as containing critical security fixes), the .NET Framework security updates (because they’re less likely to cause systemic harm if they’re buggy), and the Malicious Software Removal Tool (because I don’t recall that it has ever screwed anything up). I’m waiting a bit longer for negative user feedback on the rest, however. I’m not sure I trust the single non-security update (to Windows Update) not to incorporate Windows-10-related crap, and I no longer trust systemic “Windows 7” security updates not to bork my system. My online behavior isn’t super-risky and I have semi-decent anti-intrusion and anti-malware utilities, so I can afford to wait a bit and see if other users start screaming bloody murder about any of them.
PS: Hey, do you think the Malicious Software Removal Tool might have been reprogrammed to turn off GWX Control Panel or prevent it from starting? Just a thought…
@ Tom Hawack
I stopped using IE 11 2 years ago by disabling it. It was not as good or as versatile as Cyberfox or Google, especially Cyberfox.
You are probably right that anti Win10 settings are screwing the install.
I discovered something strange today in the hidden updates.
BEFORE I hid KB 3139929, there were 9 IE cumulative security updates listed. They were hidden because there is no point installing 450 MB of updates for unused software.
AFTER I hid KB 3139929, ALL the previous IE updates had disappeared from the list ??!!
Weird.
Unfortunately disabling IE11 as mentioned above by Mike March 9, 2016 at 9:43 pm #,
“In Win 7: Control Panel > Programs > Turn Windows features on or off then untick Internet Exploder 11 hit OK, wait. Reboot. No more IE.”
isn’t enough to prevent apps from using IE routines to access the Web, therefor maintaining the necessity of having IE updates correctly maintained, as mentioned by other users here as well.
About this March 2016 Windows Updates : here (Win7 x64) I had 10 updates including 3139929 and 9 got installed, 3139929 stated as failed as I said. No idea therefor how the fact of hiding 3139929 as you did led to other IE updates’ disappearance. Odd but not new : I notice updates I’ve hidden previously no longer mentioned in the “hidden list”, as well as updates I never hid appearing in that list. I just don’t understand any more. Like in the Addams Family TV series,
“Their house is a museum – When people come to see ’em – They really are a scream – The Addams Family.”
Replace Addams by MS and you’ve got how I feel it.
Good luck, Gary D, Good Luck to all. Women and children first, get the lifeboats ready.
just use XP and you are safe
Safe is just a deceitful word …unfortunately
but I agree with you about how better the old OS is
compared to the new resources monsters and privacy invaders
about the IE just don’t use it and leave it alone
or use some linux virtual machine for internet
Thanks for the heads up, Martin. I just uninstalled IE from the system. MS pushes, I push back. I am no longer a respected customer, they have made me their combatant.
Just for confirmation of what others have said about not being able to remove IE hears a link to a Windows Development Blog that goes into more details if anyone is interested.
http://blogs.msdn.com/b/patricka/archive/2016/01/08/if-i-remove-or-don-t-use-internet-explorer-8-9-or-10-can-i-avoid-upgrading-to-internet-explorer-11.aspx
Most valuable information, Corky, for anyone having disabled IE and wondering if Windows Update nevertheless updates IE’s components. The article states:
“When you apply security updates to the PC, the Windows components as well as the hidden IExplore.exe are serviced. Therefore, if you re-enable IE, it should be up to date.”
Thanks for the link.
how that? IE is integrated into system, you cant uninstall it
Even if aware that — as Hy reminds it — other non-MS installed programs can make use of IE, I’ve just disabled it. I never used it but the symbol perhaps more than the effectiveness of disabling a major OS component that appears to be used by Microsoft Update to combine a sneaky, *non*security* KB3146449 within it’s KB3139929 (MS16-023) cumulative *security* update for IE11 is a relief.
