The Firefox NoScript guide you have all been waiting for
Update: We have published a new NoScript guide for Firefox 57 and newer.
One of the core reasons why I'm using the Firefox web browser on my desktop PC and not another browser is that the NoScript extension is only available for that browser.
NoScript does what the name implies, it blocks scripts from running automatically on all most websites. This boosts security significantly, as most attacks run on websites require scripts to be effective. It will also improve page loading times on average, as less contents need to be loaded when NoScript is enabled.
The downside here is that site functionality may also not work properly on select sites. Since scripts are blocked by default, a site may simply not work at all, or only partially with NoScript installed.
The extension offers controls to resolve those issue though, as you can allow scripts to run temporarily or permanently on sites.
Another issue is that script are blocked on the domain level. Most websites load scripts from various sources. First from its own domain, but also from third-party servers, for instance to display ads, use tracking scripts, or to make use of a hosted version of jquery.
It is often difficult to tell which scripts are required for a site's core functionality, and which are not. This is especially true for Internet users who have little experience when it comes to domains, website technologies and scripts.
The NoScript configuration
The NoScript out of the box experience is quite good. You can use it without modifications, but if you want to get the most out of the add-on, you may want to go through the options at least once to make sure everything is configured in an optimal fashion.
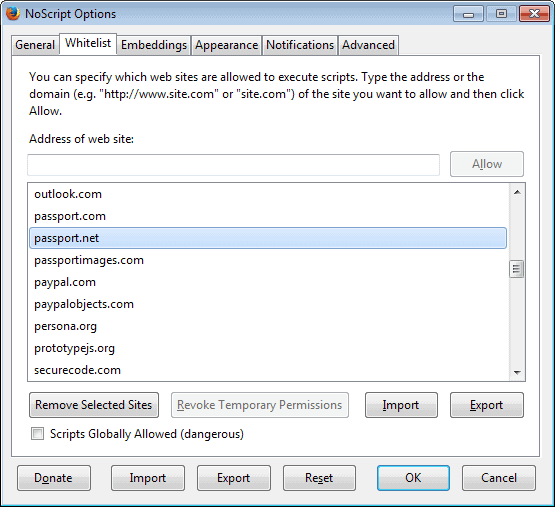
As I mentioned earlier, NoScript blocks scripts on most websites by default. The extension ships with a domain whitelist, which means that the sites that you find here are allowed to run scripts they host on their own domain.
Side Tip: NoScript distinguishes between root domains and subdomains. Domains like addons.mozilla.org and mozilla.org are handled as different domains by the extension.
Among the list of domains that are whitelisted are addons.mozilla.org, google.com, googleapis.com, live.com, hotmail.com, outlook.com or paypal.com.
You can remove any of the whitelisted sites under Whitelist in the NoScript options.
My suggestion would be to remove domains that you do not want listed here. I recommend leaving Firefox's internal pages on the list though, as you will run into issues otherwise.
Here you can also import or export the selection, useful if you use Firefox on multiple devices and want to use the same whitelist.
The second configuration change that you may want to do concerns the NoScript icon. You may want to place it in a location that you can easily access.
I have placed mine in the add-on bar, but with the removal of the bar in Firefox Australis (version 29 is the target) you may also place it on the main toolbar of the browser.
Another option that you have is to use the context menu instead exclusively for that. NoScript adds an entry to Firefox's right-click context menu which you can use to allow or disallow sites, or to open the options and other features of the extension.
If you use the icon, you can make use of a couple of smart features the developer has built-into the extension. To allow all scripts on the current site, middle-click the icon. You can furthermore enable a left-click toggle to allow or block the top-level site under General in the options.
You may notice that a message about blocked scripts is displayed on the screen in a notification. This can be useful if you use the context menu exclusively, but if you use an icon, that is also highlighted by the icon itself.
I prefer to remove the notification as it blocks part of the screen without telling me anything that I don't know already.
You can disable the notification under the notifications tab in the options.
Instead of displaying a message, you can also enable audio feedback instead. I do not recommend you do so, especially if you load many sites during a browsing session.
