Beware, your Android phone might come with preloaded spyware

Computer users know for quite some time that buying new PCs does not necessarily mean that the computer is clean, lean and ready for use immediately.
Most computer manufacturers push so called "crapware" on PCs, trial software for instance, to increase their bottom line while only a few don't or want you to pay extra for cleaning the crapware that they have put on it.
There have been cases where these were classified as spyware, think back to Lenovo's Superfish fiasco for instance.
Things are identical on most Android devices as you don't get a stock operating system usually but added apps and modifications that the manufacturer of the device preloaded on it.
A recent study by Germany security company G DATA suggests that at least 26 different Android devices shipped with pre-installed malware in the past two years.
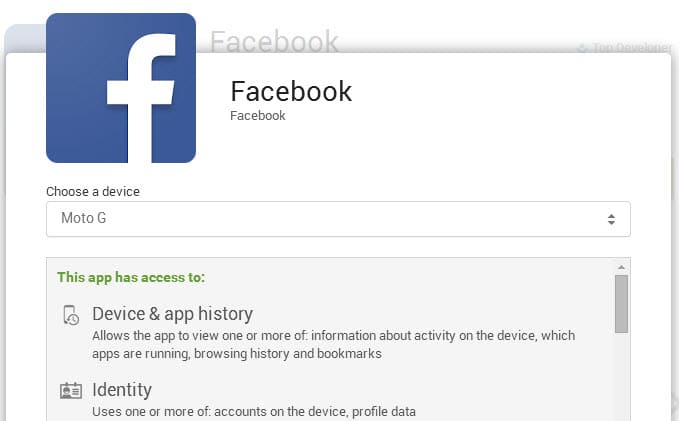
According to the report, malware is added to popular legitimate applications such as Facebook. One core difference between the malware-infected version of Facebook and the legitimate Facebook application is that the malware version requests even more permissions, and since it is installed by default, does not even require user consent for that.
The secret add-on functions are wide-ranging. In this example, the app can access the Internet, read and send SMS, subsequently install apps, see, store and amend call data and data about the smartphone, access the contact list, obtain location data and monitor app updates.
These permissions enable extensive misuse: location detection, listening to and recording telephone calls or conversations, making purchases, bank fraud or sending premium SMS.
Malicious applications that are preloaded on devices pose two main issues for users when it comes to identification and removal. First, since these apps inherit the functions of their host application, e.g. Facebook, they function as the user would expect them to.
It is therefore difficult to detect whether a preloaded application is malicious or not. One could compare the permissions of the installed application with the permissions the legitimate application to find out about that, or run security software instead to scan the system for malware. Security software on the other hand may not detect it if the malware is not known.
Once a malicious preloaded application has been detected, users bump into the issue that these applications cannot be removed as they have been pre-installed on the device. The only option available on the device itself is to disable the application.
Another option would be to root the device or start with a clean slate by installing a different environment on it.
G Data believes that the manipulation is not carried out by the device manufacturer but by middleman who operate out of China. The company discovered malware on three mobile devices in factory condition (the Star N8500, Star 8000 and IceFox Razor).
The list of infected models includes devices by Xiaomi, Huawei and Lenovo (MI3, G510 and S860), a well as devices from Alps, Sesonn, Xido and Concorde.
Most devices are sold in China and Europe. A quick check on the German and US Amazon website revealed that Xiamoi's, Huawei's and Lenovo's devices were sold there. This does not necessarily mean that the devices sold there are infected though.
Closing Words
The devices are not overly popular in Europe or America, and some of them appear to be only available in China and Asia. Still, it is important to know that this is happening and that new devices may ship with malicious code.


















Well it is possible to buy a new smartphone and go to someone to reset it and install a brand new Android 4.4.2 for example?
Any app, be it system or not, can be uninstalled. You just need root access on your device. Problem is that not all instances of pre-installed malware can be dealt with that way. Some of it may be hardcoded and not possible to get rid of, short of installing a custom ROM (and even that is not a 100 percent guarantee for a malware free device).
Pre-installed malware and spyware in Chinese devices has been a big problem for quite some time now. Chinese third party (unofficial) resellers have made it a pretty common practice to install modified ROMs of their own (in most cases loaded with some kind of malware) on the otherwise genuine devices that they sell. Even more troubling now is that even manufacturers have turned to the malpractice.
Google Nexus devices come with stock android.
Samsung likes to install many other own apps instead of using Google apps
Martin,what about updating such app through play store will it update since signature shouldn’t match?
It’s Xiaomi, not Xiamoi.
Yes, you are correct. Not being able to uninstall certain apps is a system feature meant for system apps.
Some people just abuse that… :/
Thank you.
Asus even installs Clean Master as a system app… It’s totally useless, this app just deletes temporary files and after a few hours they just come back and then you have to clean them again, it’s nonsensical. Yet you cannot uninstall it on some Asus devices, you can only disable it…
Preloaded spyware, as opposed to operating system spyware? I thought it was already decided, you can either have a smart phone OR privacy?
Regarding this: “Once a malicious preloaded application has been detected, users bump into the issue that these applications cannot be removed as they have been pre-installed on the device. The only option available on the device itself is to disable the application.”
I am no Android expert, but I own 1 Android phone and 4 Android tablets by various manufacturers, such as HTC, Samsung and Asus. Well, on each of them several apps cannot be removed, but I believe this is due to the manufacturer customizazion of Android rather than to the fact that they contain malware. Is my assumption correct?
Thanks.
Yes that is correct Marco.
Thank you Martin and Noel.
It’s very annoying though not to be able to uninstall certain apps. For example I never use Facebook on mobiles/tablets, but it’s impossible to uninstall it. Same applies to several chat apps, video apps, games etc. Basically, unless you root your device, you have not full control on it.
While your understanding is partially correct, my understanding is, the manufacturer gets paid to install some of the apps, advertisement you might say. The Chinese manufacturers have gone in step ahead to help themselves to install malware infected apps, so getting double bonus.
@Martin,
I wonder through, if these phones are listening or recording conversations around them, who has time to go through and take ‘useful’ data. There must be thousands of these phones in the market. I can’t even go through my dashcam data quickly. Really curious to know how they do it (if you know or have a hunch).