Tor Browser 4.5 introduces security slider and improvements
The Tor Browser Team has released Tor version 4.5 for all supported operating systems. The update is considered significant which is why automatic updates have been delayed for a week.
Tor users running an older version of the browser can download the most recent build from the official project page.
Here is a short introduction to Tor in case you have never come into contact with it. Tor Browser is a hardened customized version of Firefox that uses the Tor network to protect your privacy on the Internet.
The browser ships with Tor integrated (and security add-ons such as NoScript and HTTPS Everywhere) which means that you only need to download and run it to stay anonymous in the Internet and improve security and privacy in the process.
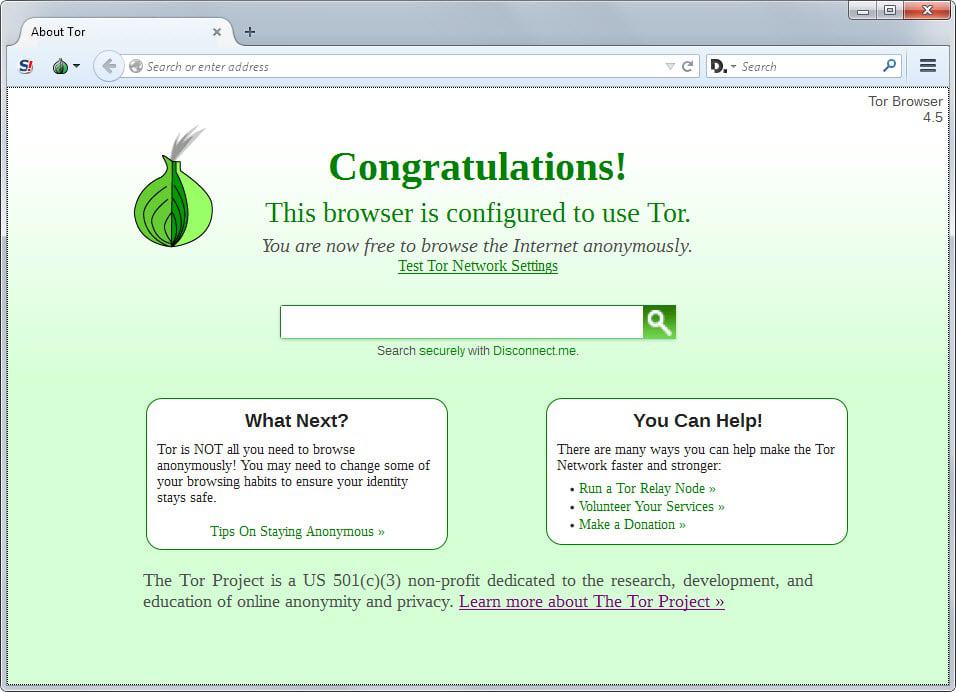
A new feature of Tor Browser 4.5 is the security slider which you access with a click on the Tor icon and the selection of privacy and security settings from the menu that opens up.
There you find a slider to adjust the general security level of the browser. The default level is set to low which ensures compatibility with most sites and technology.
If you switch it to medium-low instead, changes are made to the browser. Here is a list of what each level changes:
- High - JavaScript is disabled on all sites by default, some types of images are disabled.
- Medium-High - All JavaScript performance optimizations are disabled, some font rendering features are disabled, JavaScript is disabled on all non-HTTPS sites by default.
- Medium-Low - HTML5 video and audio are click-to-play, some JavaScript performance optimizations are disabled, remote JAR files are blocked and some methods to display math equations are disabled.
- Low (default) - All browser features are enabled.
Compatibility drops and security rises with each security level. The settings display privacy related options as well which are all enabled by default.
Browsing history and data is not recorded which means Tor Browser runs private browsing mode permanently unless the feature is disabled. Furthermore, plugins are disabled and third-party cookies restricted.
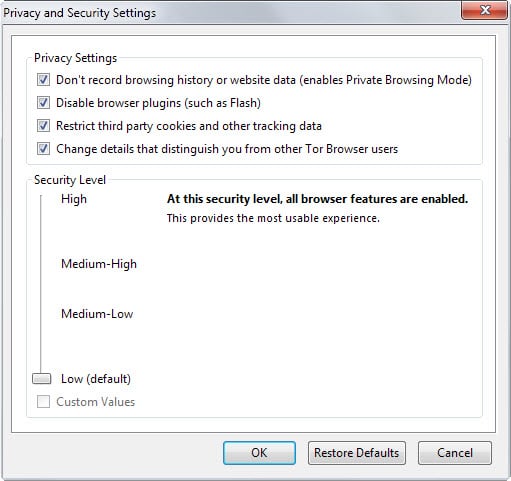
The Tor menu itself has been improved as well. It displays information about the active Tor circuit and an option to change the circuit with a single click.
The circuit refers to the servers your traffic is routed through on its way to the website or application you open in the Tor Browser.
Overall circuit handling was improved in this release. Was it previously sometimes the case that circuit information changed suddenly, and with it information about your location and language among other things, it is now the case that the same circuit will be used while a site is active in the browser.
Additional security and privacy improvements are introduced in Tor Browser 4.5. Here is a short list:
- SharedWorker API has been disabled to prevent cross-site and third-party communication.
- Device sensor and video statistics APIs have been disabled.
- Rewrite of obfs2, obfs3 and ScrambleSuit transports and introduction of obfs4 transport which comes with additional DPI and probing resistance features.
- Windows packages are signed by DigiCert.
- Automatic updates are signed with an offline signing key now.
- Default search provider changed to Disconnect.
Now You: Are you using the Tor browser? What's your take on the update and the browser in general?



















> Tor bundle is not perfectly anonymous and should not be described as such. Many issues, such as bad nodes and poor execution make it complex.