Going back to the sites listing that NoScript displays when you left-click or right-click on the icon.
The menu highlights all scripts that the site tries to run. The root domain is always listed at the bottom of the listing, while all other domains are listed on top of it.
Tip: To ensure a site's full functionality, it is usually enough to allow the root domain. I'd recommend you load sites without whitelisting first to see if it works out of the box or not. If it does not, it is likely caused by a script that needs to be loaded. There are exceptions to the rule. You may find that some sites use content distribution networks, e.g. cdn.ghacks.net that you need to allow as well, and that some sites load libraries from third party sites such as jquery.
As I have mentioned in my 6 NoScript tips guide, you can middle-click on any domain here to run a security check on it. When you middle-click, you are taken to a page on the NoScript website that links to several popular site security services such as Web of Trust, McAfee Site Advisor, or hpHost.
Use those to check a domain that you do not know anything about before you allow it. An alternative to that is to manually check a domain on Virustotal.
Tip: Right-click any domain name to copy it to the clipboard.
Digging deeper
Lets dig in a little bit deeper. NoScript offers more than just script blocking. It can be used to handle embedded contents as well.
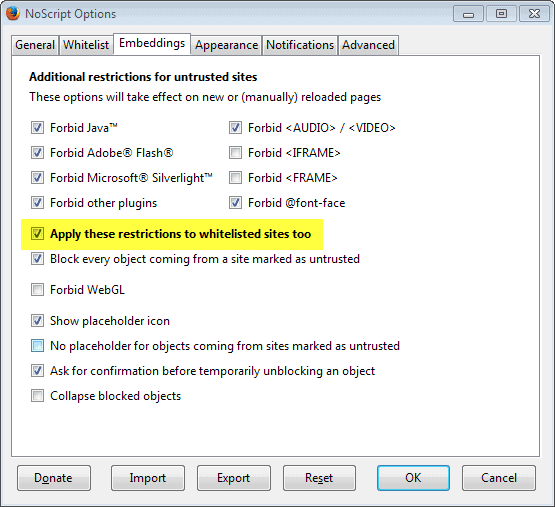
While those contents are blocked by default for sites that are not whitelist, they are not for sites that you have temporarily or permanently whitelisted.
This means that contents such as Java, Flash, Silverlight or other plugins are loaded on whitelisted sites by default. If you do not want that to happen, you have to make the following configuration change under NoScript Options > Embeddings.
Here is an example where this may be useful. Say you need to whitelist a site to make use of all of its functionality. By doing so, you may inadvertently also allow it to play Flash ads, videos, or other contents that require the use of plug-ins.
While it may make sense to allow these contents to play on whitelisted sites sites such as YouTube, as you visit the site for videos, it improves security and privacy if you apple these restrictions to whitelisted sites as well.
It means more clicking though to enable those contents, but it is a trade-off.
If you enable that feature, you will get a confirmation message every time you click on blocked contents. You can disable that by disabling "Ask for confirmation before temporarily unblocking an object".
Note: you can configure the forbidden items on the same page. So, it is theoretically possible to allow some of the contents while disallowing others. One possible option is to allow Flash, and to disallow all other contents.
Advanced options
The advanced options may look scary at first, as you find many technical terms such as XSLT, XSS, ABE, or even ping, mentioned here.
Generally speaking, those options are best left alone unless you require specific features.
One feature that may be of interest here is the handling of secure cookies. You can configure NoScript to force encryption for cookies set over HTTPS for select sites.
Some web services set cookies over a secure connection but fail to mark those cookies as secure. The result is that requests for that cookie from the same domain are allowed even if they come from non-HTTPS pages.
You may however run into issues on some sites, so that you may not be able to log in on those sites anymore, or are logged out automatically when you switch pages.
You find information about those issues by opening Firefox's Web Console using the shortcut Ctrl-Shift-i. Use the information to add exceptions to the rule.
Other features that you may want to take a closer look at are options to forbid bookmarklets on untrusted sites, allow local links for trusted sites, or to disallow the attempt to fix JavaScript links.