And while I’m at it, adding a Microsoft dedicated I-BlockList to my running PeerBlock application is just a thought and a fingertip away : that means blocking access to all Microsoft urls (except of course hardcoded DNS lookups via the dnsapi.dll). I admit I am deeply, truly shocked, revolted by Microsoft regarding its Windows 10 invasion policy. Surprised as well as I wouldn’t have dared imagine the company would tie that policy with security issues.
@Mike, no more access to IE, but it’s still a part of the system and many programs still use it for the html rendering
@Hy “IE should be kept patched”
yea, you are right, some of those security patches apply to HTML rendering engine – that is used by hh.exe in current help format files (.chm).
only solution then – extract .chm with something (7zip for example) and open it manually in another web browser, but then you will lose table of contents from left tab.
Be careful, though…
I, too, keep Internet Explorer disabled and never use it, but as lolz says, IE is integrated into the Windows OS. Even if you never use IE as a web browser, the Windows OS itself and even other non-MS installed programs can make use of IE. And thus there remain potential attack vectors for unpatched IE vulnerabilities to be exploited.
Even if you never use IE to browse, even if you’ve disabled it, IE should be kept patched. That is, at least, my understanding of it. Someone who knows more about this can clarify or correct if necessary.
Just last month in Windows Secrets newsletter the redoubtable Fred Langa had this to say on the matter:
“Even if you always use Chrome, Firefox, or some other non-Microsoft browser for surfing the Web, Internet Explorer is on your PC and its vulnerabilities could affect your system’s overall security and performance.
Never using Internet Explorer won’t keep you safe; some deep-seated IE components can be automatically used in routine and critical Windows processes such as Windows Update.
Therefore, on all Windows versions, IE must be kept up to date and secure. Trouble is, starting this Jan. 12, only IE 11 (and Edge) will receive future security updates on Windows 7, 8.1, and 10. (Vista users get a brief reprieve: IE 9 will be supported on that OS until April 11, 2017 — Vista’s official end of life.)
All other versions of IE are now unsupported, and thus potentially dangerous to use.”
“you cant uninstall it”
Except I just did. In Win 7, “turn windows features on or off” – untick IE and apply. Gone.
After doing so, go into “C:\Program Files (x86)\Internet Explorer”, and you’ll see iexplore.exe is no longer there. Some remnants remain, but Windows Update will no longer offer updates for IE.
In Win 7: Control Panel > Programs > Turn Windows features on or off then untick Internet Exploder 11 hit OK, wait. Reboot. No more IE.
“You can’t run, but you can hide”. Delete all IE links and shortcuts. That’s what I do when I install Chrome or Firefox on older customers computers, with their approval.
Who cares about IE
I can’t believe there is a huge number of Ppl still using this garbage
But the truth is obvious
the stupid ppl on the planet are too much more than the smart ppl
otherwise microgarbage won’t be able to make fun of us like that
if this is not the truth then the company is very stupid for not noticing what happening on the net
the lost trust is not easy to recover and for some ppl it’s impossible
IE-patches are also about HTML-stuff used in seemingly unrelated programs.
If it’s that important to have the latest version, where I can install IE11 if one of my PC’s still has the older version? Which is the latest upgrade for it that doesn’t have any hidden W10 bs integrated in it?
“the stupid ppl on the planet are too much more than the smart ppl”
Wise words, however look at it this way:
The stupid people are unable to install operating systems themselves and will care very little as long as the OS works for browsing the web etc. They don’t care if it’s Microsoft or Linux or iOS or Android. As long as they can check emails, browse the web, watch Youtube etc. they’re happy. As far as privacy issues go they’re naivety is staggering – they would quite happily reveal every aspect of their lives to Microsoft like some creepy stalker. If you ask them if they want to live in a glass house, however, you get a different answer and suddenly privacy is an important issue.
The smart people realise that Microsoft is turning out to be worse than feared and is gobbling up every shred of information that they can grab about you to exploit for their own personal benefit. You are now nothing more than a commodity to be traded. The smart people having realised this are able to install Linux and overcome transition. They look after their computers / laptops / tablets / phones, family members computers, friends computers, work colleagues computers and because they are smart, other people listen to them. They have influence at work and they have the ability to adapt and change easily.
