Use Fiddler to determine which connections Windows 10 establishes automatically
A lot has been found out about the data collection that is going on in Microsoft's new operating system Windows 10.
We have covered these issues in our Windows 10 privacy guide, but it became clear quickly that Windows was still phoning home at times even when you disable or block all options provided under settings and elsewhere.
Most users are probably unaware of this since it all happens in the background. You can check out Ars Technica's findings on the matter which provide you with details about network activity after turning off or disabling phone-home features such as Cortana or Web Search.
But what if you want to find out about that on your own? The following guide provides you with information on how to set up your own network monitor to get a detailed account on what is happening in the background when you are using your computer and when your computer is idle.
It works well for all kind of tasks, not only to monitor the operating system level but also applications or apps.
Note: Fiddler may not catch all network traffic even if you configure it to capture http and https traffic. As Ars Technica notes, Windows appears to use a content deliver network that bypasses network monitors.
It is recommended to run the program in a virtual machine as it needs to install a root certificate on the system in order to capture https traffic. While you can install the certificate on the underlying system as well, it is not recommended. If you still want to go ahead, make sure you remove it once you are done.
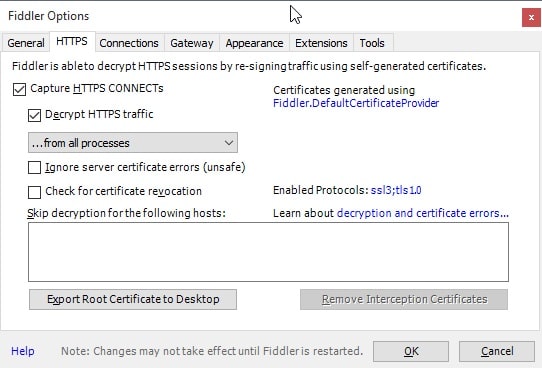
You need to download Fiddler4 from the developer website and install it afterwards. Start the program, and select Tools > Fiddler Options.
Switch to HTTPS and check the "Decrypt HTTPS traffic" box. Make sure all processes are listed and click ok. Fiddler displays its root certificate warning prompt which you need to accept to continue.
A security warning is displayed afterwards which you need to accept as well. You need to accept the User Account Control prompt as well to complete the process, and then that you "really" want to add the certificate.
Once you are back in the main interface select Stream in the main toolbar so that it is highlighted with a rectangular box around it.
Make sure capturing is listed in the lower left corner.
That's all you need to do and network traffic should start to show up in the interface as soon as it occurs. A simple example of this is the ping to bing.com when you use the search, even if you have disabled web search previously.
As soon as you start typing the first character in the search form, a ping to bing.com is sent by the operating system.
Remove the root certificate
To remove the root certificate again, do the following:
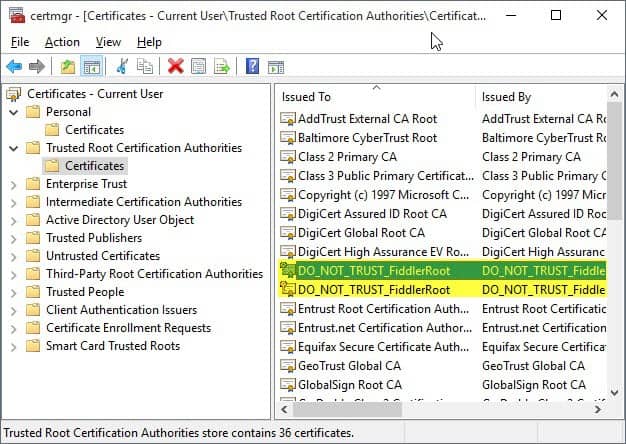
- Tap on the Windows-key and type Certificate.
- Select "Manage user certificates" from the list of results.
- Open Trusted Root Certification Authorities > Certificates.
- Locate all (should be two) DO_NOT_TRUST_FiddlerRoot certificates.
- Select them and hit the delete key on the keyboard.
- Select yes when the prompt is displayed to remove it from the system.

















I made an encrypted linux usb pen drive with steam gaming and popcorntime streaming to a dynamic ram disk =)
Thanks MS and windows for giving me the motivation to try this stuff, its so cool. Now to dual boot.
“We want to move from people needing Windows, to choosing Windows, to loving Windows, to being spied on by Windows”
I am not quite up to speed on OS support, but wouldn’t Wireshark display this traffic and more without having to (heh) fiddle with certificates?
And seeing what all is happening in Windows 10, and keeping in mind that some settings can’t be turned all the way off (especially on Windows 10 Home) perhaps it is time to take a look at Comodo’s firewall again? It used to be you could turn it up to 11 and then some…
To gain readable access to a https datastream you need a certificate regardless of the product you use; otherwise all you will see is encrypted data.
For firewalls, I’m not sure about Comodo, but several of the Win 10 compatible ones have had to hard code rules to allow certain processes in win 10 net access to avoid unwanted issues just in running the os.
This definitely does not look good for Microsoft’s brand new operating system. They like to shoot themselves in the foot, don’t they?
Although the concerns are understandable and welcome, I believe a lot has to do with misinformation. There are definitely things the UI does not allow you to control but if you disable components and behaviors, then they are disabled, period. It’d be nice if the article went deeper since it states that “it became clear quickly that Windows was still phoning home at times even when you disable or block all options provided under settings and elsewhere.” What exactly is not completely disabled if you explicitly disable it?
Take a read of the Arts article Martin linked to.
All privacy settings set to not send data, and yet in their example, there is a process called uploaddata that is sending info to MS including your machine ID. Peter couldn’t interpret the data being sent.
So if the uploaded data is not Bing, not cortana, not IE etc, what exactly is it? And why has MS hidden the data transmission using CDN?
Once upon a time, ssw.live.com was used by Windows Messenger to upload logs to MS via a built-in proxy.
I don’t know if the aspx has changed, but sending logs should not happen if you have the privacy options configured; but apparently they still might be sent.
I see some pings to:
a.gfx.ms
The page does have NO index page. Seems like jQuery server and it is owned by Microsoft.
A simple example is the ping to Bing when you run a search. Why would it need to do that if you have web search disabled?