Well, that attacks are more theoretically, and now everyone are freaking out because of this. The real story is that no matter if the exit notes are compromised, as long the encrypted traffic goes in it doesn’t matter. The only problem is that if you send in unencrypted traffic such plain text passwords it goes trough the nodes and “maybe” someone right after the first node are maybe able to log and see the traffic in fact if you use I2P together with Tor Browser Bundle I know no attack how to crack such things since the local traffic is also obfuscated.
ATM there are only theoretically attacks which is very complicated to manage even for the NSA itself (and don’t forget that NSA helped to build TOR and spent a lot of money to maintain and improve the project!) but that doesn’t automatically mean it’s insecure because the NSA may use half of all Nodes. It’s just playing with the fear of people and nothing more, since the Browser and the protocol gets regular updates and a lot of people watching that project I bet it’s actually very hard o compromise the idea behind it. Theoretically all is hackable, theoretically! But in fact to make it hard or harder with proper implemented encryption and if people watching the code all the time and compare if there is maybe suspected behavior.
http://freehaven.net/anonbib/
Tom Hawack, you seem to contradict yourself: in our society “[…]assuming, on the front-line” is something that borders on revolutionary, and yet you consider that to be a “a poor suburb state of mind”. Could you make up your mind, please?
“assuming, on the front-line” is something that borders on revolutionary” is an odd assertion but if you assume it then it’s a good start. On the front-line means not hidden among the crowd, means being responsible, and could mean being in front in order to shout for someone handling the idea as you do, and that relates to the “poor suburb state of mind” as well!
Don’t make life tougher than it is nor things complicated when in fact they are only complex once you stop conceiving them as a battle. The point is to understand, to decide and to perform. Being (excessively) hidden is more of voyeurism as I see it!
Tor bundle is not perfectly anonymous and should not be described as such.
Many issues, such as bad nodes and poor execution make it complex.
Poor Tom has no security or privacy and the ‘new era of light’ is shining on his mobile, his pc, his xbox, tv and landline,
among others. Should he try and do something about it he will face serious opposition, illurstrated below:
http://www.theguardian.com/world/2013/oct/04/tor-attacks-nsa-users-online-anonymity
https://www.schneier.com/blog/archives/2013/08/has_tor_been_co.html
Well… those who read my comments here know how much I am concerned with security and privacy! But as I wrote above privacy is one thing and navigating with Tor is another. One can perfectly well handle his privacy and security without hiding like a little rabbit! The point is the IP? Let it be known and, for the fun once in a while or in a very particular situation (besides porn which much motivate 90% of privacy seekers) then enjoy being invisible with Tor or a shadow with a VPN… but otherwise it remains IMO relevant of a state of mind which is not mine. I have good security, don’t worry for me, pal. And privacy is determined by my mood of the day, no more :)
I just remembered this article read on Slashdot a few days ago about this hacker who got caught because his ego made him forget never to publish a real email address. He had all security and privacy imaginable (Tor perhaps included), the Feds had been after him for months and… hop! Privacy is knowing what to say, how, when and where to say this or not say that. Its not only your Tor thing!
The Tor Browser usage does not necessarily mean you’re heading to the dark side of the web, there are times when anonymity is necessary, particularly in countries where freedom of expression is curbed.
Anonymity does not transform you into a villain, all depends on your intention.
“Tor users running an older version of the browser can download the most recent build from the official project page”…..
or just open it up and you’ll be asked to click on the onion to download latest version from torproject.org :)
I am not using the TOR browser and I have no intention of doing so. Privacy at the cost of anonymity at the cost of paranoia at the cost of a diminished surfing experience is not my cup of tea. Yet I am very concerned by security and privacy but not at this price and I’d even say not with this philosophy. I wish not to be in the underground proximity of a cellar which includes pedophilia, crooks, subversion together with honest users afraid of the world to the point of shaking in the depths of an institutional paranoia. Not for me.
Now, should I be aware of what I am not, I’d rather exercise intoxication and disinformation than a revolutionary state of mind opposed to entities resumed to one (“They”) by weird thinkers who conceive the world in terms of bad and good. Life is not a battle ground, we are in 2015 not in the Middle Ages, Aquarius is a new era of light, not a past one of obscurantism. Let it BE. Exercise caution but let it be.
“resumed to one”?
resigned to… Aquarius and a side order of fries?
I’ll go with the privacy and a revolutionary state of mind any time.
A poor suburb state of mind I believe, where the world is conceived as binary, the good guys (the sect) and the bad ones (the others). I really believe that evolution is not in hiding but in assuming, on the front-line. It’s a matter of equilibrium : you don’t have to hide yourself to hide your privacy, but weigh what you say, how and when. It is in fact a question of wise responsibility. There are situations of course that require a deep dive into darkness, but who is either an agent either a crook either insane? Come on, join the adventurers!
Any info on why Disconnect was chosen as default search provider?
I wish they had a Chrome version.
^ lol, innocent!
innocent ~= naïve?
“Whoa! Lookit, a magic slider!!! Now nobodee kin steal my nimmity and megahurtz”
The addition of a dumbed-down slider is obviously intended to appeal to a broader audience, to increase the reach, the accessibility, of Tor Browser Bundle. Torproject is squirming — among users and former users and potential users… the word is out that “torification is a PITA. It breaks stuff”. Does the addition of the slider represent an attempt to convey the message “yeahbut YOU get to control the degree of breakage” ?
The default slider setting does not enforce “remote JAR files are blocked”? Permitted-by-default seems an unwise setting. When the heck is allowing retrieval and execution of content within remote JAR files _ever_ sensible? Sigh, this reinforces my skepticism regarding the competency of the torbrowser devs.