The smart people, although in minority, have a much larger influence to make the changes necessary to prevent this corporate privacy violation onslaught. I myself look after seventeen machines, five of which are still running Windows. The rest run quite happily on Linux Mint.
Now it’s your turn.
Must have been a last-second-decision, as the link on “3146449” currently leads to the KB-article of the update above it.
And yeah, it’s a shabby move. Now you can’t even trust their security-updates to be adware-free.
With Billions of dollars to be gleaned at the cost of the user’s Privacy, nothing rates higher. On my lone win8.1 laptop, I removed IE right after the install. So far that laptop has escaped the forced updates etc. But, as Martin stated, I too am confident that will not always be so.
More people need to take a long serious look at Ubuntu or Lubuntu ( a trimmed Fork of Ubuntu). Not perfect, but certainly at the pointier end of open, honest and ethical. And, surprisingly easy to migrate to from windows. Take the small leap, or should I say, “hop,” as some Linux platforms are no longer a leap :)
Linux Mint is also very win-user friendly but a little farther removed in my opinion. Did my annual test of Mint last week and it is surely getting up there with Ubuntu and strains.
More than ever, it seems like blocking “anything” coming from MS is a very good idea, at least until you’ve had ample time to fully research the matter before accepting it. A trusty firewall that is properly configured is probably a Windows user’s best friend at this point.
I totally skipped the Vista and Win8 upgrades, and so far see nothing that makes me want to even come close to upgrading to Win10. For that reason, I’ll stay put with Win7 on my Windows computer and continue to run Linux on all my other machines. I’ve been running Linux for about 16 years now, and it’s always been very good experience for me, when compared to Windows operating systems.
This is not pushing anymore it’s twisting ones arm. Going full to Linux (Mint or Zorin will do it)
MS won
i will upgrade my windows 7 machines
to linux
I’ve been considering an offline-only Windows PC for gaming and Linux for everything else. I’ve been running various Debian distros for the past ten years and really prefer their interface over modern Windows.
@Anonymous:
Steam on Linux was the first big push for Linux gaming. But you may also have heard about the recent release of the Vulkan API. This is going to be a massive step forward in the next couple of years. It’s a cross-plattform, open-source, low-level gaming API that is backed by just about EVERYONE except Microsoft. There are already Vulkan-compatible drivers (in beta release) for Nvidia and Intel GPUs. All that remains is for the game developers to start turning turning out the games – and they have indicated that this is coming. Maybe – just maybe – this is why Microsoft is now trying to place all kinds of restrictions on game developers who use the Windows store.
I’m praying for Linux gaming to catch up to Windows. We’ve certainly come a long way. Right now almost 15% of my Steam Library is compatible with Linux. And for the old GOG stuff, you’ve got DOSBox and ScummVM. Certainly WAY better than when I first started tinkering with Linux.
can you recommend media player in Linux which can load whole mp3 into memory before playing? (i.e. not seeking harddisk while playing)
Steam works on Linux :)
A very good idea, except that many games & services practically require internet connectivity to function, or to fully function. I suppose you could be connected but not use a web browser on that PC?
I’m happy enough with Win7 atm. But I’m also researching and preparing what I will need to do to switch to linux if Microsoft forces Win10 onto my computer. I can’t believe the underhand methods they seem to be using.
“But I’m also researching and preparing what I will need to do to switch to linux if Microsoft forces Win10 onto my computer.”
I already did that when the question was whether I should upgrade from Win XP to Win 8 – and I never regretted that once. My entry point to Linux was Ubuntu 14.04, and a week later Xubuntu 14.04 because my computer was too ancient for nice graphics and stuff.
There was almost no application that I could not replace with something that runs on Linux, and I could even take some Windows applications with me: MS Office 2003 (Windows version) – Linux emulates it nicely, and it runs twice as fast as on Windows.