Further reading
Probably the best location for additional information about NoScript is the FAQ that the author maintains. Several of the technological terms are explained here, and there is a tips and tricks section as well that you may find handy.
Questions are based asked on the official forum which is well frequented.





















I must thank you for sharing this useful topic. Really a worth reading post ! it explains it all so easliy ! thank you for sharing this article !!
The most important feature for me is one that’s disabled by default, in the Appearance tab I check Full Addresses. This allows you to whitelist only the exact URL that the website is trying to run a script for, e.g. http://connect.facebook.net. Whitelisting a 2nd level domain will just allow anything that ends with facebook.net (e.g. photocreeper.facebook.net).
The benefit of this is that you can be assured that a website isn’t trying to use a subdomain to do something you’re not comfortable with such as analytics or pushing adverts, though arguably those are better adverts to trust than 3rd party ones the site has less control over.
It’s a little bit more work but very few sites have more than 3 subdomains that are necessary for the site to function as you’d normally see it. Twitter is the only one I use frequently that needs 3 and 2 of those are for presenting images.
This guide is just the thing I was looking for. Thank you.
I know it’s only a minor thing and maybe when this was written, it was a fact, but today it’s not right to state that “One of the core reasons why I’m using the Firefox web browser on my desktop PC and not another browser is that the NoScript extension is only available for that browser.”, because NoScript it also available to other Mozilla-based web browsers such as SeaMonkey.
Good guide. Unfortunately, I could not find anything about XSS. There is a whitelist for XSS, too, which relies on regular expressions. Thus, adding a site to the XSS whitelist is not as easy as adding it to the script whitelist.
Could you explain how one can add a site (example: http://*.ebay.*) to the XSS whitelist?
That would be highly appreciated.
Thank you very much in advance.
I’ve tried NoScript and have spent the best part of two days trying to whitelist the sites that I visit regularly.
The problem is that very few sites nowadays seem to use a single server. One of my banks for instance appears to use three separate servers. Ebay.co.uk also, for some functions, appears to need ebay.com whitelisted. Newspaper pages use various add ons for commenting (which I want to use), as well as for ads (which I don’t) and videos (which I do on one site, not on others). NoScript doesn’t help me work out which is which, and makes me whitelist all of them. Two days later the Guardian front page is still broken.
I’ve ended up switching it off. A pity, as I would love to block misformed scripts on idiot bloggers’ Nathan Barley-esque pages, that cause my computer to hang – but NoScript is wasting more time than those few scripts.
By the way, Martin, do you prefer your site
to be whitelisted or don’t you care ?
It is a personal decision. The ads keep the site alive, but we now also have the membership going that gets rid of the ads and allows you to support the site without being exposed to them.
If you ask me, I’d like the site to be whitelisted as this is what keeps it going, but if you do not like the ads, then don’t, or become a member instead and donate any amount you want.
More and more websites seem to be using more and more scripts. Which to me makes dealing with NoScript an ever increasing hassle. But fear is a great motivator so I run NoScript. I routinely forbid doubleclick and scripts that have “Google” or anything that sounds like an advertising in their name (i.e. “ad” in their name) on the theory that they’re tracking where I go. But since I don’t understand most of this stuff I don’t have a clue if what I’m doing makes any sense. As helpful and insightful as this NoScript Guide is I still don’t have the picture. I may be blocking harmless stuff and letting through the bad stuff. If a site doesn’t work unless I allow scripts how do I know which script(s) make the site work and which ones may be bad?
Since I run Firefox in Sandboxie I wonder if it’s really necessary to put up with the hassle of NoScript. As I understand it once I empty the sandbox any tracking cookies or other bad stuff that may be put on my computer will be wiped away. I’m not sure that I even want to know if I’m wrong about that. False security is comforting (for a while).
I use NoScript, but it’s an excellent review.
Thanks!
A NoScript-like extension for Chrome is ScriptSafe. It’s not as easy to use as NoScript, but it’s better than nothing for Chrome javascript blocking.
