Do this if a company's user database got hacked and your account is in it
There are several ways how attackers gain access to Internet accounts. One common attack form is to attack servers on the Internet directly, to download the user database.
While most companies protect the database, or at the very least important bits of data such as passwords in it, it is possible to decrypt many of them using dictionary-based or brute-force attacks.
Server attacks are not the only way, it is also possible that malicious software is executed on a user's home system, that data is stolen directly from a local PC, or that a user forgets to sign out on public computer systems.
Kickstarter announced yesterday that hackers gained access to the company's user database.
I would like to use the opportunity to list important steps that you should undertake if a successful server hack affected at least one of your accounts
The steps are ordered by importance, so that you know what to do first.
User database on a server was hacked
Use the following five points to secure your account and other accounts that share the password that you have used to sign in to the service that got hacked.
- Understand what happened and how you are affected.
- Change your account password immediately.
- Change the passwords of other accounts if you used the same password.
- Be wary of personalized spam messages.
- Monitor your accounts.
1. If a company server has been hacked, you may receive word of it immediately by email, notification on next log in, and in some cases never.
If a company releases an announcement, you need to read it carefully to understand what the attackers have downloaded.
Were passwords stolen, or other important data such as credit card numbers?
2. Once you are aware of the scope of the hack, you should change your account password immediately. Companies sometimes reset the passwords automatically to protect the accounts from danger.
Either way, you do need to visit the service's website, sign-in to your account, and locate the password change option to pick a new account password.
Make sure you select a secure password that cannot be easily guessed. While some services may limit the characters of the password, my suggestion would be to use at least 16 characters that include numbers, upper and lower case characters and at least one symbol.
3. If you have used the same email or username, and password on other websites, you need to head over to them and change your password on those sites as well.
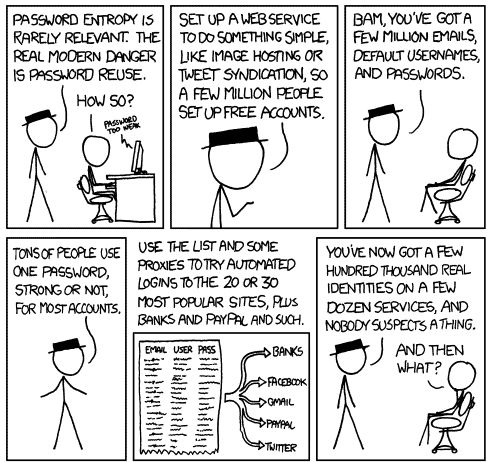
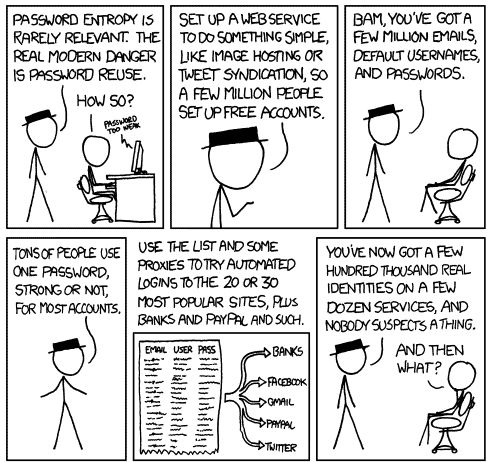
Attackers may try to gain access to other services using the emails and passwords that they have stolen knowing very well that many users do not use unique passwords for every service they use.
So, change passwords for all accounts that use the same password, and make sure it is unique for all of them.
Suggestion: Use a password manager such as KeePass (offline use) or LastPass (online use) that help you create secure passwords and remember them.
4. Hackers may gain access to additional information, such as your name or address. This provides them with information to create personalized spam messages.
Most spam does not address you by name for instance, but a security message that seemingly comes from your bank, PayPal, Facebook or Google, that is using your name, looks legit on first glance, and that is where you may fall prey again.
Suggestion: Use this phishing flowchart if you have troubles identifying spam messages.
5. It is important to monitor your accounts to make sure that everything is alright. This is especially true for financial activities, but you may also want to keep an eye on interactions with other Internet users, and spam issues.
If financial information were stolen, credit cards come to mind, you should also let your bank know about this immediately. At the very least, monitor the card's transactions closely to make sure it is not used by a third-party.
Bonus Tip:Â Make sure you make use of additional protection options such as two-factor authentication if provided by the service. Stealing only the account password won't be enough then to gain access to your account, as another code is required to do so.
Advertisement















Excellent info as always, Martin. I also use Troy Hunt’s creation to allow monitoring of email addresses getting into wild via data breaches, “PwnedList” (https://haveibeenpwned.com/, which I 1st learned about from your Last Pass article “LastPass Sentry: automatic leak checks for leaks”, I believe). I’ve followed your inclination to prefer a local pwd mgr db & migrated to KeePass – the PE v., as I prefer portable over installed versions wherever possible, even if I have to gain permission to create them myself with something like P-Apps (http://portable-app.com/) – so I need to thank you for that, as well. GHacks continues to be an invaluable resource that is greatly appreciated!
Glad that I could be of help Jones.
Think how much Facebook’s password list would be worth. And like your XKCD cartoon, that’s a free service… :-)
And if you could combine the password lists from the likes of Facebook, Twitter, Google, Microsoft & Yahoo, that would be one hell of a password list, even if only in hashed form. The sceptic in me sometimes wonders whether these breaches are really a government agency somewhere gaining data for password pattern/cracking analysis.
do they really keep any user data in plain text? what kind of security this is?
Forbes has been hacked by SEA. A file with million user+password is for grabs.
https://twitter.com/Official_SEA16/status/434375422084542465