Try it and give yourself some time. As for me: I’m not a nerd, but all went well and I would NEVER go back to Windows again. I’m glad as hell about it whenever I read stuff about Windows 10 and stuff.
I used to really enjoy Windows 7, when I didn’t have to worry about Microsoft jacking it. It had its annoyances (like no user-control over focus-stealing and poor scaling support, off the top of my head), but I didn’t have to think about it all that much. Since the arrival of GWX and a rash of seriously buggy Windows updates, I’ve had to disable automatic Windows updates, install GWX Control Panel, and vet every single update Microsoft proposes. I still enjoy Windows 7, but only between Patch Tuesdays and Rollup Whatevers (the third Tuesday of each month? — we don’t know).
I’m not a gamer and very little about Windows 10 appeals to me. If it supports better scaling than Windows 7 on high-resolution displays, that’s one real plus. But I’m horrified by its reported default uploading of things like encryption keys and passwords to Microsoft servers, forced installation of updates, and overwriting of custom system configurations.
I’ve definitively decided that Windows 7 will be my last Microsoft OS and that I will be switching to Linux, probably Linux Mint Cinnamon. (I’m ready for it. My most important programs are already multi-platform.) If Microsoft throws up one more roadblock to my “quiet enjoyment” of Windows 7 on my current computers, the switch will take place then. Otherwise, it will take place when I get my next computer. (Besides, according to what I read, it could be a challenge to install Windows 7 on systems with Skylake and later chipsets, and Microsoft will be ending extended support for Windows 7 on those systems in June 2018 instead of January 2020.)
No need to go to Linux, I would never give up a great OS like Win 7.
There are Tools available… One is from Microsoft if you are running Win 7 Pro
you can use the Group Policy Editor after getting this update from Microsoft…
https://support.microsoft.com/en-us/kb/3080351
Or you can use GWX Control Panel…
http://ultimateoutsider.com/downloads/
This does not address the Ad in IE But will prevent Win 10 from being installed.
Then again who really wants to use a crippled browser like IE anyway, I use Firefox.
Good luck to you all.
Here is an update to what I said on My Post from March 18/16.
This New tool is especially good for people who do not have Win 7 Pro.
This is from Steve Gibson from GRC, found out about it on his Twitter Feed…
Its called Never10…You can download it here…
https://www.grc.com/never10.htm
These sort of tactics really wind me up, and that’s even as a Windows 10 user. So, I can’t imagine how p*ssed off the people this is happening to must be. Especially for those who for example run Media Centre PC’s where upgrading to Windows 10 would remove Windows Media Centre.
I really don’t understand Microsoft’s logic, as these sort of tactics will not make people who have already gone out of their way to deliberately disable Windows 10 from installing to suddenly ‘cave in’ and install it. It will have the total opposite affect and make them look for an alternative Operating System to use in the future. This sort of thing sticks in peoples memories and has more long term effects on future purchasing decisions than they realise.
They are being outright coercive at this point, which is deeply troubling. A quick and easy way to try out Linux would be to install a ‘live cd’ on a flash drive and just boot it. Then you can see how much of your ordinary work flow can be done without having to do anything to your original installation.
I’m in a process of trying to switch myself. Haven’t used Linux for about 20 years, and back then it was a toy. Unfortunately I need quite a lot of Windows software, including Visual Studio, Lightroom and Photoshop. While VS is easy to push into a VM, Lightroom and Photoshop are next to impossible to run either in a VM or on Linux. So, while it’s true that some of the basic tasks like browsing, video or music consumption or word editing can be equally done on Linux, anything more advanced presents a problem.
If only Adobe has released their products for Linux!
Same for me. And use VM for programs that are not aviable on linux.
Most of those are called “games” on my system. All other things I can do on Linux. Its a convenience to not have to switch between them, but having windows in a VM will make my games unusable.
“Mixing security updates with non-security content is never a good idea” and even worse when the non-security content is an advert. Sad how low MS will go.