Oops…I should have done a text search for Chrome on this page before I commented. You already wrote an article on ScriptNo (now ScriptSafe) and linked it on this page.
Thanks for all the great informative articles.
I tried it over 3-4 times & its a hassle for the average punter ,good in principle, but i can get by without it
NoScript is effective. However, it becomes a bit of nuisance when it prevents every site from running and you don’t know exactly what you are blocking. It doesn’t seem to identify `bad scripts’, which would be helpful for my blog, as it keeps jumping around while browsing through it. If I knew what was causing my blog to be so unstable then i could remove the scripts that cause it. Another major cause of instability throughout Firefox is Adobe Flash Player. Firefox consistently refuse to address this ongoing issue and will not admit that Adobe Flash is just not compatible with it, no matter which version you have.
Great tutorials. Simple and straightforward. I’ve been looking for something like this for a while. Many thanks!
never disabled or uninstalled NoScript since installing it. that shows how good it is
*tip*
if you want to run scripts of a site on one site only
1- go to NoScrript options, Advanced, ABE, User
add this
Site .site1.com
Accept from .site2.com
Deny
2- add site1 and site2 to the NoScrript whitelist
this will allow scripts from site1.com to run only on site2.com
note that site1 can be the same as site2. this can be useful for example if you want youtube scripts to run only on youtube not on any other site
more here
http://noscript.net/abe/
I want my policy to allow me to cherry pick which Google subdomains to allow scripts to run on – I don’t want them on Google search itself. I tried setting it up for Docs:
Site .google.com
Accept from .docs.google.com
Deny
Docs works, but this breaks Google, and when I go to Google, NoScript tells me that the request has been blocked:
http://i.imgur.com/fYQKt3W.png
How do I rewrite the policy to allow Google to load results but block scripts?
Thank you so very much for the missing steps to make ABE work. It was not clear on the NoScript ABE page that site1 and site2 had to be whitelisted! :)
What this and other addons like this (Request Policy) needs is some sort of user shared easylist so we do not have to be constantly defining rules our entire life, collectively we can improve our experience.
I am so glad to Martin Brinkmann`s quick action,
i read the article, and looking for more^^
For you poor misguided souls that love the Addon Bar you can get it back with Classic Theme Restorer addon. It is activated by default.
I hate so i put my most often used buttons on the Nav Bar and the left-side of the Bookmarks Toolbar. I put my lesser used buttons in the Customize Dropdown menu.
You can also put buttons on the Menu Bar To the right of Help and toggle that bar with the Alt key.
One of my fave addons! Too bad the dev doesn’t have a built-in inspection tool so you can quickly find the visually-offending Javascript effect/animation and kill it all within the addon’s GUI (picky, aren’t I?! LOL!).
NoScript… overkill for the overly paranoid. More trouble than it’s worth and it breaks websites far too much.
Couldn’t agree more; found this site while seeking ways to disable this exceptionally intrusive nanny, which simply showed up un-bidden on this machine. If needed, I’ll sh*tpail FIrefox for good over this hijack.
Thank you for the NoScript guide i agree with you Martin
if a website cant be viewed without javascript i probably wont visited it
I find it useful to set noscript.sync.enabled to true in about:config, so that all your NoScript settings get synchronized.
Good point, thanks for the tip!
Excellent guide. Thanks. I’ve gotten happily used to NOT having auto-play ads and popovers appearing. It seems to me that web advertisers have soiled their own sheets by making advertisements intrusive and obnoxious. But that’s another discussion.
Usually rather than mess with whitelisting, I copy the website address, open Chromium in another workspace, and use it for just that site. Everyone develops their own way of doing things.
I haven’t run NoScript in years. It’s a “block all and whitelist what breaks” solution. It can take weeks to set up and it’s a constantly moving target. Too much trouble IMO.
I use Adblock Plus in the exact opposite way by blocking based on a blacklist and building rules for sites that have extra annoyances. All plugins are set to “Ask to Activate”. Sites are rarely if ever broken and I retain my sanity this way ;-)
Martin, would you mind sharing your reasons for using NoScript?
Isnt it obvious? Protection? Nah, just for the fun of using it?
Well I have three core reasons for running NoScript: security, privacy and speed.
Security because it blocks the execution of scripts that would otherwise run. If you run a blacklist approach, they will run until you blacklist them.
Privacy because it blocks the majority of tracking scripts (including social media). The only exception to the rule is server-side analytics.
Speed because you load less, and therefore things load faster on average.
You can achieve part of what NoScript does with an adblocker. If you block ads, sites will load faster, and it may also improve your privacy and security. But adblockers only go that far.
Security – I agree with the argument that NoScript doesn’t offer protection. If you allow ANY server side script to run then you are at risk. If a script is needed at a site you frequent then you whitelist it – you’re now at risk. You have no control over that site so you can’t claim “trust”.
Privacy – Most tracking scripts are blocked with the right lists in ADP. There are other ways besides scripting to track someone (you’ve written about many of them). I have my browser icon set to a batch file that executes CCleaner automatically after I close my browser. Assuring that all (except fingerprinting) forms of tracking are wiped before a new session is started.
Speed – It’s much less of an issue these days. JS engines, ISP speeds and hw are no longer huge bottlenecks. ADP is also excellent here.
Despite being open source I and many others lost faith in NoScript when the dev was constantly pushing updates driving traffic to his whitelisted home page that served up lots of ads. I don’t know if this is still the default?
I like it’s inclusion in TorBrowser but I still can’t find a good argument for everyday use. Thanks for the insight though!
About security, you have to see understand that NoScript’s approach is still better than not running it. Yes, if you whitelist a site it can run scripts, that is why this is reserved to sites that you trust. Whitelisting essential means that you go back to how Firefox handles all of these connections in first place.
Plus, even if you whitelist, you can still prevent the automatic execution of select plugins and benefit from other protection features the extension provides you with.
How I have configured NoScipt:
Check “Temporarily allow top-level sites by default” and “Base 2nd level domains”
from the general options.
This will allow all the scripts on the visited site (+2nd level domains) but still disallows all 3rd party scripts.
That’s what I do too and, combined with the whitelist, 95% of the websites works properly while the 3rd party scripts still blocked by default. This is a good compromise :)
Great article. Thanks! I didn’t know you could middle-click on the domain and get a report.
Doesn’t NoScript work with SeaMonkey? My friend suggested I try SeaMonkey for just that reason.
It is compatible according to this page, provided you use SeaMonkey 2.0 or up.
http://noscript.net/getit
Eliminate the hassle. Leave it activated. If a site you trust doesn’t work, just click ‘allow all this site’. All done! No figuring your way through the myriad of NoScript options.
This trades off some of the protection for the sake of convenience, but still protects you better than not having it at all. Coming cold into a new site you are protected. Of course using Web of Trust in conjunction with NoScript is a bit better still.
as a somewhat “advanced” user i’d love to say that i use noscript, but the times i tried it, it was just too much of a hassle with seemingly little benefit.
don’t get me wrong, i’d of course prefer it to have more control about what runs in my browser and what not, improving both privacy and security, but having to configure many sites i visit for the first time would just take too much joy out of browsing the internet.
maybe i’ll give it another try someday, but for now i’m ok without noscript.
Either you use it, or you do not – there is no “in between”; to get things done usually takes some effort, but perhaps you are somewhat “lazy”.
This. Exactly what I would have commented but since fokka did it I will just say +1
But, but Javascript is everywhere on the web now.
> Javascript is everywhere
Yes, which makes simply turning off JavaScript infeasible, unless you’re Richard Stallman. That was, in fact, the original motivation that prompted NoScript: we need a way to allow JavaScript selectively.
NoScript is capable of default-deny (out of the box), default-allow (“Scripts Globally Allowed”), or a few other modes that offer various tradeoffs of convenience and security. Plus it has some behind-the-scenes protections like the XSS and clickjacking filters.
Sure, but many sites do not require it for core functionality. Plus, if you trust a site, you can temporarily allow it.
Awesome feature and I love Mozilla because its browser is built around protecting its USERS, not spying on them. Thanks for the great tutorial!